Editor’s Note: If your personal information was exposed in the 2025 TransUnion data breach, we highly recommend subscribing to a high-quality identity theft protection service. As we discuss in our guide to identity theft protection, these services offer active identity monitoring and restoration support to minimize your risks.
TransUnion is one of the three major U.S. credit bureaus, tracking financial data on more than 260 million Americans. That scale makes any breach involving the company significant. The data it holds is precisely what criminals need to commit identity theft, open fraudulent accounts, and impersonate people in the financial system.
TransUnion has been involved in two notable security incidents in recent years. A 2022 breach targeted its South Africa division, resulting in an extortion demand and regulatory enforcement action. Then in July 2025, a far more serious incident struck its U.S. operations, compromising the Social Security numbers and personal information of more than 4.4 million Americans. Here is what happened in each case and what it means for affected consumers.
The 2025 U.S. Breach: A Salesforce Third-Party Attack
What Happened
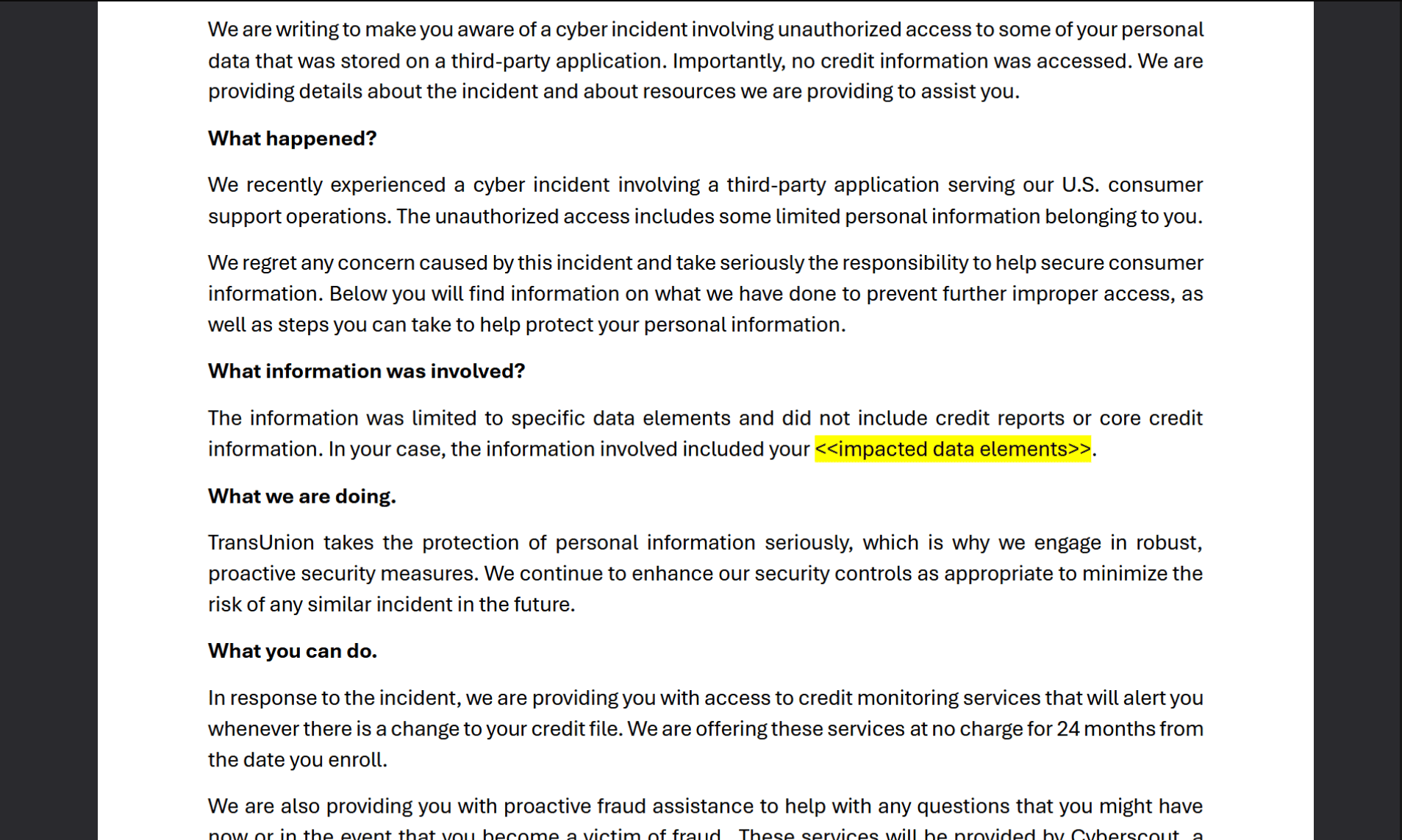
On July 28, 2025, attackers gained unauthorized access to a third-party application used by TransUnion’s U.S. consumer support operations. TransUnion identified and contained the incident within hours, designating July 30, 2025 as the official date of discovery to reflect its completed initial assessment.1
TransUnion emphasized that its core credit database and credit reports were not compromised in the incident. The breach was confined to a connected application used for customer support workflows, not the primary systems that store consumer credit files. That distinction matters for understanding the risk, but the data that was exposed is still deeply sensitive.
The stolen data, confirmed through a copy of TransUnion’s breach notification letter filed with the Maine attorneys general, included names, dates of birth, Social Security numbers, billing addresses, email addresses, phone numbers, reasons for customer transactions, and customer support tickets and messages.2 The attackers themselves claimed to have taken 13 million records in total, though TransUnion’s official count of affected U.S. consumers is 4,461,511.
>> Check Out: How To Check If Someone Is Using My Identity in 2026
Who Was Responsible
The breach is attributed to ShinyHunters, the prolific extortion-focused hacking group that has been responsible for a string of high-profile incidents in 2024, 2025, and 2026.3 The group has also been linked, under the alias UNC6040 or Scattered Spider, to a wave of Salesforce-connected attacks.4 These attacks hit dozens of organizations in the summer of 2025, including Google, Cisco, Adidas, Dior, Louis Vuitton, and Allianz Life.
The attack method in these Salesforce-linked breaches involved exploiting OAuth tokens and social engineering tactics to compromise integrations between third-party applications and Salesforce, rather than attacking Salesforce’s core platform directly. Salesforce confirmed that its own systems were not breached. The vulnerability existed in how organizations had configured their connected applications.
Try Incogni risk-free for thirty days to start removing your leaked data from data brokers and people search sites.
Response and Legal Fallout
TransUnion began sending breach notification letters to affected consumers in late August 2025 and offered two years of free credit monitoring and identity theft protection through its My TrueIdentity service. The company also engaged law enforcement and third-party cybersecurity experts for an independent forensic review.
Multiple class action lawsuits followed in the Northern District of Illinois. On December 16, 2025, the Judicial Panel on Multidistrict Litigation consolidated them into a single proceeding: In re Trans Union, LLC, Customer Data Security Breach Litigation (MDL No. 3170). The consolidated litigation is proceeding in the Northern District of Illinois, with plaintiffs seeking damages and injunctive relief requiring TransUnion to strengthen its vendor oversight and security controls.
FYI: TransUnion also owns IdentityForce, another identity theft protection service. When we tested IdentityForce, we found it offered more comprehensive protection as My TrueIdentity focuses more on credit monitoring. Despite its broader scope, IdentityForce is still among the best credit protection options.
The 2022 South Africa Breach: Stolen Credentials and a $15 Million Ransom Demand
What Happened
In March 2022, a Brazilian hacking group calling itself N4aughtysecTU gained access to a TransUnion South Africa server using the stolen credentials of an authorized client. The group claimed to have accessed and downloaded 4 terabytes of data, and demanded a ransom of approximately $15 million in Bitcoin in exchange for not publishing the stolen files. TransUnion South Africa refused to pay.5
The hackers claimed they gained entry because the compromised client account was protected by a password of “password.” TransUnion did not confirm or deny the specific password, but acknowledged that unauthorized access had occurred through misuse of a client’s credentials.
TransUnion confirmed that at least 3 million South African consumers were directly impacted. An additional 6 million ID numbers were identified where personal details could not yet be linked to specific individuals. The attackers also released what they claimed was a dataset of 54 million records. TransUnion stated that the bulk of that figure, beyond the data from its own server, related to a 2017 data incident from an unrelated source.
The data exposed in the South Africa breach included names, South African ID numbers, dates of birth, gender, contact details, marital status, employer information, vehicle finance contract numbers. In rare cases, the data also included passport numbers, credit or insurance scores, and spouse information.
>> Read More: What is Personally Identifiable Information (PII)?
Regulatory Consequences
South Africa’s Information Regulator investigated the breach and issued an enforcement notice to TransUnion in early 2024.6 The regulator found that TransUnion had violated the conditions for lawful processing of personal information in multiple ways. It failed to secure the confidentiality of data in its possession, implement appropriate access controls, detect failures in those controls, prevent unauthorized access through compromised credentials and a weak password, and follow its own information security policies.
TransUnion was given until May 26, 2024 to implement remedial measures and submit proof of compliance to the regulator. The enforcement action marked one of the most significant regulatory responses to a credit bureau data breach in South Africa’s history.
Incidents at a Glance
Here’s a quick breakdown of both TransUnion data breaches:
| Year | What Happened | Data Exposed | People Affected | Attributed To |
|---|---|---|---|---|
| 2022 | Attacker used stolen (and weak) client credentials to access South Africa server; $15M ransom demanded | Names, ID numbers, DOBs, contact details, employer info, vehicle finance data, some passport/credit score data | 3M+ South Africans confirmed | N4aughtysecTU (Brazil) |
| 2025 | Attackers exploited third-party Salesforce-connected app used for U.S. consumer support | Names, SSNs, DOBs, addresses, emails, phone numbers, customer support messages | 4,461,511 U.S. consumers | ShinyHunters / UNC6040 |
What You Can Do Now
Check Whether You Were Notified
TransUnion sent data breach notification letters to all 4,461,511 U.S. consumers affected by the 2025 breach. If you received a letter, your personal information, including your Social Security number, was compromised. If you are unsure whether you received a notification, you can contact TransUnion’s Fraud Victim Assistance Department at 800-680-7289.
Activate the Free Credit Monitoring TransUnion Offered
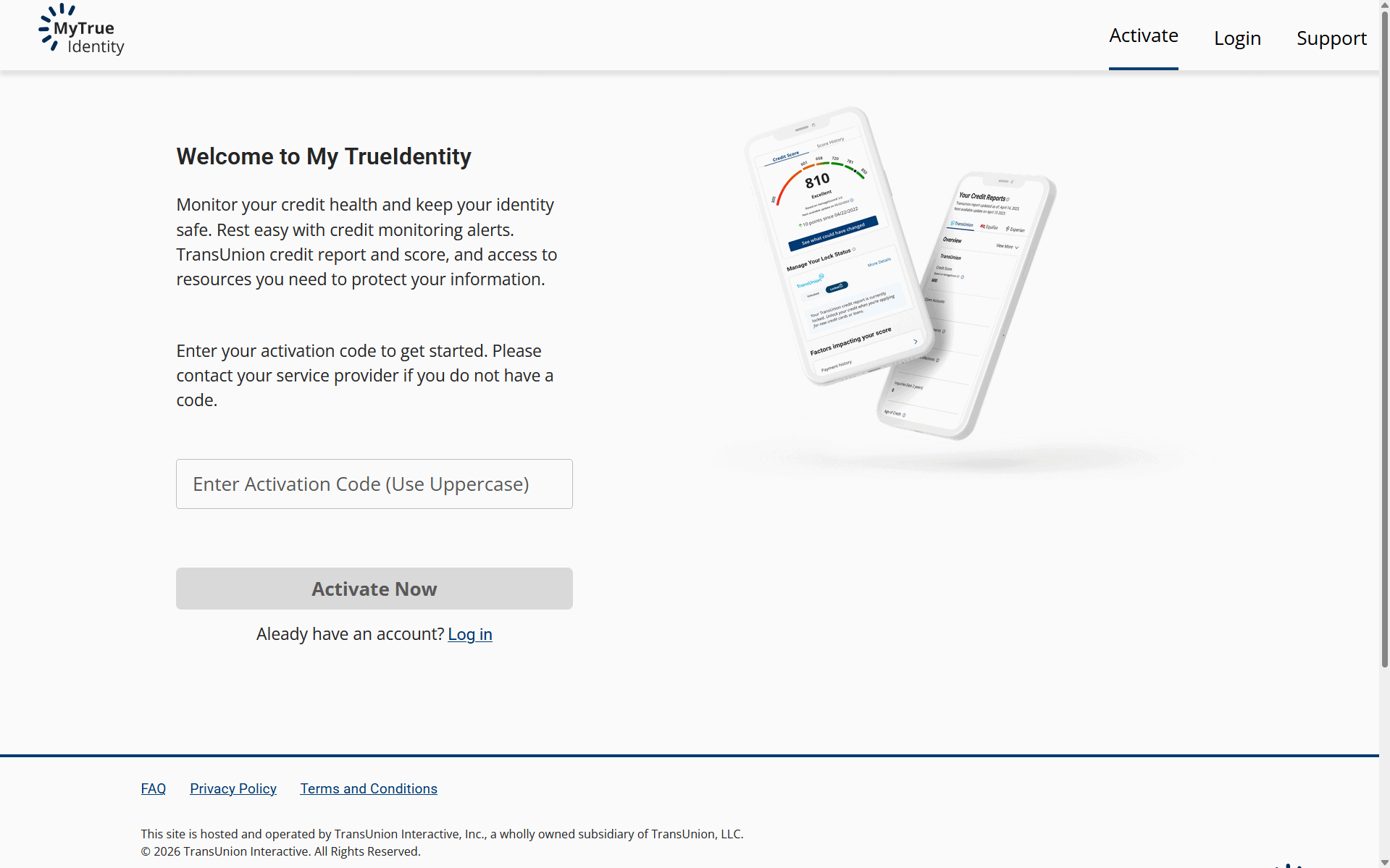
TransUnion is providing affected U.S. consumers with 24 months of free credit monitoring and identity theft protection through its My TrueIdentity service. If you received a notification letter, it will include instructions and an enrollment code. Activate this before it expires, and consider also monitoring your credit files at Experian and Equifax, since identity thieves rarely limit their activity to a single bureau’s data.
Place Credit Freezes at All Three Bureaus
Given that Social Security numbers are part of the stolen data, a credit freeze is the most protective step available. You need to place freezes separately at all three credit bureaus: TransUnion, Equifax, and Experian. All are free and can be done online through each bureau’s website. A credit freeze prevents new credit from being opened in your name without your explicit authorization.
Monitor Your Credit Reports
Request your free credit reports from all three bureaus. Then, review each report for accounts, inquiries, or changes you do not recognize. Pay particular attention to any new accounts or hard inquiries that appeared after July 2025. The stolen data, which includes SSNs and addresses, is exactly what is needed to open new credit lines in your name.
Watch for Targeted Phishing
The stolen data includes customer support messages and the stated reason for customers’ transactions with TransUnion. That means attackers have context about why you were interacting with the company, allowing them to craft highly specific phishing attacks that reference your actual account history. Be skeptical of any unsolicited emails or calls claiming to be from TransUnion or related services. Also, never provide personal information or account credentials in response to a contact you did not initiate. We cover all this and more in our guide to phishing protection.
>> Learn More: Phishing Text Messages: A Guide to “Smishing”
File a Fraud Alert If You See Suspicious Activity
If you notice unfamiliar accounts or inquiries on your credit report, file a fraud alert with any one of the three major bureaus. A fraud alert is free and requires creditors to take extra verification steps before opening new accounts in your name. The bureau you contact is required by law to notify the other two. You can also report suspected identity theft to the FTC at IdentityTheft.gov, which will help you build an individualized recovery plan. If you invest in one of the best identity restoration services, they’ll handle most of this for you.
Pro Tip: Account takeover fraud is a serious concern if your data was in the 2025 TransUnion leak, although it’s far from the only type of fraud. Read through our guide on how to avoid scams to learn easy-to-implement tips that minimize your risk.
The Problem With Breaches at Data Aggregators
There is something particularly uncomfortable about a credit bureau being breached. Most data breach victims made a conscious choice to share their information with the company that lost it. TransUnion’s customers often did not. The company accumulates financial data on hundreds of millions of people as part of its ordinary business operations, with or without those individuals ever directly interacting with it.
That’s how data brokers function as well, sourcing data from public records, purchase histories, and prior breached data to build and sell profiles of people. Data removal services like Incogni limit this exposure. When we tested Incogni, it automatically removed our information from over 700 sites in three months. If your SSN has already been stolen, reducing what else can be pieced together about you can help minimize potential damage.
The Bottom Line
The 2025 TransUnion breach is significant on its own: 4.4 million Social Security numbers exposed through a third-party application is a serious incident regardless of whether it touched TransUnion’s core credit database. And it sits within a broader pattern. The same ShinyHunters group responsible for this breach has been linked to attacks on dozens of other organizations through the same Salesforce-connected application vulnerability. That makes it one of the more consequential hacking campaigns of 2025.
If you received a notification letter from TransUnion, activating the free credit monitoring, placing freezes at all three bureaus, and reviewing your credit reports for unfamiliar activity are the three steps most likely to limit the downstream impact. The consolidated class action litigation in the Northern District of Illinois is ongoing, and any eventual settlement may create an opportunity for affected consumers to file claims.
Frequently Asked Questions
-
Did TransUnion have a data breach?
Yes. TransUnion disclosed a breach on July 28, 2025 that affected 4,461,511 U.S. consumers. The breach was traced to unauthorized access to a third-party application used in TransUnion’s consumer support operations. A separate incident in March 2022 affected TransUnion’s South Africa division, compromising the personal data of at least 3 million South African consumers.
-
What information was stolen in the 2025 TransUnion breach?
The data compromised in the 2025 breach included names, Social Security numbers, dates of birth, billing addresses, email addresses, phone numbers, and customer support messages. It also included the stated reason for customers’ interactions with TransUnion, such as a request for a free credit report. TransUnion confirmed that core credit reports and credit scores were not part of the exposed data.
-
Who hacked TransUnion?
The 2025 U.S. breach has been attributed to ShinyHunters, also tracked as UNC6040 or Scattered Spider. The group carried out the same type of attack against dozens of other organizations in the summer of 2025, exploiting OAuth token vulnerabilities in Salesforce-connected applications. The 2022 South Africa breach was claimed by a separate Brazilian group called N4aughtysecTU.
-
Is there a class action lawsuit against TransUnion for the 2025 breach?
Yes. Multiple class action lawsuits were filed after TransUnion notified consumers in late August 2025. On December 16, 2025, the Judicial Panel on Multidistrict Litigation consolidated the cases into a single proceeding, In re Trans Union, LLC, Customer Data Security Breach Litigation (MDL No. 3170), in the Northern District of Illinois. The litigation is ongoing and no settlement has been announced.
-
I did not directly give TransUnion my information. Can I still be affected?
Yes. TransUnion compiles credit and financial data on hundreds of millions of Americans as part of its standard operations, drawing on information provided by lenders, creditors, and public records. You do not need to have directly signed up for a TransUnion service to have your information in their system. If you have ever applied for a loan, credit card, or mortgage, there is a strong chance TransUnion holds a file on you. The 4.4 million people notified in the 2025 breach are those whose data appears in the specific support system that was compromised, not the full extent of TransUnion’s database.

