No major U.S. carrier has experienced as many significant data breaches in recent memory as T-Mobile. Since 2015, the company has disclosed a string of incidents that, taken together, have exposed the personal information of hundreds of millions of current, former, and prospective customers. Names, Social Security numbers, driver’s license numbers, account PINs, call records, billing addresses — over the years, attackers have gotten their hands on nearly every category of data T-Mobile holds.
If you are or were a T-Mobile customer at any point in the last decade, the odds are reasonable that your personally identifiable information was caught up in at least one of these incidents. Here is a clear-eyed look at what happened, who was responsible, and what the legal fallout has been, along with practical steps to avoid identity theft you can take right now.
A Pattern of Breaches: The Full Timeline
T-Mobile’s breach history is extensive enough that a chronological overview is the most useful starting point. The incidents vary considerably in scale, method, and the type of data exposed.
2015: The Experian Third-Party Breach
T-Mobile’s breach history effectively begins in 2015, though the company was not directly hacked. Experian, which T-Mobile used to conduct credit checks on customers applying for device financing or new accounts, suffered a breach that exposed data on approximately 15 million T-Mobile customers. The compromised information included names, addresses, dates of birth, Social Security numbers, driver’s license numbers, and passport numbers. All affected customers were notified by Experian and offered credit monitoring services.
>> Check Out: The Best Credit Protection Services of 2026
2018: Two Million Customer Records Exposed
In August 2018, T-Mobile disclosed that an attacker had accessed the records of approximately 2 million customers. The exposed data included names, billing ZIP codes, phone numbers, email addresses, account numbers, and account types. T-Mobile said it detected and stopped the breach at the time of discovery, and that encrypted passwords were also among the compromised data.
Did You Know: The average person has 168 passwords for personal accounts.1 Our research found that more than two in three people use the same credentials across multiple accounts, which is a big security risk.
2019 and 2020: Smaller but Repeated Incidents
In November 2019, T-Mobile disclosed unauthorized access to the account information of an undisclosed number of prepaid customers. In March 2020, a breach of an email vendor exposed some customers’ personal and financial information. Later that same year, in December 2020, another incident exposed customers’ proprietary network information, including phone numbers and call records.
Incogni’s data removal service scans thousands of databases and sends automated removal requests to have your personal information, including phone numbers, removed from websites on your behalf.
2021: The Largest and Most Damaging Breach
The 2021 breach is by far the most consequential in T-Mobile’s history. In August of that year, the company confirmed that attackers had gained unauthorized access to its internal systems and extracted data on approximately 76.6 million individuals, including current customers, former customers, and people who had simply applied for credit with T-Mobile.
The exposed data was deeply sensitive. For around 7.8 million current postpaid customers, it included names, dates of birth, Social Security numbers, and driver’s license or ID numbers. For the roughly 40 million former and prospective customers in the dataset, SSNs and driver’s license data were also included. An additional 850,000 prepaid customers had their names, phone numbers, and account PINs exposed.
A hacker going by the alias John Erin Binns later claimed responsibility for the attack in an interview with The Wall Street Journal. He said he had accessed T-Mobile’s systems through an unprotected GPRS gateway, using brute force to work through credentials until gaining entry. Binns stated his motivation was to retaliate against the U.S. government.2 A federal indictment was unsealed against Binns in 2024; he was subsequently arrested in Turkey, where extradition proceedings are ongoing.
2023: An API Breach Hits 37 Million Customers
T-Mobile’s most recent large-scale breach was discovered on January 5, 2023, when the company identified malicious activity tied to a vulnerable API endpoint. The attacker had first accessed data through that API beginning around November 25, 2022, meaning the breach went undetected for roughly six weeks.
Approximately 37 million customers were affected. The exposed data included names, billing addresses, phone numbers, email addresses, dates of birth, account numbers, and plan details. T-Mobile said no Social Security numbers, driver’s license numbers, passwords, PINs, or financial information were compromised in this particular incident. The company contained the breach within 24 hours of detection and began notifying affected customers.
FYI: A smaller but more targeted breach also occurred in April 2023, affecting only 836 customers. That incident was more alarming in terms of data type, as the exposed information included Social Security numbers, government ID data, and T-Mobile account PINs.
Breach Summary at a Glance
| Year | Customers Affected | Data Exposed | How It Happened |
|---|---|---|---|
| 2015 | ~15 million | SSNs, DOBs, driver’s licenses, passport numbers | Third-party breach at Experian |
| 2018 | ~2 million | Names, phone numbers, emails, account numbers | Direct network intrusion |
| 2021 | ~76.6 million | SSNs, DOBs, driver’s licenses, account PINs | Brute force via unprotected GPRS gateway |
| 2023 (Jan.) | ~37 million | Names, addresses, phone numbers, emails, DOBs | Vulnerable API endpoint |
| 2023 (Apr.) | 836 | SSNs, government IDs, account PINs | Targeted sales application access |
>> Check Out: The Best Free Identity Theft Protection Services
Lawsuits, Fines, and the $350 Million Settlement
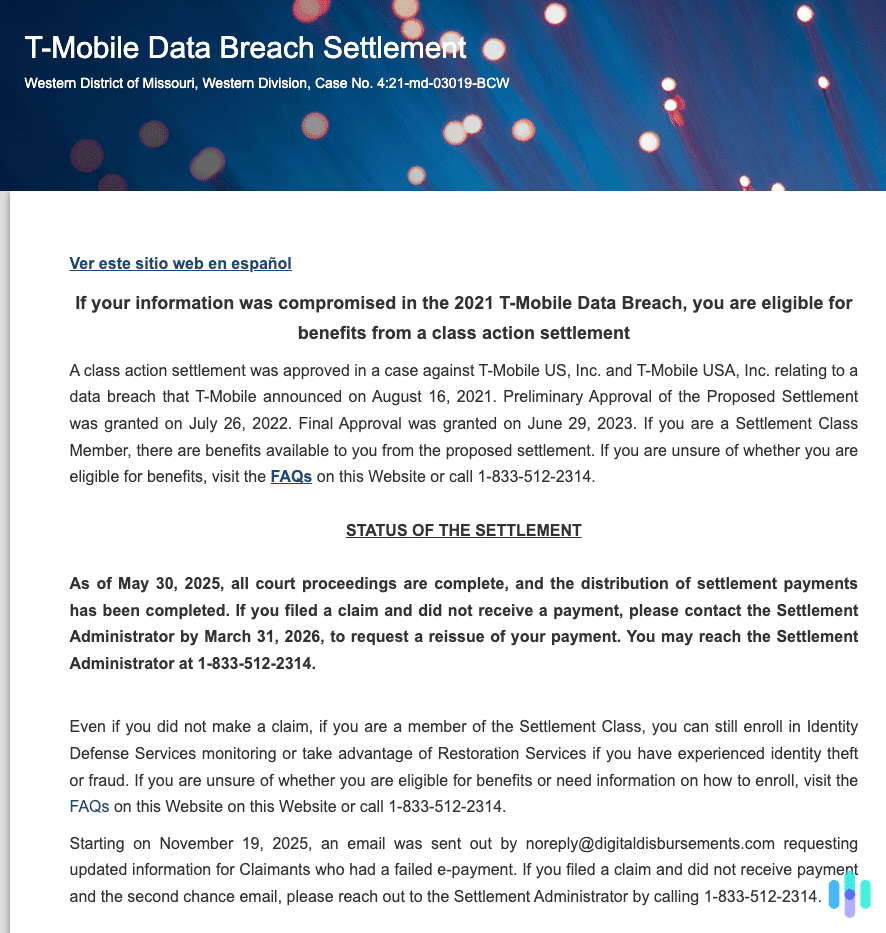
The 2021 breach triggered significant legal consequences. T-Mobile faced multiple class action lawsuits alleging that the company had failed to adequately protect customer data. In July 2022, T-Mobile agreed to pay $350 million to settle those class action claims, one of the largest data breach settlements in U.S. history at the time. As part of that agreement, the company also committed to spending $150 million on data security and cybersecurity investments.
In September 2024, the Federal Communications Commission announced a separate settlement with T-Mobile to resolve its own investigations into the 2021, 2022, and 2023 breaches. T-Mobile agreed to pay a $15.75 million civil penalty to the U.S. Treasury and invest an additional $15.75 million in cybersecurity improvements over the following two years, for a combined $31.5 million.
As part of those required improvements, T-Mobile committed to adopting a zero trust architecture, deploying phishing-resistant multi-factor authentication across its internal network, implementing data minimization practices, and submitting to independent third-party assessments of its information security. The FCC described these requirements as “long overdue” and intended to set a model for the broader mobile telecommunications industry.
>> Find Out: How to Remove Your Information From the Internet
What Can You Do to Check If You Were Affected?
Check Have I Been Pwned
Entering your email address at Have I Been Pwned (haveibeenpwned.com) is the fastest way to check whether your information appears in any indexed breach datasets, including those from the T-Mobile incidents. If your address appears, take it as a signal to review your account security across any services where you have used that email.
Pro Tip: Some of the best password managers we’ve tested include data breach and dark web monitoring. This saves you having to check Have I Been Pwned regularly to see if your credentials are safe.
Check for Notifications from T-Mobile
T-Mobile committed to notifying affected customers after both the 2021 and 2023 breaches. For the 2021 breach, notifications went out by late August 2021. For the 2023 API breach, the company began contacting affected customers shortly after its January 2023 disclosure. If you did not receive a notice but were a T-Mobile customer during any of the affected periods, you can contact T-Mobile directly through its official customer support channels to ask about your exposure.
Place a Credit Freeze
Because the 2021 breach exposed Social Security numbers for tens of millions of people, a credit freeze is one of the most protective steps you can take. It prevents new credit from being opened in your name without your knowledge, and it is free to place and lift at all three major bureaus: Equifax, Experian, and TransUnion.
Monitor Your Credit Reports
Pull your free annual credit reports from AnnualCreditReport.com and review them for accounts or inquiries you do not recognize. Given how many years T-Mobile breach data has been in circulation, this is worth doing even if you think your information was not involved.
Watch for SIM Swap Attempts
T-Mobile has experienced SIM swapping incidents where attackers convinced customer service representatives to transfer a victim’s phone number to a SIM card they controlled. If your phone suddenly loses service for no apparent reason, contact T-Mobile immediately. You should also add account takeover protection features to your T-Mobile account if you are a current customer, as the company now offers these to all postpaid users.
>> Find Out: What Can Someone Do With Your Phone Number?
Update Your Account PIN and Password
T-Mobile proactively reset PINs for some customers after the 2021 breach, but it is worth setting a new, unique PIN yourself regardless. If you reuse your T-Mobile credentials on other accounts, change those too.
Protecting Your Data After A Breach
One of the more troubling aspects of T-Mobile’s breach history is just how long the data keeps resurfacing. Records from the 2021 breach were still appearing in new contexts years later. That pattern reflects a broader reality about stolen personal data: it does not go away. It gets bought, sold, combined with data from other breaches, and used in ways that may only become apparent years after the original incident.
That is part of why managing your broader data footprint matters even if the immediate breach response is over. A service like Incogni can help reduce the amount of your personal information that remains accessible through data broker databases, which are often the conduit through which old breach data gets aggregated and resold. It will not erase data that has already been stolen, but it can limit how easily that information is findable by people looking to build a profile on you.
The Bottom Line
T-Mobile’s data breach history is a case study in what happens when a large company repeatedly fails to address foundational security weaknesses. From the 2015 Experian incident through the 2023 API breach, attackers have extracted an enormous range of sensitive data from T-Mobile systems and the third parties it works with. The legal consequences have been significant: over $380 million in settlements and fines across multiple proceedings, plus federally mandated security reforms.
If you have ever been a T-Mobile customer, treating some of your personal data as potentially compromised is the reasonable starting position. Checking Have I Been Pwned, placing a credit freeze, and keeping a close eye on your credit reports are the three steps most likely to catch any downstream consequences before they become serious problems.
Frequently Asked Questions
-
How many times has T-Mobile been hacked?
T-Mobile has disclosed at least eight significant data security incidents since 2015, ranging from the massive 2021 breach affecting 76.6 million people to smaller but still serious incidents in 2018, 2019, 2020, and 2023. The FCC’s 2024 settlement explicitly covered breaches in 2021, 2022, and 2023 alone. The repeated pattern of incidents across different years and methods of attack is part of what led the FCC to characterize its required cybersecurity reforms as long overdue.
-
Was my Social Security number exposed in the T-Mobile data breach?
It depends on which breach and what your relationship to T-Mobile was at the time. The 2021 breach exposed Social Security numbers for approximately 7.8 million current postpaid customers and roughly 40 million former and prospective customers who had applied for credit. The 2023 API breach, by contrast, did not include SSNs. If you were a postpaid customer or had applied for credit with T-Mobile at any point before 2021, checking Have I Been Pwned and monitoring your credit reports is especially important.
-
Did T-Mobile pay a settlement for the data breaches?
Yes. T-Mobile paid $350 million in 2022 to settle class action lawsuits stemming from the 2021 breach, which was one of the largest data breach settlements in U.S. history at the time. In September 2024, the FCC announced an additional $31.5 million settlement covering the 2021, 2022, and 2023 breaches, split between a civil penalty and mandatory cybersecurity investment.
-
What is T-Mobile doing to prevent future breaches?
As part of its FCC settlement, T-Mobile is required to implement a zero trust architecture, deploy phishing-resistant multi-factor authentication across its internal network, adopt data minimization practices, maintain a critical asset inventory, and undergo independent third-party security assessments on an ongoing basis. The company has also made additional voluntary investments in network monitoring and vulnerability management following the 2021 breach.
-
Can I still file a claim for the T-Mobile data breach settlement?
The claims window for the $350 million class action settlement has closed. The settlement was preliminarily approved in 2022 and administered through a dedicated settlement website. If you believe you were affected and missed the claims deadline, consulting a consumer protection attorney is the most practical next step, as individual legal options outside the class settlement may still exist depending on your circumstances and jurisdiction.

