USAA serves a specific and particularly high-value population: active-duty military members, veterans, and their families. That makes any security incident involving the organization more consequential than a typical financial data breach. Military identities carry strong trust signals in the financial system. Plus, the personal data USAA holds, including Social Security numbers, bank account details, and insurance records, is exactly what criminals need to commit fraud or open fraudulent accounts.
Between 2021 and 2024, USAA disclosed three separate security incidents. Each had a different cause, but all involved the personal information of tens of thousands of members being exposed. Here is what happened in each case, who was affected, and what the legal and practical consequences have been.
Expert Insight: USAA provided Experian IdentityWorks for free to those affected by the 2022, 2023 and 2024 breaches. However, this is not the best identity theft protection service available, so you may want to upgrade your protection with a better provider. Also take a read through our guide to identity theft protection for more useful preventive tips.
Three USAA Data Breaches, Three Different Causes
2021: The Insurance Quote Tool Exploit
In May 2021, criminals exploited USAA’s online insurance quote tool in a way the company had not anticipated. The tool was designed to help members quickly get insurance quotes by pulling in their driving records. To help confirm identity, it displayed some personal information back to the user during the process.
The problem was that the tool had no rate limiting and no CAPTCHA controls, meaning it could be queried repeatedly and automatically without raising any alarms. Attackers took previously stolen personal information from other breaches and used it to match against active USAA members, cycling through combinations until they could pull up sensitive data on real accounts. According to the New York State Attorney General, approximately 22,383 individuals were affected, with 12,627 of them in New York alone.1
The exposed data included driver’s license numbers along with other personally identifiable information. USAA removed the vulnerability from its systems and notified those affected. The incident led to class action litigation that eventually produced a settlement.
Incogni’s data removal service finds your personal information online and sends automated removal requests to take it down on your behalf.
2022 to 2023: Third-Party Contractor Credential Sharing
The second incident unfolded over a much longer window. Between December 20, 2022, and May 18, 2023, a small number of call center representatives employed by one of USAA’s third-party service providers improperly shared their access credentials with unauthorized individuals. Those credentials were then used to access USAA member accounts and extract personal data.2
The third-party provider became aware of the situation, blocked the unauthorized access, and notified USAA. The breach affected approximately 19,000 members. It exposed a combination of their names, addresses, phone numbers, email addresses, dates of birth, driver’s license numbers, the last four digits of Social Security numbers, bank account numbers, including debit and credit card numbers, and the PINs members use to authenticate when calling USAA.
FYI: Malicious actors can do an awful lot with just your name and address. That’s why data leaks like this are such a big deal and can carry such severe consequences for victims. We always recommend removing your name from the internet and removing your address from the internet to minimize your risks.
Affected members were not notified until June 26, 2023, more than a month after the breach window closed in May. USAA offered two years of free Experian IdentityWorks credit monitoring to those affected and said it was working with the provider to improve security protocols.
A separate, smaller incident also occurred in August 2023. In this incident, USAA was notified that one bank call center representative employed by a different third-party provider had handled member information inappropriately. That incident exposed the same type of data, including Social Security numbers, PINs, and bank account numbers, although it impacted fewer members.
>> Read About: What To Do If You Lose Your Social Security Card
2024: A System Error Exposes Member Documents
The most recent breach was caused not by an outside attacker or a contractor, but by an internal system error. On April 13, 2024, during a routine update to USAA’s document delivery system, a configuration error caused certain member documents to be posted to the wrong accounts.3 Another member could log in and see documents that did not belong to them.
USAA discovered the error on April 30, 2024, and launched an investigation that concluded on July 31, 2024. The breach affected 32,276 members, including nearly 4,200 Texans. The exposed data included names, addresses, Social Security numbers, driver’s license numbers, dates of birth, medical information, and property and casualty insurance policy information.
On August 27, 2024, USAA began mailing breach notification letters to affected members and offered a complimentary two-year membership to Experian IdentityWorks. The company said its investigation found no evidence of fraud or identity theft resulting from the incident. However, the range of information exposed, including Social Security numbers and medical details, made the potential risk significant.
>> Check Out: Experian IdentityWorks Review 2026
Incidents at a Glance
Here are the highlights of each of the USAA data breaches discussed above:
| Year | Cause | Data Exposed | Members Affected | Response |
|---|---|---|---|---|
| 2021 | Exploited online insurance quote tool (no rate limiting or CAPTCHA) | Driver’s license numbers, PII from driving records | 22,383 | Tool removed; class action settlement reached |
| 2022-2023 | Third-party call center reps shared access credentials | Names, addresses, SSN (last 4), bank account numbers, PINs, driver’s licenses | ~19,000 | Access blocked; 24 months Experian monitoring offered |
| 2023 (Aug.) | Single third-party call center rep mishandled data | Names, SSNs, passwords, PINs, bank account numbers | Undisclosed (smaller) | Experian monitoring offered |
| 2024 | Internal system error during routine update | Names, SSNs, driver’s licenses, DOBs, medical info, insurance policy data | ~32,276 | Error corrected; 24 months Experian monitoring offered |
Who Was Responsible
The causes of USAA’s incidents are more varied than in most large breaches. No single nation-state actor or criminal hacking group has been publicly attributed with any of these incidents. Each breach also occurred due to a different vulnerability.
- The 2021 breach was carried out by opportunistic criminals who leveraged stolen personal data from other breaches to exploit a gap in USAA’s own systems. The lack of rate limiting on the insurance quote tool was an internal design failure that made the attack possible.
- The 2022 to 2023 breach was an insider threat originating with third-party contractors, not a technical exploit of USAA’s systems. A small number of call center employees improperly passed their access credentials to outside parties, a failure of both personnel management and access controls at the third-party vendor level.
- The 2024 incident was an internal configuration error with no external attacker involved. A routine system update was implemented incorrectly, causing documents to be routed to the wrong accounts.
Taken together, these incidents reflect vulnerabilities at multiple levels: the design of public-facing tools, the management of third-party vendor access, and internal change management processes. None required a sophisticated cyberattack to succeed.
>> Learn More: Cyber Security Tips, Facts & Statistics for 2026
Legal Action and the $3.25 Million Settlement
The 2021 insurance quote tool breach generated the most significant legal response. A class action lawsuit was filed in federal court in the Southern District of New York. The lawsuit alleged that USAA’s intentional system design, specifically the tool’s lack of access controls, allowed criminals to extract member data. It also claimed that USAA failed to take reasonable steps to protect member data.
USAA agreed to a $3.25 million settlement fund to resolve those claims.4 The settlement class covers individuals whose personal information was compromised in the May 2021 incident. The estimated payout per eligible claimant was approximately $143, though the final amount depends on the total number of valid claims and legal costs.
The 2024 system error breach also attracted legal attention. A lawsuit filed by Maurice Fitzpatrick alleged that USAA was negligent in its system update process. The lawsuit also alleged that USAA took too long to notify affected members after discovering the error in April, but did not send notices until August. USAA has not admitted wrongdoing in connection with any of these incidents.
Did You Know: Most companies are required to report data breaches to those affected. One reason for this requirement is to reduce the number of account takeover instances. If you know malicious actors have access to your personal information, you’re more likely to identify phishing text messages and other attacks as you’ll be on the lookout for them.
What USAA Members Should Do
Check Whether You Were Notified
USAA sent breach notification letters by mail to affected members after each incident. If you received a notification letter from USAA related to any of these incidents, it confirms that your information was involved. Members who are uncertain whether they were affected can log in to their USAA account or contact USAA member services directly to ask.
Check Have I Been Pwned
Entering your email address at Have I Been Pwned (haveibeenpwned.com) is a useful secondary check. While not all USAA breach data has been indexed there, it can surface exposure from related incidents and provide a broader picture of where your credentials have appeared.
Activate the Free Credit Monitoring USAA Offered
USAA offered affected members either 24 months of free Experian IdentityWorks credit monitoring (for the 2022 to 2023 and 2024 incidents) or similar identity protection. If you received a notification letter with an engagement number, contact Experian directly using the number provided in the letter to activate your monitoring before it expires.
Change Your USAA PIN and Account Credentials
The 2022 to 2023 contractor breach exposed PINs that members use to authenticate when calling USAA, as well as bank account numbers. If you were affected by that incident and have not already changed your USAA PIN and account password, do so immediately. Treat any account linked to an exposed credential as compromised until you have updated it. You can use our password generator to create secure credentials for your compromised accounts.
>> Read More: How Secure Is My Password? | Password Strength Checker
Place a Credit Freeze
Given that Social Security numbers were exposed in both the 2022 to 2023 contractor breach and the 2024 system error, a credit freeze is among the most protective steps available. It prevents new credit from being opened in your name without your authorization and is free to place and lift at all three bureaus: Equifax, Experian, and TransUnion. We also recommend requesting a free credit report from all three bureaus and confirming accuracy.
Be Alert to USAA-Themed Phishing
Because USAA serves a specific and identifiable population, criminals who obtain USAA member data can use it for phishing attacks designed to look like legitimate USAA communications. Be skeptical of unsolicited calls, texts, or emails claiming to be from USAA. Most importantly, never provide your account credentials or personal information to someone who contacts you first. USAA will never call you and ask for your password or PIN. For more tips, read through our guide to phishing protection.
Why Military Members Face Elevated Risk After a Breach
USAA’s membership is not a random cross-section of the public. Military members and veterans are considered high-trust identities in the financial system. That makes their data more valuable to criminals than average consumer data. A fraudster working from stolen USAA member information can attempt to exploit that perceived trustworthiness in applications for credit, benefits claims, and account takeovers.
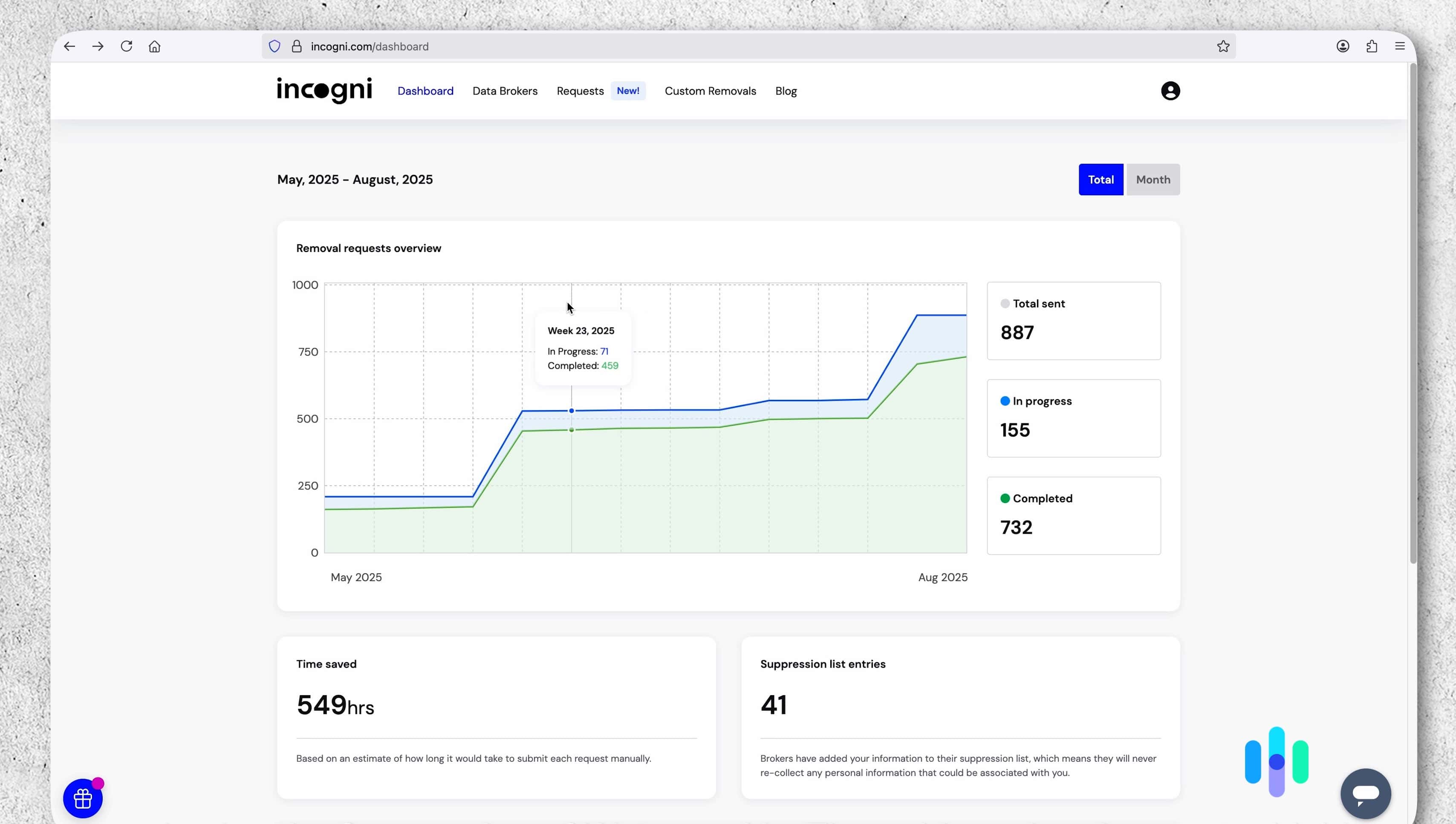
For members concerned about how broadly their personal information is circulating, data broker removal services can help. When we tested Incogni, it automatically removed our data from over 700 data brokers in just three months. This reduces the footprint criminals can work from when targeting individuals with stolen data. It addresses a different layer of the problem than a credit freeze does, and the two approaches work well together.
The Bottom Line
USAA’s breach history between 2021 and 2024 covers three distinct types of failures: a design gap in a public-facing tool, a third-party insider threat, and an internal configuration error. The total number of members directly affected across all incidents is estimated at over 73,000. That said, the full scope may be broader given the smaller, undisclosed second contractor incident in 2023. Each breach involved sensitive financial and personal data, and the population served makes that exposure particularly serious.
If you are a USAA member, check your notification status to see if you were involved in a breach. Then, activate any credit monitoring USAA offered, update your account credentials, and place a credit freeze if your Social Security number was exposed. The $3.25 million settlement related to the 2021 breach is currently open for claims if you are a victim. Also consider investing in a data removal service like Incogni to minimize the spread of your personal information.
Frequently Asked Questions
-
Has USAA had multiple data breaches?
Yes. USAA disclosed at least three distinct security incidents between 2021 and 2024. The first, in May 2021, involved the exploitation of an online insurance quote tool. The second ran from December 2022 through May 2023 and involved third-party call center employees improperly sharing access credentials. The third, in 2024, was caused by an internal system error during a routine update that posted member documents to the wrong accounts.
-
What information was exposed in the USAA data breaches?
The data exposed varied by incident. The 2021 breach primarily involved driver’s license numbers and other PII pulled from driving records. The 2022 to 2023 contractor breach exposed names, addresses, phone numbers, email addresses, dates of birth, driver’s license numbers, the last four digits of Social Security numbers, bank account and card numbers, and account PINs. The 2024 system error exposed names, full Social Security numbers, driver’s license numbers, dates of birth, medical information, and insurance policy details.
-
Is there a USAA data breach settlement I can claim?
A $3.25 million class action settlement was reached in connection with the 2021 breach. The settlement class covers individuals whose information was compromised in that incident. A final approval hearing occurred in May 2025. Currently, the settlement is open for claims.
-
How do I know if I was affected by the USAA data breach?
USAA mailed breach notification letters to affected members after each incident. If you received one, your data was involved. You can also log into your account or contact USAA member services to ask about your specific status if you’re uncertain whether your data was leaked. Checking your email address at Have I Been Pwned is also a useful step, though it may not capture all USAA-specific breach data.
-
Why are USAA members at higher risk of data breaches?
Military members and veterans are considered high-trust identities in the financial system, meaning their credit profiles are often viewed favorably by lenders. This makes them attractive targets for identity fraud, as criminals can potentially use stolen USAA member data to open accounts or apply for loans. Some criminals may also attempt to file fraudulent benefits claims. Targeted phishing attacks are also a heightened risk, since criminals with USAA member data can craft communications that appear highly specific and credible.

