The Tea app launched in 2023 with a clear pitch as a secure, anonymous space where women could share information about men they had dated or encountered online, flag red flags, and warn others about potentially dangerous behavior. To join, users had to submit a selfie and a government-issued ID for identity verification. The promise was privacy and safety. Then, in July 2025, that promise collapsed.
Within a single week, the app experienced two distinct security failures that exposed the personally identifiable data of users who had signed up before February 2024. Government IDs and selfies were left in an unprotected cloud storage bucket and then leaked on 4chan. Days later, a security researcher discovered a separate, accessible database containing over one million private messages. The very platform designed to protect women from predatory men had left their most sensitive information exposed to anyone who went looking.
Here’s the full tea.
What Happened: Two Breaches in One Week
The Exposed Firebase Storage Bucket (July 25, 2025)
On the morning of July 25, 2025, an anonymous post appeared on 4chan claiming that Tea was storing user identity verification images in an unsecured Firebase storage bucket, a cloud folder managed through Google’s Firebase platform. The post included a link that reportedly allowed anyone to download the stored files.
Tea identified the data breach the same day, at 6:44 AM PST, and engaged external cybersecurity experts. The company confirmed that its legacy data storage system had been compromised and that the exposed dataset covered users who registered before February 2024, when Tea had migrated to more secure infrastructure. The old system, however, had not been properly secured or wiped.
The exposed archive contained approximately 72,000 user images in total. This included roughly 13,000 selfies and government-issued ID photos, such as driver’s licenses and passports, submitted as part of the verification process, and about 59,000 images shared through user posts, comments, and direct messages within the app.
A particularly serious element of the leak was that some photos retained metadata, including GPS coordinates embedded in the image files. At least one person reportedly used that metadata to create a map plotting the approximate locations of affected users. Tea had previously told users that ID images were deleted immediately after verification, a claim directly contradicted by the breach.1
>> Check Out: The Data Big Tech Companies Have On You
Breach Two: Over One Million Private Messages Exposed (July 28, 2025)
Days after Tea issued its initial statement about the image leak, security researcher Kasra Rahjerdi discovered a second, separate database that had been left accessible without authentication. This database contained more than 1.1 million private messages sent between Tea users, spanning from early 2023 through the week of the discovery.
Rahjerdi reported the finding to 404 Media and directly to Tea rather than publishing it, but provided a database sample to confirm his findings. The messages included highly sensitive personal communications: discussions of abortions, infidelity, relationship conflicts, health information, and in many cases phone numbers and other identifying details that made it straightforward to connect messages to real-world identities.
Tea confirmed the DM exposure in an updated statement on July 30, 2025, acknowledging that direct messages had been accessed as part of the initial incident. The company took the affected system offline and disabled the in-app messaging feature as a precautionary measure.
Breach Summary
Here are the highlights of each of the USAA data breaches discussed above:
| Date Discovered | What Was Exposed | Root Cause | Users Affected |
|---|---|---|---|
| July 25, 2025 | ~72,000 images: 13,000 selfies and government IDs; 59,000 images from posts and DMs | Unsecured Firebase cloud storage bucket left publicly accessible | Users registered before February 2024 |
| July 28, 2025 | 1.1 million+ private messages, including sensitive personal conversations, phone numbers, and location details | Separate database left accessible without authentication | Users from early 2023 onward |
What Caused the Breach
The core failure was a misconfigured cloud storage bucket. Tea used Firebase, Google’s mobile development platform, to store user verification images. The bucket holding those files was not secured behind authentication, meaning anyone with the correct URL could access and download its contents without a password or login.
The second failure compounded the first. Despite migrating to more secure storage in February 2024, Tea had not deleted or properly secured the data in its legacy systems. Users had been told their ID images were deleted immediately after the verification process. They were not. Those images sat in an unsecured bucket for months to years, waiting to be found.
Security analysts who examined the Tea app’s code after the breach found additional structural problems, including API keys and client tokens hardcoded directly into the app’s source code, the absence of SSL pinning, and no mechanism to detect if the app was running on a compromised device. While these did not directly cause the storage bucket exposure, they reflect a pattern of security being treated as secondary to rapid growth.
FYI: Tea had reached the top of the Apple App Store charts in the days just before the breach went public, with more than 6 million users at the time. The combination of rapid scaling and weak foundational security practices created the conditions that made the breach possible and wide-reaching.
The Real-World Harm
The data exposed in the Tea breach is not the kind that leads only to account takeovers. Government IDs contain full legal names, home addresses, and physical descriptions. Private messages on Tea contained deeply personal disclosures that users shared under an expectation of anonymity. The combination created conditions for doxxing, physical harassment, stalking, and identity theft.
The data spread quickly after appearing on 4chan, a forum not known for restraint. Users on that platform openly discussed using the exposed database to retaliate against Tea’s user base, sharing ID photos and calling on others to build tools from the stolen records. The location metadata embedded in some photos gave bad actors a way to map where affected women lived.
FYI: One of the lawsuits that followed was filed by a single mother from Nevada who had been using Tea while fleeing domestic violence. Another used the app to warn other women about a man she said had sexually assaulted members of her community. The breach put both of them at potential physical risk.
Lawsuits and Legal Consequences
Legal action began almost immediately. The first class action lawsuit was filed on July 28, 2025, by Griselda Reyes in the Northern District of California, just three days after the initial breach was discovered. By early August, at least ten lawsuits had been filed in federal and state courts, with five of the federal cases consolidated before U.S. Magistrate Judge Alex G. Tse.2
The consolidated lawsuits allege negligence, breach of implied contract, and failure to adequately secure user data. They also claim Tea misrepresented its data practices, specifically its stated policy of immediately deleting ID images after verification, which the breach demonstrated was not being followed. Several suits seek damages under the California Consumer Privacy Act, which allows statutory damages without requiring proof of individual harm.
Separate lawsuits have also been filed in Illinois alleging violations of the Biometric Information Privacy Act, which requires written consent and a published data retention policy before collecting biometric data, including facial geometry captured through selfies. Courts have not yet ruled on the merits of those claims.
A legal expert quoted by NBC News noted that while proving liability in data breach cases is often straightforward, proving damages is harder. However, the fact that Tea users’ home addresses were actively mapped and circulated online after the breach strengthens the argument that real, traceable harm occurred. At least four suits seek a minimum of $5 million in damages, and settlements in comparable cases have reached hundreds of millions.
Latest Update: Tea has declined to comment on the legal proceedings. No settlement has been announced as of this writing.
What Affected Users Should Do
Assume Your Data Was Exposed If You Signed Up Before February 2024
Tea stated that only users registered before February 2024 were affected by the image breach. However, the private message exposure covered a database stretching from early 2023 through the week of discovery, which means DM content from users who joined later may also have been included. If you were using the app at any point before late July 2025 and sent private messages, treat your communications as potentially compromised.
Incogni’s data removal service scans the internet for your personal information, and sends removal requests to take it down on your behalf.
Check Whether Tea Has Notified You
Tea was criticized for delays in notifying affected users. The lawsuits allege the company failed to provide timely and accurate notice of the breach. If you have not received a notification from Tea, log into your account and check for any communications, or contact Tea directly to ask about your status.
Freeze Your Credit If You Submitted a Government ID
The combination of your full name, home address, and a photo of your face on a government ID is more than enough for an identity thief to open accounts in your name, apply for credit, or attempt to pass verification checks at financial institutions. A credit freeze at all three bureaus, Equifax, Experian, and TransUnion, is free and prevents new credit from being issued without your explicit authorization.
>> Check Out: How to Get a Free Credit Report
Be Alert to Targeted Phishing and Harassment
Because the stolen data includes private conversations about personal relationships, health matters, and location information, affected users face risks that go beyond financial fraud. Bad actors who have this data can craft highly personalized phishing attempts, impersonate people you discussed in messages, or use location metadata to find you. Be skeptical of any unsolicited contact that references personal details you shared on the app
Document and Preserve Any Evidence of Harm
Given the active class action litigation, affected users who experience any concrete harm traceable to the breach, including identity theft, cyberbullying, or fraudulent account openings, should document it carefully. This includes saving screenshots, police reports, bank statements, and any communications you receive. That documentation may be relevant to any future settlement claims.
When the Data You Shared in Private Becomes Public
The Tea breach illustrates a risk that most people don’t fully weigh when signing up for apps that require identity verification: the data you hand over for one purpose, like proving you’re a real person, doesn’t necessarily disappear once that purpose is served. Tea told users their IDs would be deleted immediately. They weren’t. That gap between stated policy and actual practice is where breaches like this do the most damage.
Separately from the breach itself, reducing your overall data exposure is worth thinking about. Data brokers routinely aggregate personal information from public records, app data, and prior breaches, making it easy for anyone to compile a profile on you. A service like Incogni submits automated removal requests to those databases on your behalf. It won’t undo what happened with Tea, but shrinking the pool of information that’s publicly findable about you is a meaningful layer of protection, particularly when the data already out there includes your home address.
>> Learn More: How to Remove Your Address From the Internet
The Bottom Line
The Tea app breach is notable not just for its scale but for the specific nature of what was exposed and who was harmed. An app designed to protect women from predatory behavior left their most sensitive identifying information, government IDs, private conversations, and location data, accessible to anyone who went looking. The irony was not lost on users or the courts: the very tool meant to make dating safer became the mechanism of harm.
If you used Tea before February 2024 and submitted a government ID during signup, your information almost certainly touched the breached system. Freezing your credit, staying alert to targeted harassment or phishing, and documenting any harm you experience are the most important practical steps. The consolidated class action litigation in the Northern District of California is ongoing, and any settlement would likely require affected users to file claims to participate.
Frequently Asked Questions
-
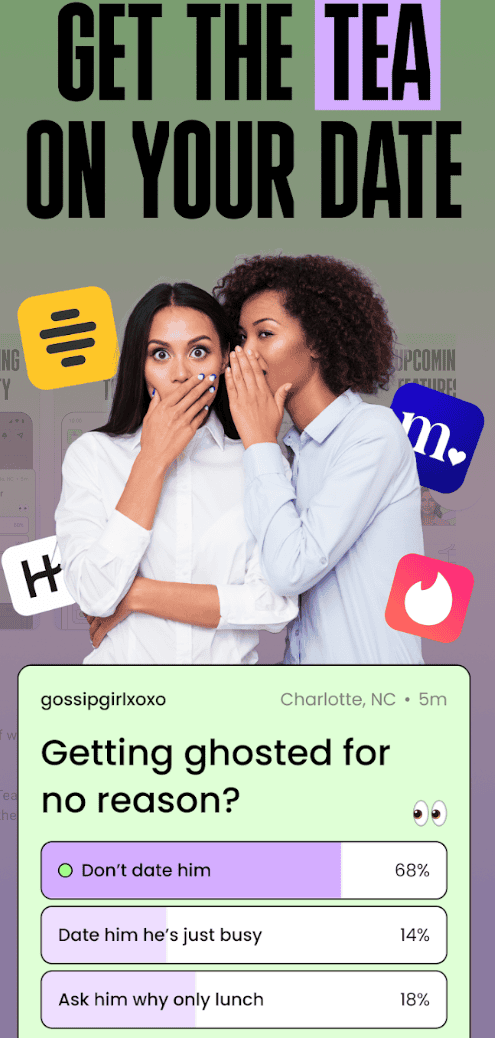
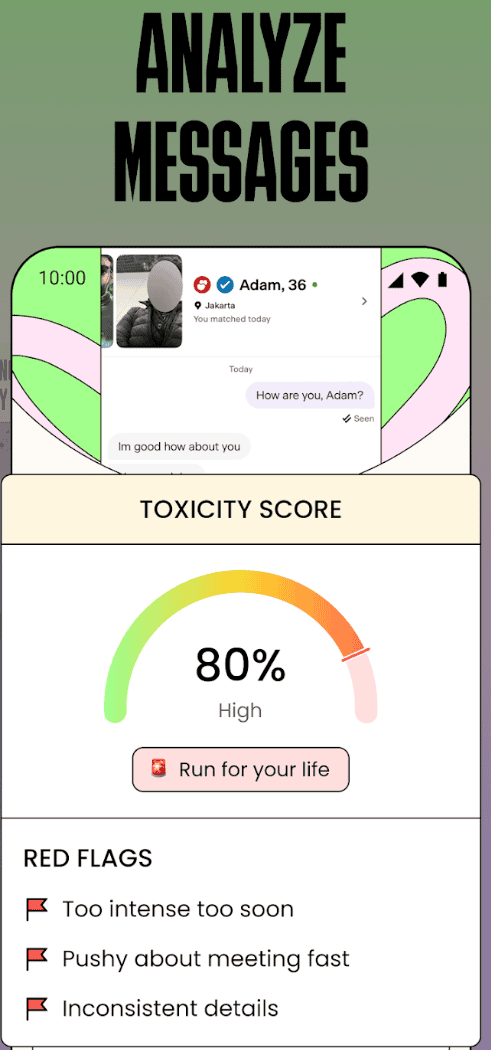
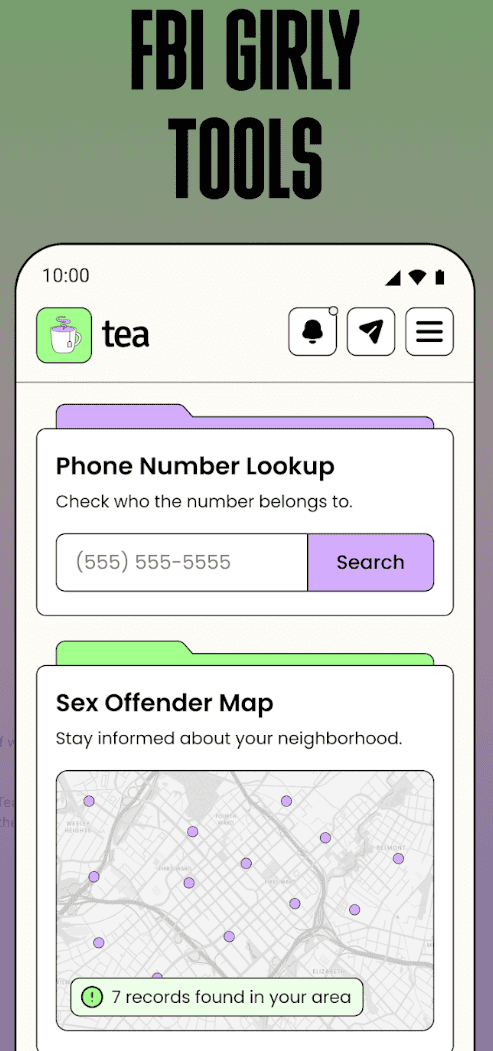
What is the Tea app?
Tea is a women-only dating safety app launched in 2023. It allows verified users to anonymously share information about men they have dated or encountered, including red flag warnings, background check results, reverse image searches, and community reviews. To join, users must submit a selfie and government-issued ID for identity verification. The app reached the top of the Apple App Store charts in July 2025 and claimed over 6 million users at the time of the breach.
-
Who was affected by the Tea app data breach?
Tea stated that the image breach affected users who registered before February 2024, when the company migrated to more secure data storage. The private message database covered communications from early 2023 through the week of the breach, meaning DM content from users who joined before or around that window may also have been exposed. Tea had over 1.6 million users at the time of the breach disclosure.
-
What information was leaked in the Tea app breach?
The first breach exposed approximately 72,000 images, including around 13,000 selfies and government-issued ID photos such as driver’s licenses submitted during account verification, and roughly 59,000 images from user posts, comments, and direct messages. Some of those images contained GPS metadata. The second breach exposed more than 1.1 million private messages containing personal conversations, phone numbers, and other identifying information.
-
Is there a lawsuit against the Tea app?
Yes. At least ten lawsuits were filed in federal and state courts following the breach. Five federal class action cases have been consolidated before a single magistrate judge in the Northern District of California. The suits allege negligence, breach of contract, and violations of the California Consumer Privacy Act. Separate lawsuits in Illinois allege violations of the Biometric Information Privacy Act related to the collection of selfies for verification. No settlement has been announced.
-
Did Tea delete user IDs after verification as it claimed?
No. Tea’s privacy policy stated that identity verification images were deleted immediately after the review process was complete. The breach demonstrated that this was not the case: government IDs and selfies from users who signed up as far back as 2023 were sitting in an unsecured cloud storage bucket at the time of the breach in July 2025. This gap between Tea’s stated policy and its actual practice is central to the class action lawsuits.

