Steam, Valve’s PC gaming platform, has more than 130 million registered accounts and stores payment information, game libraries, and personal details for a massive global user base. It is, by any measure, an attractive target for cybercriminals. Over the years it has been the subject of genuine security incidents and viral but inaccurate data breach claims. Understanding which is which matters for knowing what actions, if any, you actually need to take.
Two incidents have generated the most concern: a real 2011 database breach that compromised user credentials and encrypted financial data, and a widely reported but largely misunderstood 2025 incident involving leaked SMS one-time codes that Valve confirmed did not constitute a breach of its systems. Here is a clear account of both.
>> Learn More: How to Stop Spam Texts
The 2011 Steam Database Breach: A Real Incident
What Happened
On November 6, 2011, attackers defaced the Steam community forums. Valve’s investigation into that defacement revealed the intrusion extended further than the forums alone. Attackers had used credentials obtained from the forum breach to access a Steam database containing sensitive user account information.
Valve CEO Gabe Newell disclosed the breach on November 10, 2011. He confirmed that attackers had obtained access to a database containing usernames, hashed and salted passwords, game purchases, email addresses, billing addresses, and encrypted credit card information. At the time, Steam had approximately 35 million active user accounts.
The breach deepened in early 2012 when Valve disclosed a further development. A follow-up email from Newell to Steam users revealed that it was probable the attackers had also downloaded a backup file containing Steam transaction history from 2004 to 2008. That backup included Steam usernames, encrypted billing addresses, and encrypted credit card information, though it did not include account passwords.
Incogni’s data removal service finds your personal information online and sends removal requests to take it down.
What Was Exposed
Valve emphasized that the passwords were hashed and salted, which means they were stored using a one-way encryption method that makes them significantly harder to crack than plaintext passwords. The credit card data was also encrypted. Valve said it had no evidence at the time that encrypted credit card numbers had been decrypted and misused, or that Steam accounts had been directly compromised using the stolen information.
A possible suspect was identified in early 2012 when a conference call between the FBI and UK Metropolitan Police, later leaked online, referenced a 15-year-old hacker known as TehWongZ who had allegedly claimed credit for the Steam breach and stated he had downloaded 32,000 Steam usernames, passwords, and credit card details.1
How Valve Responded
Valve took the Steam forums offline during the investigation and required all forum users to change their passwords before regaining access. The company urged Steam account holders to change their account passwords as well, particularly if they had used the same password for both their Steam account and the Steam forums. Valve also recommended that users monitor their credit card statements and remove payment information from their Valve accounts if they were concerned.
In response to the breach, Valve accelerated the rollout of Steam Guard, its account security feature, and subsequently made two-factor authentication a stronger part of its security infrastructure. It also began requiring game developers on Steam to register with phone numbers for SMS-based verification.
FYI: Steam users using the same password for Steam account and Steam forums isn’t surprising. Our research into password habits revealed that two out of three people use the same passwords across multiple accounts.
The 2025 SMS Leak: What Was Really Exposed
How the Story Started
In early May 2025, cybersecurity firm Underdark AI published a LinkedIn post claiming a massive Steam data breach. The post alleged that a threat actor using the alias “Machine1337” was selling a database containing records from 89 million Steam accounts on a dark web forum for $5,000. The story spread rapidly across gaming communities and tech news outlets, with initial reporting speculating that Twilio, a provider of SMS-based authentication services, might be the source.
What the Data Actually Contained
Valve examined samples of the leaked data and responded publicly within a day. In a statement, Valve confirmed that the incident was not a breach of Steam’s systems. The leaked data consisted of older SMS text messages containing one-time authentication codes, along with the phone numbers they were sent to. Those one-time codes were only valid for 15-minute windows and had long since expired by the time the data appeared for sale.
Critically, the leaked data did not associate phone numbers with specific Steam accounts. It did not contain account passwords, payment card information, email addresses, usernames, or any other data that could be used to access a Steam account.
Both Valve and Twilio denied that their systems had been breached. Valve’s assessment was that the SMS messages had been intercepted from somewhere in the broader SMS delivery chain, which involves multiple unencrypted intermediary providers. SMS messages are transmitted without encryption as they route between carriers and service providers, creating exposure points that are not controlled by Valve.
Valve stated plainly that Steam users did not need to change their passwords or phone numbers as a result of this event, and that the exposed codes could not be used to access accounts.
Why the Story Spread So Quickly
Several factors contributed to the alarm. The number 89 million is genuinely large. The initial reporting mentioned Twilio, a recognizable name in authentication services. And the $5,000 asking price, while low for such a supposed dataset, was widely misread as evidence of seriousness rather than the more likely indicator that the data had limited practical value.
Security analysts who examined samples of the data confirmed that while the records appeared to be authentic SMS messages, they lacked the elements needed to access accounts. The one-time codes had expired. Phone numbers were not linked to account identities. No credentials, payment data, or personal identifying information beyond phone numbers were present.
The Two Incidents Compared
| Vendor Breached | Data Exposed | |
|---|---|---|
| Was Steam’s system breached? | Yes | No — Valve confirmed Steam was not compromised |
| What was exposed | Usernames, hashed passwords, email addresses, billing addresses, encrypted credit card data, game purchase history | Expired one-time SMS codes and phone numbers only; no account association |
| Accounts at risk of takeover? | Potentially, if users reused passwords | No — expired codes cannot unlock accounts |
| Payment data exposed? | Encrypted credit card data in backup file | No |
| Action required by users? | Yes — password change, monitor credit card statements | No required action, per Valve; general hygiene recommended |
The Ongoing Threat to Steam Accounts: What Actually Happens
While the 2025 story was not the catastrophic breach it was initially portrayed as, Steam accounts are compromised regularly through other means that have nothing to do with Valve’s systems. Understanding the actual threat landscape is more useful than focusing on mischaracterized incidents.
The most common ways Steam accounts are hijacked include credential stuffing, where attackers try username and password combinations leaked from other breached services and find users who reuse the same credentials; phishing emails and fake Steam login pages designed to harvest account credentials; malware that captures Steam session tokens and bypasses authentication entirely; and social engineering through Steam’s trading and chat features where attackers impersonate friends or offer fraudulent deals.
None of these require Valve’s systems to be compromised. They exploit user behavior and the value of Steam libraries, which can contain games worth hundreds or thousands of dollars and trading items with real monetary value.
>> Learn More: The Ultimate Phishing Protection Guide for 2026
How to Keep Your Steam Account Secure
Enable Steam Guard Mobile Authenticator
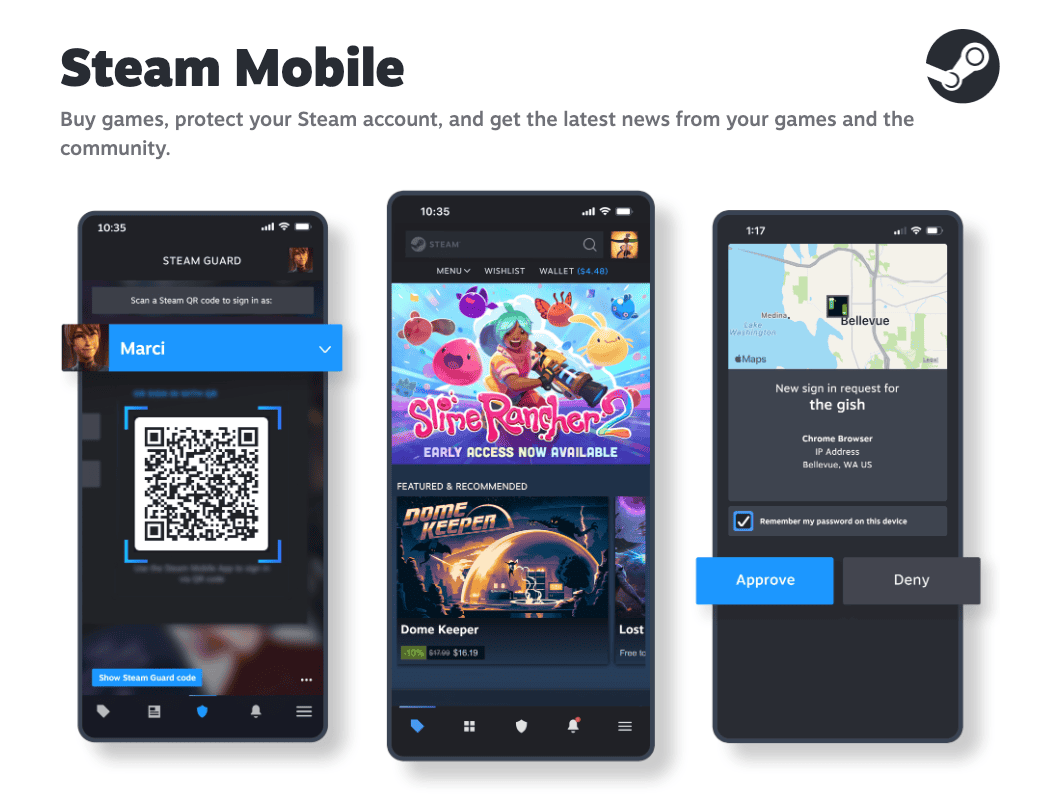
Valve’s own recommendation after the 2025 SMS incident was to use the Steam Mobile Authenticator rather than SMS-based two-factor authentication. The Mobile Authenticator generates time-based codes locally on your device and does not rely on SMS, eliminating the supply-chain vulnerability that made the 2025 incident possible. It also provides Steam Guard protections that alert you to new device logins and require additional confirmation for trades and market transactions.
Use a Unique, Strong Password
Given that credential stuffing from other breached services is one of the most common ways Steam accounts are hijacked, using a password for Steam that you do not use anywhere else is one of the most effective protections available. A password manager can generate and store a strong, unique credential so you do not have to remember it.
Pro Tip: Before you lock in a new password, use your password strength checker tool to ensure it’s safe and tough to crack.
Review Authorized Devices
Steam allows you to view and manage all devices currently authorized to access your account. Valve specifically recommended checking this page after the 2025 incident. You can review your authorized devices at store.steampowered.com/account/authorizeddevices. Remove any devices you do not recognize.
Treat Unexpected Security Messages with Suspicion
Valve’s statement after the 2025 incident explicitly noted that it is a good reminder to treat any account security messages you have not explicitly requested as suspicious. If you receive an SMS code or email prompt you did not initiate, do not click any links or enter the code anywhere. Instead, go directly to Steam’s website and check your account security status there.
>> Find Out: What Can Someone Do With Your Phone Number?
Check Have I Been Pwned
Entering your email address at Have I Been Pwned (haveibeenpwned.com) can tell you whether it appears in any known breach datasets from other services or on the dark web. If your email has appeared elsewhere and you use the same password on Steam as that breached service, your account could be at risk through credential stuffing even if Steam itself was never compromised.
Be Skeptical of Phishing Attempts
Fake Steam login pages, phishing emails claiming your account has been compromised, and scam trade offers through the Steam chat or community are persistent threats. Always access Steam directly through your browser or the Steam client rather than following links in emails or chat messages. Valve will never ask for your password through chat or email.
>> Find Out: How to Prevent Being Scammed Online
Gaming Accounts as an Overlooked Privacy Risk
Most people think carefully about protecting their bank account or email. Fewer think as carefully about their gaming accounts, even though those accounts can hold hundreds of dollars in digital goods, linked payment methods, and years of personal activity data. When those accounts are compromised, the consequences are often both financially significant and difficult to reverse.
Part of good digital hygiene is reducing how much of your personal information is available through data brokers and aggregators, which makes social engineering and phishing attacks harder to execute convincingly. A service like Incogni automates the submission of removal requests to those databases, limiting how much personal context a scammer can find about you before crafting a targeted attack. It is one layer of a broader security posture, and it works alongside the direct account protections above.
The Bottom Line
Steam has been involved in one genuine data breach, in 2011, when attackers accessed databases containing hashed passwords, email addresses, and encrypted financial data for millions of users. That incident prompted Valve to significantly strengthen its security infrastructure, including the rollout of Steam Guard and stronger two-factor authentication options.
The 2025 incident that generated widespread alarm was not a breach of Steam’s systems. Expired SMS one-time codes and phone numbers with no account linkage were found in a dataset offered for sale, most likely intercepted somewhere in the SMS delivery chain. Valve confirmed that no action was required and that the data could not be used to compromise accounts.
The real ongoing threat to Steam accounts comes not from headline-grabbing breach claims but from credential stuffing, phishing, and account hijacking methods that are entirely avoidable with strong, unique passwords and the Steam Mobile Authenticator.
Frequently Asked Questions
-
Was Steam hacked in 2025?
No. Valve confirmed that the May 2025 incident was not a breach of Steam’s systems. A dataset of older SMS one-time codes and phone numbers appeared for sale on a dark web forum, but those codes had already expired and could not be used to access accounts. Neither Valve nor Twilio, which was initially suspected as the source, had their systems compromised. Valve stated that Steam users did not need to change their passwords or phone numbers as a result.
-
Has Steam ever had a real data breach?
Yes. In November 2011, Valve’s Steam forums were defaced and attackers used credentials from the forum hack to access a broader Steam database containing usernames, hashed passwords, email addresses, billing addresses, and encrypted credit card information. A subsequent disclosure in early 2012 revealed that a backup file with transaction data from 2004 to 2008 had likely also been stolen. Valve said there was no evidence of fraudulent use of the encrypted financial data.
-
What was in the 89 million Steam records offered for sale in 2025?
Valve examined the data and found it consisted of older SMS text messages that had been sent to Steam users containing one-time authentication codes, along with the phone numbers those messages were sent to. The codes were only valid for 15-minute windows and had long expired. The phone numbers were not linked to Steam account identities, and no passwords, email addresses, payment data, or other personal information was included.
-
How do most Steam account hijackings actually happen?
The most common methods are credential stuffing, using passwords stolen from other breached services to log into Steam accounts where users reused the same credentials; phishing, where users are tricked into entering their Steam login on fake websites; and malware that captures Steam session tokens from infected computers, bypassing two-factor authentication entirely. None of these require a breach of Valve’s systems.
-
What is the most important thing I can do to protect my Steam account?
Enable the Steam Mobile Authenticator rather than relying on SMS-based two-factor authentication. The Mobile Authenticator generates codes locally on your device and is not subject to the SMS supply-chain vulnerabilities that made the 2025 incident possible. Pair it with a unique password you do not use on any other service, and regularly review your authorized devices at store.steampowered.com/account/authorizeddevices.

