Finding the right antivirus can be an overwhelming endeavor. As you’re doing your research, combing through the dozens of available antivirus software services, it’s perfectly acceptable to wonder, “Is this really going to protect me from hackers?” How much protection can you really get when the average cost of antivirus software is $30 to $50 per year anyways?
Well, our cybersecurity experts set out to answer that question exactly. We use the European Institute for Computer Antivirus Research (EICAR) malware test file to figure out how well common antivirus software works to stop hackers.1 Our team looked at everything from built-in antivirus like Windows Defender to top-tier third-party antivirus software. After having tested over 40 different antivirus software, we’ve figured out how well antivirus works for stopping hackers. So, let’s dig in.
Does Antivirus Software Stop Hackers?
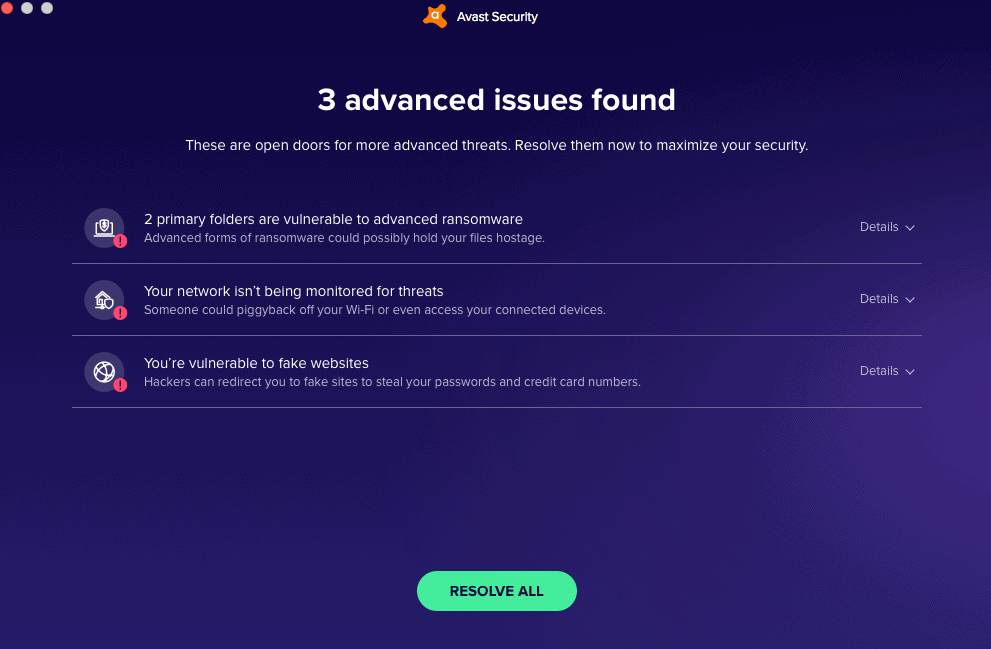
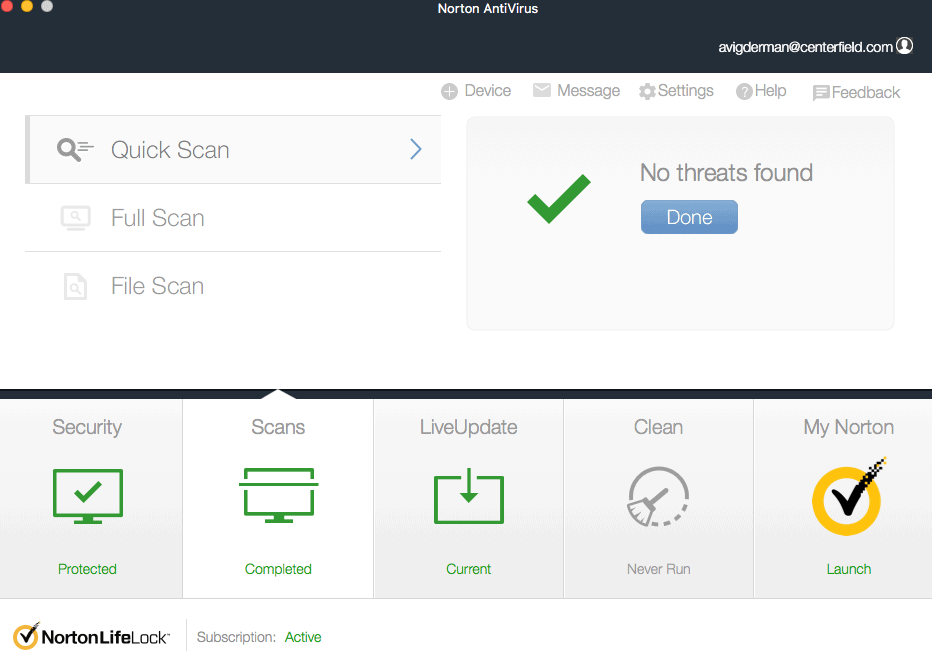
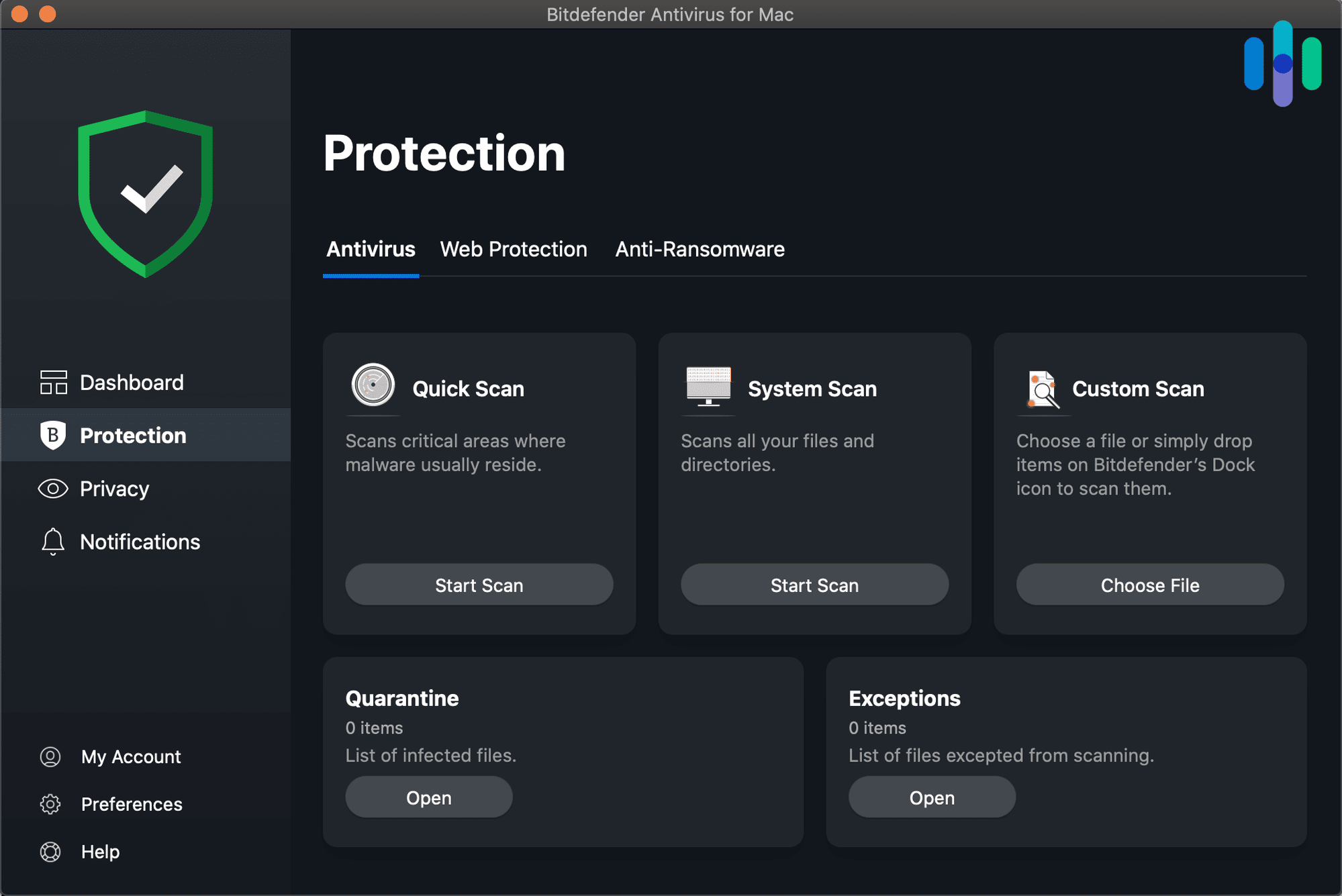
Antivirus software immunizes our computers against unauthorized software or coding, which means it can stop hackers that use malware, remote access trojans (RAT), and other malicious programs. You just need good antivirus software, and we give you three highly-rated options below.
No Antivirus Is 100 Percent Foolproof
Although antivirus is an essential part of digital security, it is not foolproof. Each day, more than 350,000 new malware programs are created,2 and it’s very possible for newly created malware to get around protections. That’s why our team uses our computer’s built-in protections like Windows Defender and macOS Security on top of third-party antivirus software.
Insider Tip: No singular digital security method is completely bulletproof. To have the best chance of protecting yourself, a combination of methods like VPNs, password managers, and identity theft protection is necessary.
What Is Antivirus Software?
Antivirus software is a type of software developed to protect computers and mobile devices from harmful programs. It preemptively detects, neutralizes, and disposes of malware. Antivirus software identifies malware and viruses through files in its database, and most also scan our devices for suspicious behavior, enabling them to spot threats that are not included in the database.
How Antivirus Works
Antivirus deploys a number of methods to stop hackers and fight against unauthorized code, or software that could threaten the operating system. For starters, it detects threats in real time; if we downloaded a file that the antivirus software flagged as dangerous, we would get a notification, and then we’d know not to open that file. Once the threat is identified, the antivirus software removes the malware, foiling the hacker’s attempt to compromise our information or system. It also conducts scans regularly and notifies us when harmful viruses or malware is detected.
Antivirus programs use methods like signature analysis and behavior-based detection to identify threats. Signature analysis compares potential threats to a database of identified malware. The downside is that if the threat isn’t in the database, it won’t be detected. That’s where behavior-based detection comes in. Behavior-based detection looks for suspicious activity and can successfully detect new malware that might not be included in the antivirus’ database.
Who Are Hackers?
Hackers, as we think of them, are criminals who gain unauthorized access to a network and devices with the intent to steal sensitive data like financial information or company intelligence. But in reality, not all hackers are criminals. Some take on a hacker role to help organizations find vulnerabilities. It all depends on what hat the hacker is wearing. Here’s an overview of the three different types of hackers:
- White hat hackers: These “good hackers” try to help businesses by finding holes in security networks and then notifying the business so the weakness can be addressed. White hat hackers are often compensated because they help businesses patch holes in their security, preventing them from dealing with data breaches.
- Black hat hackers: Black hat hackers are what we think of as a traditional hacker. They break into businesses’ or individuals’ systems and use stolen information either for extortion or for personal gain.
- Gray hat hackers: Gray hat hackers have the skill sets to break into all kinds of systems, but they see it more as a hobby or challenge. They aren’t trying to bolster a company’s security or inflict harm; rather, they hack as a sport and break into systems just because they can.
Types of Hacking
Antivirus software protects us from hackers by scanning for different types of hacking techniques. And just like there are many different types of hackers, there are also many types of hacking,3 including:
- Malware: Malware is kind of a catchall term for cyberthreats, like viruses and ransomware, that can take control of your machine and send confidential data to the attacker’s home base. Once hackers obtain the right information, they can use it for identity theft and other nefarious acts. Trojans are another type of malware. They masquerade as real software, and once a user mistakenly downloads them, they take control of devices.
- Phishing: Phishing happens when an attacker sends an email that appears to be from someone we know and trust. Typically, it has some urgency to it and requests that you open an attachment or enter personal credentials. Doing so could install malicious software onto your system, or enable hackers to log into your accounts.
- SQL injection: This type of attack specifically targets servers that store critical data in the form of the SQL programming language. Altering the underlying code of a website could cause a site to divulge sensitive or confidential information that it typically wouldn’t.
- Cross-site scripting: Instead of targeting a website, like in SQL injections, in cross-site scripting, the hacker targets a user visiting a website.
- Distributed Denial of service (DDoS): In DDoS attacks, hackers flood a website with more traffic than it can handle, bogging down servers and making the website inaccessible for visitors.
Did You Know? While we usually think of hackers as ultra-smart people with degrees in Computer Science, some types of hacks are surprisingly easy to execute. For example, to run a DDoS attack, a criminal can buy a botnet for as little as $200 and then direct that botnet to a website, server, or network.
- Session hijacking: When we visit a website, we are given a unique session ID between us and the website. Attackers can hijack the session and pose as the computer or site, making a request for private information and consequently stealing our data.
- Credential reuse: Though it’s a best practice to have a unique password for every account, hackers know that many users use the same credentials across multiple platforms. Once a hacker obtains a collection of usernames and passwords, they can easily use the same credentials to log in to other sites.
Do You Really Need Antivirus Software?
When it comes to digital security, more is more. Hackers tend to start by targeting free, built-in software that runs on millions of machines before moving on to third-party antivirus software. There are more than 677 million malware programs out there, with more being made each day.4 Additional protection is necessary to keep up with evolving threats as they are created.
What to Look for in Antivirus Protection
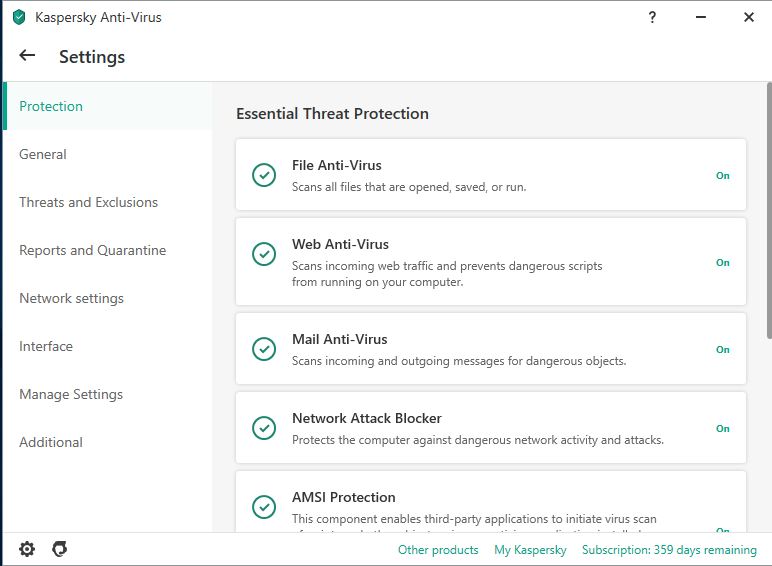
The most important thing to look for in antivirus protection is how well it can detect malware and viruses, but there are many other important factors to consider when evaluating a service, such as:
- Scanning capabilities: On-access scanning runs in the background whenever the software is running, and on-demand scanning happens when we request it specifically. We prefer on-access scanning because it detects viruses and malware in real time, but we also like to have the option to scan when we want to. Ideally, a service should have both.
- Firewall: Some antivirus software comes with firewalls built in that monitor network traffic based on a set of security rules and determine what activity to block.
- Behavior-based detection: Traditional antivirus matches programs to a database, while behavior-based detection spots threats based on suspicious activity. Behavior-based detection is especially beneficial because new threats are developed constantly, and they aren’t always included in preexisting databases.
- Privacy policy: We always check what types of information services are keeping track of. Data, like payment information, is acceptable, while browsing activity and geolocation are not.
- Devices connected: We want to make sure we can use the same subscription across all the devices in our household.
- Customer service options: When we’re in a pinch, we like to have options, so we check for multiple ways to reach customer support, like a FAQ database, live chat, email, and the gold standard, a phone line.
- Cost: Of course, the bottom line is always a consideration, especially for a long-term investment like antivirus. A ballpark estimate is around $40 per year, but there are services that are both cheaper and more expensive.
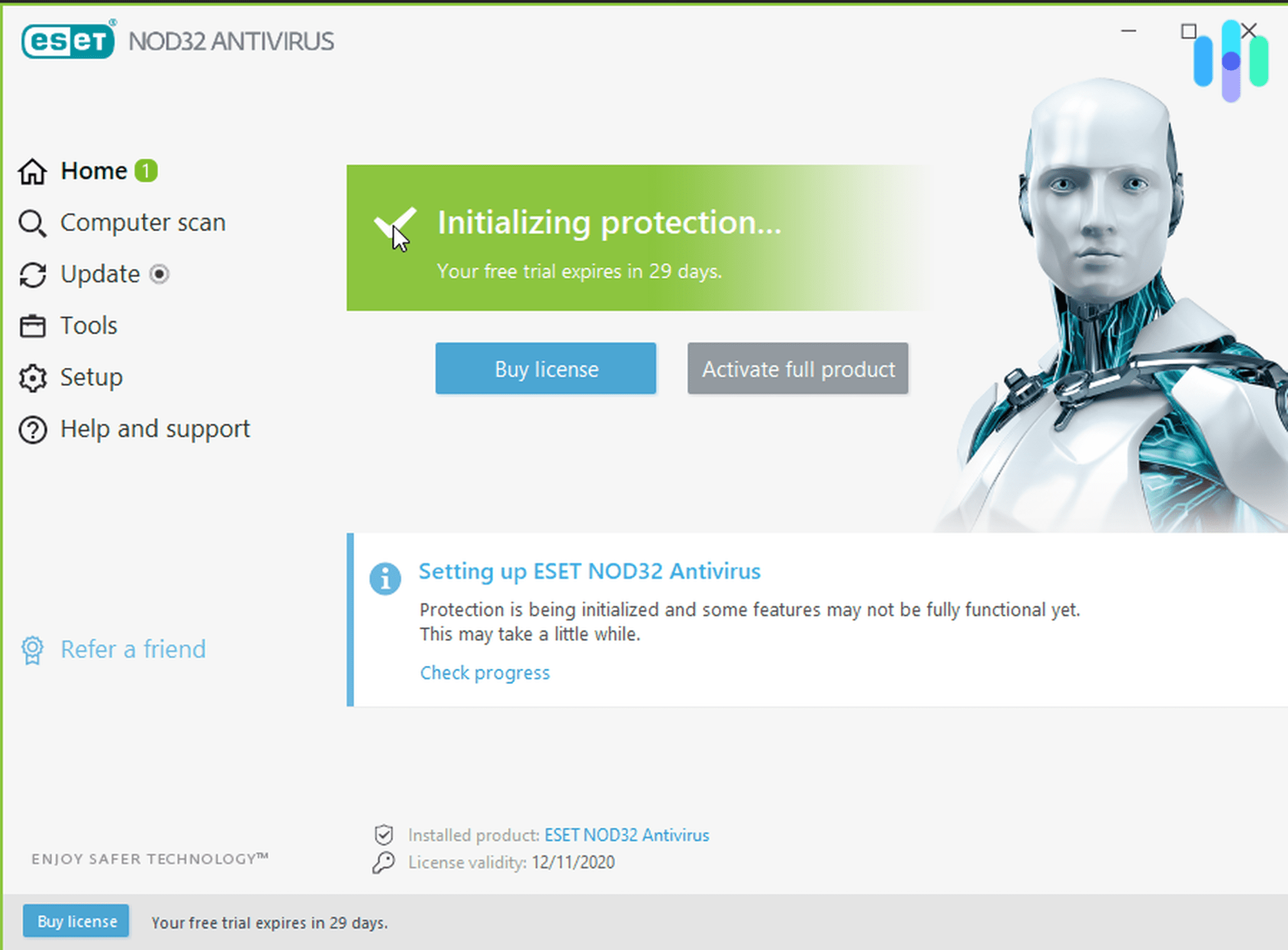
Money saver: Most antiviruses offer a free-trial or a money-back guarantee so you can test different services to find which suits you best.
Other Ways to Stop Hackers
There’s a wide range of tools you can deploy to stop hackers from getting your information. We recommend the following best practices:
- Deploy firewalls or boost network protection to scan devices and networks for threats. Sometimes, these come bundled with antivirus software.
- Get a VPN to encrypt your web traffic and hide your IP address.
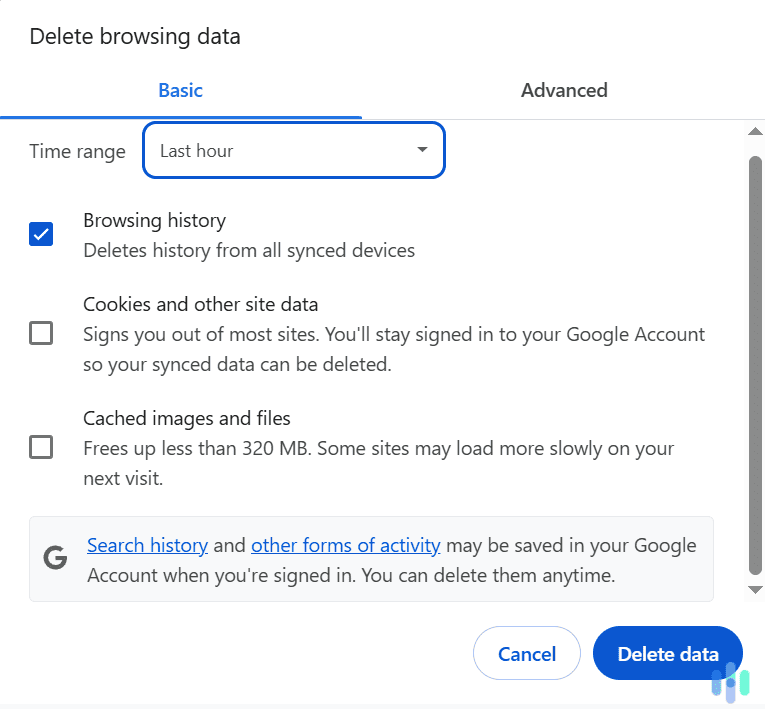
- Implement your system’s updates to patch digital security software.
- Ignore spam or suspicious emails.
- Utilize a password manager to store all your usernames and passwords in an encrypted vault. You can also evaluate your current passwords using our password strength tool (it’s free!).
- Activate two-factor authentication to validate a login on multiple devices, through either sending a PIN to your phone or emailing a code.
- Opt for multi-factor authentication (biometrics like fingerprint or facial recognition) to access accounts, when available.
In Summary
After testing over 40 different antivirus software, we can confidently say that no antivirus offers 100 percent protection. Cyberthreats develop too quickly for any antivirus software to keep up. But, our entire team still uses antivirus software since it gives us solid protection as the basis of our security. From there, we add on extra protections like VPNs, firewalls, and password managers.
There’s simply too many threats out there to rely on a single piece of software for complete protection but antivirus software is a great place to start.
FAQs
Here are the most common questions we get asked about antivirus and hackers.
-
What software prevents hackers?
Software such as Bitdefender, McAfee, Norton Antivirus, and VIPRE prevents hackers.
-
Can hackers be stopped?
Yes, hackers can be stopped, but typically stopping them takes several methods working in tandem, like:
- Additional antivirus software
- Password managers
- VPNs
- Firewalls
- Web traffic encryption
There is no way to guarantee that hackers won’t penetrate your devices, but these methods significantly decrease the likelihood of a hacking.
-
Can antivirus kill viruses?
Yes, antivirus software can kill viruses. Antivirus programs scan your computer and find malware in the system, regardless of how long it has been there. Once the file is located, the software can remove it.
-
Can your computer get hacked if it’s off?
Generally, no, your computer can’t get hacked if it’s turned off. However, it could still be possible if the turned-off computer is connected to a shared network in an office environment, because, typically, there are features that allow for the system to be turned on remotely.