Picture this: you’re playing your favorite multiplayer video game when suddenly, you’re disconnected. You try to Google the problem, but that doesn’t work either. In fact, your internet connection is cut off entirely. The culprit? A distributed denial-of-service, or DDoS, attack.
A DDoS attack can take down an internet connection, website, or application. The effects range from the inconvenient (like losing a game) to devastating (like losing customers). Thankfully, there are things you can do to prevent them. Things like using a VPN.

Do VPNs Stop DDoS Attacks?
Generally speaking, yes, VPNs can stop DDoS attacks. A primary benefit of a VPN is that it hides IP addresses. With a hidden IP address, DDoS attacks can’t locate your network, making it much harder to target you. Additionally, VPNs encrypt web traffic, creating a tunnel between your computer and network, thus hiding activity from your internet service provider (ISP).
However, a VPN is not a foolproof solution to stop a DDoS attack. If a hacker already knows your computer’s IP address, then there isn’t much a VPN can do. Not to mention that sometimes hackers go straight to the VPN companies’ servers. If the company itself has poorly implemented DDoS attack protection, its users are likely unsafe. While VPNs can’t stop DDoS attacks in progress or already in servers, they can stop attacks once the VPN is set up on your devices.
What Is a DDoS Attack?
“DDoS” stands for “distributed denial of service,” which is a type of cyberattack that forces people offline. Hackers’ goals in committing DDoS attacks are to flood a network with unwanted requests and traffic. Subsequently, a site can’t handle the influx any further, preventing legitimate traffic from coming through.
DDoS Attack Statistics
DDoS attacks have increased by 55% year-over-year, with hyper-volumetric attacks exceeding rates of three terabits per second.1 What makes this alarming is that these attacks are becoming more accessible thanks to the rise of DDoS-for-hire services, sometimes called “booter” or “stresser” services. They allow virtually anyone to launch an attack for a few dollars.
DDoS vs. DoS
Now, let’s get into some deeper technicalities. Denial-of-service (DoS) attacks, while seemingly similar to DDoS attacks, have some important differences. Firstly, a single source perpetrates DoS attacks, while multiple sources perpetuate DDoS attacks. From there, DoS attacks fall into two major categories:
- Application attacks: Application attacks put operational strain on the software serving the requests so that it cannot handle additional requests.
- Network attacks: These attacks saturate bandwidth by overwhelming a server with force or flooding it with malformed requests. As firewall configurations have advanced, these types of attacks have become less common.
To summarize:
| DDoS | DoS | |
|---|---|---|
| Source | Multiple computers | One computer |
| Speed | Faster | Slower |
| Threat level | High | Low to medium |
| Malware involved? | Yes, a botnet can be made up of infected PCs | No |
How Do DDoS Attacks Work?
A DDoS attack is when an attacker or multiple attackers make it impossible for a service to be delivered. They do this by blocking access to:
- Servers
- Devices
- Services
- Networks
- Applications
- Specific transactions within applications
These attacks are a lot like a flash sale where thousands of shoppers flood a retailer’s site at once. The server ends up buckling under the pressure and legitimate users can’t get through. This can mean sending a web server so many requests to serve a page that it crashes, or hitting a database with a high volume of queries. As a result, internet bandwidth, CPU, and RAM capacity become overwhelmed.
Types of DDoS Attacks
There are three types of DDoS attacks:
- Volume-based attacks: These attacks use massive amounts of fabricated traffic to overwhelm a website or server. They include ICMP, UDP, and spoofed-packet flood attacks.
- Protocol or network-layer DDoS attacks: These attacks consume server resources to force a network offline. If that’s not possible, they’ll eat up load balancer and firewall resources instead. Some types of protocol attacks are the Ping of Death, SYN flood, and Smurf DDoS.
- Application-layer attacks: These are among the trickiest to defend against because they mimic legitimate user behavior. They target the layer where the web server generates webpages and responds to requests, overwhelming it until it crashes.
Who Performs DDoS Attacks?
Cybercriminals and hackers use botnets, networks of malware-infected computers, to deploy DDoS attacks. This makes it hard to trace the crime3 to any particular person.
What Is the Motive Behind DDoS Attacks?
The motivations behind DDoS attacks continue to evolve. Today’s attackers might be state-sponsored groups targeting critical infrastructure, hacktivists making political statements, or cybercriminals running extortion schemes. Hackers can use DDoS attacks to extort companies and gain notoriety within the hacker community. Additionally, cyberterrorists use DDoS attacks to slow down websites of utility companies, banks, and even entire governments.
Are DDoS Attacks Legal?
DOS and DDoS attacks are definitely not legal, at least not in the United States, where they fall under federal statutes.4 Participants risk being charged with both criminal and civil complaints. The Computer Fraud and Abuse Act prohibits a person from “knowingly caus[ing] the transmission of a program, information code, or command, and as a result of such conduct, intentionally caus[ing] damages without authorization to a protected computer.” DDoS attacks are the transmission of a program, information code, or command, damaging the integrity or availability of data, a program, a system, or information, so they are classified as an illegal activity.
How Do I Know if I’ve Been DDoSed?
These are some of the warning signs that you’ve been DDoSed:
- Website down
- Lack of access to website management
- Slow response
- Loss of internet access
- Unusual spike in traffic from a single IP address or geographic location
- 503 Service Unavailable errors appearing frequently
What To Do if You’re DDoSed
If you didn’t get your VPN set up in time and got DDoSed, there are some steps you can take:
- If you manage your website, put it into maintenance mode to prevent loss of website data.
- Inform your company management team of the issue.
- Call your ISP and tell them that you are under attack.
- Call any other third parties responsible for service delivery or perimeter security management to let them know that you are under attack.
- Capture as much information as possible, such as:
- Time the event started
- Duration of event
- Traffic statistics, if possible, to show traffic throughput
- Server logs
- Changes that might take place during or soon after the DDoS event
- Update your location by changing your IP address.
- If things are still out of hand after you complete those steps, take more serious actions, like contacting law enforcement. You can fill out a ticket with the FBI’s Internet Crime Complaint Center here.
DDoS, VPNs, and Gaming
DDoS attacks are a particular threat during gaming sessions. A VPN is a good way to protect against DDoS attacks during sessions because of hidden IP addresses. We compiled the best VPNs for gaming, but gamers can also protect themselves by not accepting unknown video call requests and by getting routers with built-in DDoS attack protection.

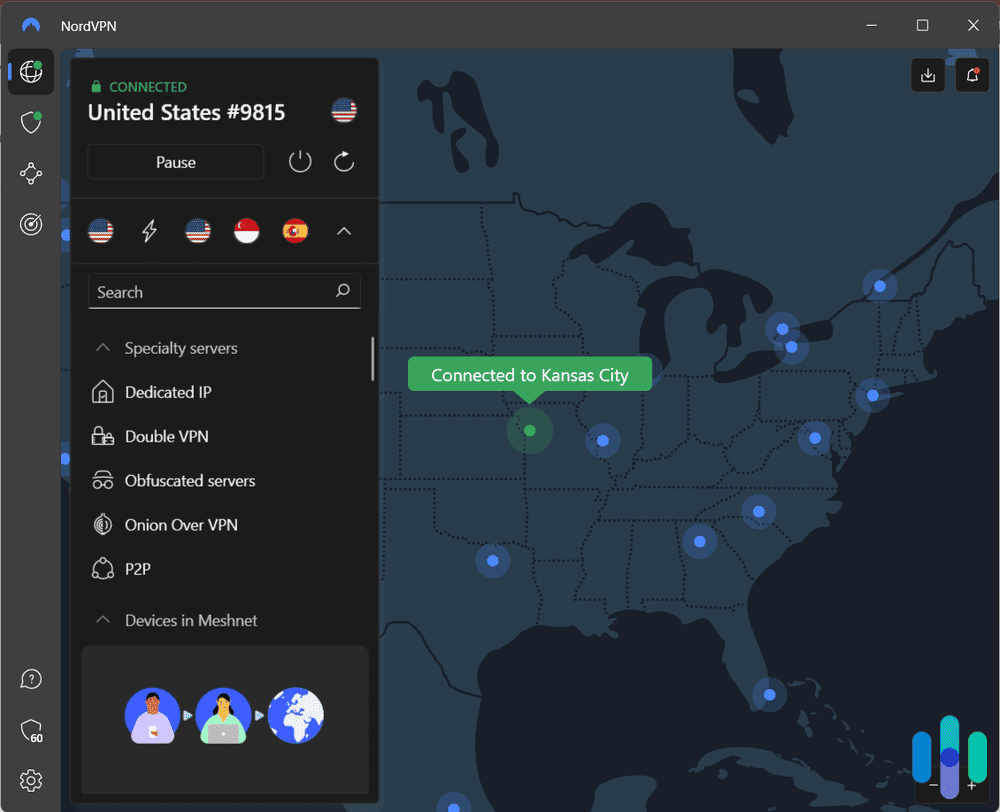
Pro Tip: Changing to a server near your location can increase speed. VPNs with a lot of servers give more options for switching
How To Prevent DDoS Attacks
Getting a VPN is a solid first step toward protecting yourself from DDoS attacks, but it shouldn’t be your only line of defense. Here are some best practices worth adding to your security toolkit:
- Have a singular point of failure elimination. Architect your systems so that there are multiple entry points, making it harder to target your site.
- Use DDS rules. Make sure your hosting system has built-in DDS functionality, which can monitor traffic and allow access only to users who meet your specific criteria.
- Limit the number of entries to your data. Allow access to sensitive data to as few people as possible. This limits exposure and therefore risk.
- Enable rate limiting on your network to prevent a single source from overwhelming your system with requests.
- Look into a content delivery network (CDN) that bundles DDoS protection into their service.
What Is a VPN?
We hear about them all the time, but what is a VPN, really? Virtual private networks (VPNs) create an encrypted tunnel between your computer and a network, typically a public Wi-Fi network. This means all of your web traffic, along with your IP address, will be hidden from the ISP.
How Does a VPN Work?
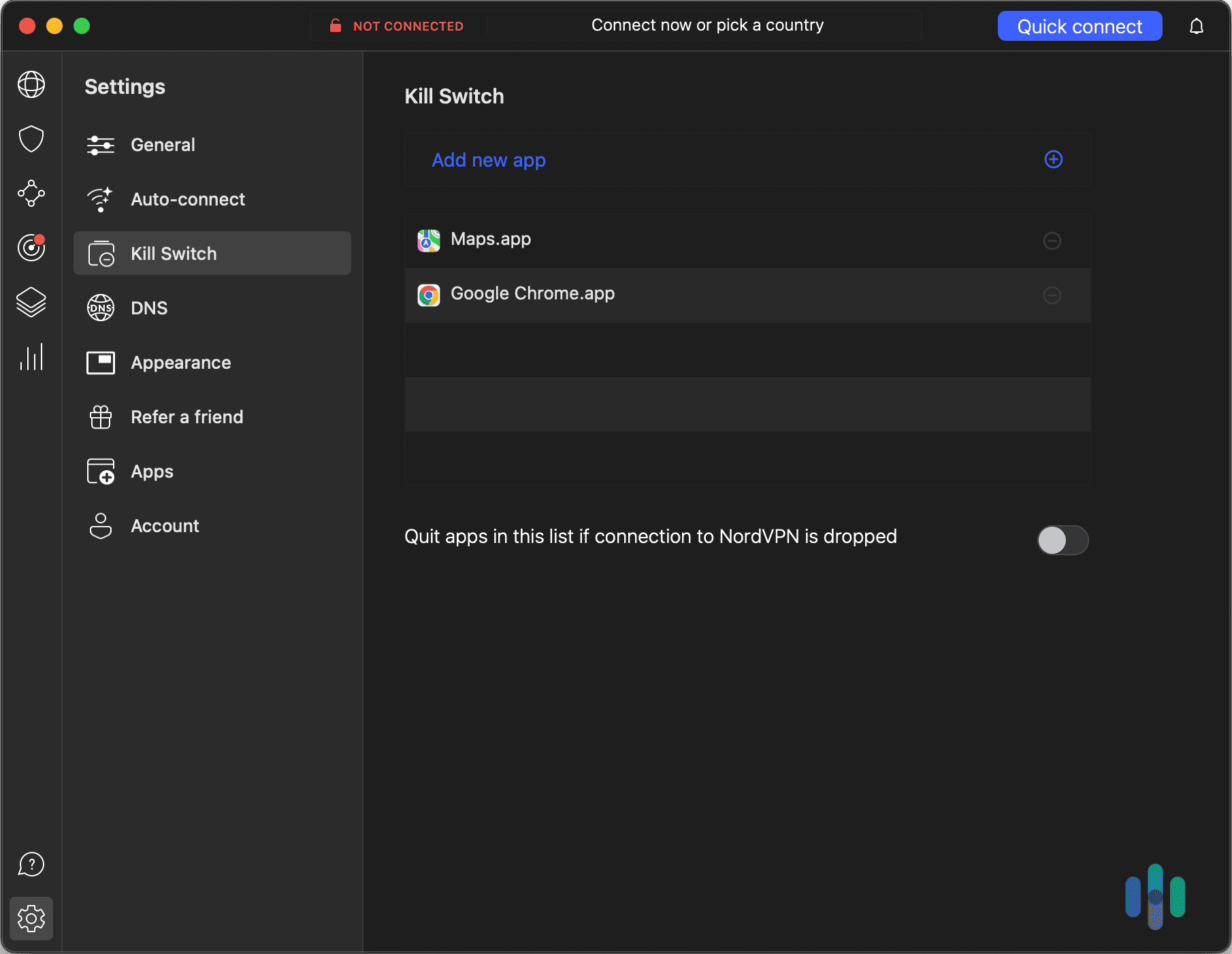
VPNs work by connecting a user’s device and a (typically public) network via encrypted tunnel. The tunnel encrypts the user’s online activity and hides their IP address, replacing it with the IP address of the private server the user connected to. To transmit the data from the device to the private server, VPNs use internet protocols that put the data in packets and make sure it gets sent in the proper order. In case the VPN fails, most come with kill switches that will shut down all windows or apps with web traffic, leaving the user protected and private online.
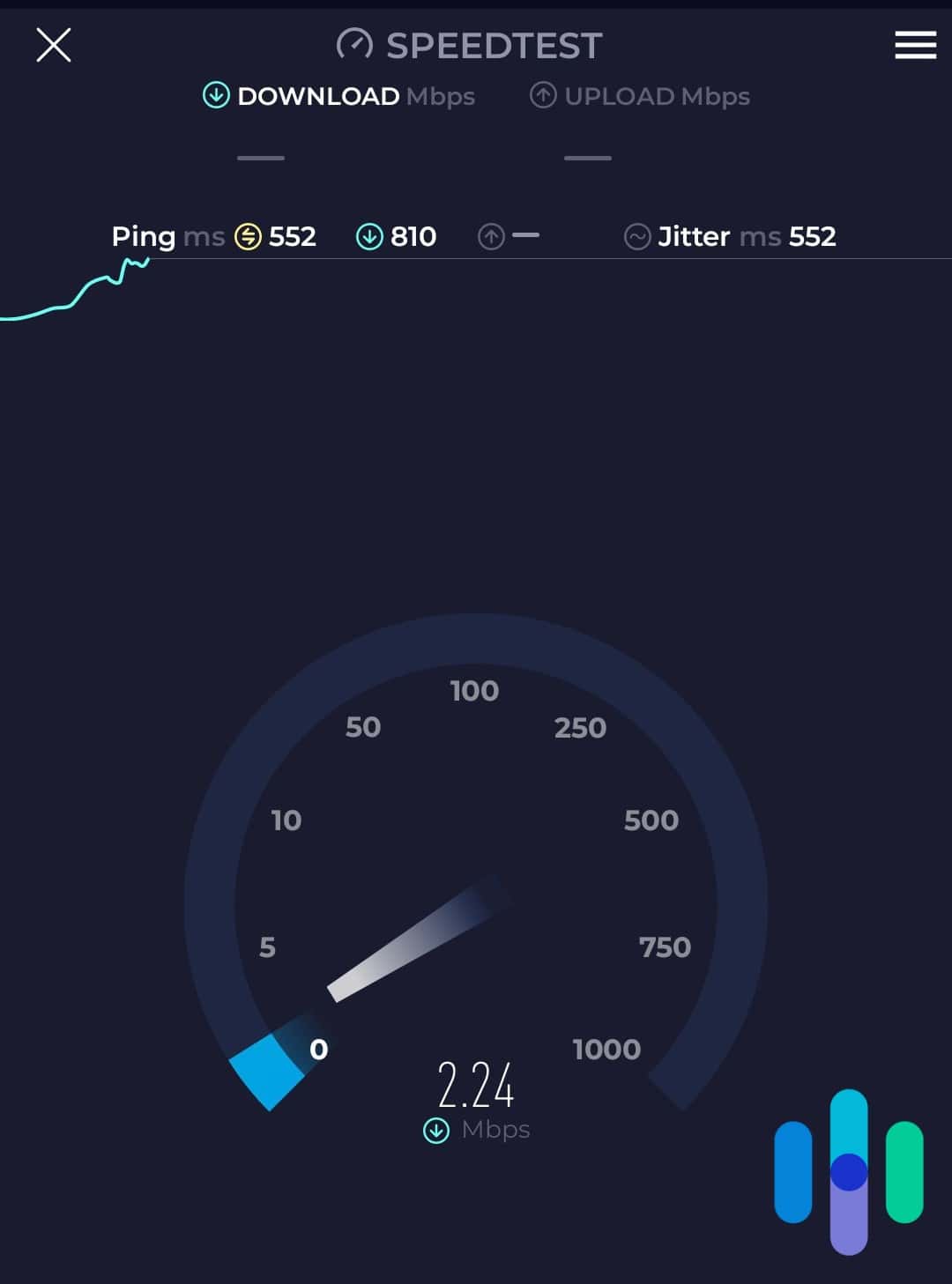
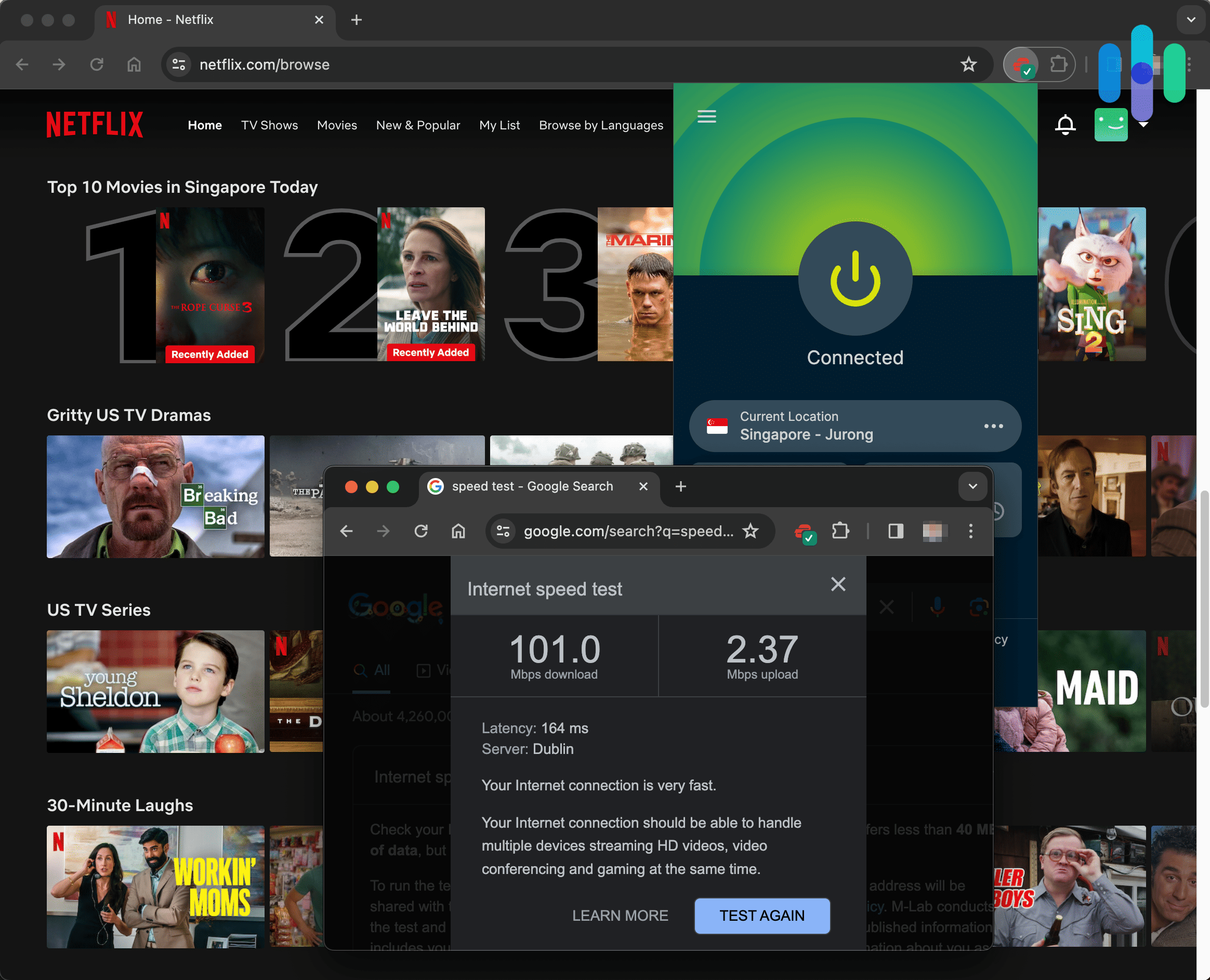
Watch Out: One of the downsides of a VPN is that it can bog down your system, causing it to run slower.
What To Look For in a VPN
There are many criteria to consider when you’re choosing a VPN. These are the most important features to keep an eye out for:
-
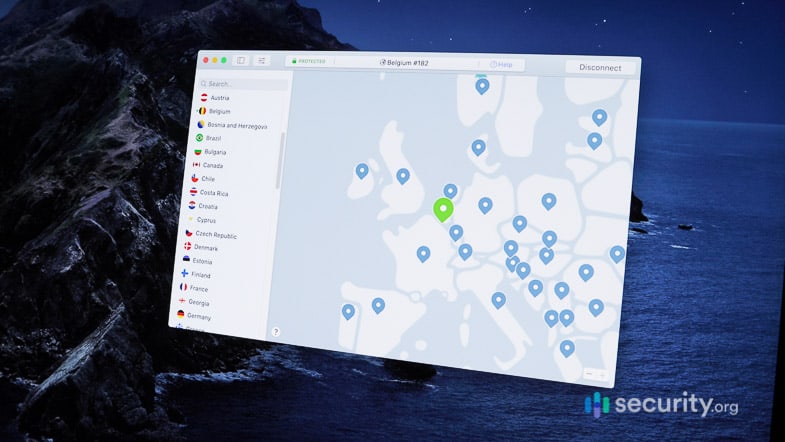
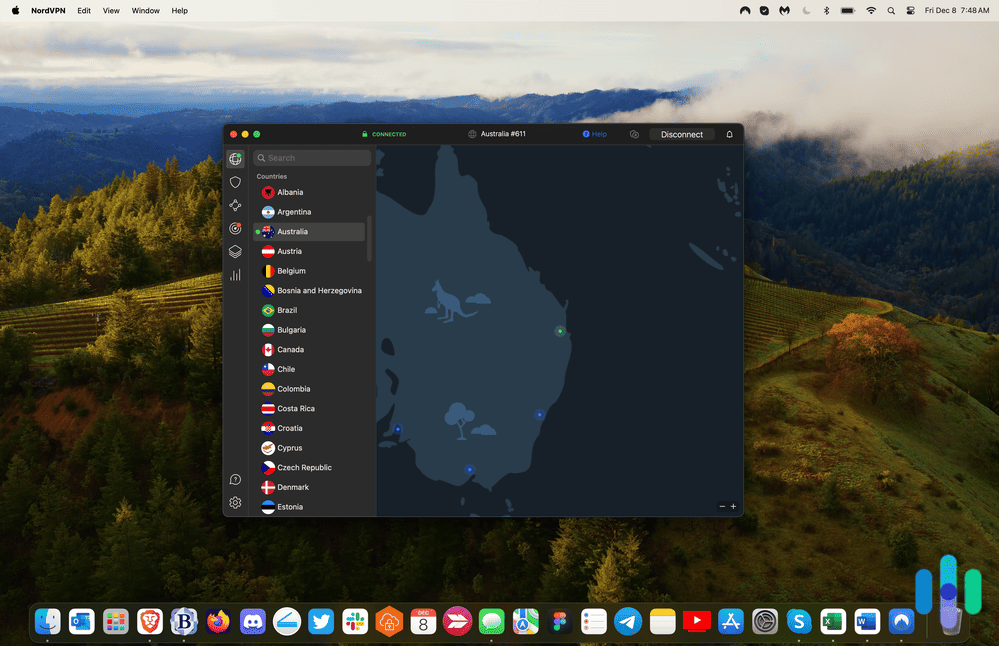
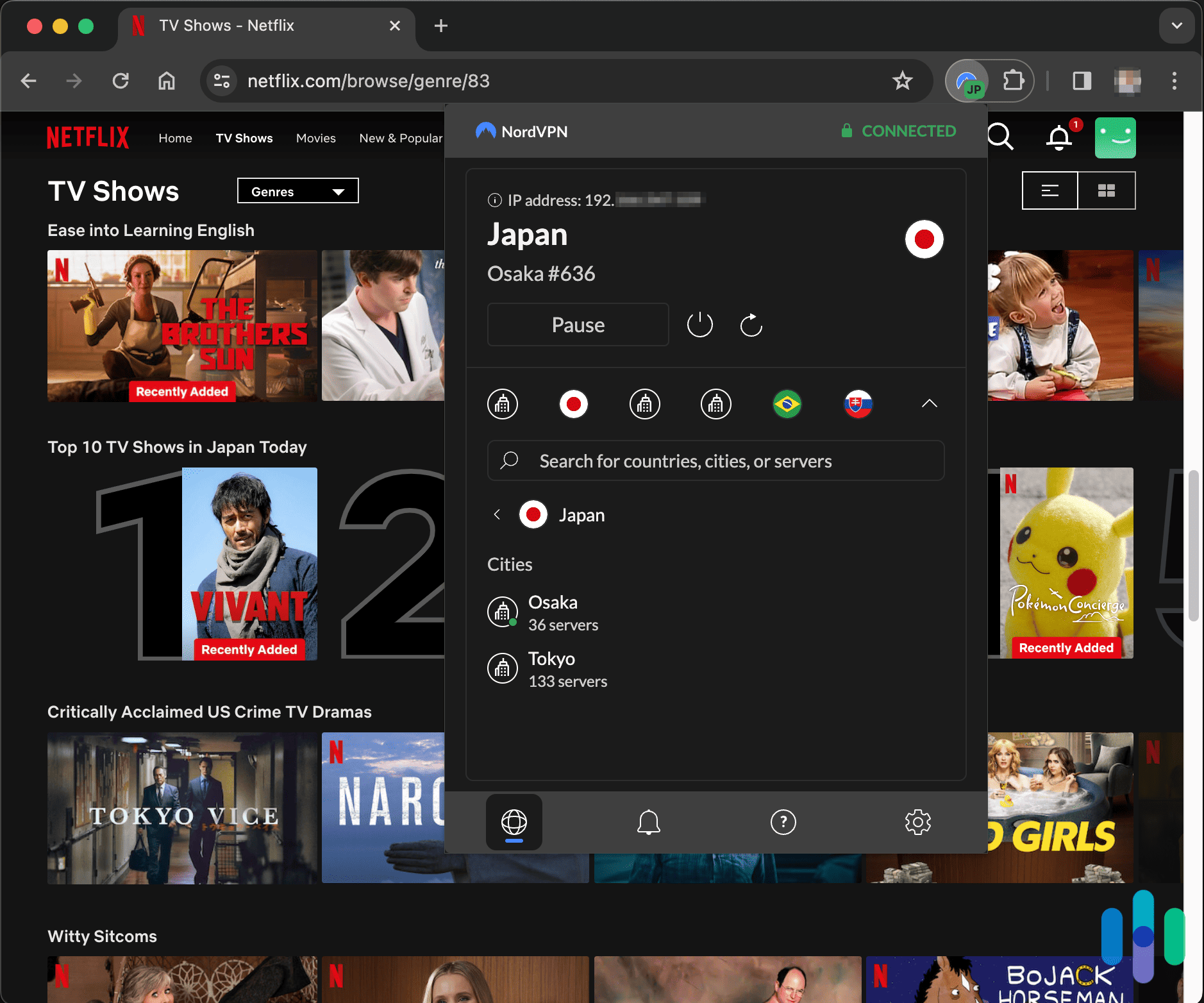
- Number of servers: Logging in to different servers can lead to a whole different internet experience, especially when you’re watching Netflix with a VPN.
- Speed: The trade-off for VPN security is typically speed, and you don’t want to slow down your computer or devices too much.
- Encryption: We check for AES-256, the gold standard for encryption.
- Privacy policy: Make sure the company is not keeping track of too much data, especially unnecessary information like your browsing activity or IP address.
- Headquarters location: Where companies are based has implications for what data laws they have to abide by and if they can be forced to surrender your data to the government. We prefer VPN companies headquartered in countries outside the jurisdiction of the Five Eyes, Nine Eyes, and 14 Eyes alliance or in countries with no strict data retention laws.
- Kill switch: A kill switch is a fail-safe that automatically shuts down activity in the unlikely event that a VPN disconnects.
- IP addresses: These can be dynamic or static. Dynamic IP addresses change every time you connect to the VPN, and static IP addresses don’t change. Dynamic is preferable, but static is OK if many users share the IP address.
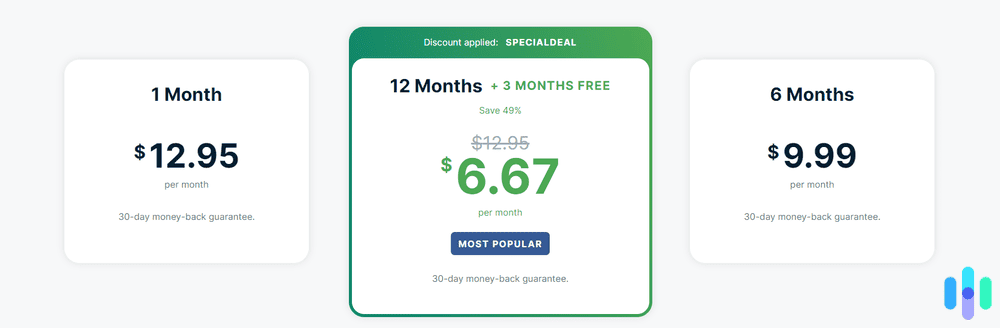
- Cost: A service might have everything you need, but it still needs to fit into your budget. VPN services cost from $3 to $15 per month, with the best deals usually tied to annual or multi-year subscriptions. There are also free VPNs out there, though they almost always come with data caps or feature limitations. If you’re serious about protection, we recommend choosing a paid plan.
- Customer service options: We prefer a variety of customer support options, including email, live chat, and phone.
- DDoS protection features: Look for VPNs that specifically advertise DDoS protection. We also recommend looking for features like automatic server switching if an attack is detected.
Conclusion
VPNs are your first line of defense against DDoS attacks, but success isn’t guaranteed. VPN companies could have poorly implemented DDoS protection, and attackers might already have your IP address, in which case there’s not much a VPN can do. However, when used correctly and set up in advance of an attack, VPNs are one of the best tactics to prevent DDoS attacks. We recommend combining VPNs with firewalls and regular IP address changes to get the protection you need to stay safe online.
Most Common Questions
Here are the questions we get most frequently about VPNs and stopping DDoS attacks.
-
Does changing your IP stop DDoS attacks?
No, if you are already under a DDoS attack, resetting your IP address won’t help much. However, resetting your IP address every few days is a good habit to develop if you’ve been the target of multiple DDoS attacks, or if you’re a streamer or a highly visible gamer. While changing your IP address won’t prevent an attacker from searching for your new IP address, it can delay them from finding it.
-
Are DDoS attacks illegal?
Yes, DDoS attacks are illegal under the U.S. Computer Fraud and Abuse Act. Starting a DDoS attack against a network without permission will cost perpetrators up to 10 years in prison and up to $500,000 in fines.
-
How can I tell if I'm being DDoSed?
There are a few telltale signs of being DDoSed. You’ll notice that your server slows down and responds with a 503 due to service outage. The TTL (time to live) on a ping request could time out, or, if you use the same connection for internal software, your employees could notice speed issues. Log analysis solutions could also show a huge spike in traffic, indicating that not all traffic is organic.
-
Can you call the cops for a DDoS attack?
You can report a DDoS attack to law enforcement if you were threatened or blackmailed, or if you lost money as a result of the attack. In most cases, contact your national web crime unit. In the U.S., file a complaint online with the FBI’s Internet Crime Complaint Center.
-
What's the difference between a VPN and DDoS protection services?
VPNs can mask your IP address to help prevent targeted attacks, but dedicated DDoS protection services like Cloudflare or Akamai offer a deeper layer of defense. These services scrub malicious traffic at the network level before it ever reaches your infrastructure, which is something a VPN can’t do alone. For the strongest setup, we recommend pairing a VPN for everyday privacy with a purpose-built DDoS protection service for your business or gaming environment.