PowerSchool is the most widely used student information system in North American K-12 education. It processes grades, attendance, enrollment, health records, and family contact information for schools across the continent. In December 2024, a hacker exploited a basic security gap in PowerSchool’s customer support portal and walked away with the personal data of approximately 62 million students and 9.5 million teachers. It is the largest breach of children’s data in U.S. history.
The attacker was eventually identified, prosecuted, and sentenced to prison. But the data he stole was never fully recovered, and follow-on extortion attempts against individual school districts continued months after PowerSchool paid a ransom. Here is the full account of what happened, who was responsible, what was taken, and what families, students, and school staff can do now to protect their identities.
>> Protect Your Identity: Best Identity Theft Protection Services of 2026
What PowerSchool Is and Why This Breach Mattered
PowerSchool is a cloud-based education technology company headquartered in Folsom, California. Its Student Information System (SIS) is used by more than 18,000 school organizations across 90 countries, serving the records of over 60 million students in the United States and Canada.1 It typically runs in the back-end system of schools to manage everything from enrollment records to health alerts.
Parents who enrolled their children in school, and teachers who worked in those districts, must provide highly sensitive personal information to their schools. Those schools store that information with PowerSchool. The parents and teachers had no way to opt out of PowerSchool, so when it was breached, it impacted them all.
How the Breach Happened
The attack began in September 2024, when the hacker used the credentials of a PowerSchool subcontractor to access PowerSource, PowerSchool’s customer support portal. PowerSource was the tool that PowerSchool’s own engineers used to access school districts’ SIS instances for support and troubleshooting. At the time, PowerSource did not require multi-factor authentication. That means the hackers only needed a username and password to gain access to an administrative maintenance tool with reach across thousands of school districts.
Using that maintenance access in September 2024, the attacker initially accessed data from one school district. He then leased a server from a cloud provider in Ukraine and, between December 19 and 28, 2024, used the same credentials to systematically download student and teacher databases from thousands of districts. That allows him to exfiltrate data at scale before PowerSchool detected the intrusion.2
PowerSchool learned of the breach on December 28, 2024, when the attacker sent the company an extortion demand. This prompted an investigation by the Ontario Information and Privacy Commissioner.3 They found that the lack of mandatory MFA, an “always on” remote maintenance feature, limited log retention, and delayed detection all contributed to the breach’s severity.
Incogni’s automated data broker removal service reduces the footprint of your compromised data.
The Ransom Payment and the Second Wave of Extortion
PowerSchool received a demand for approximately $2.85 million in Bitcoin on December 28, 2024. If it was not paid, the hacker threatened to release the stolen data “worldwide.” PowerSchool’s leadership decided to pay, believing it was in the best interest of the students and communities they served. The attacker provided a video purportedly showing the deletion of the stolen data.4
The payment did not end the extortion. By May 2025, attackers were sending ransom demands directly to individual school districts in Canada and the United States. They included samples of the stolen student data to prove they still held it. PowerSchool stated it did not believe this was a new breach, but that the same data from December was being weaponized to extort downstream customers.5
Who Was Responsible
The hacker was identified as Matthew D. Lane, a student at Assumption University in Worcester, Massachusetts, who was 19 years old at the time of the attack. Lane pleaded guilty in May 2025 to four federal charges: cyber extortion conspiracy, cyber extortion, unauthorized access to protected computers, and aggravated identity theft.
On October 15, 2025, U.S. District Judge Margaret Guzman sentenced Lane to four years in federal prison, followed by three years of supervised release. He was also ordered to pay approximately $14.1 million in restitution and a $25,000 fine. Prosecutors had sought eight years. Lane was required to surrender to federal prison by December 1, 2025.6
Court documents indicate that Lane worked with at least one unnamed co-conspirator. Before targeting PowerSchool, Lane and his co-conspirators also attempted to extort an unnamed U.S. telecommunications company. Prosecutors described Lane as having a history of hacking dating back to 2021, signaling a serious risk of continued criminal conduct. The investigation into other potential participants remains ongoing.
FYI: Some companies invest in cyber insurance to negotiate with cyber extortionists and pay a ransom if deemed necessary. The best cyber insurance companies also provide a 24/7 breach response service to minimize potential damage. Check out our guide on how much cyber insurance costs to see if it could fit into your budget.
What Data Was Stolen
The stolen data came from the student and teacher tables in PowerSchool’s SIS instances. What was in those tables varied based on what each district stored. CrowdStrike’s forensic investigation found no evidence that data was taken from other tables, and PowerSchool confirmed there was no evidence that banking or credit card information was compromised.
| Category | Types of Data That May Have Been Exposed |
|---|---|
| Personal identifiers | Full names, addresses, phone numbers, email addresses, dates of birth |
| Government identifiers | Social Security numbers (for a subset of students and most staff) |
| Health and medical | Medical alert information, health conditions, disability accommodations, individualized education plans (IEPs) |
| Academic records | Grades, attendance, disciplinary records, enrollment history |
| Family information | Parent and guardian names and contact information, bus stops and transportation routes |
| Staff-specific data | Salary information, licensing records, passwords (in some districts) |
PowerSchool noted that fewer than 25 percent of registered students had Social Security numbers stored in the affected system. However, given the total scope of the breach, even that fraction represents a very large number of children. The exposure of SSNs for minors is particularly serious because child identity theft regularly goes unnoticed until they apply for credit or student loans years later.
Legal Consequences and Ongoing Litigation
PowerSchool faces lawsuits on multiple fronts. Multiple class action suits were filed after the breach was disclosed, with plaintiffs alleging negligence, failure to implement adequate security, and failure to provide timely breach notifications.
The Texas Attorney General filed a lawsuit against PowerSchool, alleging that the company failed to implement basic security features including multi-factor authentication, adequate access controls, and proper encryption. Despite the lack of security, PowerSchool marketed its products as meeting “the highest security standards.” The Texas Attorney General also highlighted the exposure of bus stop information, noting it could be used to physically locate children.7
Did You Know: Online behavior can turn into real-world dangers. That’s why we put together a guide to protecting your kids online. One of our top recommendations is to use a high-quality parental control app, so you can identify risky online behavior before it escalates into a dangerous situation.
In Canada, the Ontario Information and Privacy Commissioner released a final report in November 2025. It found that the institutions involved had not maintained reasonable measures to prevent unauthorized access and had not responded adequately to the breach. The report ordered affected Ontario institutions to demonstrate compliance with security and oversight recommendations within six months.
PowerSchool’s breach response cost the company more than $14 million, including the cost of identity theft monitoring for victims. Lane was ordered to pay $14.1 million in restitution, though prosecutors acknowledged that amount would be unlikely to be collected in full. Only about $161,000 in proceeds traced to Lane’s crimes was forfeited.
What Families, Students, and School Staff Should Do
Check Whether Your School Uses PowerSchool
The breach specifically affected schools using PowerSchool’s Student Information System. If your child’s school or your employer district uses PowerSchool SIS, your records were potentially within scope. You can confirm by contacting your school or district’s technology office. PowerSchool said it notified all affected SIS customers and coordinated with Experian and TransUnion to notify affected individuals.
Note the Credit Monitoring Enrollment Deadline
PowerSchool offered two years of complimentary identity protection services through Experian IdentityWorks to affected students (through their parents or guardians) and educators. When we tested Experian IdentityWorks, it provided comprehensive identity and credit monitoring. The enrollment deadline was July 31, 2025, and that window has now closed. If you enrolled before that date, your coverage remains active through its two-year term.
Pro Tip: Missed the enrollment deadline? You can always sign up for a free identity theft protection service with basic identity monitoring. Then, you can monitor your credit by requesting free credit reports and reviewing them for suspicious activity regularly. Alternatively, invest in one of the best credit monitoring services.
Place a Credit Freeze for Children
For children whose Social Security numbers were among the data exposed, placing a credit freeze is especially important and often overlooked. Children do not have established credit files, which means fraudsters can use a child’s SSN to open new credit lines for years without detection. All three major bureaus, Equifax, Experian, and TransUnion, allow parents and guardians to freeze a minor’s credit file for free. This step prevents a credit file from being opened in the child’s name without authorization.
Monitor for Medical Identity Theft
The PowerSchool breach exposed health records, disability accommodations, and individualized education plans for many students. Medical identity theft using a child’s information can result in fraudulent claims being filed under their name or incorrect entries in their medical history. Review your child’s medical records periodically for any entries or services you do not recognize.
Watch for Targeted Phishing Using School Data
The stolen data includes parent and guardian contact information alongside children’s records. That combination allows criminals to craft highly convincing phishing messages targeting parents. Be skeptical of any unsolicited messages referencing your child’s school, grade information, or enrollment details, and verify through known official contact numbers before responding. For more tips, read through our phishing protection guide.
>> Read More: Phishing Text Messages: A Guide to “Smishing”
Contact Your School or District
Because the data exposed varied by district, your school or district is the best source of information about exactly what was stored in their PowerSchool instance and therefore what of yours may have been affected. The U.S. Attorney’s Office in Massachusetts also advised students and teachers who suspect their information was compromised to contact their local school district directly.
Children’s Data Carries Risks That Persist for Decades
Most data breaches affect adults who can take immediate protective steps. The PowerSchool breach is unusual because the majority of its victims are minors. They cannot monitor their own credit or place credit freezes. Plus, identity theft might go unnoticed until they apply for a student loan or a first credit card a decade from now.
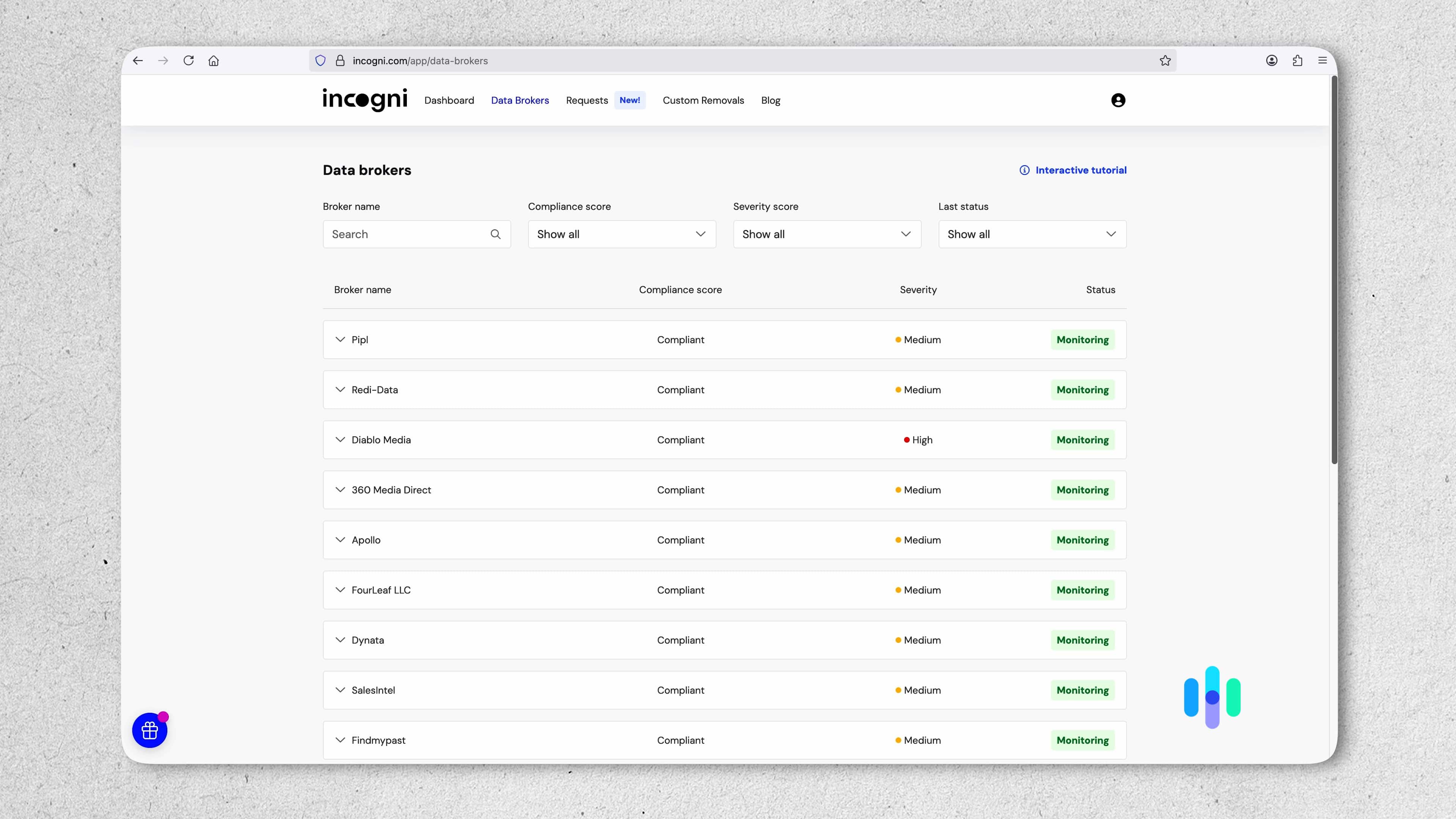
For parents concerned about their family’s broader data exposure beyond this specific breach, data broker removal is a practical layer of protection. Our tests of Incogni revealed its one of the most effective data removal services available. It automatically submits removal requests to data brokers, reducing how much of your family’s information is readily available online. This limits the amount of information criminals can exploit, reducing your downstream risks.
>> Learn About: A 2026 Guide to Data Removal Services
The Bottom Line
The PowerSchool breach is the largest breach of children’s educational data in U.S. history. A single compromised contractor credential, combined with a customer support portal that lacked multi-factor authentication, gave a 19-year-old hacker access to the records of 62 million students and 9.5 million teachers. The hacker was caught, prosecuted, and sentenced to four years in prison. However, the data he stole remains unaccounted for and individual school districts continued to receive extortion demands months after the initial breach.
If your child attends a school that uses PowerSchool, or if you work for a school district that does, your information was within the scope of this incident. To keep yourself and your kids, immediately place a credit freeze, monitor health records, and stay alert to school-themed phishing attempts. You may also want to invest in a data removal service like Incogni to limit the exposure of your personal data.
Frequently Asked Questions
-
What is PowerSchool and why did the breach affect so many people?
PowerSchool is the most widely used student information system in North American K-12 education, serving over 18,000 school organizations and the records of more than 60 million students. Because thousands of school districts store their data on PowerSchool’s centralized platform, a single breach of PowerSchool’s systems exposed data from all of those districts simultaneously. Most affected individuals had no direct relationship with PowerSchool and no knowledge that the company held their or their children’s records.
-
Was my child's Social Security number exposed?
It depends on your district. PowerSchool noted that fewer than 25 percent of registered students had Social Security numbers stored in the affected system, and that data varied by district. Some districts stored SSNs, some stored medical information, and some stored neither. Your child’s school or district is the best source for confirming what was specifically stored in their PowerSchool instance.
-
Who hacked PowerSchool?
Matthew D. Lane, a Massachusetts college student who was 19 at the time of the attack, hacked PowerSchool in 2024 and then demanded a ransom of $2.85 million. Once caught in 2025, he was charged and sentenced to four years in federal prison. He was also ordered to pay $14.1 million in restitution. Prosecutors said Lane worked with at least one unnamed co-conspirator, and the investigation remains ongoing.
-
Did PowerSchool pay a ransom?
Yes. PowerSchool confirmed it paid a ransom after receiving an extortion demand on December 28, 2024. The company received a video purportedly showing the deletion of the stolen data. However, the payment did not prevent further extortion. By May 2025, individual school districts were receiving separate ransom demands using samples of the same stolen data. PowerSchool stated it did not believe this represented a new breach.
-
What should I do if my child's school used PowerSchool?
Contact your school or district to understand exactly what information they stored in PowerSchool and whether that data was affected. Place a credit freeze for your child at all three major credit bureaus, Equifax, Experian, and TransUnion. If enrolled by the deadline, use Experian IdentityWorks to protect your family’s identity. Also, monitor your child’s health records periodically for unfamiliar entries, and stay alert to school-themed phishing attempts that reference personal details from your child’s enrollment records.

