Bank of America, the second-largest bank in the United States with roughly 69 million clients, has not been directly hacked in any of the recent incidents that have exposed customer data. That is a meaningful distinction, but it offers limited comfort to the customers affected. In each case, a third-party vendor that handled Bank of America customer data was breached, and the information flowed out through that opening rather than through the bank’s own systems.
Between 2023 and 2025, Bank of America customers were caught up in at least four separate security incidents involving different vendors. The nature of the data exposed, and the number of people affected, varied considerably across those incidents. Here is a clear account of each one, what was taken, and what you should do if your information was involved to avoid identity theft.
Incogni’s data removal service scans the internet for your personal information and sends removal requests to take it down on your behalf.
May 2023: Ernst & Young / MOVEit (30,210 Customers)
In May 2023, the Clop ransomware gang exploited a zero-day vulnerability in the MOVEit Transfer file transfer platform, a mass-exploitation campaign that ultimately affected hundreds of organizations worldwide. Ernst & Young, the accounting firm that Bank of America uses for certain services, was among the victims.
Ernst & Young confirmed that Bank of America’s own systems and servers were not affected. The breach at Ernst & Young’s end exposed the financial account information, credit card details, Social Security numbers, and other unique identification numbers of 30,210 Bank of America customers.
>> Learn More: What is Personally Identifiable Information?
November 2023: Infosys McCamish Systems / LockBit (57,028 Customers, Later Revised to 6 Million Total)
On November 3, 2023, the LockBit ransomware group attacked Infosys McCamish Systems, a U.S. subsidiary of Indian IT giant Infosys that provides life insurance and retirement software and services. The attackers accessed IMS systems between October 29 and November 2, exfiltrating data and then deploying ransomware to encrypt more than 2,000 corporate systems. LockBit later claimed that IMS offered a $50,000 ransom payment, which the group refused as insufficient before leaking stolen data.
IMS notified Bank of America on November 24, 2023, that data concerning deferred compensation plans serviced by the bank may have been compromised. Bank of America sent breach notification letters to affected customers on February 6, 2024, nearly three months after the original attack. A filing with the Maine Attorney General on behalf of Bank of America initially identified 57,028 affected individuals.1
The data potentially compromised included names, addresses, business email addresses, dates of birth, Social Security numbers, and other account information related to deferred compensation plans. Bank of America noted it was “unlikely” that it would be able to determine with certainty exactly what information was accessed.
Critically, IMS’s own investigation later revealed the breach was far broader than initially disclosed. By June 2024, IMS revised its count to 6.08 million individuals across all affected clients, not just Bank of America, making the IMS breach one of the largest data incidents of 2023.2
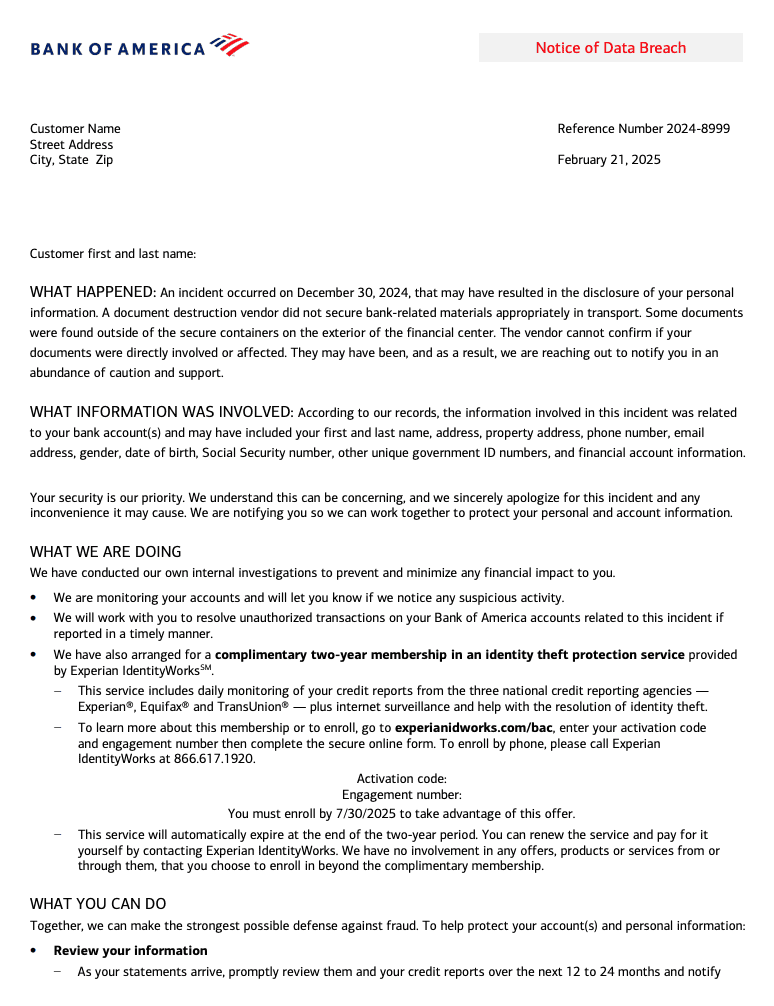
December 2024: Document Destruction Vendor Incident
On December 30, 2024, a third-party document destruction vendor failed to properly secure Bank of America materials during transit. Physical documents were discovered outside of their secure transport containers at the exterior of a bank financial center. Bank of America began notifying some affected customers in early 2025 and offered two years of complimentary identity theft protection services.
This incident involved physical documents rather than a cyberattack, making it categorically different from the other breaches. The scale was smaller, with Bank of America confirming at least two Massachusetts customers directly affected, though the full scope was difficult to determine given the nature of physical document exposure.
FYI: Bank of America also disclosed a separate January 2025 incident in which data from at least 414 customers was compromised through another third-party security failure.
Incidents at a Glance
| Year | Vendor Breached | Data Exposed | BoA Customers Affected | Attack Type |
|---|---|---|---|---|
| Feb. 2023 | NCB Management Services | Names, SSNs, DOBs, driver’s licenses, credit card and account numbers, account balances | ~495,000 | Unauthorized access |
| May 2023 | Ernst & Young (via MOVEit) | Financial account info, credit card details, SSNs, unique IDs | ~30,210 | MOVEit zero-day (Clop) |
| Nov. 2023 | Infosys McCamish Systems | Names, addresses, SSNs, DOBs, deferred compensation plan data | 57,028 (BoA-specific) | Ransomware (LockBit) |
| Dec. 2024 | Unnamed document destruction vendor | Physical banking documents (scope unclear) | Limited, scope unclear | Physical mishandling |
A Pattern of Third-Party Failures
Every significant Bank of America data exposure in recent years has originated with a vendor rather than with the bank’s own systems. Regulators have taken note of this pattern across the industry. In January 2024, the Federal Reserve’s vice chair for supervision stated that there have historically been “gaps” in banks’ efforts to manage risks posed by third parties, and that reliance on outside service providers had grown considerably, bringing greater cyber risk with it.
Security experts note that while the breaches technically occurred at vendor companies, the regulatory and reputational responsibility falls on the bank. Banks are the entities that hold the primary relationship with customers, and customers provide their data to the bank expecting it to be protected regardless of which downstream partners handle it. When vendors are the point of failure, the bank still bears responsibility in the eyes of both regulators and the public.
>> Check Out: Which States Are At Highest Risk of Cyberattacks?
The Infosys McCamish Settlement
Multiple class action lawsuits were filed following the IMS breach, alleging negligence for failing to adequately protect customer data and for delayed and insufficient breach notification. In March 2025, Infosys McCamish Systems agreed to a $17.5 million settlement to resolve six consolidated class action lawsuits. Infosys confirmed the settlement in a regulatory filing on March 14, 2025, noting that the agreement was reached without admission of any liability.
The settlement covers the 6.08 million individuals across all affected IMS clients, not only the 57,028 Bank of America customers initially identified. The agreement is subject to court approval.
Pro Tip: If you received a breach notification in connection with the IMS incident, you should monitor for information about how to file claims once the settlement process is underway.
What Affected Customers Should Do
Check Whether You Received a Notification Letter
Bank of America sent breach notification letters to customers affected by each incident, though often with significant delays. If you received a letter referencing NCB Management, Infosys McCamish, Ernst & Young, or a document destruction vendor, your data was involved in that specific incident. If you had a past-due Bank of America credit card account at any point before 2023 and have not received a notification but are concerned, contact Bank of America directly or check with NCB Management about your status.
Use Have I Been Pwned
Entering your email address at Have I Been Pwned (haveibeenpwned.com) can surface whether your credentials appear in known breach datasets, including those tied to some of the vendor incidents above. This is a useful supplementary check alongside any formal notification you may have received.
FYI: Websites like Have I Been Pwned can also let you know if your data appears on the dark web.
Place a Credit Freeze
Multiple incidents exposed Social Security numbers, and the NCB breach also included credit card numbers and full financial account details. For anyone whose SSN was part of any of these breaches, a credit freeze at all three major bureaus, Equifax, Experian, and TransUnion, is the most effective step to prevent new fraudulent accounts from being opened. It is free and reversible
>> Find Out: How to Get a Free Credit Report
Monitor Your Credit Reports and Bank Statements
Pull your credit reports from AnnualCreditReport.com and review them carefully for accounts or inquiries you do not recognize. Review your Bank of America statements and any statements from other financial institutions for transactions you did not make. Report anything suspicious to your bank immediately. If your closed Bank of America credit card account number was among the NCB data, be alert to attempts to use that information in fraudulent applications elsewhere.
Activate Any Free Identity Protection Offered
Bank of America offered two years of free identity theft protection services to customers affected by the document destruction vendor incident in 2024. For the IMS breach, IMS provided its own notification and protection offering. Check any breach notification letter you received for enrollment instructions, and activate those services before any stated deadline.
>> Check Out: The Best Credit Protection Services
Watch for the Infosys McCamish Settlement
If you were among those notified about the IMS breach, you may be eligible to participate in the $17.5 million class action settlement. The settlement is pending court approval. Once approved, affected individuals will likely receive instructions on how to file a claim. Legal news sources and the settlement administrator’s website will carry updates on the claims process.
Why Vendor Breaches Are So Difficult to Prevent on Your Own
One of the more frustrating aspects of the Bank of America breach pattern is that there is essentially nothing a customer can do to prevent it. You did not choose Infosys McCamish or NCB Management. You probably did not know those companies had your data. And yet your Social Security number, financial account details, and personal information flowed through their systems and were exposed when those systems were attacked.
That reality is part of what makes data broker removal a useful complement to the standard breach response toolkit. Even before these breaches occurred, information about you was likely available through data broker databases that aggregate records from public sources, past breaches, and commercial data purchases. A service like Incogni automates removal requests to those databases on your behalf, limiting the pool of information that criminals can easily cross-reference with what was stolen in any given breach.
FYI: Data removal services can’t undo an exposure. They help reduce how much information is freely findable online, making the stolen data less useful.
The Bottom Line
Bank of America’s own systems have not been directly compromised in any of the recent incidents that exposed customer data. But that framing provides little practical protection to the hundreds of thousands of people whose Social Security numbers, credit card numbers, and financial details were stolen through the bank’s vendor chain. The NCB, MOVEit, and IMS breaches collectively affected well over half a million Bank of America customers, with the IMS breach ultimately touching a much broader population of 6 million individuals across all affected IMS clients.
If you have ever had a Bank of America account, including a closed or past-due account that may have been sold for collection, your information may have passed through one of these vendors. Checking whether you received a notification, placing a credit freeze, and monitoring your credit are the three most impactful steps you can take right now. For those notified about the IMS breach, the $17.5 million settlement awaiting court approval may eventually provide an avenue for compensation.
Frequently Asked Questions
-
Was Bank of America directly hacked?
No. In every incident that has exposed Bank of America customer data in recent years, the breach occurred at a third-party vendor rather than at the bank itself. NCB Management Services, Ernst & Young, and Infosys McCamish Systems were the entities whose systems were compromised. Bank of America confirmed in each case that its own systems and servers were not affected. However, because those vendors held Bank of America customer data, the exposure of that data is still a significant risk to affected customers.
-
How many Bank of America customers were affected by data breaches?
Across the incidents between 2023 and 2025, the number of Bank of America customers directly affected runs into the hundreds of thousands. The NCB Management breach affected approximately 495,000 individuals with former Bank of America credit card accounts. The IMS breach initially identified 57,028 Bank of America deferred compensation customers, though IMS’s total breach count across all clients eventually reached 6.08 million. The Ernst & Young MOVEit breach affected 30,210 Bank of America customers.
-
What data was exposed in the Bank of America / Infosys McCamish breach?
The IMS breach potentially exposed names, addresses, business email addresses, dates of birth, Social Security numbers, and other account information related to Bank of America deferred compensation plans. IMS’s broader data review confirmed the stolen dataset also included financial account numbers, policy numbers, driver’s license numbers, passwords, salary information, and in some cases personal medical information, though not all data types applied to every individual.
-
Is there a settlement for the Bank of America data breach?
Infosys McCamish Systems agreed to a $17.5 million settlement in March 2025 to resolve six class action lawsuits filed in connection with the November 2023 ransomware attack. The settlement covers individuals across all of IMS’s affected clients, not only Bank of America customers. It is pending court approval. Separate legal action related to the NCB Management breach was also investigated by consumer law firms.
-
How can I check if my Bank of America data was exposed?
The most direct way is to check whether you received a data breach notification letter from Bank of America, NCB Management, or Infosys McCamish. If you had a past-due Bank of America credit card account before 2023, or if you participated in a Bank of America deferred compensation plan, your data was within the scope of the relevant breaches. You can also check your email address at Have I Been Pwned (haveibeenpwned.com) and contact Bank of America’s customer service to ask about your specific status.

