The 2017 Equifax data breach is one of the most consequential identity theft incidents in American history, and the reason is simple: Equifax is not a company most people interact with directly, but it holds some of the most sensitive financial data on nearly every adult in the United States. When attackers got in, they walked away with Social Security numbers, dates of birth, home addresses, driver’s license numbers, and other personally identifiable information for approximately 147.9 million Americans. That is close to half the country’s population.
What made it worse was how it happened and how long it took Equifax to say anything. A known software vulnerability sat unpatched for months. Attackers moved through Equifax’s systems for 76 days before anyone noticed. And when Equifax finally told the public, it was six weeks after the company had discovered the data breach internally. The fallout included a $700 million settlement, criminal indictments against Chinese military hackers, and a congressional report declaring the breach entirely preventable.
What Happened: A Preventable Failure in Three Acts
The Vulnerability Was Known and Ignored
On March 7, 2017, Apache publicly disclosed a critical vulnerability in its Struts web framework, a software component widely used to build enterprise applications. The flaw, tracked as CVE-2017-5638, allowed an attacker to remotely execute commands on any unpatched system. Apache released a patch the same day.
The Department of Homeland Security issued its own alert the following day, and on March 9 Equifax’s own Global Threat and Vulnerability Management team sent an internal email instructing employees who ran Apache Struts to install the patch within 48 hours. The patch was never applied to Equifax’s Automated Consumer Interview System, the online portal through which consumers submitted dispute documents. On March 10, attackers probed Equifax’s systems and found it still vulnerable.
Compounding the problem was an expired security certificate. A tool Equifax used to scan its own encrypted network traffic for signs of malicious activity had been running with a certificate that expired in May 2016, more than a year before the breach began. Because of that expired certificate, the tool was blind to suspicious encrypted traffic moving through the network.
Attackers Roamed Undetected for 76 Days
The breach itself began in earnest on May 13, 2017, when attackers moved from the initially compromised server into other parts of Equifax’s network. From there, they found plaintext credentials stored on internal systems, which gave them access to databases well beyond the one they had originally entered.
Between May and late July 2017, the attackers queried 51 separate Equifax databases, pulling records in small increments designed to avoid detection and encrypting their communications to obscure their activity. The GAO later concluded they had accessed the personal information of at least 145.5 million U.S. consumers during this period.
Incogni’s data removal service finds your data on broker websites and people search sites, and sends removal requests to take it down on your behalf.
Discovery, Delay, and a Botched Response
Equifax finally detected the intrusion on July 29, 2017, when a security team member renewed the expired network scanning certificate and the tool immediately began flagging suspicious activity. The company took the compromised portal offline the following day and hired cybersecurity firm Mandiant to investigate.
Despite knowing about the breach internally by late July, Equifax did not tell the public until September 7, 2017. The company said the delay was necessary to determine the scope of the intrusion. During those six weeks, three senior Equifax executives sold nearly $1.8 million worth of company stock. The executives were later cleared of insider trading on the grounds that they had no knowledge of the breach at the time of the sales, though one lower-level executive was charged.
When the public disclosure came, the response was widely criticized. The website Equifax set up for consumers to check whether their data was compromised was not hosted on an Equifax domain, had a flawed security implementation, and initially appeared to return random results rather than accurate information. The site also contained terms of service with an arbitration clause that some attorneys warned could be read to bind users to arbitration for claims related to the breach.
Who Was Responsible
On February 10, 2020, the U.S. Department of Justice indicted four members of China’s People’s Liberation Army for the Equifax hack: Wu Zhiyong, Wang Qian, Xu Ke, and Liu Lei, all from PLA Unit 54398.1 The Chinese government denied the accusations.
Investigators believe the attack was part of a broader Chinese intelligence operation rather than a financially motivated hack. Notably, the stolen data never appeared on dark web markets, which is consistent with state-sponsored intelligence gathering rather than criminal resale. Security analysts have theorized that, combined with data from other major Chinese-attributed breaches such as the 2015 Office of Personnel Management hack, the Equifax records could be used to build detailed dossiers on U.S. government employees, intelligence officers, and military personnel.
FYI: The House Committee on Oversight and Government Reform’s investigation concluded in December 2018 and found the breach was preventable. Equifax’s failure to patch the known vulnerability and its inadequate security posture had made the attack possible.
What Was Stolen
| Data Type | Number of Records | Population Affected |
|---|---|---|
| Names, addresses, dates of birth, SSNs, driver’s license numbers | ~147.9 million | U.S. residents |
| Credit card numbers | ~209,000 | U.S. consumers (primarily those who paid Equifax directly) |
| Dispute documents with personal identifiers | ~182,000 | U.S. consumers |
| Personal records (names, partial financial data) | ~15.2 million | U.K. residents |
| Personal records | ~19,000 | Canadian residents |
The core data exposed for most affected Americans, including names, Social Security numbers, dates of birth, and home addresses, is precisely the combination of identifiers used to open new financial accounts, file fraudulent tax returns, and pass identity verification checks. Unlike a compromised password, this information cannot be changed, which is what made the Equifax breach so durably damaging.
>> Find Out: How to Protect Yourself From Identity Theft
The $700 Million Settlement
In July 2019, Equifax reached a global settlement with the FTC, the Consumer Financial Protection Bureau, and the attorneys general of all 50 states and territories. The total value of the settlement was up to $700 million, making it one of the largest data breach settlements in U.S. history. Of that amount, up to $425 million was designated as a consumer fund, with $175 million going to the states and $100 million as a civil penalty to the CFPB.
Affected consumers who filed valid claims were eligible for
- Free credit monitoring for up to 10 years through all three major bureaus;
- Cash reimbursement of up to $20,000 for documented out-of-pocket losses;
- Compensation for up to 20 hours spent dealing with the breach at $25 per hour;
- And a $125 cash payment if they already had credit monitoring services in place and chose not to enroll in the free monitoring offered
The claims deadline passed on January 22, 2024. Payments to claimants have been distributed in waves, including additional funds added to prepaid cards in August 2025. Free identity restoration services remain available to affected consumers through January 2029, even for those who never filed a formal claim.
Pro Tip: We always recommend choosing an identity theft protection service offering three-bureau credit monitoring, just in case one misses some suspicious activity. Check out our guide on the best credit protection services to find the best one for you.
What You Can Do Now
Check Whether You Were Affected
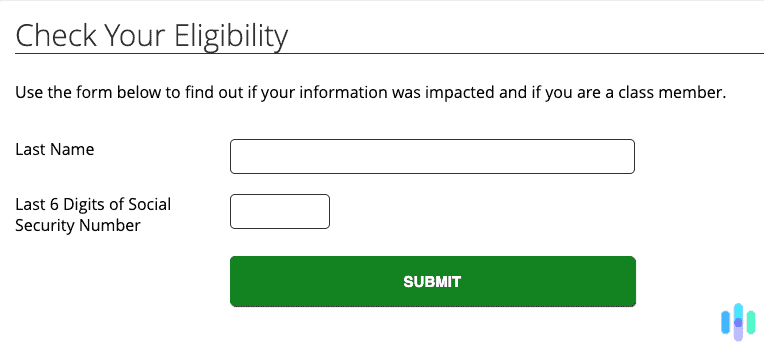
The official settlement website at equifaxbreachsettlement.com includes a look-up tool where you can check whether your personal information was included in the breach. You will be asked to provide your last name and the last six digits of your Social Security number. This is the official tool run by the settlement administrator, not by Equifax itself.
Access Free Identity Restoration Services
Even if you never filed a settlement claim, you are still entitled to free identity theft recovery help through January 2029 if your data was affected. The FTC’s settlement page has a phone number and engagement number to connect you with those services once you confirm your eligibility through the look-up tool.
>> Check Out: The Best Free Identity Theft Protection Services
Place a Credit Freeze at All Three Bureaus
Because Social Security numbers and dates of birth were exposed for nearly 148 million people, a credit freeze is the strongest available protection against new accounts being opened in your name. You need to place freezes separately at Equifax, Experian, and TransUnion. All three are free. The Equifax settlement also entitled affected consumers to up to seven free Equifax credit reports per year through 2026.
Pro Tip: The best identity theft protection services let you freeze all three credit bureaus at once, with just a press of a button. It saves you having to make three separate inquiries.
Monitor Your Credit Reports and Tax Filings
Pull your free credit reports from AnnualCreditReport.com and review them for accounts, inquiries, or changes you do not recognize. Because SSNs were part of the stolen data, fraudulent tax return filing is also a realistic risk. If the IRS sends you a notice about a return you did not file, respond immediately and report it to the FTC at IdentityTheft.gov.
Watch Out for Scams Related to the Breach
The FTC has warned that scammers have used the Equifax breach as cover to approach affected consumers, posing as settlement administrators or offering to help people file claims. The FTC is clear that no one should ever have to pay to file a claim or receive settlement benefits. All legitimate communications about the settlement come from the equifaxbreachsettlement.com domain.
>> Learn More: What Is a Scam, and How Can You Avoid One?
The Longer-Term Risk of Exposed Permanent Data
Most breaches involve credentials that can be changed. The Equifax breach is different because the most sensitive data it exposed, Social Security numbers, dates of birth, and home addresses, is essentially permanent. That means the risk does not expire. Years after the breach, those records are still useful to fraudsters looking to open accounts, file fake tax returns, or pass identity verification checks.
Reducing your overall exposure online is one way to make that stolen data somewhat less useful. A data removal service, such as Incogni, can remove your personal information from data broker sites that aggregate and sell records, making it harder for anyone working from a stolen dataset to build a complete profile on you. It is not a fix for the breach itself, but as a long-term privacy measure it is worth considering, especially given how durable the risk from this particular incident is.
The Bottom Line
The Equifax breach stands apart from most data incidents because of what was taken and who holds it. Social Security numbers and dates of birth for nearly half of all American adults are not credentials you can reset. They are permanent identifiers, and a foreign government is believed to have them. The immediate legal consequences were significant: a $700 million settlement, federal indictments, and years of regulatory oversight. But the real long-term consequence is the ongoing identity theft risk carried by tens of millions of people who had no relationship with Equifax and no say in how their data was stored.
If you have not already checked the settlement site, placed credit freezes, and set up monitoring for your credit reports and tax filings, those steps are still worth taking. The identity restoration services through the settlement are still available until January 2029.
Frequently Asked Questions
-
How do I know if I was affected by the Equifax data breach?
The official settlement website at equifaxbreachsettlement.com has a look-up tool where you can check whether your information was included in the breach. You will need your last name and the last six digits of your Social Security number. Given that the breach affected approximately 147.9 million Americans, roughly 40 percent of the U.S. adult population, the probability that your data was exposed is meaningful even if you have never been a direct Equifax customer.
-
Who hacked Equifax?
In February 2020, the U.S. Department of Justice indicted four members of China’s People’s Liberation Army, specifically Wu Zhiyong, Wang Qian, Xu Ke, and Liu Lei from PLA Unit 54398, for carrying out the attack.The Chinese government denied responsibility. The attackers were never arrested, as China does not extradite its citizens on cybercrime charges brought by foreign governments. The stolen data has never surfaced on criminal marketplaces, which analysts consider consistent with state-sponsored intelligence gathering rather than financially motivated crime.
-
How much did Equifax pay for the data breach?
Equifax agreed to a settlement valued at up to $700 million. The consumer fund portion was up to $425 million, with $175 million going to state governments and $100 million paid as a civil penalty to the CFPB. The total cost of the breach to Equifax, including mandatory security investments, legal fees, and settlements, has been estimated at approximately $1.38 billion.
-
Can I still get money from the Equifax settlement?
The claims deadline for most benefits was January 22, 2024, so the window to file for cash reimbursement has closed. However, free identity restoration services remain available to affected consumers through January 2029, regardless of whether a claim was ever filed. If you received prepaid card notification emails from distribution@EquifaxBreachSettlement.com, those are legitimate and funds on those cards remain accessible.
-
Why was the Equifax breach so serious compared to other data breaches?
Most large breaches expose credentials that can be changed, like passwords or account numbers. Equifax exposed permanent identifiers: Social Security numbers, dates of birth, and home addresses for nearly half of all American adults. Those cannot be reset, which means the identity theft risk from this breach does not diminish over time the way it might from a stolen password. The fact that many of those affected had no direct relationship with Equifax, and that most never chose to share their data with the company, made the breach feel particularly unfair to the millions caught up in it.