Best Antiviruses for Businesses in 2025, Tested on Our Office Devices
Norton offers excellent protection for small businesses — real-time protection, access to a VPN, a password manager and identity theft monitoring, and support for up to 20 devices.


- Provides excellent real-time protection
- Bundled with a VPN and identity theft protection
- Includes a password manager to secure company passwords
- Provides excellent real-time protection
- Bundled with a VPN and identity theft protection
- Includes a password manager to secure company passwords
- High-end malware protection and endpoint security features
- Can secure up to 100 devices
- Provides multiple business-specific support options
- High-end malware protection and endpoint security features
- Can secure up to 100 devices
- Provides multiple business-specific support options

- Is bundled with one of the best VPNs in 2025
- Provides access to 24/7 live chat support
- Is more affordable than other business-grade antiviruses
- Is bundled with one of the best VPNs in 2025
- Provides access to 24/7 live chat support
- Is more affordable than other business-grade antiviruses
Keeping your business safe goes beyond just securing your physical assets with one of the best security systems for businesses. It also means taking steps to protect your company data against cyber threats by using antivirus software and a VPN made for businesses. We even recommend scheduling regular training sessions with your staff to focus on the information in our guide to antivirus protection and internet security.
Picking the right antivirus for your organization could be difficult, though. There are tons of options that provide high-end security, great scalability, and good technical support. We made things easier for you by testing a dozen business-grade antiviruses to see which provide the best value. Our top picks are Norton, Bitdefender’s GravityZone, Surfshark Antivirus, Avast, and McAfee Business Protection. Read on to find out why.
The Best Business Antivirus Software at a Glance
| System |
Norton Small Business

|
Bitdefender Antivirus
|
Surfshark Alert

|
Avast Antivirus

|
McAfee Antivirus

|
|---|---|---|---|---|---|
| Ranking | 1st | 2nd | 3rd | 4th | 5th |
| Ratings | 9.5/10 | 8.7/10 | 9.5/10 | 8.5/10 | 8.8/10 |
| Free Trial | Yes (30 days) | Yes (30 days) | Yes (7 days) | Yes (30 days) | No |
| Money-Back Policy | 60 days | 30 days | 30 days | 30 days | 30 days |
| Endpoint Security | Yes | Yes | No | Yes | No |
| Centralized Management Console | Yes | Yes | Yes | Yes | Yes |
| Behavior-based detection | Yes | Yes | Yes | Yes | Yes |
| Operating Systems | Windows, macOS, iOS, Android | Windows, macOS, Linux, iOS, Android, ChromeOS | Windows, macOS, Android | Windows, macOS, Windows Server | Windows, macOS, Linux, iOS, Android, ChromeOS |
| Maximum Number of Devices | 20 | 100 | 5 | 999 | Unlimited |
| Customer Support Channels |
|
|
|
|
|
| Read Review | Norton Small Business Review | Bitdefender Antivirus Review | Surfshark Alert Review | Avast Antivirus Review | McAfee Antivirus Review |
Summary: The Best Antivirus for Businesses
- Norton Small Business - Best for Small Businesses
- Bitdefender Antivirus - Best for Medium-to-Large Businesses
- Surfshark Alert - Best for Very Small Businesses
- Avast Antivirus - Best for Enterprises
- McAfee Antivirus - Best for Businesses That Use Dell PCs
A Closer Look At Our Favorite Business Antivirus
-
1. Norton Small Business - Best for Small Businesses
View Plans Links to Norton.comProduct Specs
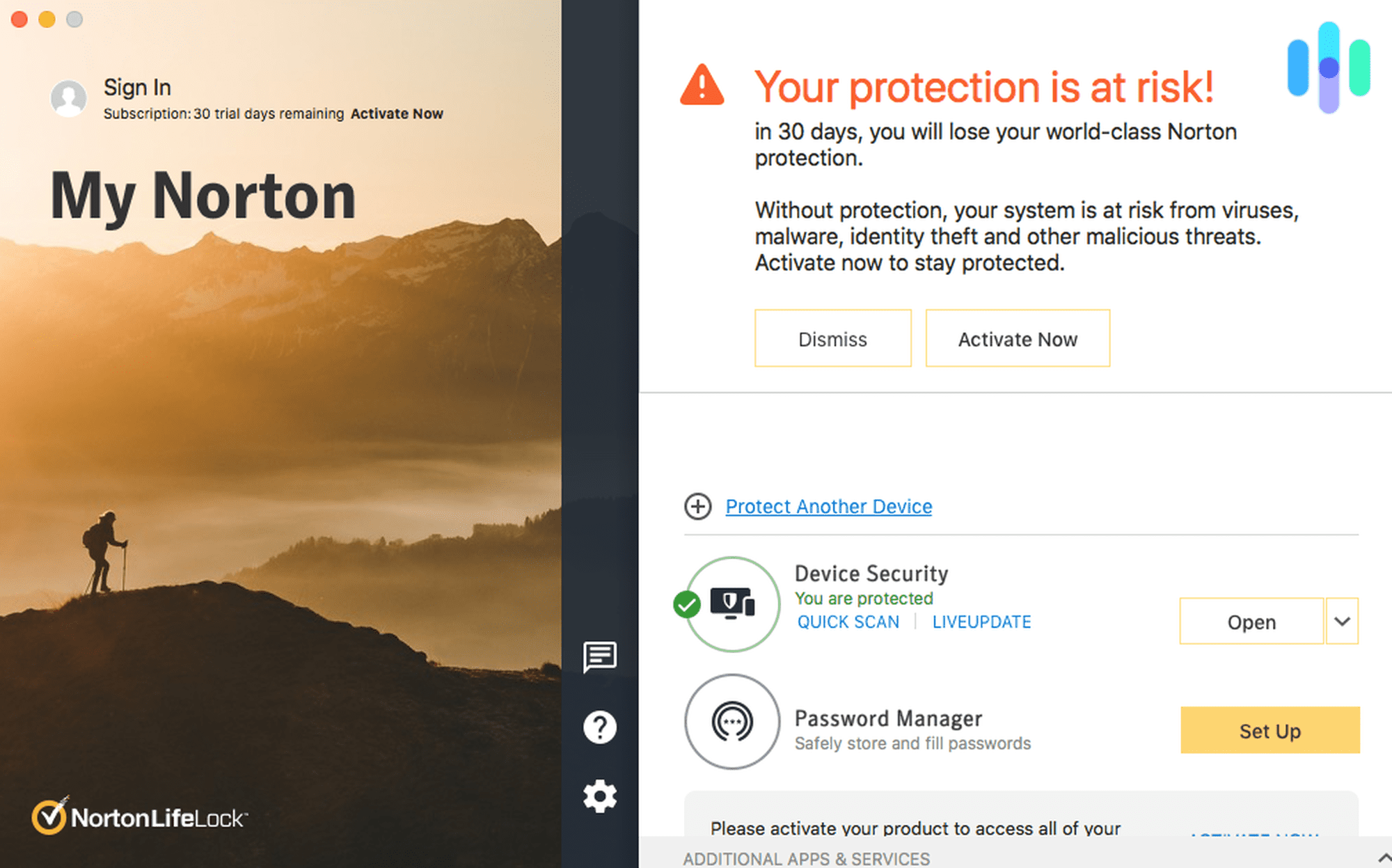
Virus Detection Yes Malware Detection Yes Firewall Yes Full, quick, and scheduled scans Yes Real-time protection Yes Behavior-based monitoring Yes Norton provides excellent antivirus protection that’s specifically tailored for small businesses. We recommend getting Norton if you run a small business with up to 10 employees. The antivirus offers excellent protection, and we like how it also comes bundled with many useful security services.
Pros
- Offers excellent antivirus protection for small businesses
- Covers up to 10 employees and 20 devices
- Includes access to useful security services like a VPN, password manager, and identity theft protection
Cons
- The firewall isn’t available on all devices
- The scalability is pretty limited
Security Features & Services
Norton’s antivirus protects your business with real-time protection that continuously scans for malware and online threats in the background. It also comes with a firewall that prevents malicious actors from compromising your company’s network. Even Norton’s personal-use antivirus made our list of the best antivirus software with a firewall.
We also like how the antivirus has an AI-powered feature that protects against scams, called “Genie Scam Protection.” For example, it can alert your employees about suspicious texts that could contain phishing links.
>> Related: Phishing Text Messages – A Guide to “Smishing”
Norton also provides access to several security services, depending on which subscription tier you get. The list includes a VPN (Virtual Private Network) that protects online traffic, a password manager that secures logins, and identity theft protection for your employees. We tested Norton’s VPN before and found it to be really secure and easy to use. Also, in terms of identity theft protection, Norton’s LifeLock service monitors your business’s bank accounts for suspicious transactions, alerts you if employee data is leaked, and prevents admin social media accounts from being taken over.
Multi-Device Coverage & Scalability
Norton’s antivirus offers great cross-platform compatibility — it can secure your company’s Windows, macOS, Android, and iOS devices. The plan coverage is perfect for small businesses, as Norton can cover up to 10 employees and secure two devices per user (for a total of 20 devices).
Unfortunately, you can’t cover more than 10 employees and 20 devices. So, if your business grows, the only option for scalability is to get another subscription. We don’t think that’s very good price-wise, though. Instead, we recommend Bitdefender if your small business starts to expand, as its antivirus service can secure up to 100 devices.
Customer Support
Norton offers access to helpful support guides, as well as round-the-clock live chat support. Norton provides excellent 24/7 customer support. By default, you get access to live chat support, phone support, and even support over social media. There’s also a community forum that’s pretty active, and you get access to step-by-step setup and troubleshooting tutorials. Also, the highest subscription tier for NordVPN’s business antivirus service includes 24/7 business tech support, which can assist with common issues and malware removal.
We tried out Norton’s live chat and phone support when we wrote this guide, and we generally had a very good experience. The live chat and phone reps we talked to were all very friendly, and they were also able to answer all of our questions really fast.
>> Related: Antivirus Software How-to Guides
Pricing
Norton offers two tier-based subscriptions for businesses: “Norton Small Business” and “Norton Small Business Premium.” If you’re mainly interested in the antivirus, the “Norton Small Business” subscription is a good pick. On top of antivirus protection, it includes access to a password manager, a secure browser, and monitoring for exposed employee data on the dark web. If you choose to cover up to 10 employees, you’ll pay $149.99 for the first year.
We like how Norton’s business subscriptions also come with a free 30-day trial. It also backs its plans with a 60-day money-back guarantee.
>> Read More: How Much Does Norton Cost in 2025?
-
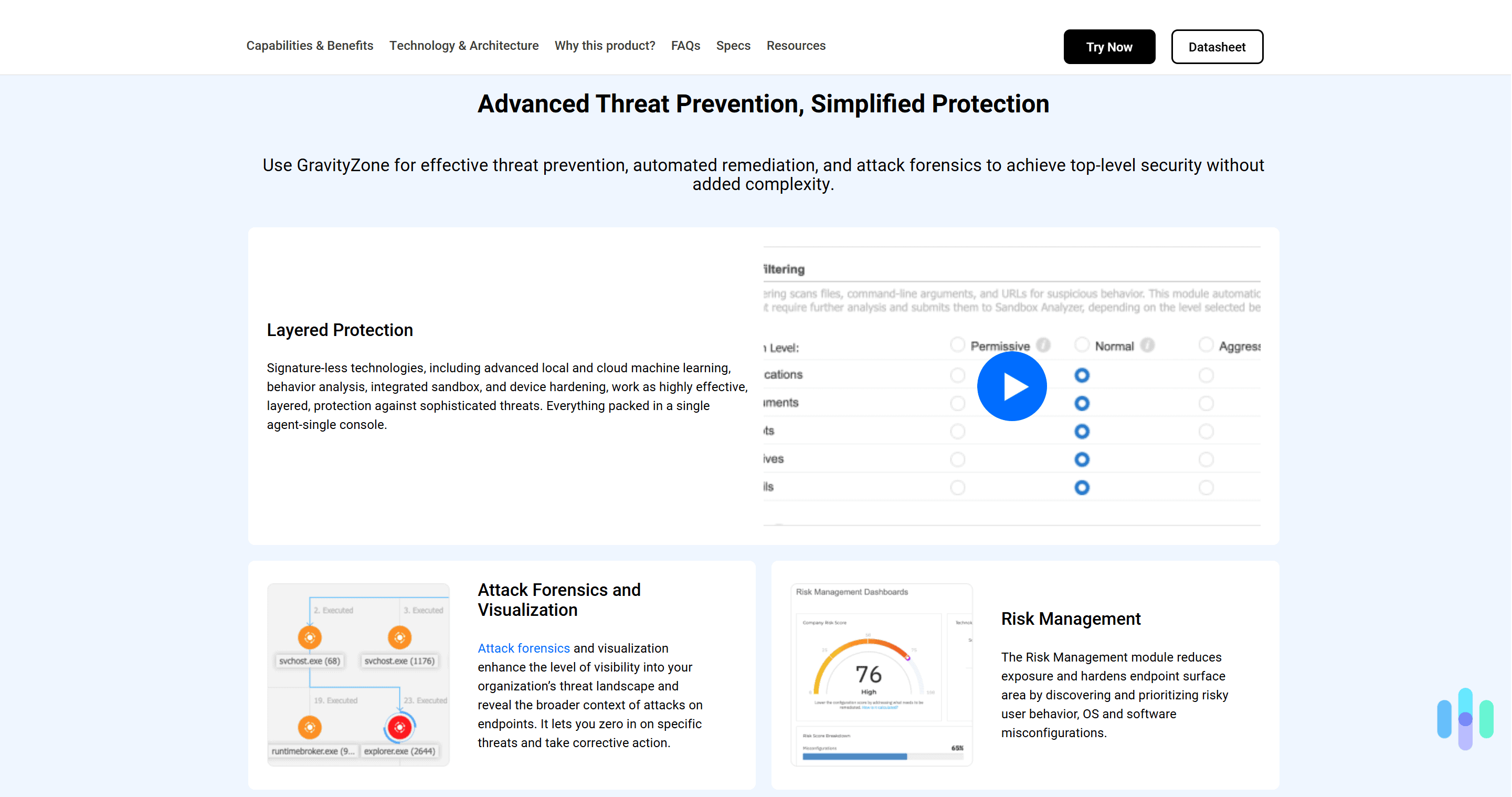
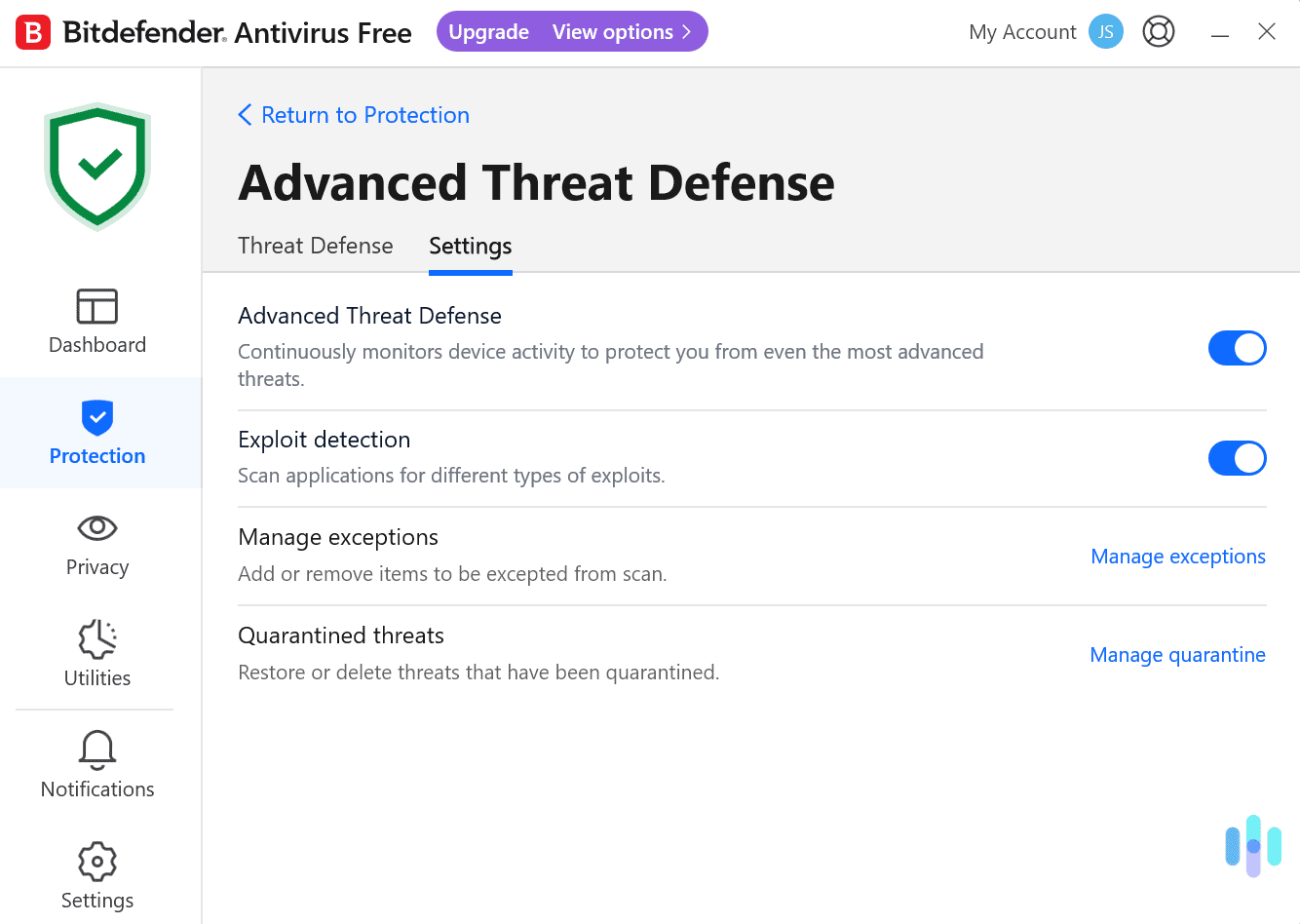
2. Bitdefender Antivirus - Best for Medium-to-Large Businesses
 View Plans Links to Bitdefender Antivirus
View Plans Links to Bitdefender AntivirusProduct Specs
Virus Detection Yes Malware Detection Yes Firewall Yes Full, quick, and scheduled scans Yes Real-time protection Yes Behavior-based monitoring Yes 
Who Bitdefender Is Good for
Bitdefender offers excellent protection for businesses via its GravityZone service. We recommend Bitdefender for medium-to-large businesses. It provides antivirus solutions for business via its GravityZone service. GravityZone not only offers very flexible scalability, but also comes with excellent endpoint security, attack forensics and visualization, risk management, web filtering, and more.
Pros
- Offers excellent malware protection, endpoint security, and automated threat prevention
- Provides great scalability since it can secure up to 100 devices
- Offers excellent customer support for businesses
Cons
- The GravityZone service isn’t bundled with Bitdefender’s VPN
- GravityZone protection for mobile devices is available as a separate add-on
Security Features & Services
Bitdefender’s antivirus service provides excellent real-time malware protection. And its GravityZone platform adds access to many other high-end security tools that keep businesses safe from malicious actors and online threats. The service provides endpoint security, which makes sure that all devices connected to your company’s network are secure. GravityZone also comes with web protection, a firewall, root cause analysis to trace the origin of security incidents, cloud-based sandboxing to isolate and test suspicious files in a secure environment, and much more.
There are also a few security services that you can add to Bitdefender GravityZone. For example, you can add “GravityZone Security for Email,” which protects your company’s email users from major email threats. There’s also “GravityZone Full Disk Encryption,” which secures all data stored on endpoints with proven encryption.
FYI: Bitdefender’s GravityZone service doesn’t come bundled with Bitdefnder’s VPN (called Bitdefender Premium VPN). So, you’ll need to buy the service separately if you’re interested in adding this security service to your company’s network.
Multi-Device Coverage & Scalability
Bitdefender’s GravityZone platform is compatible with Windows, macOS, and Linux endpoints. There’s also a “GravityZone Security for Mobile” package that protects Android, iOS, and ChromeOS devices from the latest mobile threats.
We think that Bitdefender offers really good scalability for medium and large businesses. That’s because you can customize the plans to secure up to 100 devices.
Customer Support
We tried out Bitdefender’s support channels for businesses, and generally had a really good experience. Bitdefender offers excellent support for businesses. It offers around-the-clock technical support via live chat, phone support, remote assistance, a dedicated security account manager, 24/7 threat management, and even online and on-site training to familiarize your team with the GravityZone platform.
We tested Bitdefender’s live chat and phone support, and we were really happy with it. It generally took less than two or three minutes to be connected to a Bitdefender rep. And the reps we talked with were always able to provide us with accurate answers.
Pricing
Bitdefender’s GravityZone service offers multiple tier-based subscriptions. The pricing for each subscription varies depending on the plan length you choose, and how many devices you want to secure. For this guide, we tried out the “GravityZone Business Security Premium” subscription, and we think this plan would be enough for most medium-to-large businesses.
Bitdefender GravityZone offers a free 30-day trial, which we think is great. The service also covers all plans with a 30-day money-back guarantee.
>> Find Out More: Bitdefender Full 2025 Pricing Guide
-
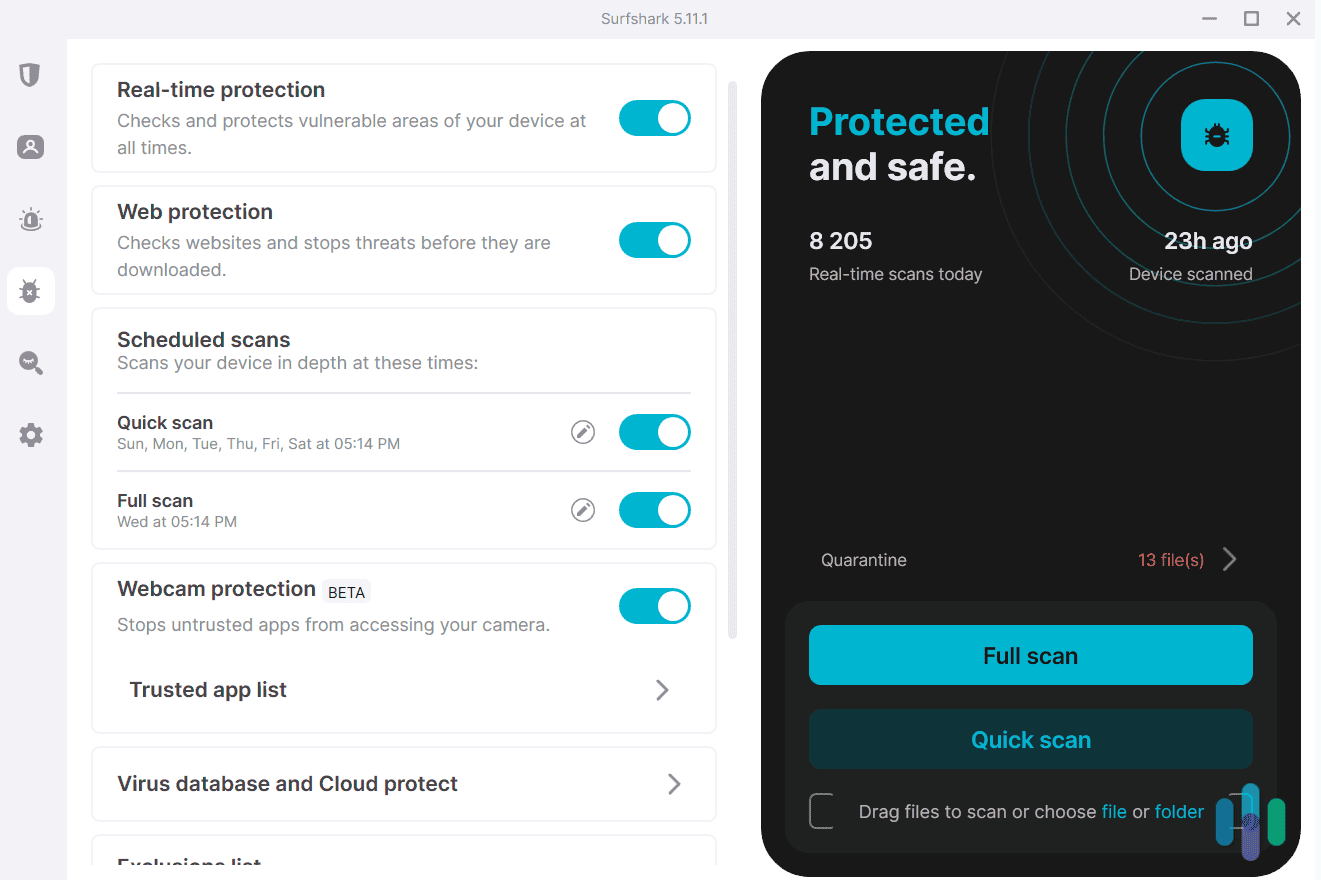
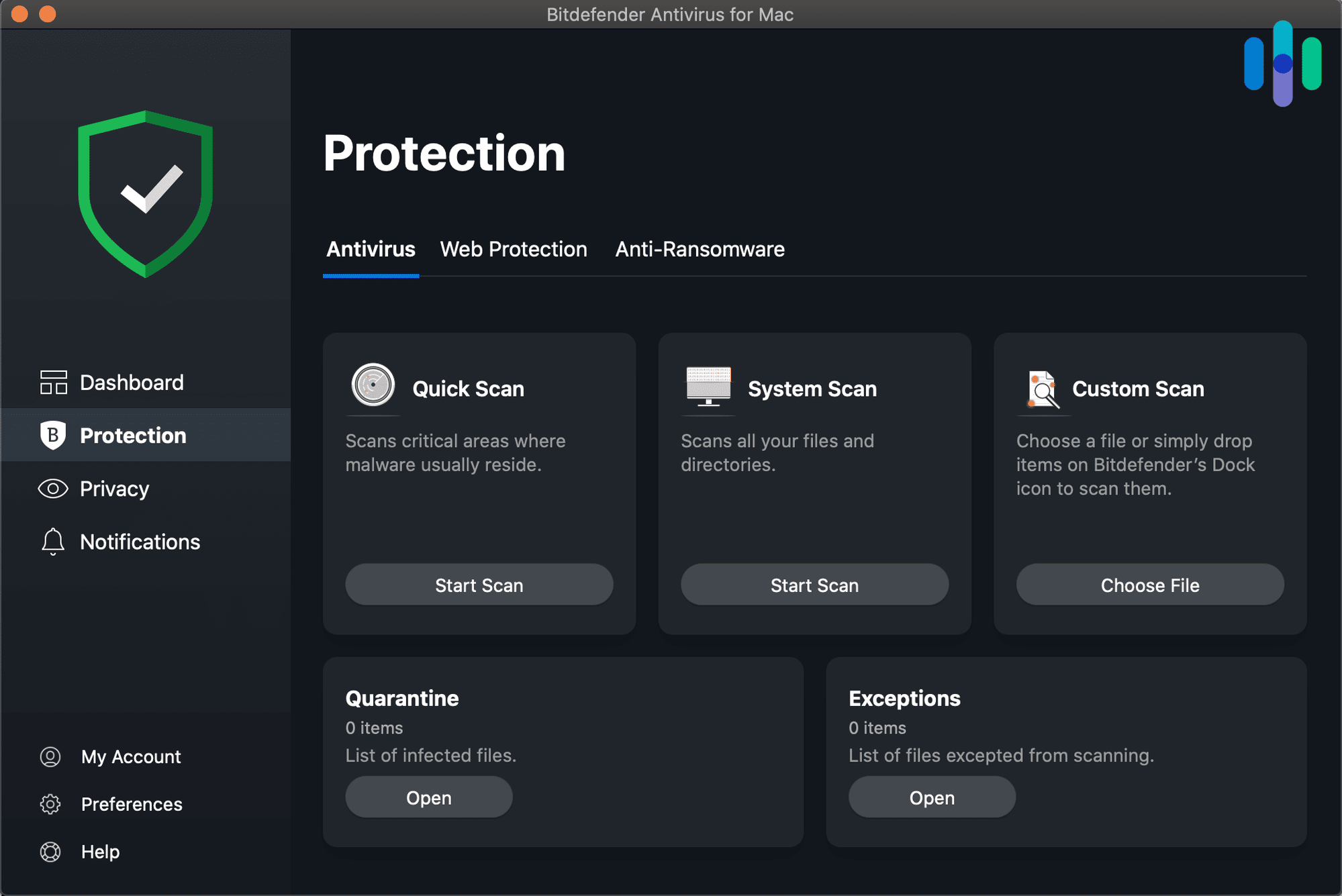
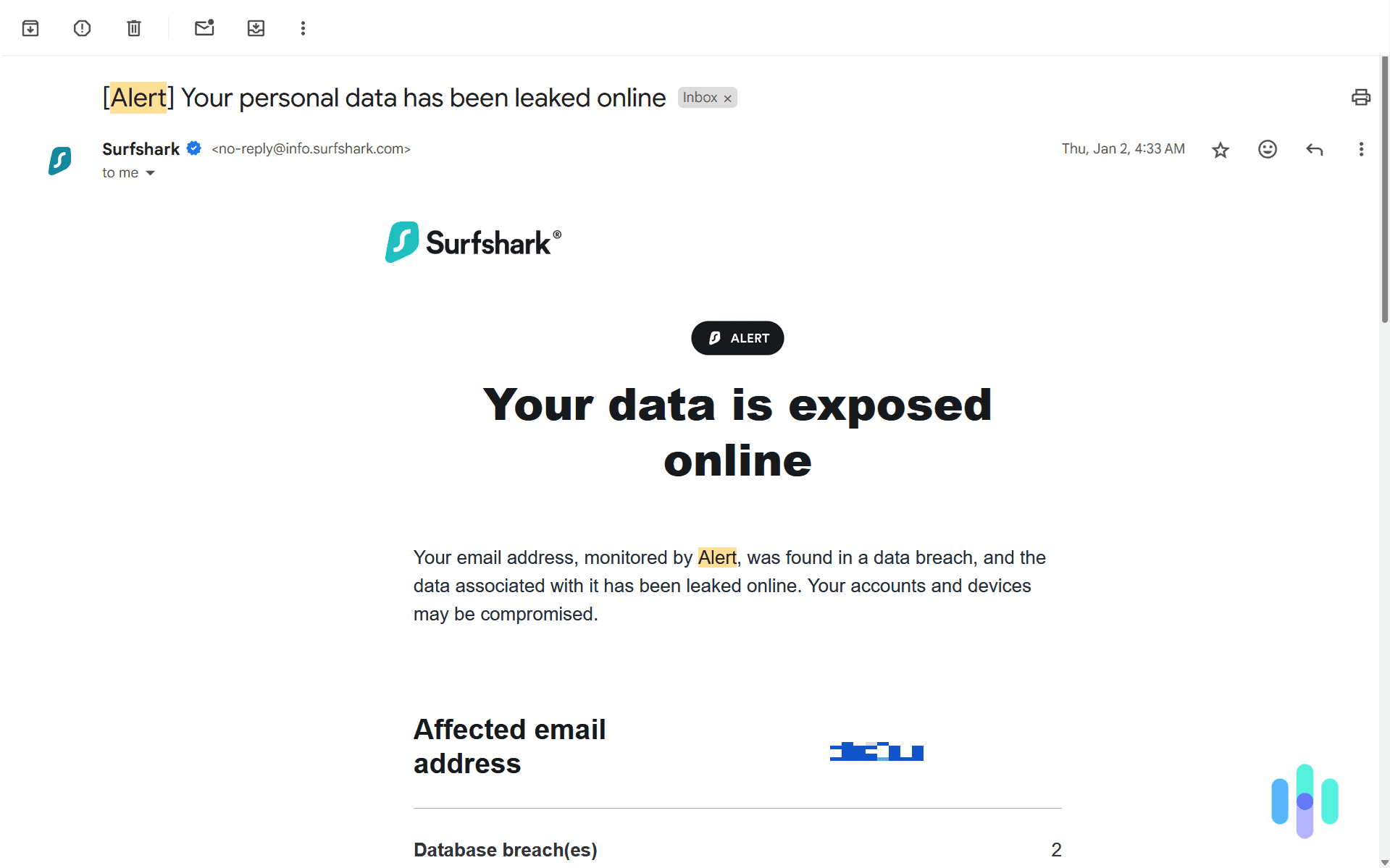
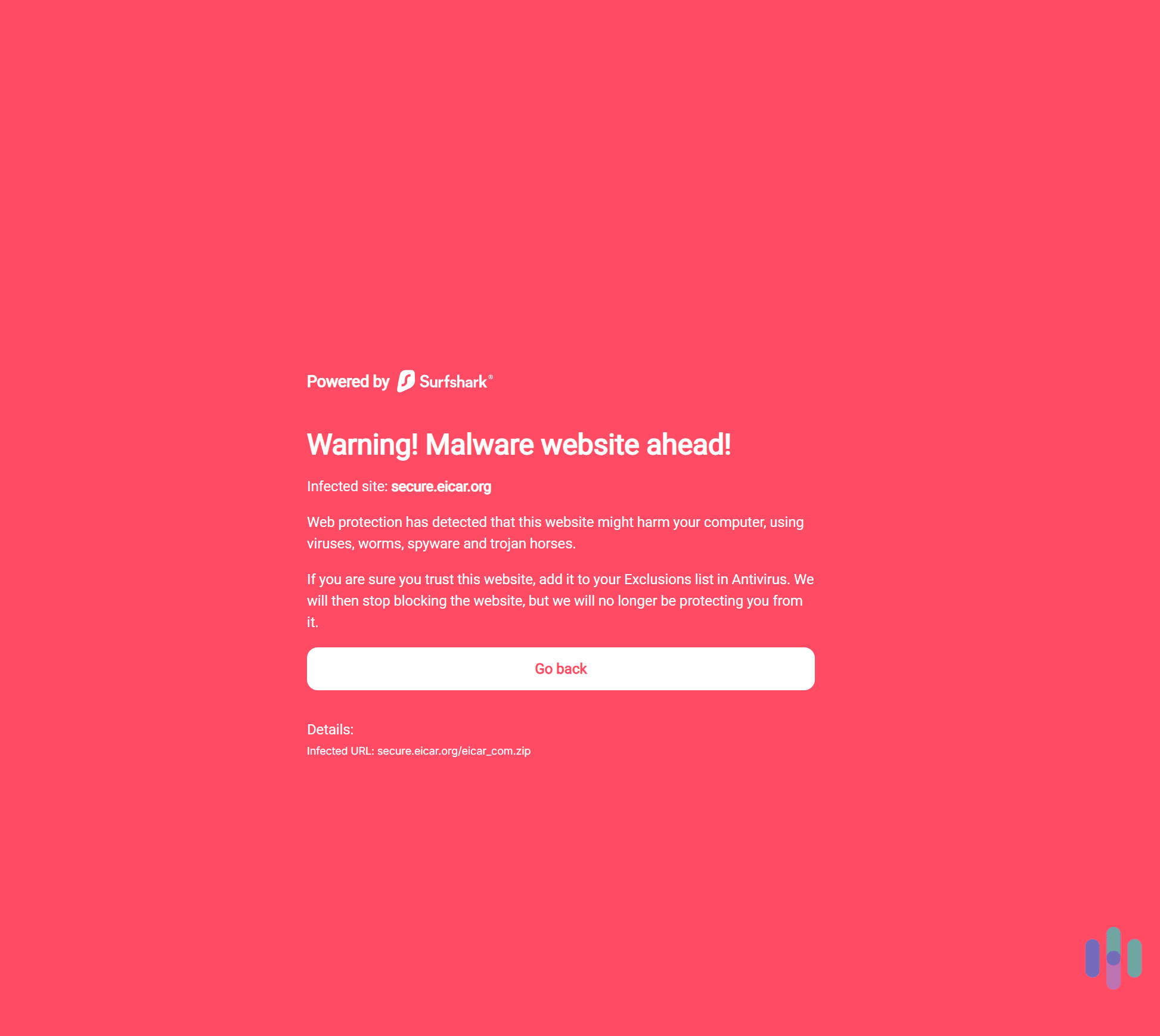
3. Surfshark Alert - Best for Very Small Businesses
View Packages Links to Surfshark.comProduct Specs
Dark Web Monitoring Yes Credit Reporting No Insurance Coverage No Free Trial 30-day money-back guarantee Individual Monthly Plans $2.69 and up Family Monthly Plans $2.69 and up Who Surfshark Antivirus Is Good for
Surfshark Antivirus offers excellent (and very affordable) protection for really small businesses. We think Surfshark Antivirus is a good fit for really small businesses that only want to use an antivirus to secure one or two on-site devices. For example, a local restaurant or coffee shop that wants to secure the computer they use for tracking inventory. That’s because Surfshark Antivirus can only secure up to five devices per subscription. Plus, it’s also very affordable compared to other business antivirus services.
Pros
- Provides very good real-time malware detection and protection
- Is much more affordable than other business antivirus services
- Bundles the antivirus with an excellent VPN service
Cons
- The antivirus isn’t as feature-rich as other competitors
- Only covers up to five devices, so scalability is limited
- Doesn’t offer phone support
Security Features & Services
You can use Surfshark Alert to keep tabs on your company’s credit cards.
Surfshark Antivirus is a great personal-use antivirus. As a business antivirus, it isn’t as feature-rich as the other services on our list, but it still provides excellent real-time protection against malware. We even tested it using multiple malicious test files and the antivirus was always able to detect them in less than one or two minutes.
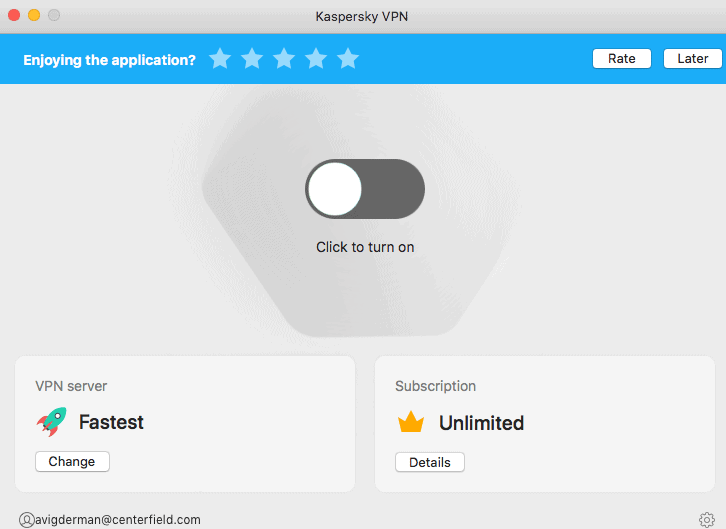
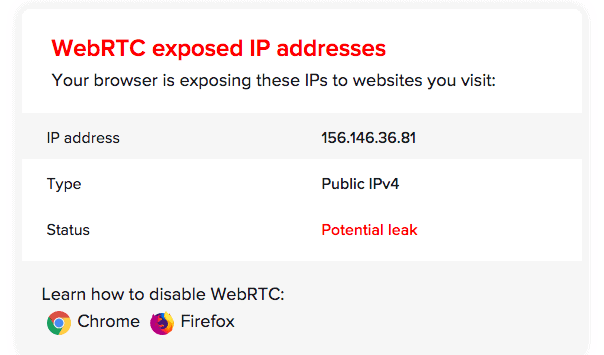
Plus, Surfshark Antivirus comes bundled with Surfshark’s VPN service, which is one of the best VPNs in 2025. It provides excellent security and privacy, it’s very fast, and it’s also really easy to use. Plus, you get access to Surfshark Alert, which sends you alerts if a personal data leak is detected. You could use this feature to check and make sure that employee IDs and company credit cards are not leaked on the dark web.
Pro Tip: Unlike the antivirus, Surfshark’s VPN supports unlimited simultaneous connections. This means you can install and use it to secure as many employee devices as you want. You can also have Surfshark Alert monitor as many pieces of personal information of your employees as needed.
Multi-Device Coverage & Scalability
Surfshark Antivirus is compatible with Windows, macOS, and Android devices. It also only covers up to five devices, so we only recommend getting this antivirus service if you need to secure a few on-site computers or smartphones.
There’s not much in terms of scalability. The only way to cover more devices is to buy another Surfshark Antivirus subscription. If your small business starts to grow a bit, we recommend switching to Norton instead. Its antivirus for business can cover up to 10 employees and 20 devices.
Customer Support
Surfshark’s customer support is pretty good. You get access to an in-depth support library that provides step-by-step setup tutorials and troubleshooting guides. Plus, Surfshark also offers 24/7 live chat and email support. We used the live chat to ask Surfshark’s reps a few questions about how the antivirus works, and the reps always provided us with helpful answers.
That said, you don’t get access to phone support or dedicated 24/7 tech support teams, like you do with other business antivirus services. This is understandable though, as Surfshark is primarily a VPN company and its antivirus is mostly an additional service.
Pricing
Surfshark’s antivirus plan is available with the “Surfshark One” and “Surfshark One+” subscriptions. We recommend getting “Surfshark One” since it’s affordable, and it also includes the VPN and Surfshark Alert alongside the antivirus.
Surfshark One Subscription Costs 1-Month Plan $17.95/month 1-Year Plan $3.39/month 2-Year Plan $2.69/month Surfshark doesn’t have a free version, but it does offer a free 7-day trial if you sign up via its mobile apps. Also, the service has a 30-day money-back guarantee that covers all plans.
>> Read More: How Much Does Surfshark Cost in 2025?
-
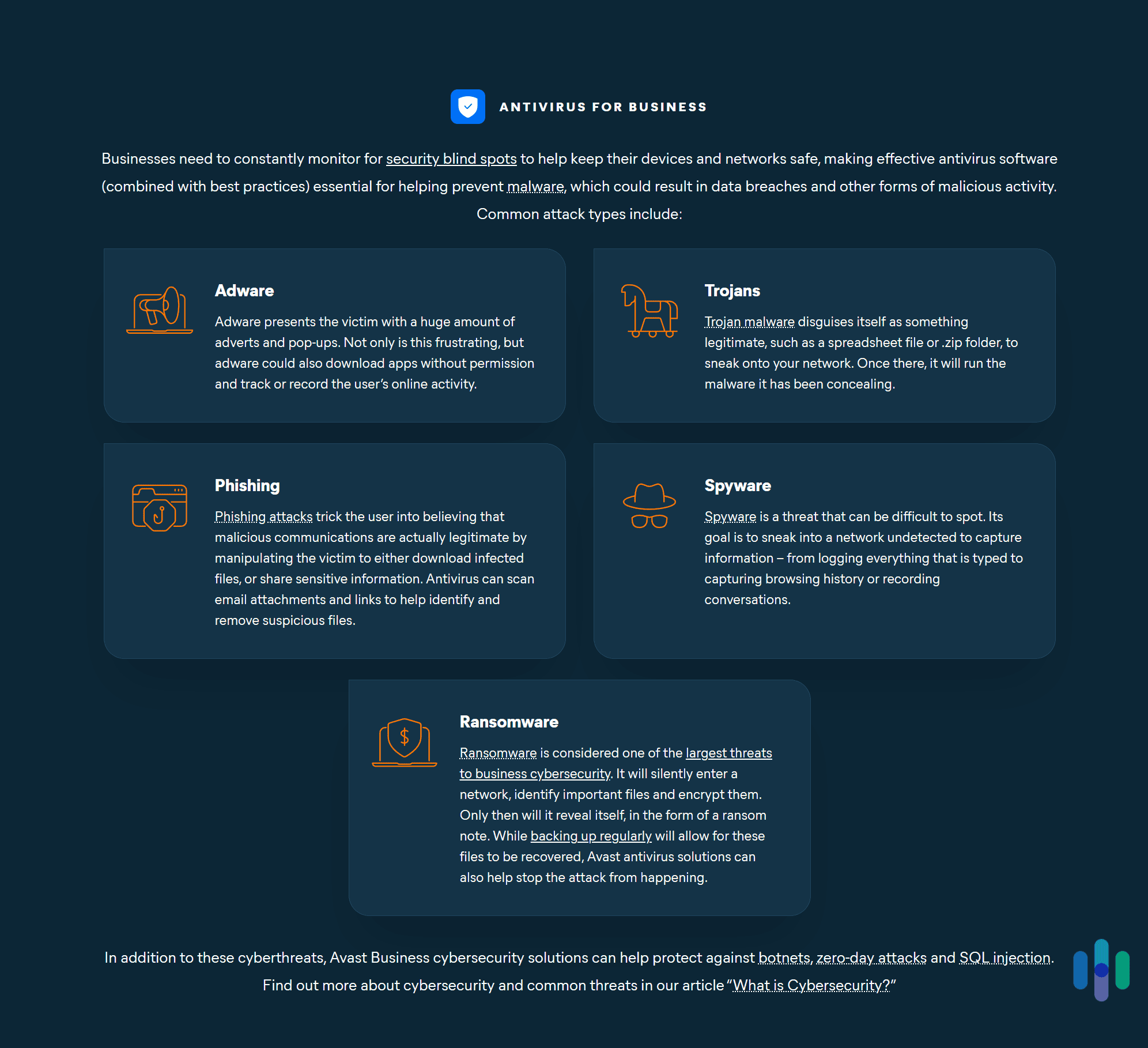
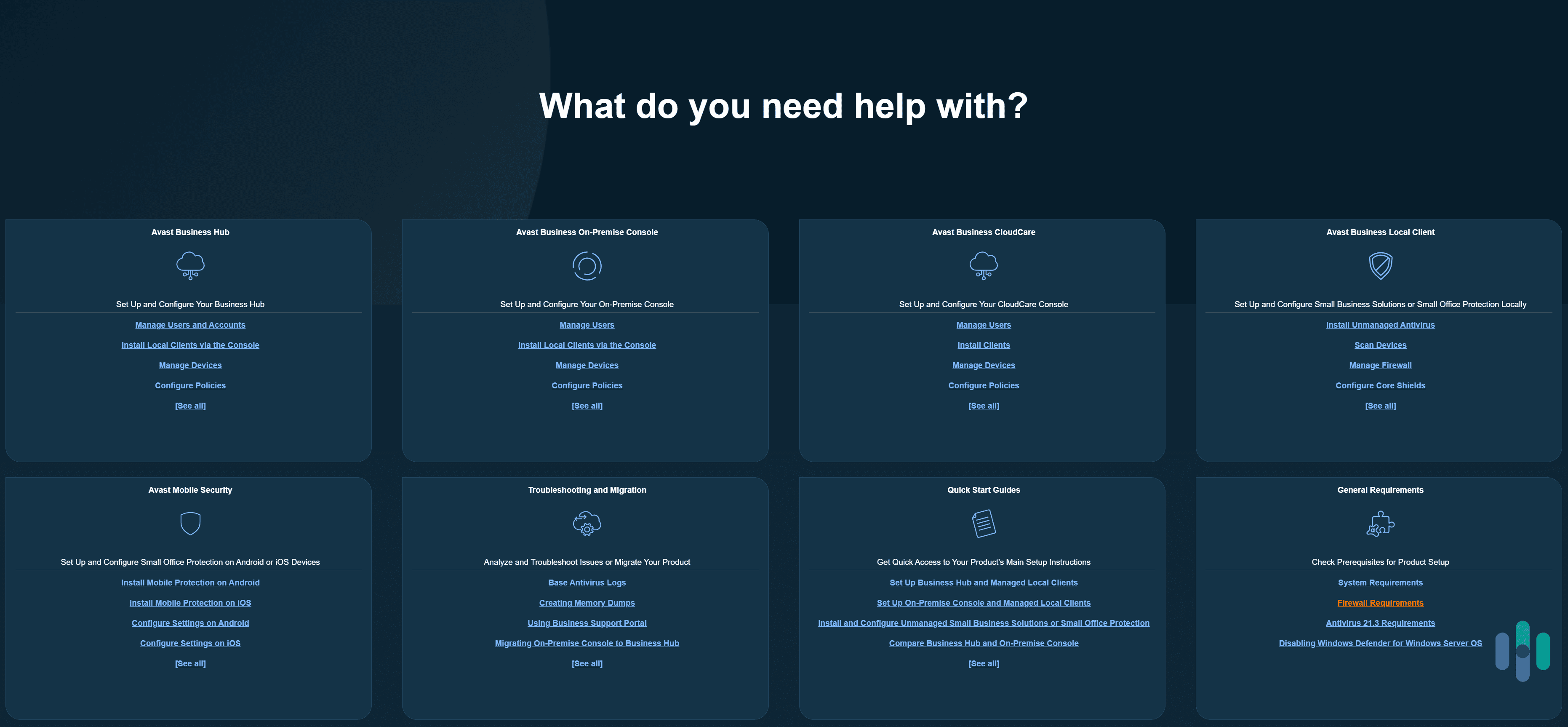
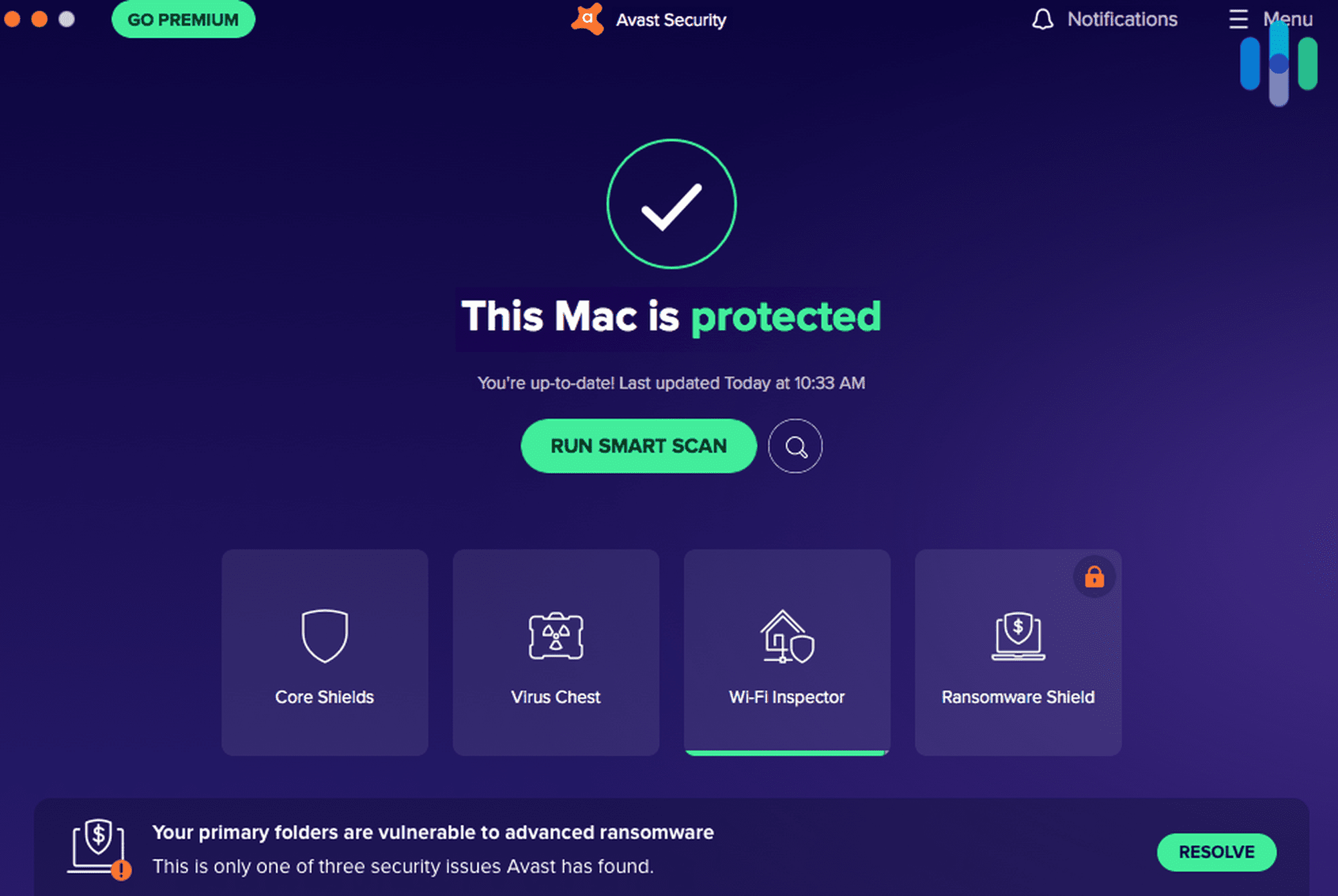
4. Avast Antivirus - Best for Enterprises
 View Plans Links to Avast.com
View Plans Links to Avast.comProduct Specs
Virus Detection Yes Malware Detection Yes Firewall Yes On-demand Scanning Yes On-access Scanning Yes Behavior-based monitoring Yes 
Who Avast Is Good for
Avast’s business solution provides excellent protection against all kinds of threats. We think Avast is a good pick for enterprise-level businesses, mainly because it lets you secure up to 999 devices. On top of that, it also provides access to excellent antivirus protection, including endpoint protection.
Pros
- Provides great protection against cyber threats, ransomware, and phishing attacks
- Offers excellent scalability since it covers up to 999 devices
- Some subscriptions include access to a decent VPN service
Cons
- Its support options for businesses are limited compared to competitors
- Has a free trial, but is only available for the highest subscription tier
Security Features & Services
Avast’s business packages provide access to excellent antivirus protection, including ransomware protection, a firewall, protection against phishing websites, and web domain and content filtering. There are also many endpoint protection features. For example, Avast scans incoming and outgoing emails for malicious links, and it also has a real-time scanner that checks all endpoints for suspicious activity or code.
Depending on your subscription, you could also get access to Avast’s VPN service (Avast SecureLine VPN). The VPN is overall secure, it’s easy to use, and it maintains good speeds. The highest subscription tiers also includes the Patch Management service, which automatically fixes app vulnerabilities on Windows devices.
Multi-Device Coverage & Scalability
Avast’s business antivirus is compatible with Windows and macOS devices, as well as devices running Windows Server. Avast lets you secure up to 999 devices, which is why we think it’s perfect for enterprise-level businesses.
It’s actually possible to cover more than 999 devices, but you’ll need to contact Avast’s sales team for this. The sales reps will be able to provide a quote according to your business needs.
Customer Support
We read through Avast’s knowledgebase, and found all support articles really helpful. In terms of customer support, Avast’s strongest suite is its support section. It’s extremely detailed, and all of its support guides provide tons of helpful information. We also like how most guides have screenshots, which makes them very easy to follow.
But its other support options are lacking compared to Norton or Bitdefender. While Avast offers live chat and phone support, it’s mainly geared towards consumers, not businesses. For organizations, the only way to get in touch with Avast’s support team is to submit a support ticket and wait for them to contact you.
Pricing
Avast has several tier-based subscriptions tailored for businesses. The price varies depending on the plan length you choose and how many devices you need to secure. For an enterprise-level business, we recommend the “Avast Ultimate Business Security” subscription, as it includes access to the VPN, Patch Management service, and web filtering, in addition to antivirus and endpoint protection.
Avast offers a free 30-day trial, but it’s only available for its highest subscription tier. In addition, Avast also backs all purchases with a 30-day money-back guarantee.
>> Related: How Much Does Avast Cost in 2025?
-
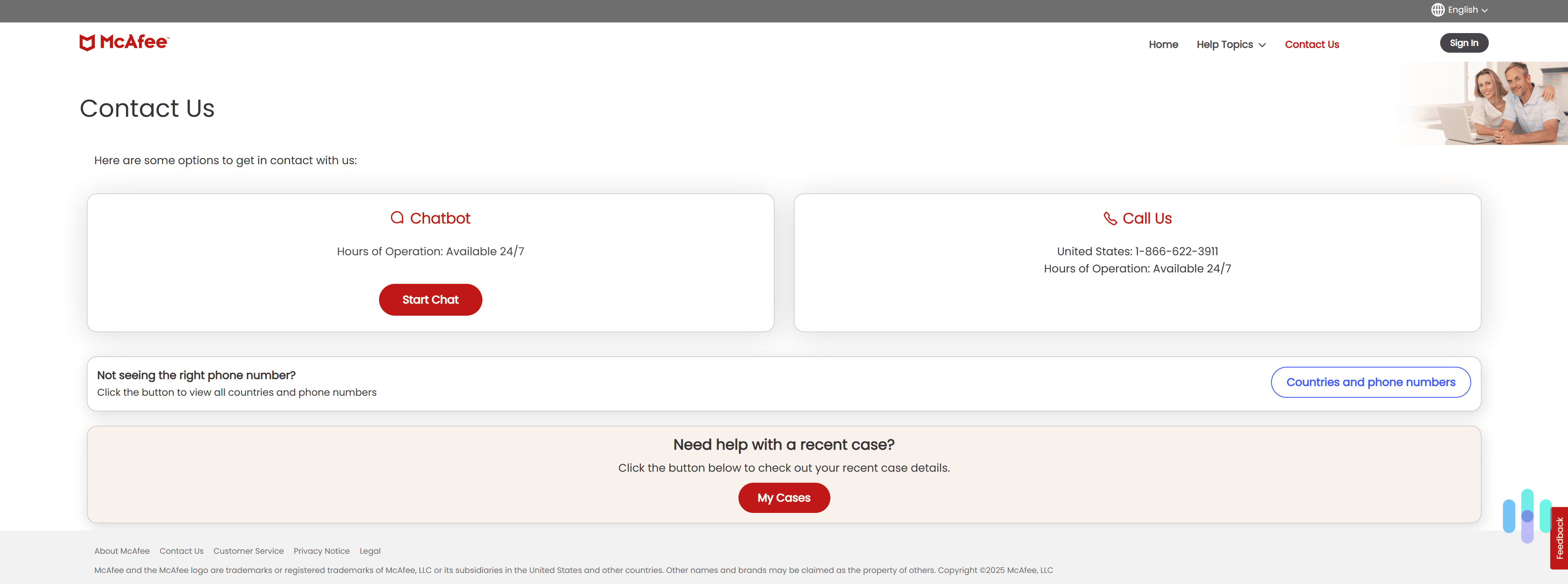
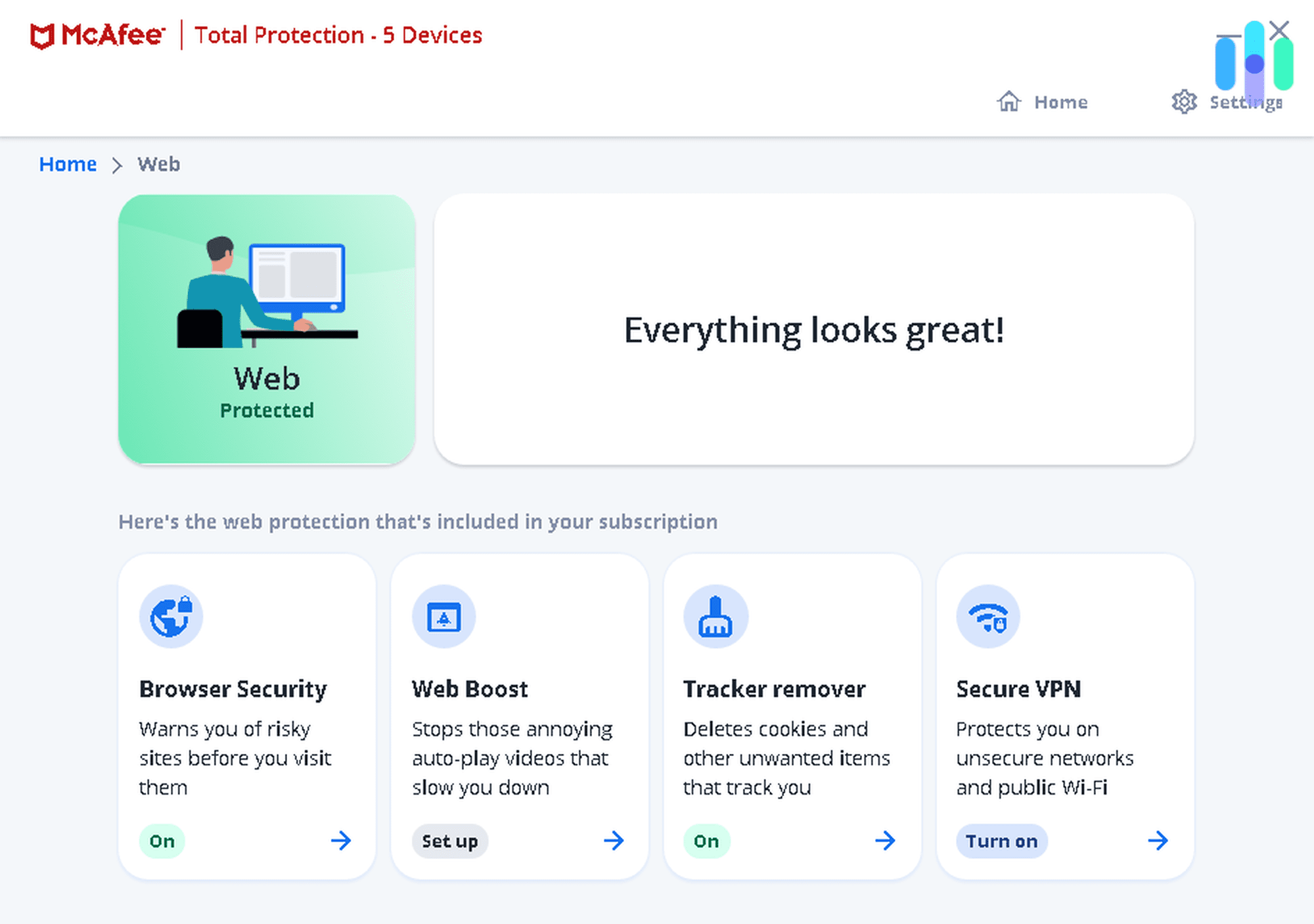
5. McAfee Antivirus - Best for Businesses That Use Dell PCs
View Plans Links to McAfee AntivirusProduct Specs
Virus Detection Yes Malware Detection Yes Firewall Yes Full, quick, and scheduled scans Yes Real-time protection Yes Behavior-based monitoring Yes Who McAfee Business Protection Is Good for
McAfee’s antivirus for businesses is exclusively available on Dell laptops and desktops. If your organization uses Dell laptops or desktops, McAfee’s business antivirus (McAfee Business Protection) is a good option. That’s because you can only sign up for it via Dell PCs. All of them come with the Business Protection app — you just need to run it, pick a subscription plan, and you can start using McAfee’s antivirus.
Pros
- Provides excellent protection against all malware strains
- Bundles its business antivirus services with a VPN
- Alerts you about leaked employee emails and phone numbers
Cons
- You can only sign up for the business antivirus service via Dell PCs
- The business antivirus service isn’t bundled with the password manager
- Doesn’t offer a lot of business-specific support options
Security Features & Services
McAfee Business Protection comes with tons of great security features. It provides excellent real-time protection against spyware, viruses, trojans, ransomware, computer worms, and more. It also provides access to a firewall, anti-phishing protection, and web protection.
In addition, McAfee Business Protection provides access to a VPN, which is called McAfee Safe Connect. It also has an identity theft monitoring service that checks if your employees’ emails and phone numbers are leaked on the dark web. There’s also a File Shredder service, which completely deletes sensitive work-related files from devices.
FYI: McAfee Business Protection also alerts you if a company device isn’t password-protected. Unfortunately, this service doesn’t provide access to McAfee’s password manager. That said, if your company needs to use such a service, we recommend picking one from our list of the best password managers in 2025.
Multi-Device Coverage & Scalability
McAfee Business Protection is exclusively available through Dell PCs, but it can secure multiple operating systems. The antivirus service is compatible with Windows, macOS, Android, iOS, and ChromeOS devices.
The antivirus protects up to five users. That seems like a scalability issue at first, but it actually isn’t because each user can secure an unlimited number of devices.
Customer Support
McAfee’s support for businesses isn’t very in-depth, but at least there’s round-the-clock live chat and phone support. McAfee provides customer support via support articles and 24/7 live chat and phone support. We like the support articles — they’re pretty in-depth, they’re easy to follow, and most have screenshots. We also tried out the live chat and phone support, and the reps we spoke to provided helpful information.
That said, other competitors provide more business-specific customer support. For example, Norton offers 24/7 business tech support via its highest subscription tie, and Bitdefender’s GravityZone service provides remote assistance, 24/7 threat management, a dedicated security account manager, and even on-site training.
Pricing
To get a subscription, you’ll need to use the Business Protection app on your Dell PC. The app will then redirect you to a webpage showing the subscription tier options. McAfee also backs its plans with a 30-day money-back guarantee.
>> Find Out More: How Much Does McAfee Cost in 2025?
Methodology: How We Chose the Best Antivirus Software for Businesses
We spent a few weeks testing 20 business antivirus solutions to see which are the best. We wanted to make sure that we only recommend services that have great malware detection rates, provide access to additional security services, and offer good customer support options. Here’s the exact criteria we used to decide which services to add to our list:
- We tested each antivirus service’s malware detection. We used a library of malicious test files on one of our office computers. We made sure that each antivirus program’s real-time protection is able to immediately block the files when it detects them.
- We considered what extra security tools and services are available. Most of the antiviruses that we ranked provide access to security features that are useful for businesses, like endpoint protection, firewalls, web protection, and cloud-based sandboxing. We also prioritized antivirus platforms that provide access to a VPN, a password manager, or identity theft protection.
- We assessed cross-platform compatibility, scalability, and ease of use. We prioritized antiviruses that can cover multiple operating systems. We also made sure to recommend services that are easy to set up, and have user-friendly apps and account dashboards. And most of the services we ranked also offer good scalability, as they can cover tens (if not hundreds) of devices.
- We tested each antivirus service’s customer support. We checked what customer support channels are available for business owners. Most of the services that we ranked offer 24/7 live chat and phone support, and all of them have in-depth support sections. Plus, some even offer extra support options for businesses. For example, Norton has 24/7 business tech support, and Bitdefender offers online and on-site training for its business antivirus platform.
- We looked at each antivirus’s pricing options. We prioritized services that offer affordable plans, whether you’re a small, medium, or large business. We also decided to only rank antivirus services that offer a free trial or a generous money-back guarantee.
Does a Small Business Need an Antivirus?
Yes, definitely. Cybercriminals actually target small businesses pretty often. They take advantage of the fact that many small business owners believe they don’t need antivirus protection. They just assume their servers don’t store any valuable data. But in reality, they do — payment information, customer data, and employee information. If malicious actors manage to compromise any of that data, they won’t just do financial damage to your company; they’ll also harm its reputation.
A business antivirus would protect your company from those threats. And if you’re running a very small business and are worried about expenses, you could try out Surfshark Antivirus. It’s extremely affordable since its prices start at just $72.63 for the first two years. It doesn’t offer endpoint protection or a firewall like most business antivirus services, but it still provides excellent real-time protection against malware.
Can You Use a Free Antivirus for Your Business?
No, as most business antivirus services don’t come with a free version. Generally, only consumer-oriented antiviruses have free plans. Business antiviruses, instead, offer a free trial. For example, Norton, Bitdefender GravityZone, and Avast all have a free 30-day trial.
While there are some good free antivirus services in 2025, we can’t really recommend using them for your business. Free antivirus apps usually lack real-time protection, which is essential for keeping your company data secure. If you really insist on using a free antivirus, maybe try out Bitdefender’s free version. It provides real-time protection, but keep in mind it’s aimed at consumers, not businesses. Also, the free version only covers up to three devices, so it’s only ideal for very small businesses.
Personal vs. Business Antiviruses
If you’re not completely sure what type of antivirus you need, here are the main differences between consumer and business antiviruses:
- Security features. Business antiviruses usually offer access to security features that are not available with consumer antiviruses. For example, business users might get access to endpoint security, cloud-based sandboxing, email scanning, and root cause analysis.
- Scalability. Consumer antiviruses are only intended to cover a few devices. Usually, most personal antiviruses cover up to 10 devices. Business antivirus solutions, on the other hand, can secure tens or even hundreds of devices.
- Management. With a personal antivirus, the individual user manages the antivirus app. With business antiviruses, however, a centralized console is usually employed to manage antivirus protection across all company devices.
- Customer support. Business-grade antiviruses usually provide better technical support. This could include online or on-site training, remote assistance, or dedicated help with deploying or troubleshooting the antivirus platform. Personal antiviruses, however, usually provide just live chat and phone support and access to a support section.
- Pricing options. Personal antiviruses are much more affordable than business antiviruses. What’s more, personal antivirus services often come with a free version. Business antiviruses, on the other hand, lack a free version, but often provide access to a free trial.
Recap
Antivirus solutions are necessary to protect company data. We reviewed the best antiviruses in 2025 to see which ones have plans specifically designed for businesses. We then tested each service on our office devices and network to see which ones provide excellent security, scalability, and technical support for businesses.
After weeks of tests and research, we found that Norton, Bitdefender’s GravityZone platform, Surfshark Antivirus, Avast, and McAfee Business Protection offer the best value for organizations.
Frequently Asked Questions
-
Do business-grade antiviruses have free versions?
No, we haven’t come across any business antivirus services that offer free plans. Instead, most business antiviruses offer a free trial (usually a 30-day trial).
-
Do business antiviruses offer endpoint protection?
Yes, most business antivirus solutions provide endpoint security. They ensure that all the devices connected to your company’s network are secure, so that malicious actors can’t use them to compromise your business.
-
What antivirus software is best for businesses?
Our research and tests show that Norton, Bitdefender, Surfshark Antivirus, Avast, and McAfee Business Protection are the best options for businesses.
-
How much does business antivirus software cost?
The price mainly depends on which subscription tier you choose and how large your organization is. On average, you should expect to pay at least $100 or $200 per year, with the pricing going up to over $500 per year if you pick an enterprise-level antivirus.