In 2019, Capital One became the target of one of the largest financial data breaches in U.S. history. A single attacker, exploiting a misconfigured firewall in Capital One’s cloud infrastructure, made off with personal information on more than 100 million people across the United States and Canada. The breach affected anyone who had applied for a Capital One credit card going back to 2005, whether or not they ever became a customer.
What followed was a years-long legal reckoning: a criminal conviction, an $80 million regulatory fine, a $190 million class action settlement, and enforcement actions from both the Office of the Comptroller of the Currency and the Federal Reserve. Here is a complete account of what happened, how it unfolded, and what it means for people whose data was exposed.
What Happened
The breach traces back to a single vulnerability in Capital One’s cloud setup on Amazon Web Services. Paige Thompson, a 33-year-old former software engineer who had previously worked at AWS, built a custom scanning tool to search for AWS accounts with misconfigured firewalls.1 When she found Capital One’s vulnerable web application firewall, she used a technique called server-side request forgery to extract temporary credentials from AWS’s internal metadata service. Those credentials gave her access to hundreds of Capital One’s data storage buckets.
The initial unauthorized access occurred between March 22 and 23, 2019. Thompson then spent months accessing data from those storage buckets. Capital One had no idea any of this was happening until July 17, 2019. A GitHub user spotted Thompson posting about the stolen data under her alias “erratic” and sent a tip to Capital One through its responsible disclosure program.
Capital One confirmed the breach on July 19, 2019 and immediately notified the FBI. Investigators were able to identify Thompson from her online posts. FBI agents executed a search warrant at her residence, found electronic storage devices containing a copy of the stolen data, and arrested her in late July 2019. The breach was publicly disclosed on July 29, 2019.2
Try Incogni today to start removing your personal data from hundreds of data brokers.
What Happened To The Hacker
Thompson made little effort to conceal what she had done. She posted about the stolen data on GitHub using her full name, boasted about the Capital One hack in Slack channels, and discussed her methods openly on social media using the same handle she used elsewhere online.
In June 2022, a Seattle jury convicted Thompson on seven counts, including wire fraud and five counts of unauthorized access to protected computers. Prosecutors had requested a seven-year prison sentence. In October 2022, the judge sentenced her to time served plus five years of probation, citing her documented mental health challenges. Prosecutors appealed, and in March 2025, an appeals court ruled the sentence was too lenient and remanded the case for resentencing.3
>> Read More: What is a Data Breach and How to Prevent a Breach in 2026
Breach Summary at a Glance
| Year | Customers Affected | Data Exposed | How It Happened |
|---|---|---|---|
| 2015 | ~15 million | SSNs, DOBs, driver’s licenses, passport numbers | Third-party breach at Experian |
| 2018 | ~2 million | Names, phone numbers, emails, account numbers | Direct network intrusion |
| 2021 | ~76.6 million | SSNs, DOBs, driver’s licenses, account PINs | Brute force via unprotected GPRS gateway |
| 2023 (Jan.) | ~37 million | Names, addresses, phone numbers, emails, DOBs | Vulnerable API endpoint |
| 2023 (Apr.) | 836 | SSNs, government IDs, account PINs | Targeted sales application access |
>> Check Out: The Best Free Identity Theft Protection Services
What Data Was Stolen
The scale and variety of compromised data was substantial, reflecting just how much information Capital One had accumulated from credit card applications spanning more than a decade.
| Data Type | Records Affected | Who Was Impacted |
|---|---|---|
| Names, addresses, phone numbers, email addresses, dates of birth, self-reported income | ~106 million | U.S. and Canadian credit card applicants |
| Social Security numbers | ~140,000 (U.S.) | U.S. credit card customers |
| Canadian Social Insurance numbers | ~1 million | Canadian applicants |
| Linked bank account numbers | ~80,000 | Secured credit card customers |
| Credit scores, credit limits, balances, payment history | Large subset | Existing credit card customers |
Capital One later disclosed that additional Social Security numbers beyond the original count had also been accessed. A follow-up investigation in January 2021 found that approximately 4,700 more Social Security numbers had been compromised during the breach. The compromised application data covered people who had applied for Capital One credit cards between 2005 and 2019.
No credit card account numbers, login credentials, or payment card information were among the stolen data, which Capital One emphasized at the time of disclosure. The company also said there was no evidence the data had been used for fraud, though it acknowledged that fully assessing misuse was difficult given the volume of information involved.
Did You Know: Last year, 62 million Americans experienced credit card fraud. This surge is partially due to major incidents like the 2019 Capital One data breach.
How the Breach Was Discovered and Resolved
Capital One did not catch the breach through its own monitoring. It was alerted by an outside tip from a GitHub user who had seen Thompson’s posts about the stolen data. Upon receiving the tip on July 17, 2019, Capital One investigated, confirmed the intrusion two days later, and contacted the FBI. Capital One said it immediately fixed the server-side request forgery vulnerability that Thompson had exploited and closed off the compromised access points.
The OCC later noted that Capital One’s internal audit function had failed to identify the cloud security weaknesses that made the breach possible. They also noted that when concerns were raised, the board failed to take adequate action. The OCC specifically cited Capital One’s failure to establish effective risk assessment processes before migrating its technology operations to the public cloud.
>> Learn About: Securing Confidential Personal Data Both Online and Offline
Fines, Lawsuits, and Settlements
The legal fallout from the breach moved on multiple tracks simultaneously from several agencies:
- Office of the Comptroller of the Currency: In August 2020, the Office of the Comptroller of the Currency fined Capital One $80 million.4 That marked the first significant OCC penalty issued for a cloud-related data breach. The OCC also issued a consent order requiring Capital One to form a compliance committee and submit plans for improving its risk management and cloud security controls. This order remained in effect until September 2022, when the OCC determined Capital One had sufficiently addressed the concerns.
- Federal Reserve: At the same time, the Federal Reserve entered into a separate cease-and-desist order with Capital One’s parent holding company. They required the board to submit detailed plans for improving risk management and internal controls. The Fed did not impose a monetary penalty in its action. It terminated its enforcement action in July 2023, concluding that Capital One met its requirements.5
- Class Action Lawsuits: On the civil side, customers filed multiple class action lawsuits that were consolidated into a multidistrict litigation proceeding. In December 2021, Capital One agreed to pay $190 million to settle. The settlement fund covered out-of-pocket losses directly attributable to the breach, with claims accepted through August 2022. Capital One and AWS both denied liability as part of the settlement.
Needless to say, Capital One was heavily punished for this data breach even though it was conducted by a malicious actor. At the end of the day, they’re still responsible for securing their clients’ information as seen by the results of these legal actions.
Did You Know: Individual payouts from the class action lawsuit varied from $75 for those without proof up to $25,000 with proof of damages. However, it’s difficult to come up with adequate proof on your own. That’s one reason why the best identity restoration services thoroughly document every instance of identity theft to help in these cases.
What You Can Do to Check If You Were Affected
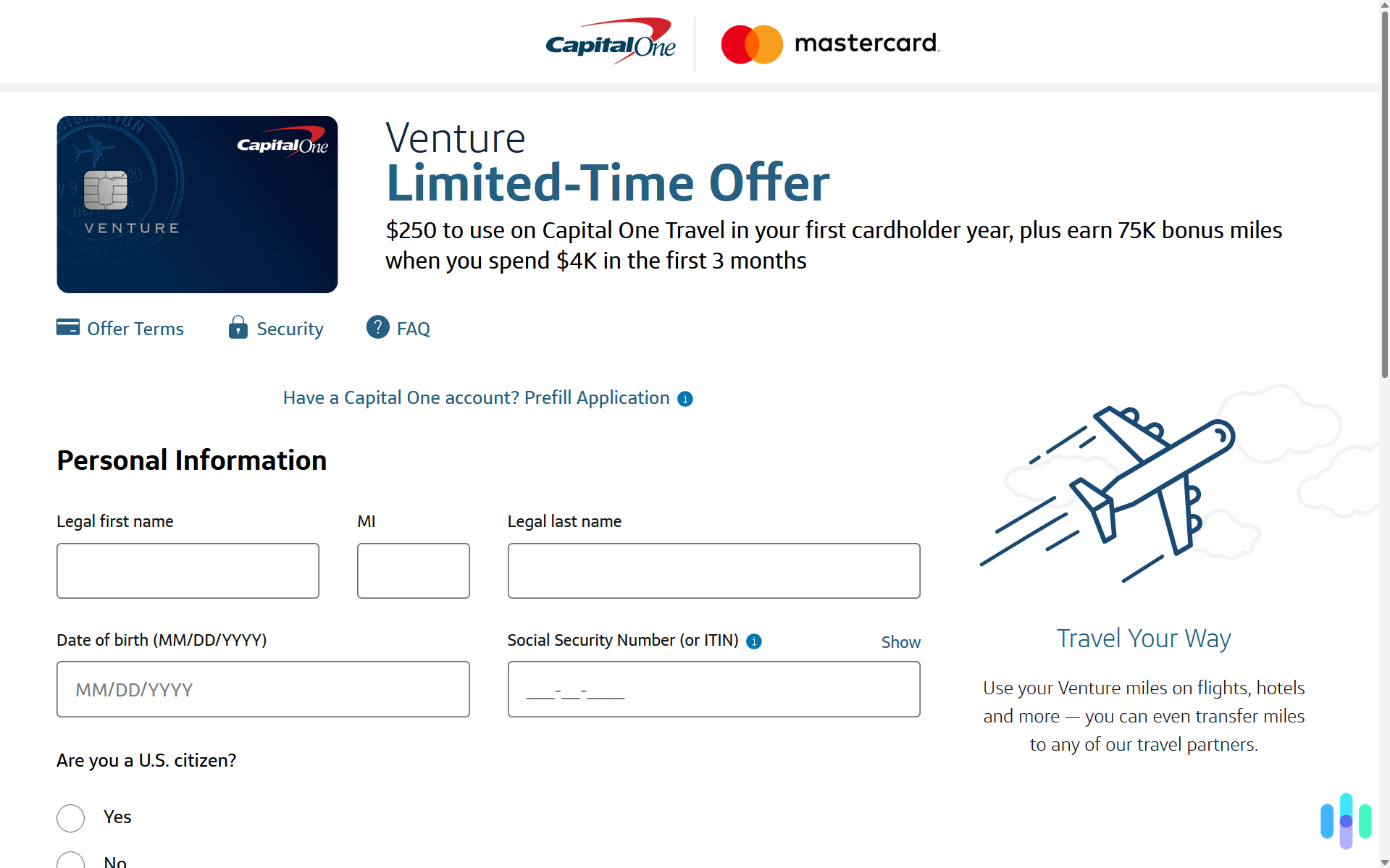
Look for Notifications from Capital One
Capital One committed to notifying all affected individuals after the breach and provided a dedicated support page and customer hotline for those who wanted to verify their status. If you applied for a Capital One product at any point between 2005 and 2019, you were within the range of potentially affected applicants.
Place a Credit Freeze
If your Social Security number was among the approximately 140,000 exposed in the breach, a credit freeze is one of the most effective protections available. It prevents new credit from being opened in your name without your explicit authorization and is free to place and lift at all three major bureaus: Equifax, Experian, and TransUnion. Many of the best credit protection services can help you with this as well.
Monitor Your Credit Reports and Financial Accounts
Pull your free credit reports from AnnualCreditReport.com and look for accounts, inquiries, or activity you do not recognize. Given that the breach covered application data going back to 2005, it is worth checking even if you have not been a Capital One customer for years. Also review your bank and credit card statements for any unfamiliar transactions.
Check Have I Been Pwned
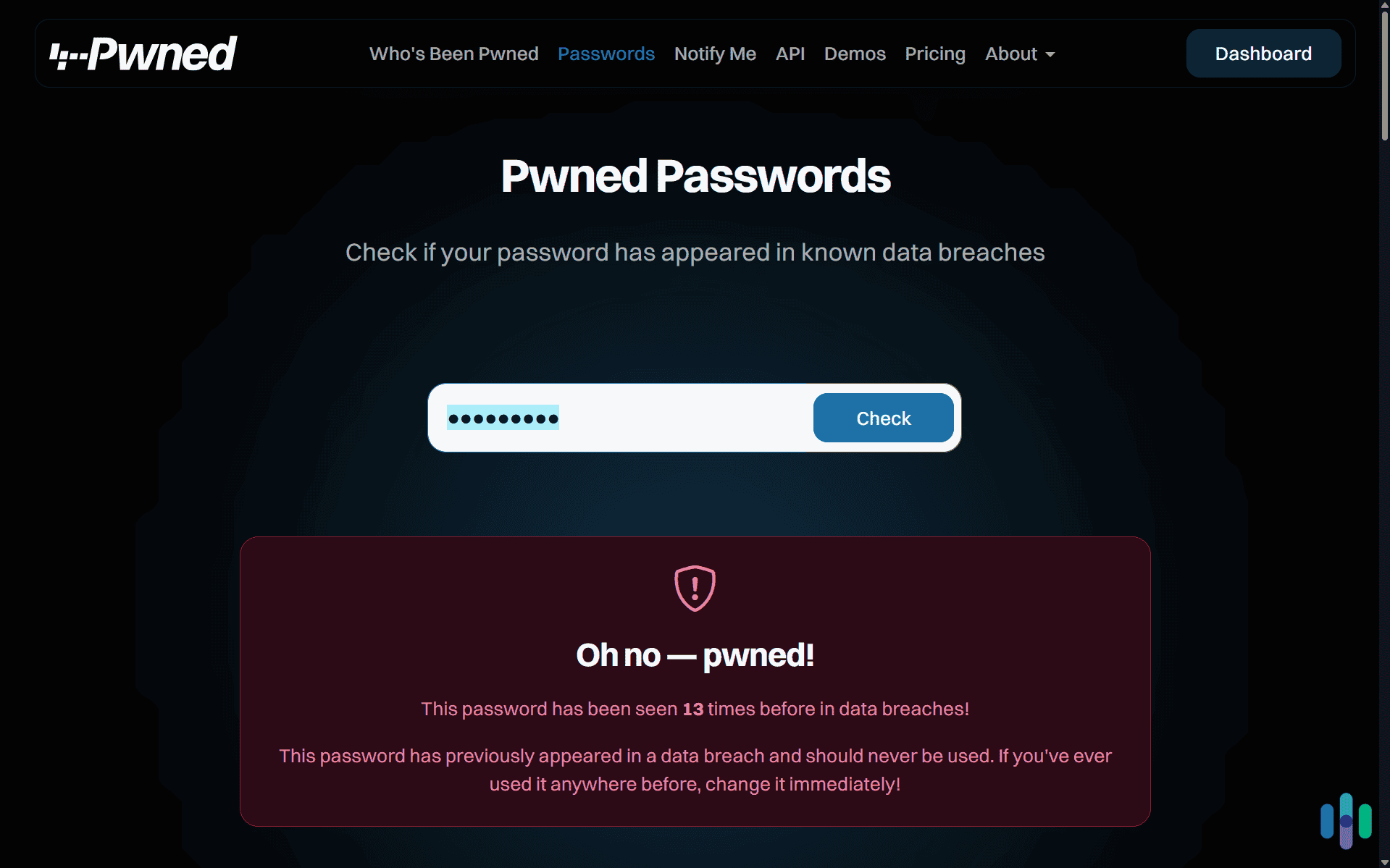
Entering your email address at Have I Been Pwned will show whether your information appears in any major indexed breach datasets. You can also enter your password to see if it leaked as well. Given the scale of the Capital One breach and the range of application data involved, this is a straightforward first check.
Stay Alert for Targeted Phishing
The breadth of contact information in the stolen dataset, including names, email addresses, phone numbers, and mailing addresses, makes targeted phishing a real risk. Be skeptical of unsolicited communications claiming to be from Capital One or any financial institution, particularly ones that ask you to confirm personal details or click a link. Read through our phishing protection guide for more details.
>> Learn More: Phishing Text Messages: A Guide to “Smishing”
Your Information Doesn’t Stay Put After a Breach
One of the less visible consequences of a breach this size is what happens to the data afterward. Even when, as Capital One suggested, there is no immediate evidence of fraud, breached information has a long shelf life. Records get traded across criminal networks, combined with data from other incidents, and eventually find their way into data broker databases that anyone can access.
If the Capital One breach has you thinking about how much of your personal information is floating around online, that concern is warranted well beyond the breach itself. A service like Incogni sends automated removal requests to data broker databases on your behalf. This reduces how findable your information is to people looking to exploit it. During our tests of Incogni, it requested the removal of our information from over 800 sites in three months. While that won’t undo a breach, it greatly reduces your exposure.
>> Check Out: A 2026 Guide to Data Removal Services
The Bottom Line
The Capital One breach is a useful reminder that major data exposures do not always require sophisticated, nation-state-level attacks. A single misconfigured firewall and one person with the knowledge to exploit it were enough to expose more than 100 million people’s personal information. Capital One paid more than $270 million in fines and settlements, faced years of regulatory oversight, and had to rebuild significant parts of its cloud security program in the aftermath.
If you applied for a Capital One credit card or product at any point between 2005 and 2019, your information was within the scope of the breach. Checking your credit, placing a freeze if your SSN was exposed, and staying alert to phishing attempts are the most impactful steps you can take from here. You can also consider investing in a data removal service like Incogni to minimize any lasting exposure.
Frequently Asked Questions
-
How many people were affected by the Capital One data breach?
Approximately 106 million people in the United States and Canada had their information exposed. This included around 100 million U.S. residents and 6 million Canadians who had applied for Capital One credit card products at any point between 2005 and 2019. Not everyone’s data was equally sensitive: only around 140,000 people had Social Security numbers exposed, and about 80,000 had linked bank account numbers compromised.
-
How did the Capital One data breach happen?
The breach was caused by a misconfigured web application firewall in Capital One’s Amazon Web Services environment. A former AWS engineer named Paige Thompson exploited this misconfiguration using a technique called server-side request forgery. This allowed her to extract AWS credentials and use them to access Capital One’s cloud storage buckets containing customer data. The attack required no malware and no phishing. It was a direct exploitation of a configuration error.
-
Was the Capital One hacker caught and convicted?
Yes. Paige Thompson was arrested by the FBI in July 2019, just days after the breach was publicly disclosed. In June 2022, a federal jury in Seattle convicted her on seven counts, including wire fraud and unauthorized access to protected computers. She was sentenced to time served and five years of probation in October 2022. Prosecutors appealed that sentence, and in March 2025 an appeals court ruled it was too lenient, sending the case back for resentencing.
-
Can I still receive money from the Capital One settlement?
The claims deadline for the $190 million class action settlement was August 2022, so that window has closed. However, identity protection services for those who were eligible remain available through February 2028. If you believe you were affected and missed the deadline, a consumer protection attorney can advise you on whether any individual legal options remain.
-
Was Amazon Web Services responsible for the Capital One breach?
AWS maintained that its systems were not compromised and functioned as designed. The vulnerability was in how Capital One had configured its web application firewall within the AWS environment, not in AWS’s underlying infrastructure. Both Capital One and AWS denied liability in the class action settlement. The OCC’s $80 million fine and enforcement action were directed solely at Capital One, citing its failure to establish adequate cloud security risk assessment processes before migrating sensitive data to the cloud.