Mobile hotspots have become a vital tool for accessing the internet wherever you get cell service, allowing us to share our cell connections with one or several other devices. But hotspots do pose some security risks.1 Cybercriminals and hackers can easily intercept your data or gain unauthorized access to your devices if you’re not careful.
In this guide, our cybersecurity experts tackle how to mitigate security risks and safeguard your hotspot connections with strong passwords and military-grade encryption courtesy of virtual private networks, or VPNs.
What Is A Hotspot?
A hotspot is any device that supplies Wi-Fi to another nearby device. Typically, we use our mobile phones as hotspots, drawing off our cellular data to connect our laptops to the internet. This can be very useful when you need an instant connection to get some work done. But, as we said above, if you’re not careful about it, hotspots can also expose you to a virtual sea of fraudsters as well. More on this below.
How Do Mobile Hotspots Work?
There are three components to a hotspot.
- The source is whatever your hotspot uses to access the internet. In most cases, it’s your mobile phone’s 4G or 5G connection.
- The hotspot device is usually your mobile device, i.e. a phone or tablet with cellular data.
- The tethered device is the device you’re connecting to the hotspot and giving Wi-Fi to. Usually this is a laptop, but it could also be the phone of a friend or child who’s out of data.
In a nutshell, the hotspot device connects to the source and the tethered device connects to the hotspot, drawing Wi-Fi.
Where Are the Weak Spots, and How Do You Fix Them?
What can possibly go wrong in a setup like this? Plenty.
Your hotspot — your mobile device — has two connections: one to the source and one to the tethered device. Either could potentially leak your data so anyone else on the network can see who you are and what you’re up to. Someone in the vicinity could also connect to your hotspot and run up your data bill by streaming their own Spotify playlists.
What do you do about those problems? That depends on how you’ve set up your connections. Let’s consider both ends of the equation.
Source Connections
There are basically three ways to connect your hotspot to the internet.
- You can connect through your mobile data plan. You’re actually pretty safe with 5G, 4G, and even 3G, at least from hackers or casual observers.2 The downside to this type of connection is that you’re using data, and at some point you may be hit with overage charges. Your mobile carrier also still has access to information about what sites you’re visiting and what apps you’re using. When it comes to privacy, you can do better.
- You could instead connect to public Wi-Fi if it’s available, but it begs the question: If you have access to public Wi-Fi, why do you need to create a hotspot in the first place? You can log on with any of your devices. More importantly, public Wi-Fi is notoriously insecure. The whole point is to allow anyone and everyone who happens to be at the location to join the same network. Once everyone is on the same network, you can never tell who is doing what.
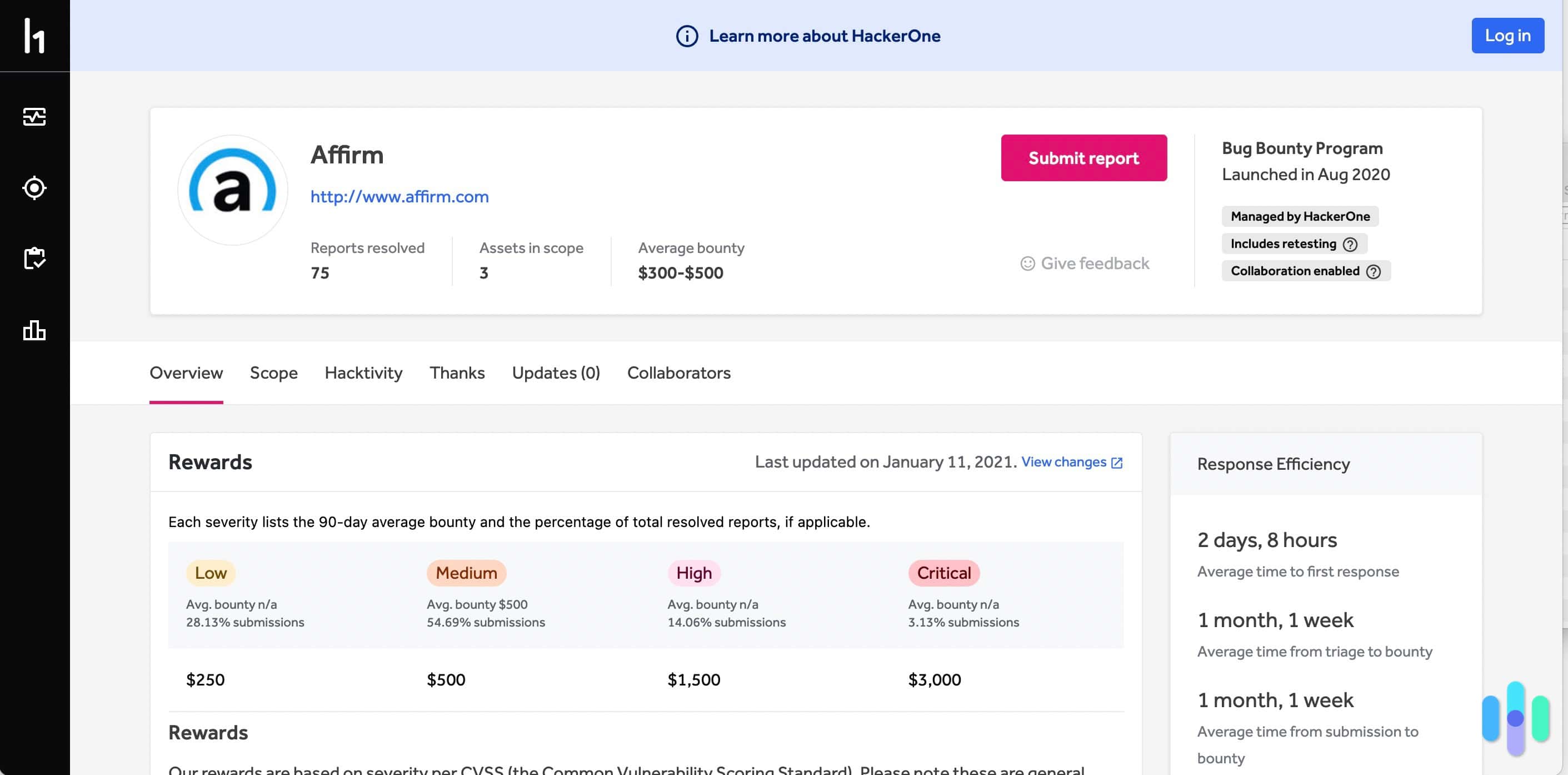
- A third option is a VPN, which lots of people choose when faced with public Wi-Fi. A VPN is an encrypted tunnel to the internet. You still need either your data plan or public Wi-Fi to get to the tunnel, but once you’re in the tunnel, you know for certain no one has access to your personal information. No one knows your IP address, and no one can see your browsing history.
Did You Know: A VPN is an encrypted tunnel that connects you to the internet, but you can’t use a VPN if you don’t have an existing internet connection. Check out our 2024 guide on VPNs to learn more.
What does all this mean?
- Never use public Wi-Fi for your hotspot source if you can help it. It’s never safe logging on to public Wi-Fi, but you’re magnifying your vulnerabilities if you use it for a hotspot.
- Your mobile data plan keeps you safe from hacking and casual intrusion, but your service provider may still log your browsing history — and they’re charging you while they do it.
- The safest option for a hotspot source is to connect to the internet through a reputable VPN. No one can access your data or see what you’re up to online.
NordVPN uses military-grade encryption to secure your digital information regardless of the network you connect to.

The Tether
Your hotspot makes a second connection, to the device or devices using it as a hotspot. The second connection is known as the tether.
The tether connection is just as vulnerable to eavesdropping and hacking as the source connection. If left unsecured, anyone nearby can log on to your hotspot. Obviously, that puts your data at risk. They don’t have to go to the trouble of sorting through your device to wreck your day. They can simply use your hotspot as free internet, cavorting on the web to their heart’s content on your dime.
It’s important that you secure this connection too. Since you’re the one who created it, you’re the one who will have to do the securing.
- Make sure you give your network — SSID — a name. Databases exist that contain the passwords for Android, iPhone, and portable hotspot devices, and these passwords are keyed to the default SSID. Naming your network will help prevent anyone from using one of these passwords to access your network.
- You need to set a strong password for your hotspot so you — and only you — can access it. For maximum security, you’ll also want to change the password regularly.
- Use WPA2 or WPA3 encryption.
Pro Tip: Like they say, if the internet is a door then your password is the key. Keep your data safe using our password generator to create the strongest passcode possible.
The best VPNs can also significantly improve the security of your tether connection, but a VPN on a mobile hotspot device will not protect your tethered device. Android OS and iOS do not allow VPN security to move in two directions. If you want to secure your tether connection, you need to install a VPN on the tethered device. It helps to sign up with a VPN that allows as many simultaneous connections on as many devices as possible, so you won’t pay extra to install the software on both the mobile hotspot and the tethered device.
Pro Tip: Windows allows VPNs to work two ways at once. If you don’t have access to a VPN-ready router, you can use your Windows-based computer as a hotspot, and your VPN coverage on that device will extend to all your tethered devices.
The Bottom Line
A mobile hotspot is not inherently safe. Quite the opposite, in fact. It can be hacked either at the point where it connects to the internet or the point where it connects to any tethered device. Others can see what you’re up to and, in certain circumstances, may even be able to take over your entire network.
That doesn’t mean you can’t use this handy technology in a pinch or even to improve your existing security. The trick is to know exactly how your hotspot works and how to shore up any potential holes in your security. A VPN and some strong passwords can ensure you’re safe as houses, even if you’re using a tethered device.
Looking for a great VPN to help ensure your internet connection is absolutely secure? Check out our complete NordVPN review and our review of Surfshark.
>> Related Reading: What is a Password Manager