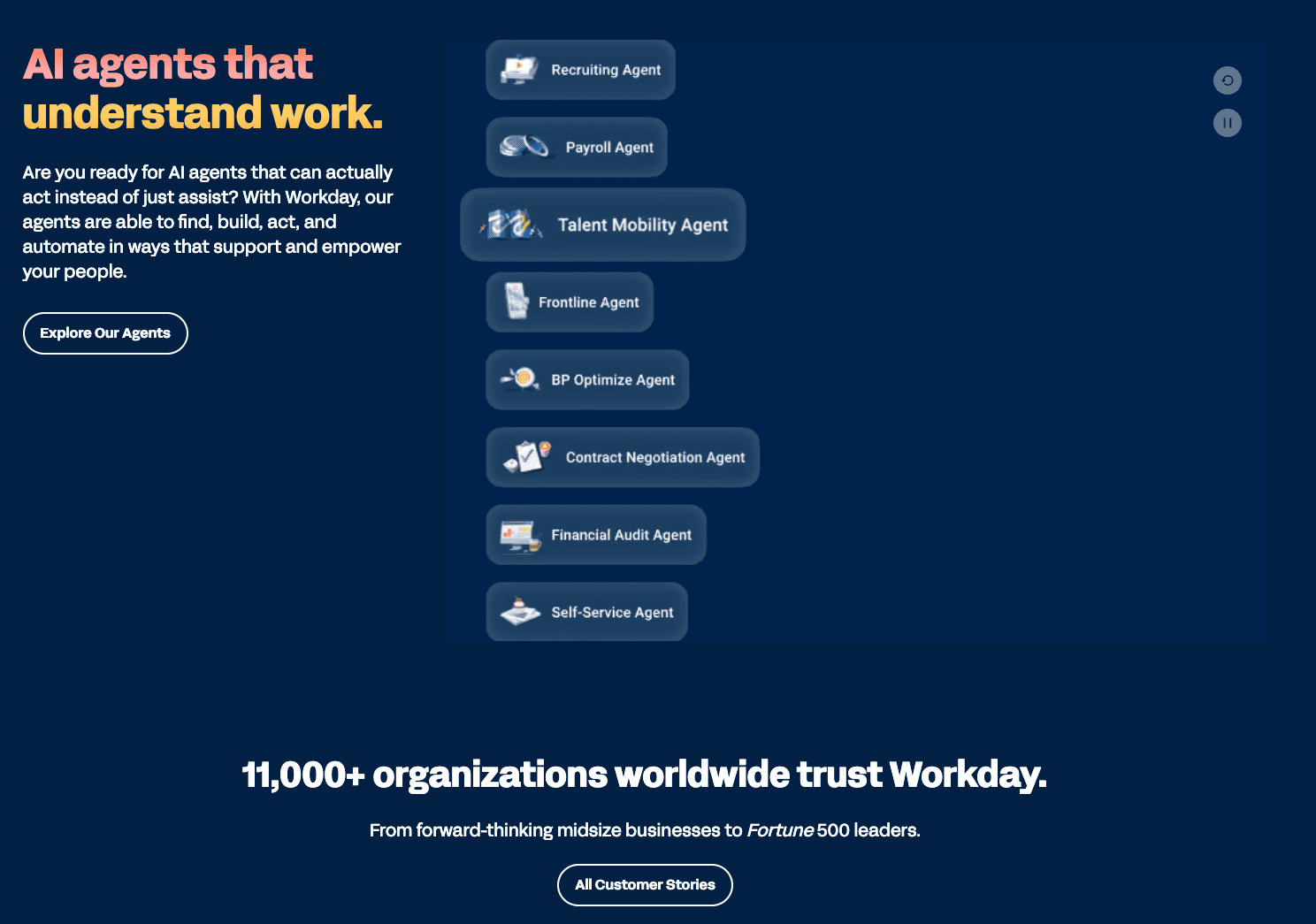
Workday is one of the world’s largest enterprise software platforms, handling HR, payroll, and financial systems for more than 11,000 organizations, including more than 60 percent of Fortune 500 companies. That scale makes it an enormously attractive target for attackers looking to reach thousands of corporate clients and tens of millions of employees through a single point of compromise.
In 2025, Workday was caught up in two distinct but related security incidents, both tied to its use of Salesforce as a customer relationship management platform. The first involved a social engineering attack carried out by a group linked to ShinyHunters in which Workday employees were targeted with voice phishing calls to obtain Salesforce access. The second was a broader supply-chain data breach in which a third-party integration called Salesloft Drift had its OAuth tokens stolen, giving attackers access to the Salesforce data of more than 700 organizations, including Workday.
Neither incident resulted in a breach of Workday’s core HR or payroll systems, and no employee or customer payroll data, Social Security numbers, or financial records within Workday’s own platform were compromised. What was exposed was business contact information and support case data held in Workday’s Salesforce environment. But the incidents are notable for what they reveal about how enterprise software companies are targeted today: not through their own code, but through the trusted third-party tools they connect to.
Incident One: The ShinyHunters Social Engineering Attack (August 2025)
On August 6, 2025, attackers posing as internal HR and IT staff placed phone calls and sent SMS messages to Workday employees. Through these vishing attempts, they tricked employees into sharing credentials or approving a malicious OAuth application that appeared to be a legitimate Salesforce integration. Once the malicious app was approved, attackers obtained an OAuth token granting ongoing API-level access to Workday’s Salesforce CRM environment without requiring the user’s password again.
On August 15, 2025, Workday published a public statement acknowledging that threat actors had accessed data from its third-party CRM platform. The company stated that there was no indication of access to customer tenants or the data within them, and that the compromised information was primarily business contact details.
BleepingComputer reported that the Workday incident was part of a coordinated campaign attributed to ShinyHunters, also tracked as UNC6040, and the associated Scattered Spider group. The same campaign targeted dozens of high-profile organizations including Adidas, Qantas, Google, Cisco, Chanel, Louis Vuitton, Dior, Tiffany & Co., and others, all of which used Salesforce as a CRM platform. The attacks relied entirely on social engineering rather than exploitation of any technical vulnerability in Salesforce itself.
>> Learn More: Phishing Text Messages: A Guide to Smishing
What Was Exposed
Workday confirmed the exposed data consisted primarily of business contact information, including names, email addresses, and phone numbers. The company characterized this as commonly available business contact information. Workday warned, however, that even this category of data could be weaponized by attackers to craft convincing phishing and social engineering campaigns against Workday customers and their employees.
One analysis estimated that the Salesforce CRM data accessed through this campaign included records associated with up to 11,000 corporate customers and 70 million individual user records.
FYI: Workday did not independently confirm the figures. The company’s public communications described the scope as a limited subset of CRM data.1
Incident Two: The Salesloft Drift Supply-Chain Breach (August 2025)
A separate but overlapping incident unfolded through Salesloft’s Drift application, a sales chatbot tool that many organizations, including Workday, had integrated with their Salesforce environments. The root cause of this breach traced back to March 2025, when attackers accessed Salesloft’s GitHub account and downloaded content, establishing workflows that would enable later attacks.
Between August 8 and August 18, 2025, the threat actor tracked as UNC6395 used stolen OAuth tokens from the Drift integration to query and export data from connected Salesforce environments across hundreds of organizations. Because the OAuth tokens represented legitimate, trusted credentials, the attacker could interact with Salesforce APIs without triggering standard authentication alerts. The attacker deliberately deleted bulk query jobs after execution to reduce detection but did not succeed in eliminating log traces.
The scale of this second incident was far larger. Security analysts reported that more than 700 organizations had their Salesforce data accessed through the compromised Drift integration. Among those confirmed affected were Palo Alto Networks, Zscaler, Cloudflare, Proofpoint, Qualys, Tenable, and HackerOne. Salesforce removed the Drift application from its AppExchange on August 27 and disabled all Salesloft integrations on August 29.
What Workday Confirmed About the Drift Incident
Workday became aware of the Salesloft Drift compromise on August 23, 2025, and responded the same day by disconnecting the Drift app, invalidating all associated OAuth tokens, and beginning the removal of related integrations. Workday simultaneously engaged an external forensic firm and began reviewing all vendor relationships that used Drift.
Workday’s investigation confirmed it had been impacted. The attacker’s access was limited to a small subset of Workday’s Salesforce records, including business contact information, basic support case details, tenant attributes such as tenant and data center names, product and service information, training records, certificates, and system event logs. No external files, contracts, or attachments were compromised.
Workday issued a specific warning to customers: support cases submitted through Workday’s CRM may have been accessible to the attacker, and while Workday advises customers not to include credentials or sensitive details in support cases, some may have done so. Workday stated it was proactively reviewing all case data for credentials and would notify affected customers directly if any were found. All customers were urged to rotate credentials previously shared in support cases.
Incogni’s data removal service scans the internet to find your data and sends removal requests to websites to take it down.
The Credential Hunting Dimension
Google’s Threat Intelligence Group (GTIG), which investigated the broader Drift campaign, identified a specific secondary objective beyond the mass collection of contact records. After exfiltrating CRM data, the attacker searched through it looking for embedded secrets: AWS access keys, Snowflake authentication tokens, and plaintext passwords that organizations had inadvertently included in support case notes or CRM records. Cloudflare later disclosed that 104 internal tokens had been exposed through its support case notes during this campaign.2
This dimension is what makes the Drift breach more serious than a simple CRM contact list theft. Credentials stored in support cases can be used to access cloud infrastructure, database systems, and other platforms entirely independent of Workday.
Pro Tip: Any organization that may have included credentials in Workday support cases should treat those credentials as compromised. We recommend rotating them immediately.
The Two 2025 Incidents Compared
| ShinyHunters Social Engineering (August 2025) | Salesloft Drift OAuth Supply Chain (August 2025) | |
|---|---|---|
| Attack method | Voice phishing (vishing); malicious OAuth app approval | Stolen OAuth tokens from Drift integration via earlier GitHub compromise |
| Who did it | ShinyHunters/UNC6040, Scattered Spider | UNC6395 (distinct cluster); ShinyHunters claimed credit without proof |
| Date discovered | August 6, 2025 (breach); August 15 (public disclosure) | August 23, 2025 (Workday notified); active Aug 8-18 |
| Workday’s systems breached? | No — only Salesforce CRM environment affected | No — Drift/Salesforce layer only; no customer tenant access |
| What was exposed | Names, business emails, phone numbers from CRM | Business contacts, support case content, tenant attributes, system event logs |
| Additional risk | Phishing/social engineering using verified contact data | Credentials (AWS keys, passwords) potentially embedded in support cases |
| Scope | 91+ organizations across the broader campaign | 700+ organizations across the Drift campaign |
| Lawsuits | At least 14 lawsuits filed against Salesforce | Ongoing investigations; no Workday-specific suit publicly confirmed |
Why Workday Was a Target
Both incidents exploited the same fundamental characteristic of modern enterprise software: interconnection. Workday uses Salesforce to manage customer relationships. Salesforce integrates with dozens of third-party tools. Each integration creates a trust relationship that attackers can abuse. When ShinyHunters convinced a Workday employee to approve a malicious OAuth app, that single approval gave them access to Workday’s entire Salesforce environment. When the Drift integration was compromised at the Salesloft level, attackers inherited valid tokens for every connected Salesforce org without needing to target Workday specifically at all.
This is the defining pattern of enterprise data theft in 2025: attackers do not need to crack Workday’s security. They identify trusted services that Workday uses, compromise those services or the employees who manage them, and ride existing access rights into the target organization’s data. The attack does not require a software vulnerability and leaves limited traces in conventional security monitoring because the activity looks like normal API usage.
The extortion phase that followed the Salesforce campaign made the stakes explicit. A group claiming affiliation with ShinyHunters demanded a ransom from Salesforce itself, claimed to hold approximately one billion records, and released samples of stolen data from multiple victims when payment was refused. Salesforce refused to pay and stated that its core platform had not been compromised. The FBI seized a BreachForums domain used by ShinyHunters as an extortion site in October 2025.3
What Workday Customers and Users Should Do
Rotate Credentials Shared in Support Cases
This is Workday’s most urgent recommendation and it applies to both incidents. If you or anyone on your team has ever submitted a Workday support case that included a password, API key, AWS access key, Snowflake token, or any other credential, treat that credential as compromised and rotate it immediately. Support case content was within the scope of the Drift breach, and Workday confirmed it is actively scanning case records and will notify customers if sensitive credentials are found. Do not wait for notification.
>> Learn More: The Best Password Managers for Businesses in 2026
Audit Third-Party OAuth Integrations
Both incidents exploited OAuth integrations. Enterprise administrators should audit which third-party applications have OAuth access to their Salesforce and other CRM environments, remove any that are not actively needed, and apply least-privilege principles so that integrations only have the minimum access required. Salesforce administrators can review connected apps in Setup under Connected Apps OAuth Usage.
Require Multi-Factor Authentication
Workday’s own post-incident guidance specifically recommends requiring multi-factor authentication for all users, meaning individuals must complete additional verification steps even after entering a correct password. MFA significantly raises the barrier for social engineering attacks because a stolen password alone is not sufficient to gain access.
Train Employees to Recognize Voice Phishing
The ShinyHunters campaign succeeded by impersonating HR and IT staff over the phone and via SMS. Employees should be trained to treat any unsolicited call or message requesting credential changes, app approvals, or login information as suspicious, regardless of how convincing the caller appears. Legitimate internal IT teams do not request credentials or OAuth approvals by phone.
Never Include Credentials in Support Cases
Going forward, establish and enforce a policy that no passwords, API keys, or access tokens are ever included in support tickets or CRM records. Workday advises this explicitly. The Drift breach demonstrated that support case content is accessible to anyone who obtains API-level access to a connected CRM, and it may remain in case records indefinitely.
Be Alert for Targeted Phishing
Workday explicitly warned that verified business contact information exposed in these incidents, including names, email addresses, and phone numbers, could be used to craft credible phishing and social engineering campaigns against Workday customers. Be skeptical of emails, calls, or messages that reference your Workday account, support cases, or HR data, particularly if they request credentials or direct you to log in through a link.
Pro Tip: Check out our guide on account takeover fraud, which includes tips on how to protect yourself and your business from malicious events.
When Your Work Contact Details Become a Phishing Resource
Business email addresses, direct phone numbers, and job titles rarely feel like sensitive information. They appear on LinkedIn profiles, email signatures, and corporate directories. But when they are verified in bulk through a CRM breach and linked to specific platforms, they become the raw material for highly targeted attacks.
Workday itself warned that the contact data exposed in these incidents could be used to run convincing impersonation campaigns against its customers. The same problem applies more broadly: data brokers and people-search sites compile and sell verified professional contact profiles that make social engineering significantly more credible. A service like Incogni automates the process of requesting removal from those databases, reducing the amount of verified personally identifiable information available to attackers before they ever place a call or send an email.
>> Find Out: How to Protect Yourself From Identity Theft
Frequently Asked Questions
-
Was Workday itself hacked?
No. Workday’s core HR, payroll, and financial systems were not compromised in either incident. Both breaches affected Workday’s Salesforce CRM environment, a separate customer relationship management platform that Workday uses to manage business contacts and support cases. Workday confirmed there was no access to customer tenants or the data within them.
-
What data was exposed in the Workday breaches?
The ShinyHunters social engineering incident primarily exposed business contact information, including names, email addresses, and phone numbers. The Salesloft Drift supply-chain incident exposed a similar set of contact data plus basic support case content, tenant attributes, product and service information, training records, and system event logs. Neither incident resulted in exposure of payroll data, Social Security numbers, financial records, or other sensitive HR data held within Workday’s own platform.
-
Who was responsible for the Workday breach?
The social engineering campaign has been attributed to ShinyHunters, also tracked as UNC6040, a financially motivated extortion group that also worked in tandem with the Scattered Spider gang. The Salesloft Drift supply-chain breach has been attributed to a separate but related cluster tracked as UNC6395 by Google’s Threat Intelligence Group. ShinyHunters later claimed credit for the Drift breach as well, but investigators found no credible evidence supporting that claim.
-
How many Workday customers were affected?
Workday described the scope as a limited subset of its Salesforce data and did not disclose a precise count of affected customers or individuals. One analysis estimated the broader ShinyHunters Salesforce campaign reached data associated with up to 11,000 corporate customers and 70 million individual records. The Drift supply-chain breach affected more than 700 organizations across both campaigns. Workday stated it would directly notify customers if their support case data was found to contain sensitive credentials.
-
Has Workday announced a settlement or class action?
As of the current date, no Workday-specific class action lawsuit or settlement has been publicly announced in connection with these incidents. At least 14 lawsuits were filed against Salesforce in connection with the broader 2025 campaign, and investigations are ongoing. The legal landscape around SaaS supply-chain breaches is evolving, and additional proceedings are possible. Check security.org for updates as this situation develops.

