Something you might not know about Security.org is that we consist of experts in many areas of security, including home security and digital security. And sometimes, those areas overlap. This is one of those times.
Smart security systems that connect to the internet provide a lot of convenience. For starters, they allow us to view live footage and speak to visitors through security cameras. They also let us control smart home devices such as smart lights and smart locks. But just like with anything internet-connected, the cybersecurity specialists in us worry about security system hacking. Are smart security systems safe to use, despite that scary possibility? Let’s investigate.

Can Home Security Systems Be Hacked?
In a word, yes. Any device connected to the internet can be hacked if not properly secured. That is the key point of this whole guide. If you have good digital security hygiene, security system hacking is less of a concern. But if you leave your internet-connected security equipment vulnerable to cyberattacks, then you should worry. Hacking is a real possibility, and we should know – we’ve watched publicly posted live streams from hacked security cameras ourselves.
FYI: There are websites that show live video feeds from hacked security cameras all over the world. We will not mention the names of those sites for the safety and privacy of those affected by the hacking, but it seems that a common theme for those hacked security cameras is that their owners didn’t change the default password.
What Makes Security Systems and Cameras Vulnerable to Hacking?
Hearing about security camera and security system hacking is scary, but let us assure you that most of the reasons cameras get hacked are within the control of the user and/or the manufacturer. So really, if you don’t want your cameras to get hacked – and who does? – you should adopt good digital security practices and avoid home security products that are not digitally secure.
In any case, these are the most common causes of security camera and security system hacking.
- Lack of a strong password: Our study on America’s password habits has found that nearly half of Americans use passwords of only eight characters or less. That’s easy to guess. Moreover, some users don’t make it a habit to change their default passwords. An IP camera, for example, comes with a default password that is the same for all users. If you don’t change it to a secure password, all a hacker needs to do is find out your camera’s IP address. To see if your password is strong, use our tool, how secure is your password.
- Lack of authentication: Even with strong passwords, accounts can still get hacked if advanced authentication isn’t set up. Two-factor authentication requires an additional passcode sent to a mobile device while biometric authentication requires fingerprint or facial recognition, preventing unauthorized access.
- Data breaches: Sometimes, a company will undergo a data breach where a hacker breaks into its system and steals users’ credentials. For example, in 2019, Ring had a data breach that affected over 3,000 users.1 This led to people logging into other people’s accounts and viewing their live footage, which is clearly a huge privacy violation. In response, Ring mandated two-factor authentication and urged users to change their passwords ASAP.
- Lack of encryption: Not to come down too hard on Ring, but another issue they had was a lack of encryption, meaning that the data was visible to both the user and the receiver on both ends without an exchange of a secret handshake or key. While the user can’t do anything about encryption, we recommend shopping for systems with end-to-end encryption built in from the jump. And note that Ring also eventually added end-to-end encryption to all of its camera devices, proving the necessity of encryption in the first place.
- Lost devices: Finally, lost devices, like mobile phones or tablets without passcodes, can allow people easy access to home security systems and camera monitoring.
Pro Tip: Lost your phone? Learn how to protect your personal information on your lost device.
How Easy Is It To Hack into Security Systems?
First, let’s define hacking, a term that most of us recognize but may not understand completely. Hacking is when people exploit vulnerabilities to break into computer systems, with hopes of:
- Blocking access to system
- Gaining access to other devices in the same network
- Gathering data.
There’s no clear answer we can give you on how easy it is to hack into security systems, as it depends on the system itself. If it doesn’t have or require passwords or advanced authentication, it’s easier to hack than a system that does. Data breaches also make hacking easier as does lack of encryption. However, a security system that adheres to the above best practices isn’t easily hacked (although again, anything connected to the web is technically vulnerable to hacking).
How Hacks Happen: Types of Security System Attacks
How do hacks happen, exactly?
- Phishing: The easiest and most common method of hacking is through social engineering, a fancy way of asking for people’s usernames and passwords. Social engineering occurs via phishing emails or text messages that impersonate legitimate websites. When people click on the phishing links, they’re led to fake website login pages, where they type in their credentials, unknowingly giving them to hackers. In security systems, the aspect most vulnerable to this type of attack is the app. If a hacker manages to access your app, they’d be able to monitor your system (i.e. find out if you’re home or away based on how the system is armed).
- Programming attacks: While phishing is the most common cause of security system hacks, we can’t count out programming. Programming-based hacks are much harder to do than phishing, as they require evaluating a system’s vulnerabilities and gaining full administrative privileges within it.
- Brute-force attacks: Brute-force attacks occur when a hacker simply guesses a user’s password until they’re able to log in. Note that many online accounts lock access after a certain number of attempts, making these attacks pretty antiquated.
- Man-in-the-middle attacks: In contrast, man-in-the-middle attacks are programming-based. In essence, a hacker needs to capture data packets to get passwords, intercepting the sender and receiver and “listening” for login credentials.
- Physical access: Finally, physical access means that the hacker can, well, physically access a device on a long-term basis, gaining access to sensitive information.2
How To Identify Hacked Security Systems
How do you know when you’ve been hacked? Here are some key red flags to watch out for:
- Unrecognizable noise is coming out of your cameras’ speakers
- Your cameras’ LED lights are on unexpectedly
- Your cameras’ pan and/or tilt unexpectedly
- Your password stops working, but you haven’t changed it
- Your account was accessed on an unknown device.
It’s important to look out for these red flags, as hacking of security systems and cameras is, above all, an enormous violation of privacy.
Vulnerability of Security Systems to Hacking
While we don’t want you to add security system hacks to the list of your biggest fears, a few recent hacks have stayed in our memory, and in the memory of the entire smart home market in general. Specifically, ADT, SimpliSafe and Ring Alarm have all experienced hackings to varying degrees, and although each company has taken steps to address these attacks, we still want our readers to be informed about their complicated history.
- ADT: ADT is far and wide the most recognized and trusted name in smart home security, with over 140 years in business. However, even this safety vanguard couldn’t prevent a hacking from taking place— mainly because, as they say in the movies, “the call was coming from inside the house”. By that, we mean that a former ADT installer had intentionally never taken his personal email address off of a system’s account after setup was over so he could spy on users at home. However, the installer himself pled guilty and ADT is resolving concerns with all affected customers,3 so this physical access hack is far from a common occurrence for ADT. To learn more, read our ADT review.

- SimpliSafe: Unlike ADT, hacks aren’t uncommon for the newer security company SimpliSafe. Rather, in 2019 a Youtube account named LockPickingLawyer discovered that they could hack the SimpliSafe security system with a $2 dongle from Amazon when physically near the system. The access was so complete, in fact, that they could even disable SimpliSafe’s door/window sensors,4 which is more than a little unsettling. That being said, SimpliSafe maintains that they’ve never received reports of hacks from over three million U.S customers, so ultimately, customers can decide for themselves whether to trust SimpliSafe or not. Read more in our SimpliSafe review.

- Ring Alarm: Ring, Amazon’s smart home security superstar, has not only Ring Alarm, their security system, but also a huge variety of Ring cameras and Ring video doorbells. However, as mentioned earlier, they’ve also had their fair share of hackings after a data breach exposed user credentials in 2019. In response, Ring has launched end-to-end encryption, mandated two-factor authentication and created privacy zones to hide sensitive areas from view. So while the idea of being spied on at home still remains in the back of our heads, we appreciate Ring’s swift responses and privacy improvements to their products. You can dive deeper in our Ring Alarm review, our Ring cameras review, or our Ring video doorbells review.

Types of Security Systems
Obviously, the security system safest from hacking is a local alarm system, but that’s not going to work for modern-day users who want notifications and apps. However, there are some middle grounds that offer the user the option to use the internet or not. For example, many Reolink cameras don’t require Wi-Fi. Rather, they record directly onto their micro-SD cards, which are only hackable if they’re stolen physically.
But if you want to be alerted when any of your alarms or sensors go off, look for a system with required passwords, authentication, and end-to-end encryption. And, if you’re concerned about someone hacking into your electrical system to disable your security sensors and cameras, battery-operated devices may be your best bet. As an alternative, look for a system with cellular or landline backup that will stay on even in a power outage. There are many different types of security systems, and there’s no hard and fast rules about which types are safest. Regardless, here’s an overview of the main types of systems:
- DIY security systems: DIY security systems means that users install them themselves, an increasingly popular option in the smart home security market. Users will typically self-monitor these systems through their respective mobile apps, although professional monitoring may be an option, as well.
- Wireless security systems: Wireless security systems have mostly battery-powered components that aren’t reliant on a home’s electrical system. However, many users prefer to add on landline or cellular backup in case the Wi-Fi fails.
- Professional security systems: Last but not least, professional security systems are either professionally installed, professionally monitored or both.
At the end of the day, it’s not the type of security system that determines how susceptible it is to hacking, but the safeguards that both the company and the user implements to prevent access by hackers.
How To Protect Your Security System From Hacking
While you can’t dictate that a company mandates two-factor authentication like Ring Alarm, there are some areas that a user can control in order to make their home security system less hackable:
FYI: On iPhones and iPads, multi-factor authentication is either Touch ID or Face ID, depending on your model.
- Password hygiene: Of course, use a strong password on both your security system app and your Wi-Fi network, and don’t share your password over email or text.
- Turn authentication on: If possible, turn on two-factor authentication or even better, multi-factor authentication.
- Choose encryption: Do a little research and find out if the app has end-to-end encryption or not. As we’ve seen with previous hacks, this isn’t the case industry-wide, unfortunately.
- Use antivirus software: Most antivirus software includes protection against phishing and network intruders, making it a great catch-all to prevent hackings. Make sure you install antivirus software on all devices you use to access your security system, especially your smartphone.
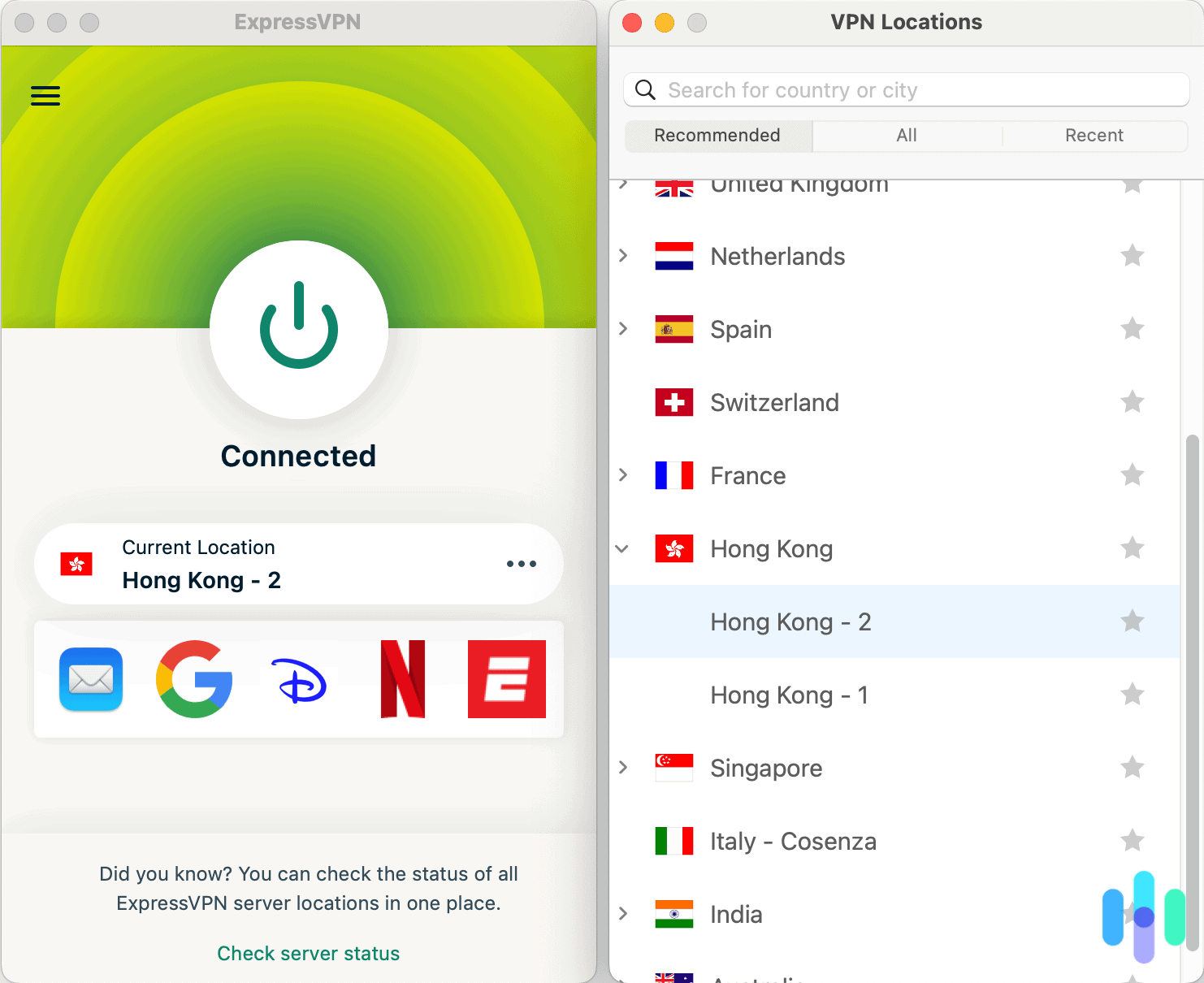
- Use a VPN: This won’t work on all types of security systems and cameras, but it’s worth a shot. Create a Wi-Fi network specifically for your smart security devices, and then encrypt that network using a VPN. You’ll most likely need a VPN router to accomplish that.
- Choose secure protocols: Security protocols are what encrypts data between the sender and the user, and they rely on encryption keys. There are three different types of wireless security protocols, but some are more secure than others:
- WEP: Wired Equivalent Privacy was the first wireless security protocol, invented in the late 1990s, and just like the Backstreet Boys, it’s out of fashion. Rather, opt for the following two, more effective protocols, WPA or WPA2.
- WPA: Wi-Fi Protected Access replaced WEP in 2003 and generates 256-bit keys for data packets.
- WPA2: The most secure method of all is WPA2, which replaced WPA in 2004. It’s got the best authentication and encryption methods, making it the most secure protocol for personal and business use alike.5
Recap
Since the internet permeates nearly every corner of our lives, we can’t live in fear of hacking (and stay sane, anyway). Rather, it’s best to take preventative measures to protect your home security system, so it can protect you, your home and your family.
Frequently Asked Questions
We’re not done yet! Here are the questions we get the most about hackings of security systems, a hot-button issue that affects any smart security system-user.
-
Are home security systems hackable?
Not all home security systems are hackable. Local alarm systems, for instance, aren’t connected to the internet and thus aren’t hackable. Smart home security systems, on the other hand, are connected to the internet, so there is a possibility of hacking, like any other internet-connected product.
-
What is the safest home security system?
The safest home security system, according to Security.org’s privacy rating database, is Frontpoint. Frontpoint updates its software regularly, allows customers to delete their data and has no history of surveillance.
-
How secure are wireless alarm systems?
It’s impossible to say if wireless alarm systems are secure or not without knowing more information. For example, wireless alarm systems with end-to-end encryption, required passwords and advanced authentication, and WPA protocols are more secure than systems with no encryption, no mandated passwords or authentication, and WEP protocols. In short, it depends on the system itself.
-
Can SimpliSafe be hacked?
In 2019, a Youtube account called LockPickingLawyer found that SimpliSafe could be hacked if someone was nearby with a $2 dongle from Amazon. However, SimpliSafe denies this claim and says that they’ve never had reported hacks from their three million U.S customers.