If you’ve ever visited a high-traffic website without it crashing, or noticed that major platforms seem to brush off cyberattacks without missing a beat, there’s a good chance a reverse proxy was working behind the scenes. It’s one of those foundational technologies that quietly keeps the internet running, but most people have never heard of it.
That’s why we had our cybersecurity experts break down what a reverse proxy is, how it works, and its common uses. They share similarities with virtual private networks (VPNs), although they protect web servers instead of users. We’ll also discuss a few key risks of running a reverse proxy. Let’s dig in.
>> Check Out: The Best VPN Services of 2026
What Is a Reverse Proxy?
Think of a reverse proxy as a bouncer at the front door of a building. Visitors (your web traffic) never walk straight into the building — they talk to the bouncer first. The bouncer checks who they are, decides where they should go inside, and delivers the response back to them. Strangers can’t get into the actual rooms inside the building (your origin servers) without being vetted by the bouncer first.
That’s the core of what a reverse proxy does. It’s a server that sits in front of one or more web servers to intercept and forward requests from clients. This can increase security, performance, and reliability.1
Forward Proxy vs. Reverse Proxy: What’s the Difference?
This is where people get tripped up, so let’s sort it out clearly.
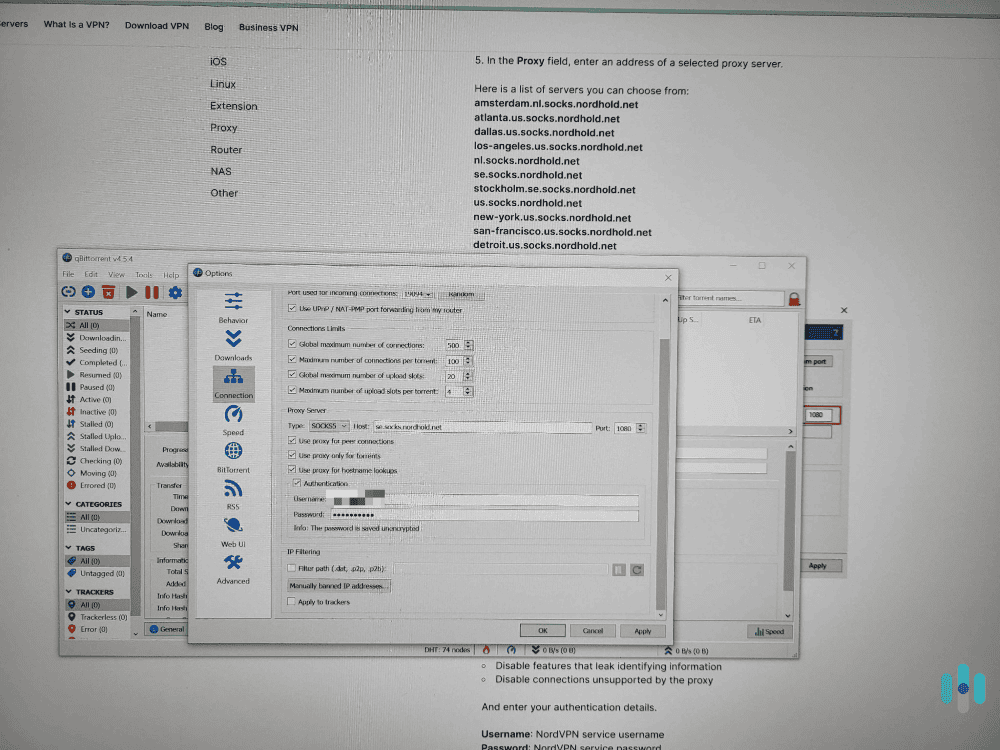
A forward proxy acts on behalf of the client — the person browsing the internet a.k.a. you. It sits between your device and the internet, forwarding your requests outward. This is what most people refer to when they discuss using a proxy server. Putting a server between you and the internet hides your identity from the websites you visit. VPNs use similar logic on the client side with additional encryption for added security and privacy.
Reverse proxies flip the perspective entirely. Instead of representing the client, it represents the server. It intercepts incoming traffic from users and manages how those requests reach the backend infrastructure.
Here’s a quick comparison:
| Forward Proxy | Reverse Proxy | |
|---|---|---|
| Sits in front of | Clients (users) | Servers (web infrastructure) |
| Hides identity of | The user | The origin server |
| Primary use | Privacy, access control | Security, load balancing, performance |
| Typical users | Individuals, corporate networks | Businesses, web applications |
How Does a Reverse Proxy Work?
To prevent any slowdowns for users, reverse proxies use a seamless and efficient process that quickly vets and routes incoming traffic. Here’s the six-step process that reverse proxies use to operate:
- A user types a URL into their browser and hits Enter.
- The request travels across the internet and hits the reverse proxy server — not the actual web server.
- The reverse proxy evaluates the request: Is it legitimate? Which backend server should handle it? Is a cached version available?
- It forwards the request to the appropriate backend server.
- The backend server sends the response back to the reverse proxy.
- The reverse proxy delivers that response to the user.
The user never interacts with the origin server directly. From their perspective, they just loaded a webpage. But underneath, an entire layer of traffic management just happened invisibly.
Expert Insight: In everyday life, middlemen get a bad reputation — they add complexity and cost without adding value. A reverse proxy is the opposite. By intercepting traffic before it reaches your servers, it adds security, performance, and redundancy without the user ever noticing. It’s the kind of invisible infrastructure that makes the modern web feel fast and reliable.
What Does a Reverse Proxy Actually Do?
Now that you understand how reverse proxies work, let’s dig into a few of their features to further illustrate the value they provide.
Load Balancing
When a website gets hit with thousands of simultaneous requests, a single server can’t handle it alone. A reverse proxy distributes incoming traffic across multiple backend servers to prevent any single server from getting overwhelmed and crashing. In the event that a server goes down, reverse proxies act as a failover solution. They reroute traffic to a server that’s up, ensuring continued site availability.
This is why massive platforms — social networks, e-commerce sites, streaming services — can stay online during traffic spikes without slowing to a crawl.
DDoS Protection and Attack Mitigation
In addition to load balancing, reverse proxies also help thwart DDoS attacks. These attacks continue to grow in both frequency and scale year after year with the last quarter of 2025 seeing the largest attacks reported thus far.2
A reverse proxy absorbs the flood of data sent during a DDoS attack, preventing it from ever reaching the target server. Even if an attacker successfully targets the reverse proxy, the backend infrastructure is still shielded — and the proxy is built to take these kinds of hits.
>> Learn More: What is a Data Breach and How to Prevent a Breach in 2026
Web Application Firewall (WAF) Capabilities
Many reverse proxies integrate WAF functionality, filtering out malicious requests before they reach your application. This protects against:
- SQL injection attacks
- Cross-site scripting (XSS)
- Bad bots and scrapers
- Known exploit patterns and vulnerability probes
While not as common as DDoS attacks, these web application attacks still pose a threat. In 2024, SQL injection attacks were in the top five most common types of web application and API attacks of which there were over 300 billion.3 WAF intercepts these types of attacks before they can reach your backend and cause damage.
>> Learn About: What Is an SPI Firewall and How Does it Work?
SSL/TLS Termination
Managing SSL certificates and encrypting/decrypting HTTPS traffic uses a lot of server resources. Rather than taxing every backend server with this work, a reverse proxy can handle all SSL termination in one place. It can decrypt incoming traffic, inspect it, and re-encrypt if needed before passing it along. This offloads processing overhead and centralizes certificate management to servers optimized for this purpose.
Caching
A reverse proxy can store (cache) frequently requested content. The next time a user requests the same page or asset, the proxy serves it directly without bothering the backend server at all. This speeds up load times and reduces server strain.
IP Address Masking
The web servers can be hidden behind a firewall on a company-internal network, with only the reverse proxy directly exposed to the internet. This puts up a wall between your servers and malicious actors attempting direct-to-server attacks or scanning for vulnerabilities. They’ll only be able to find the proxy server, keeping your actual infrastructure shielded.
Who Uses Reverse Proxies?
Pretty much everyone that runs a web application at scale uses reverse proxies. Here’s where you’ll encounter them in the real world:
- Large websites and SaaS platforms use them to distribute load across dozens or hundreds of servers.
- E-commerce sites use them to maintain uptime during flash sales or high-traffic events.
- API gateways sit behind reverse proxies to manage and secure API traffic.
- Enterprise networks deploy them to protect internal applications from the public internet.
- Content delivery networks (CDNs) are essentially large-scale reverse proxy networks, distributing cached content from servers geographically close to users.
All of these real world use cases primarily rely on three common reverse proxy software: NGINX, HAProxy, and Apache HTTP Server. That said, most companies outsource the management of their reverse proxies to cloud providers like Cloudflare and AWS.
>> Related Reading: The Best Identity Theft Protection for Businesses in 2026
Reverse Proxy vs. VPN: Are They the Same Thing?
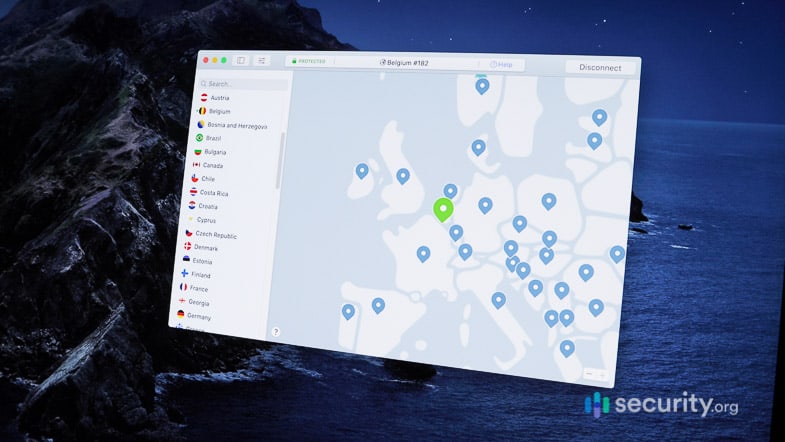
The confusion is understandable, but the answer is “no.” Both technologies involve routing traffic through an intermediary. However, reverse proxies and VPNs serve completely different purposes and operate at different ends of the connection.
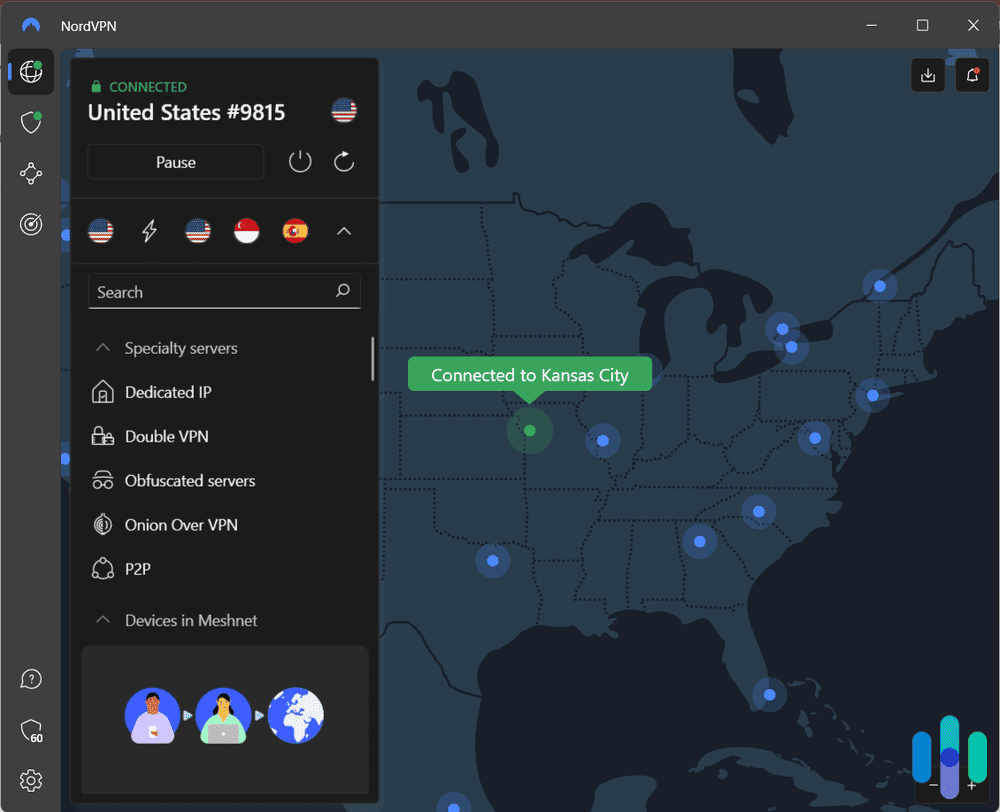
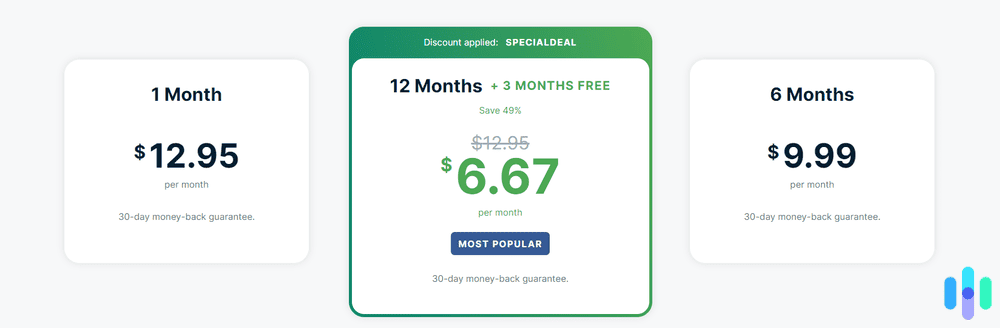
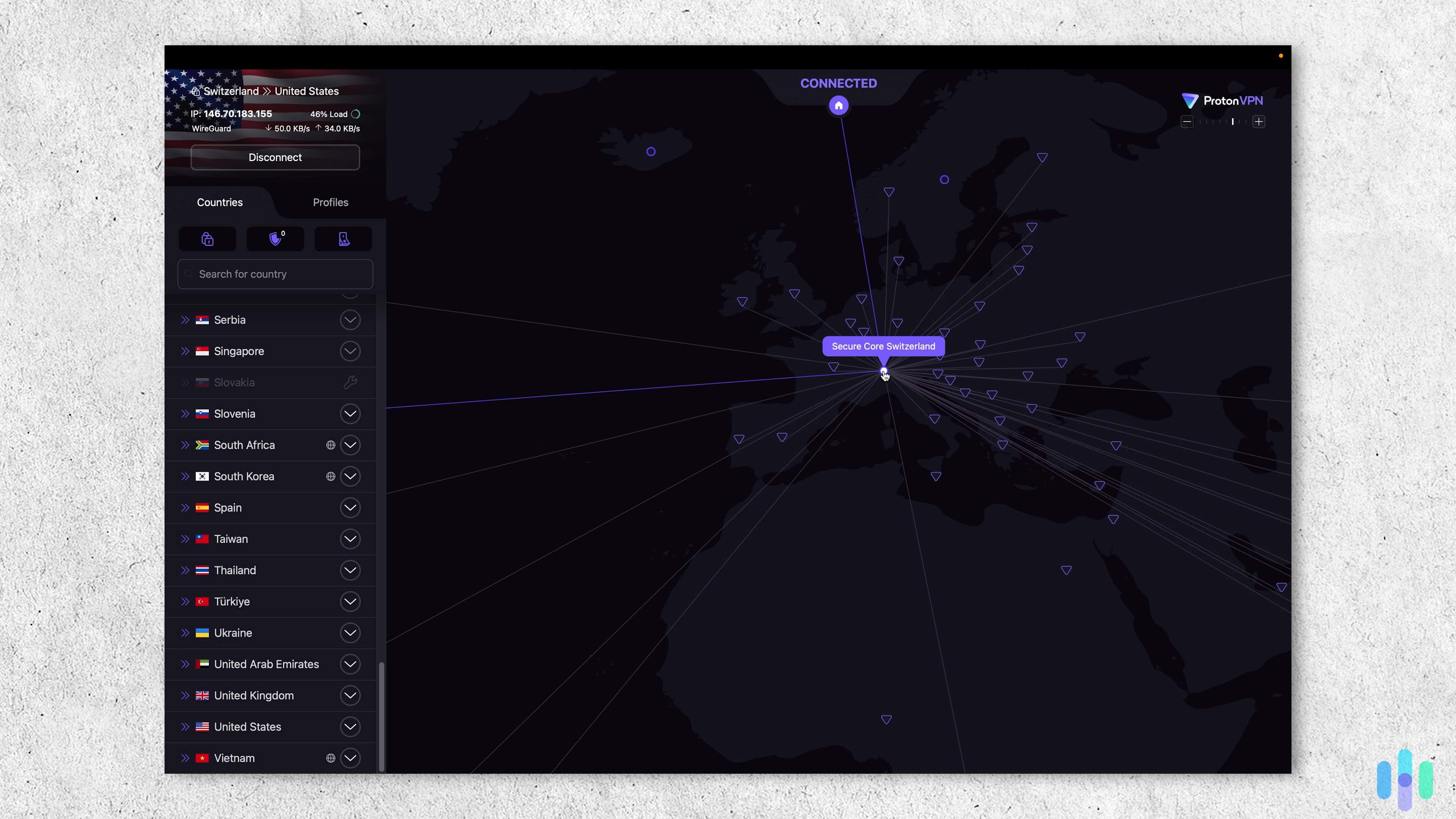
A VPN (virtual private network) is a client-side tool designed to protect the user’s privacy, making them more similar to forward proxies. Also, VPNs encrypt all traffic leaving your device and hides your IP address from the websites you visit. That’s what sets them apart from proxies in general. A VPN is what you’d use on public Wi-Fi to keep your browsing private, or to access content from another region.
Reverse proxies, by contrast, are server-side tools that protect the web server and its infrastructure from the clients connecting to it. They can also help optimize the service being delivered.
Here’s a simple way to think about it: a VPN shields you from the internet; a reverse proxy shields a web server from the internet.
FYI: VPNs and reverse proxies can be complementary. An organization might use a business VPN to give remote employees secure access to internal systems, while those same systems are protected from external traffic by a reverse proxy.
Reverse Proxy vs. Forward Proxy vs. Load Balancer
These three technologies often get lumped together. In reality, they each serve distinct purposes with unique use-cases. Here’s a quick overview of each:
- Forward proxy: Clients use forward proxies to protect their privacy and filter content. Organizations can also use them for access control. If this is what you’re looking for, check out our roundup of the best proxy servers.
- Reverse proxy: As a server-side tool, reverse proxies manage inbound traffic for security, performance, and load distribution.
- Load balancer: Although reverse proxies can help with load distribution, load balancers specialize in it. They more efficiently distribute traffic across servers but lack the broader security and caching features of a full reverse proxy.
Understanding these differences will help you find the right tool for your needs.
The Risks of Running a Reverse Proxy
For all their benefits, reverse proxies aren’t a set-it-and-forget-it solution. There are real risks to be aware of:
- Single point of failure: If your reverse proxy goes down and you don’t have redundancy, it can take your entire site with it.
- Misconfiguration vulnerabilities: A poorly configured proxy can create security holes instead of closing them. Outdated attack signature databases mean zero-day exploits can slip through unfiltered.
- SSL key exposure: Because a reverse proxy handles SSL termination, it must have access to your private keys. If a third-party provider runs your reverse proxy, you’re trusting them with those keys.
- Application breakage: Reverse proxies are often hardcoded to work with specific application versions. When applications update, the proxy configuration may need to be updated as well — and mismatches can break functionality.
These risks can all be mitigated with appropriate configuration and operations. For instance, some companies use redundant reverse proxies that rollover if one fails, keeping their site operational. Overall, reverse proxies still enhance the overall security of a site or web app, despite these risks.
Pro Tip: Even the best reverse proxy isn’t a complete security strategy. It works best as part of a layered approach that includes a high-quality firewall and the best business antivirus. Think of it as one strong layer in a multi-layer defense — not the only line of defense.
Do You Need a Reverse Proxy?
For individual users browsing the web, the answer is no — reverse proxies operate on the server side. You still interact with them constantly, but you don’t need one yourself.
That said, if you’re running a web application, API, or any kind of online service, you might need a reverse proxy. It all depends on the scope and scale of what online service you run.
- Small personal sites: In most cases, small personal sites don’t need reverse proxies. That said, it’s still worth using the free tier of services like Cloudflare for basic reverse proxy benefits.
- Small to mid-size business websites: Once you start selling products or services as a business, reverse proxies become a necessity as any downtime costs you money. Specifically, look for one that provides DDoS protection and SSL management.
- High-traffic applications: At this point, reverse proxies become essential. To handle the load of a high-traffic application, load balancing and caching becomes critical otherwise your application will slow down for end users.
- Applications handling sensitive data: While you need more than a reverse proxy to keep sensitive data safe, the WAF and IP masking capabilities can go toward your security measures.
If you’re more concerned about your personal online privacy rather than running a web service, that’s where tools like VPNs and antivirus software come in. We got both bundled together when we tested Surfshark. You should also consider one of the best identity theft protection services to round out your online safety. When we tested Aura, they bundled all three services and then some into one subscription.
>> Read About: The Best Antivirus Software of 2026
The Bottom Line
A reverse proxy is a deceptively simple concept that does heavy lifting in the background of nearly every major web service you use. It keeps servers hidden, distributes traffic intelligently, filters out malicious requests, and speeds up content delivery — all without the end user ever knowing it’s there.
For web operators and IT professionals, understanding reverse proxies is foundational knowledge. Most users, however, just consider them as part of the invisible infrastructure that makes modern web services fast, reliable, and resilient.
Frequently Asked Questions
-
What is a reverse proxy in simple terms?
A reverse proxy is a server that sits between internet users and your web server. When someone sends a request to your website, it hits the reverse proxy first, which then forwards the request to the appropriate backend server. The user never interacts with your actual server directly.
-
What's the difference between a reverse proxy and a VPN?
A VPN protects the individual user’s privacy by encrypting their outbound traffic. Reverse proxies protect web servers from inbound traffic. They work at opposite ends of the connection.
-
Is a reverse proxy the same as a load balancer?
Not exactly. A load balancer distributes traffic across multiple servers. A reverse proxy does that and much more — including security filtering, caching, SSL termination, and IP masking. All load balancers can be implemented through a reverse proxy, but not all reverse proxies are just load balancers.
-
What are examples of reverse proxy software?
NGINX, HAProxy, and Apache HTTP Server are popular open-source options. Cloudflare, AWS Application Load Balancer, and Azure Application Gateway are common managed services.
-
Can a reverse proxy hurt performance?
In theory, adding any intermediary introduces latency. In practice, the caching and load balancing benefits of a well-configured reverse proxy almost always improve performance rather than hurt it.