What's the Difference Between a Proxy and a VPN?
Proxy servers and VPNs have some overlap, but their differences are actually pretty vast.
If you’re reading this, then you probably want to change your IP address, but maybe you want to encrypt all of your web activity, as well. Which one should you use, a VPN or a proxy server? Each has its advantages and disadvantages, so we’ll help you make a well-informed and quick decision.

What Are Proxy Servers and VPNs?
Let’s start with the basics, what is a VPN, and what is a proxy server.
VPNs
VPNs are Virtual Private Servers that encrypt all of a users’ web activity and device IP addresses. Typically, they come in the form of either an app or a browser extension. To learn more about VPNs in general, read our VPN guide.
Proxy Servers
A Proxy server, on the other hand, is a computer that stands between the user and their server that hides only their device IP address, not all of their web activity. It also works on one website or app, not several. We see the following types of proxy servers most commonly:
- SOCKS5: Many people opt to use SOCKS5 for things like file sharing, video streaming, and online gaming, but it’s much slower than HTTP, coming up next.
- HTTP: HTTP is a proxy server commonly used to access geo-restricted websites. If you live in a country with high levels of internet censorship, HTTP is a good option for you.
- Transparent: Proxy servers aren’t just used to unlock certain websites. They can also be used for the opposite purpose. You know how you can’t go on Facebook at those computers in your public library? Well, that’s because those pesky librarians may have used a transparent proxy server, which blocks certain websites from view. Colleges and employers use these servers frequently, as well.
FYI: You might need a VPN to bypass your transparent proxy server, which restricts access to certain websites.
Proxy vs. VPN
Depending on your needs, you might want to use a proxy server or a VPN, but most likely a VPN will be more convenient. Let’s break down why.
| Feature | Proxy | VPN |
|---|---|---|
| Cost | Usually free | Usually paid |
| Number of uses | 1 | Unlimited |
| Encrypt IP address | Yes | Yes |
| Encrypt web activity | No | Yes |
| Sells user data | Yes | No |
| Coverage | 1 website or app | All websites and apps |
| Compatible with streaming and gaming | Yes | Yes |
| Can be used to bypass geo-restrictions | Yes | Yes |
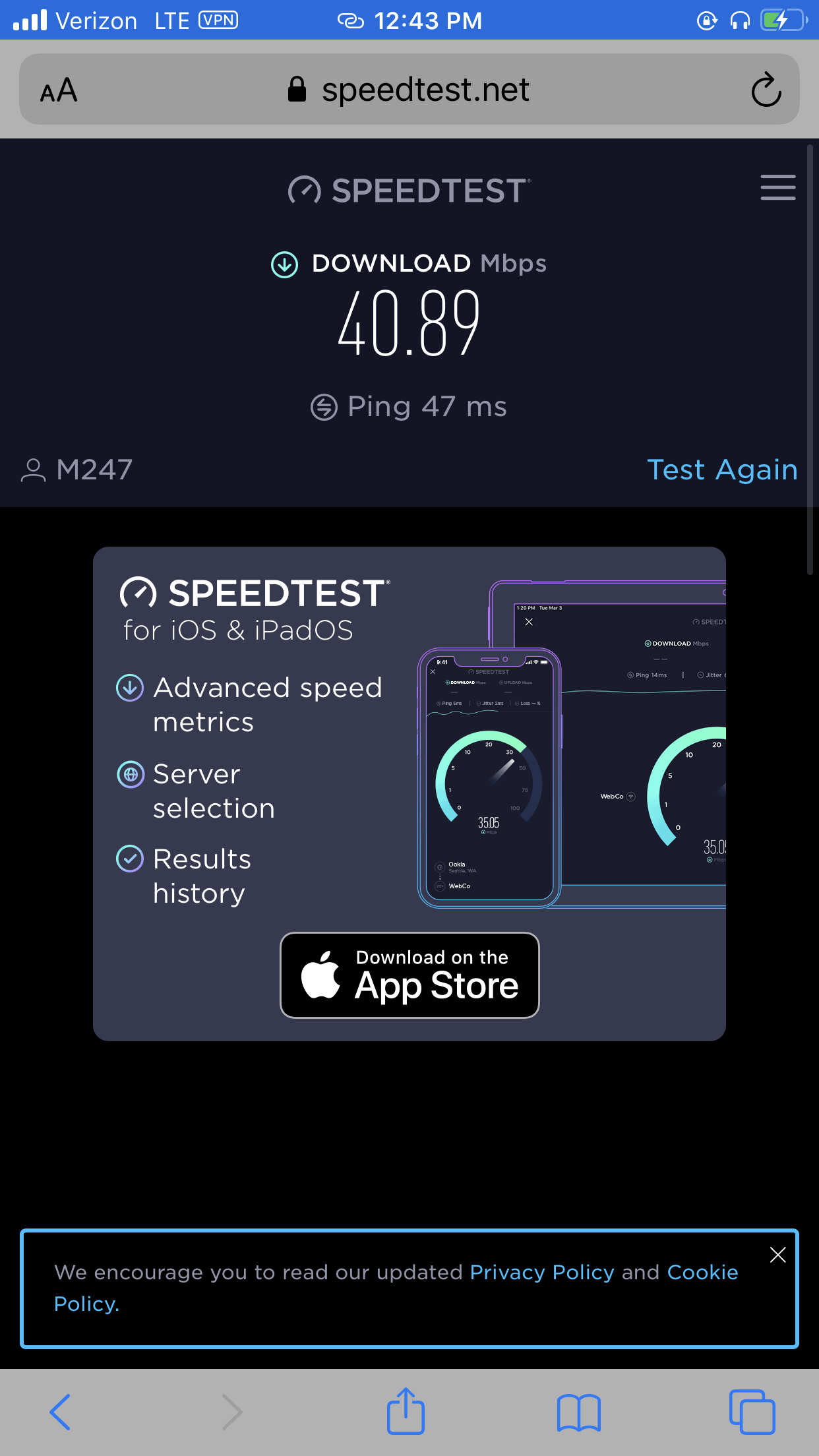
| Slows down browsing speeds | Yes | Yes |
Key Differences
First, let’s talk about the major differences between VPNs and proxy servers.
- Encryption: The main difference between a VPN proxy and a VPN is encryption. VPNs hide not only your private IP address but all your web activity, such as the websites you visit, using encryption. Proxy servers, on the other hand, will only change your IP address, but they won’t encrypt your online activities.
- Selling data: Most proxy servers are free, and to make up for this lack of charge, many will sell user data to advertisers. Most VPNs on the other hand are paid and do not log or share user traffic data.
- Paid vs. free: While there are many free VPNs options available, the majority have limits on how much data you can use per day, how many servers you can switch to, and more. For most people, it makes sense to invest in a paid option, whereas the majority of proxy servers are free.
Pro Tip: Many VPNs offer discounts for students, usually through Student Beans. If you’re a student who needs your web activity completely protected, take advantage of these discounts, which can range from 15 to 80 percent.
- Coverage: While VPNs encrypt all of a user’s web activity, no matter the website or app, proxy servers only hide one website or app at a time.
Key Similarities
Searching for common ground, here’s what we came up with.
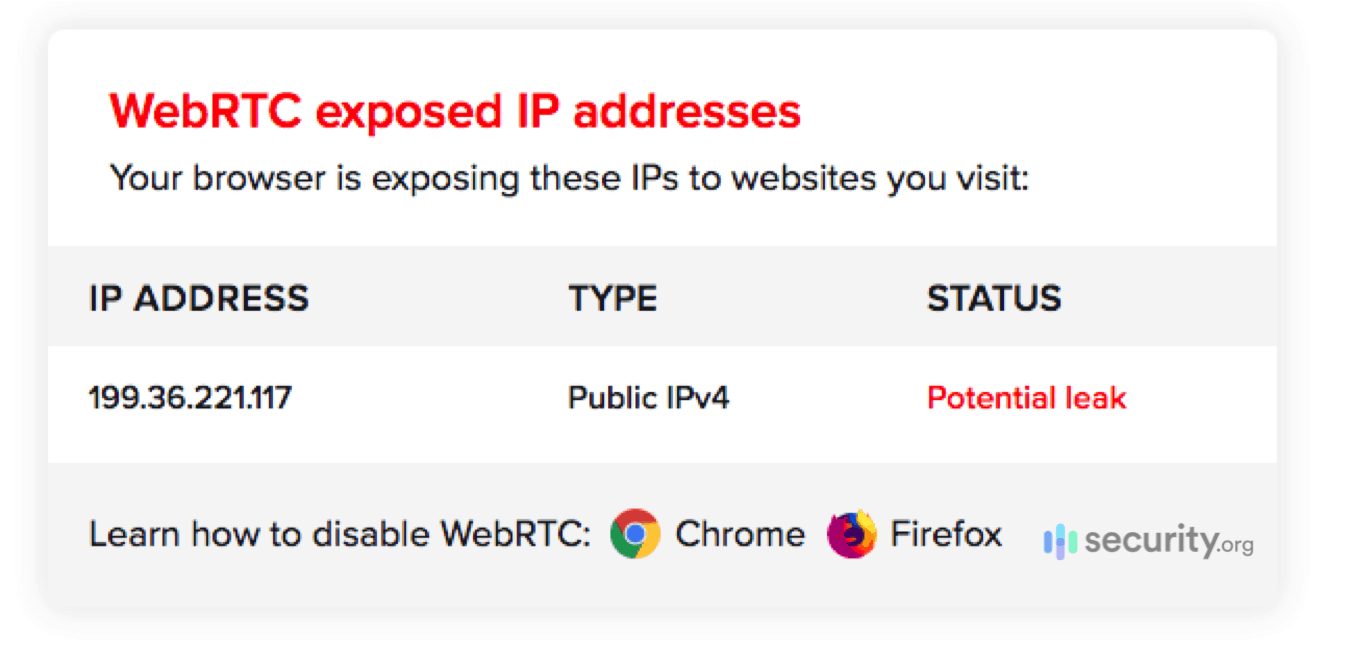
- Hide IP addresses: Both VPNs and proxy servers will hide your device IP address.
- Streaming and gaming-compatible: Both work with streaming services and gaming consoles, although for proxies, you must use a SOCKS5.
- Slow down browsing speeds: Both methods will slow down your browsing speeds at least a little (but we’ll admit that proxy connections are typically slower than VPN connections).
- Bypass geo-restrictions: If you want to get around a government’s internet restrictions, both a VPN and a proxy server could get the job done.
Do You Need Both?
In a word, no, it’s not necessary to download a proxy if you already have a VPN. VPNs encompass what proxy servers do, so the redundancy isn’t needed.1 However, if you have a transparent proxy server that’s blocking certain websites, you may need a VPN to bypass these restrictions.2
Which One Should You Use? How To Choose
Now here comes the moment of truth, should you use a proxy server or a VPN? We’ve made the case for each and played devil’s advocate.
Why You Should Use A VPN
- Coverage of all websites and apps: If you want more than one website or app covered, then a VPN is the easiest option.
- Encryption of web traffic: It’s also the only option if you want your websites visited to be encrypted and not just your device’s IP address
- No traffic logging: Most VPNs won’t log any of your traffic, which isn’t the case for proxy servers.
- Better speeds: While speeds differ greatly from VPN to VPN, in general, they’re faster than proxy servers.
Why You Shouldn’t Use A VPN
- If you need one-time use only: If that’s the case, using a proxy server will probably be easier and cheaper.
- May have to pay: Again, there are some VPNs that are completely free or have free trials, but in general, VPNs usually cost money while proxies are free.
Why You Should Use A Proxy Server
- Only need one website or apps’ IP address hidden: If you need a one-and-one, getting a proxy server to cover a single website or app will be easier than downloading a VPN.
- No payment required ever: No payment, no problem!
Why You Shouldn’t Use A Proxy Server
- Doesn’t encrypt web traffic: Your Internet Service Provider will still be able to see exactly what you do online, just not your device’s IP address.
- Logs and sells web traffic: Not only will proxy servers log your web activity, but they’ll also sell it, potentially to third-party advertisers.
- Only works on a single website or app: Most people are going to want protection for all of their web activity.
Recap
While proxy servers certainly have their purpose, VPNs are a much more comprehensive and effective way to stay private online. If you’re not sure where to start, check out our rankings of the best VPN for every occasion.
FAQ Section
That about covers it, but we’re still with you for any final questions.
-
Is a proxy server the same as a VPN?
Proxy servers are not the same as VPNs. While proxy servers can encrypt the IP address of a single website or web app, VPNs encrypt all web activity.
-
Is Tor a VPN or a proxy server?
Tor is neither a VPN nor a proxy server. Rather, it’s a secure browser that hides its web activity from your Internet Service Provider.
-
Are proxy servers safe?
Proxy servers are safe to use in that you probably won’t get a virus; however, your data may be shared and sold with third parties for advertising purposes, so they’re not great for protecting your web activity.
-
Is SOCKS5 the same as a VPN?
SOCKS5 is not the same as a VPN. Rather, SOCKS5 is a type of proxy server that’s typically used for online gaming, sharing files or video chatting on a single website or app. VPNs, on the other hand, encrypt all web activity across all websites and apps.
-
Norton. (2021). Proxy vs. VPN: 4 differences you should know.
us.norton.com/internetsecurity-privacy-proxy-vs-vpn.html -
StackPath. (2016). What is a Transparent Proxy?
blog.stackpath.com/transparent-proxy/