You probably don’t have to know much about computer code or software to know that a computer worm is a bad thing. It is a type of malware that’s different from viruses in that a computer worm can reproduce on its own, in the same way a biological worm can reproduce asexually.
Some computer worms are benign, and others can wreak havoc on your computer or device. Let’s get into the details of what a computer worm is and what you can do to keep them from crippling your devices. Spoiler alert: A good antivirus program is the best way to protect yourself from computer worms.
What Is a Computer Worm and Can Antivirus Software Fight It?
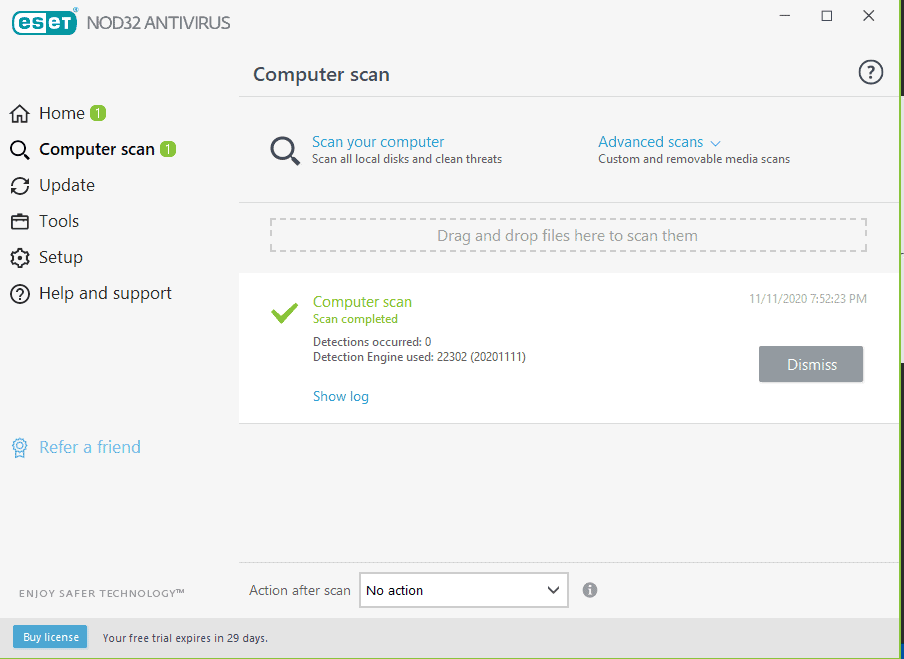
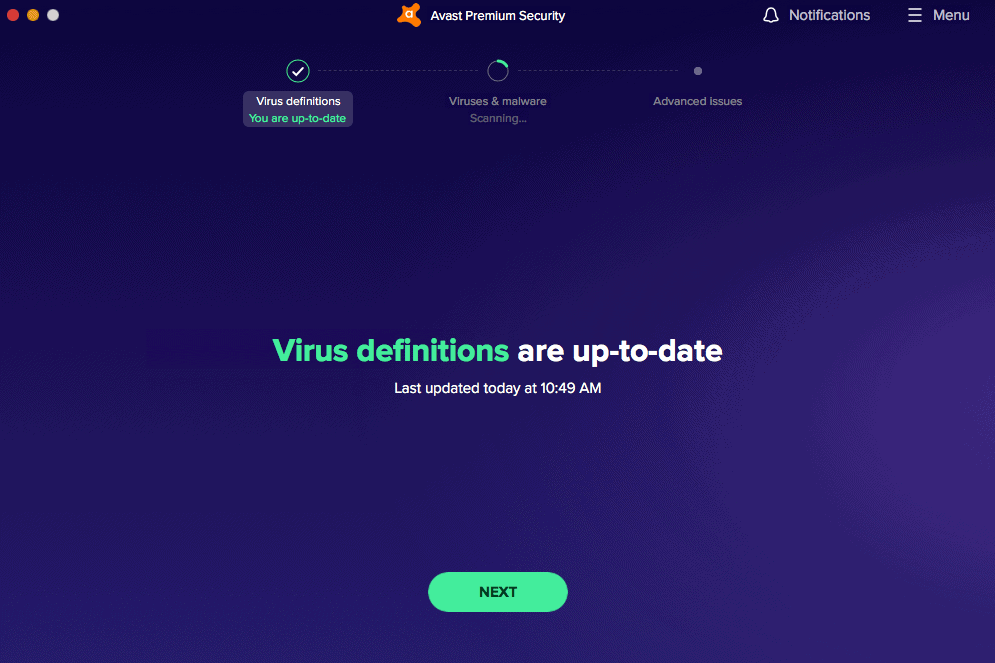
By definition, a computer worm is a type of malware. Its most distinct feature? Its ability to spread quickly without human interaction. It self-replicates once it gets into your computer, smartphone, or tablet, which is why it’s one of the scariest types of malware. Fortunately, the best pieces of antivirus software on the market are trained to fight worms by detecting, quarantining, and removing them. Here are our top-picks:
How Does a Computer Worm Work?
In the same way you want to keep your pets (and your body) worm-free, you want to keep computer worms out of your electronic devices. Both types of worms are self-replicating, but computer worms can act with deliberate, malicious intent. When a computer worm gets into your device, there are three types of consequences:
- Infestation: Some computer worms simply replicate, which is harmless at first but can get to the point where they fill your storage space and system memory, crashing your device.
- Infection: Having computer worms can open up your devices to other types of malware. Sometimes, it’s the worm itself that downloads malware. Other times, the worm modifies or deletes files and settings (e.g. Windows Defender settings), leaving you more vulnerable to attacks.
- Parasitism: Some computer worms are parasitic, stealing vital data from your devices by installing backdoor programs and spyware. The infamous WannaCry worm (aka WannaCryptor) is an example.1
How a Worm Spreads
A computer worm takes advantage of system vulnerabilities to accelerate its spread. It can jump from one device to another through different means, be that an email attachment, malicious link, or local area network (LAN). Here are the most common ways a computer worm spreads:
- The internet: Most devices connect to the internet via a network, which is a convenient superhighway for computer worms to spread. Once a worm infiltrates a device, it can spread to other devices throughout the LAN.
- Emails: Have you ever received a suspicious email with a link or an attachment from a stranger? That’s how some hackers spread malware, including worms. There are also worms that can make email programs such as Outlook send emails containing the malware to contacts autonomously.
- File-sharing platforms: Unless you know where it’s from, there’s really no way to tell if the file you’re downloading from a peer-to-peer file sharing platform contains malware. That’s why worms spread easily through such platforms.
- Instant messaging: Similar to malicious emails attachments, instant messages may be computer worms posing as harmless links or attachments.
- Smartphones: Smartphones are ideal worm carriers because we tend to connect our phones to multiple Wi-Fi networks, which could accelerate the spread of worms.
- Removable drives: A flash drive or a removable hard drive can get infected if plugged into an infected computer. Subsequently, infected removable drives can spread the worm when they are connected to different computers.
- Installer downloads: Looking to pirate a software program? Be careful – phishy websites may offer downloadable software installers that are actually malware.
- Torrent: You may think you’re downloading a pirated version of “The Avengers: Infinity War” (which is illegal, by the way), but it could actually contain a worm. The bottom line is, don’t pirate anything or use a VPN when torrenting non-copyrighted content.
- IoT devices: It’s scary to think that our smart home devices can turn against us, but according to researchers, the possibility is real. In a controlled environment, researchers were able to weaponize a single smart bulb to spread a computer worm to neighboring Zigbee IoT devices.2
The Damaging Impact of Computer Worms
Computer worms have caused billions of dollars in damages over the past few decades. The MyDoom worm alone caused approximately $38.5 billion in economic damages when it first came out in 2004.3 It targeted business websites, causing massive slowdown of services, bandwidth clogging, productivity delays, and overall loss of business.
Computer worms can hit close to home for everyday users, too. Depending on its payload — the code that carries out the malware’s mission — a worm can modify or wipe your files, lock you out of important folders, or seriously bog down your device’s performance. Some attackers even deploy worms specifically to harvest personal data, which can lead to identity theft. That’s why knowing how to protect yourself against computer worms isn’t just good practice — it’s essential.
Infamous Examples of Computer Worms
There have been many significant computer worm attacks in the past, and the scary thing is, some of them exist to this day. The MyDoom worm, for instance, has been sending itself through email attachments for over two decades since its creation in January 2004 — if it were a person, it’d be old enough to rent a car. Here are several other computer worms that have caused significant damage in the past:
- Morris worm: The Morris worm was the first computer worm with real-world impact. A computer science student accidentally created the worm in 1988, which crashed many of the 6,000 computers it affected.
- WannaCry/WannaCryptor: The WannaCry worm encrypted files of Windows users in 2017 and asked for a ransom in exchange for their files. It was a worm that spread ransomware.
- ILOVEYOU/Love Bug/Love Letter worm: The ILOVEYOU worm spread through emails in 2000 posing as a love letter attachment. It infected over 10 million computers.
- Nimda: Nimda was the first computer worm that modified existing websites to offer malicious downloads.4 It spread by sending mass emails and then began propagating in LANs.
- Code Red: The Code Red worm initiated a DDoS attack (distributed denial of service) aimed at the U.S. White House using infected computers. This attack forced the White House and its web servers to change IP addresses.
- MSBlast/Blaster: Originally, the Blaster displayed two messages when executed: “I just want to say LOVE YOU SAN” and “billy gates why do you make this possible ? Stop making money and fix your software!!” However, it also forced computers to shut down as a side effect.
- Sobig worm: The Sobig worm had several versions, from Sobig.A to Sobig.F. It spread as an email attachment with common subject lines such as “Thank You” or “Re: Details.” Once it infected a computer, the worm searched for its next targets by sending 20 or more emails to the user’s contacts.
- Jerusalem/BlackBox worm: This was a type of worm that ate computer resources. When triggered, it deleted any program run on Friday the 13th of any year. It also infected .exe files repeatedly until they grew too large for the computer to handle.
The History of Computer Worms
Computer worms have evolved over the decades. What started out as a simple programming mistake by a computer science student is now a dangerous hacking tool.
The Worm That Started It All
The Morris worm (aka The Worm) was the very first computer worm with real-world impact. It wreaked havoc in 1988. Named after its creator, Robert Morris, the Morris worm was a software program that exploited the vulnerabilities of email protocols during that time.
Morris created The Worm for a good cause – to spread awareness about those vulnerabilities – but it ended up causing far greater damage than he anticipated. Within 24 hours, it spread to about 10-percent of all internet-connected computers on the planet back then. Granted, there were only about 60,000 internet-connected computers in 1988, but the rate at which The Worm spread was unprecedented. Even worse, it spread so rapidly that it rendered most of the infected computers unusable.
The Morris worm did achieve its goal of highlighting network weaknesses, as it gained significant media attention. But the cost was great. Financially, the U.S. Government Accountability Office estimated damages amounting to $10 million.6 Ouch!
Computer Worms as Pranks
For some time after the Morris worm incident, hackers used computer worms for pranks. For instance, the Father Christmas worm infiltrated NASA’s network to deliver greetings on Christmas Eve, 1988.7 Though harmless, the worm prompted NASA to strengthen its network security measures, and it’s a good thing they did. The measures they implemented helped foil a similar computer worm attack three weeks later. In the following decades, however, computer worms became more and more pesky. In 1999, the Happy99 worm spread through emails and, like the Father Christmas worm, displayed a New Year greeting. However, in the background, it modified system files.8 Similar computer worms spread throughout the early 2000s, with some capable of deleting or modifying files, stealing passwords, defacing websites, and even spreading political views.
The More You Know: A computer worm may exhibit traits of a virus. Known as worm hybrids, this type of malware spreads like a computer worm but with the ability of viruses to alter program codes.
Computer Worms and Cybercriminals
Eventually, cybercriminals found a way to make money out of computer worms, usually at the expense of unsuspecting users. The WannaCry worm mentioned above, for instance, contained ransomware that locked people out of their computers through encryption unless they paid a ransom.
Some computer worms, on the other hand, are just there to cause damage. One example is the Code Red worm, which orchestrated a DDoS attack on the U.S. White House, eventually forcing its servers to change IP addresses.9 Today, computer worms are more sophisticated and destructive than ever — and they’re not slowing down. Ransomware attacks, many of which rely on worm-like propagation, are projected to cost victims globally an estimated $265 billion annually by 2031. That’s why it’s vital for each of us to know how to protect ourselves from this type of malware. But in order to do that, we must first understand the different types of worms, how they spread, and how to detect them.
Types of Computer Worms
Computer worms are usually classified by how they spread. Here are the different types:
- Internet worms: An internet worm jumps from one device to another via the LAN. It starts by infiltrating one computer and then spreads to other vulnerable devices connected to the same internet connection.
- Email worms: An email worm disguises itself as an email attachment. It could come from a contact with a compromised computer or a spam email. You can tell it’s a worm if the attachment has more than one file extension, for instance, “.mp4.exe,” although that’s not always the case. An example of an email worm is the ILOVEYOU worm.10
- File-sharing worms: A file-sharing worm, as the name suggests, comes from peer-to-peer file-sharing platforms. You might think you’re downloading a media file or a software installer, but actually, it could contain a computer worm that activates the moment it enters your device.
- Instant messaging (IM) worms: Much like email worms, an IM worm disguises itself as an attachment or link shared through instant messaging platforms. Sometimes, they even come with creative clickbaits like “This will blow your mind” or “LOL cat” just so IM users will click on them and inadvertently download the worm.
How to Prevent and Get Rid of Computer Worms
Now that we know what to look out for, let’s learn how to get rid of computer worms.
How to Tell if Your Device Has a Worm
The first step is detecting if a worm has infected your computer. Infected computers often show warning signs such as:
- A full hard drive
- Slow performance due to used up resources
- Missing files
- Hidden files or folders
- Unrecognized files or programs
- Programs running or websites opening automatically
- Irregular browser performance
- Unusual program behavior such as notification pop-ups, error messages, etc.
- Emails sent to your email contacts without your knowledge
If you notice one or more of these symptoms on your computer, smartphone, or tablet, then you most likely have a worm. To verify, you could scan your device with antivirus software.
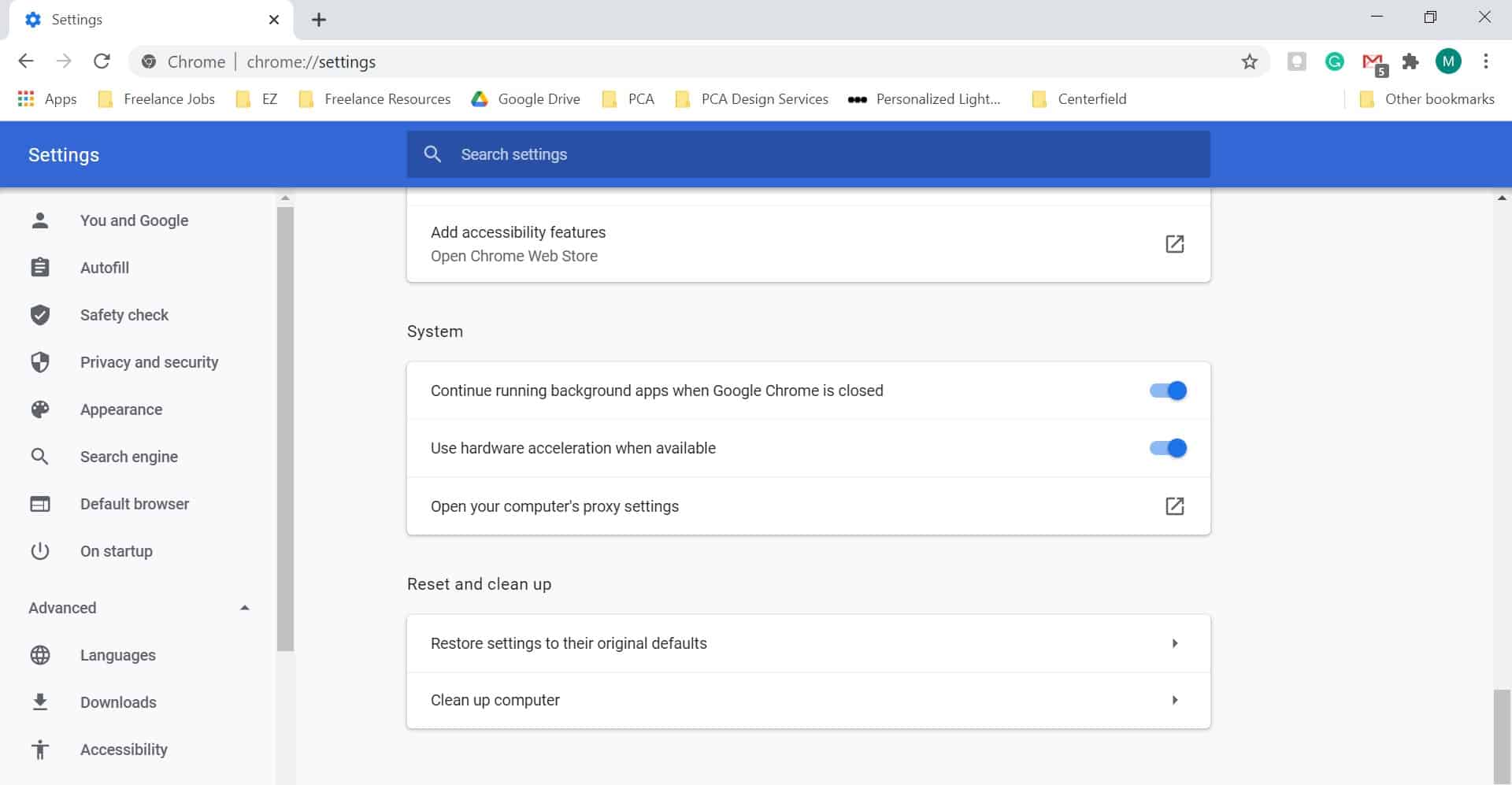
How to Remove a Computer Worm
And if there really is a worm, what do you do now?
- Isolate the device. First, isolate the infected device. Worms can spread through LANs, so disconnect your infected device from the internet and remove it from your LAN.
- Assess the spread. Next, scan your other devices using antivirus software to see if the worm has already spread. If it has, isolate all the other infected devices and perform steps three and four.
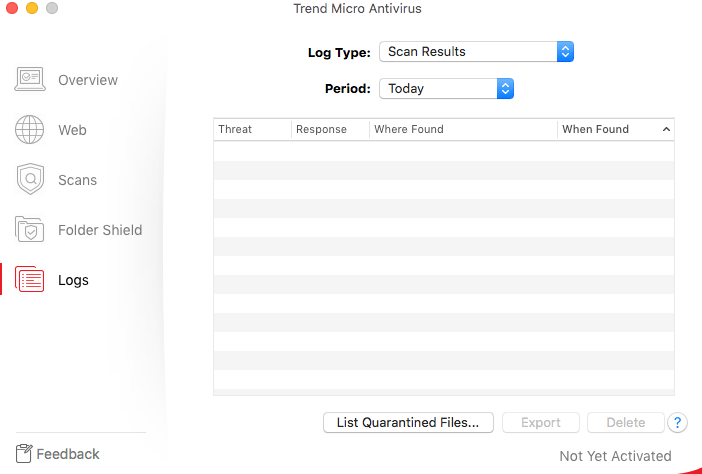
- Remove the worm. The next step is to remove the worm. Most antivirus tools that detect computer worms can also remove them. Once they find a worm, most antivirus software can quarantine or remove the malware automatically.
- If needed, use a specialized worm-removal tool. Some worms are more stubborn. If your antivirus software can’t remove it, search the internet for a worm-removal tool specific to the type of worm on your device. Your antivirus’s scan log should offer a clue as to what type of worm it is.

Prevention Is the Best Cure
When it comes to computer worms, the old saying holds true — an ounce of prevention is worth a pound of cure. Here are a few practical tips to keep worms off your devices:
- Be cautious when opening email attachments or links. It’s best practice to not open an email link or attachment from an unknown sender. It could be a phishing scam or an email blast designed to spread malware. If you’re unsure about the legitimacy of an email or attachment, scan the email or file first using your antivirus.
- Don’t click on pop-up ads while you’re browsing. Computer worms may inject adware into legitimate websites to force their way into devices. A common adware example is an ad that says you’ve won something, or that your computer or device has a virus.
- Use a VPN when torrenting. Avoid using peer-to-peer platforms to download files from unknown sources, but if you really must torrent something, use a VPN.
- Update software regularly. Keep your operating system and programs up to date to remove software vulnerabilities. If possible, enable automatic updates.
- Update your passwords. Do not use default passwords on anything, especially your router configuration, as some worms use default credentials to infect various devices.You can take our password strength test for starters, and use our password guide to create better, stronger passwords.
- Protect your files. Encrypt important files to protect sensitive data on your devices and to keep them safe in case of malware infections.
Protect Yourself With a Strong Antivirus
There’s one more thing you can do to protect yourself against computer worms: Get a strong antivirus software program. Here are some features of antivirus software proven effective in fighting against computer worms:
- On-access scans: Antivirus tools with this feature actively scan your device in the background to detect and prevent the spread of worms. Since computer worms self-replicate without human interaction, having your antivirus protect your device continuously is ideal.
- Email scans: The scope of an antivirus’s malware scan includes your email sometimes. When you open an email that has a link or attachment, the antivirus scans it first and notifies you if it’s safe to open.
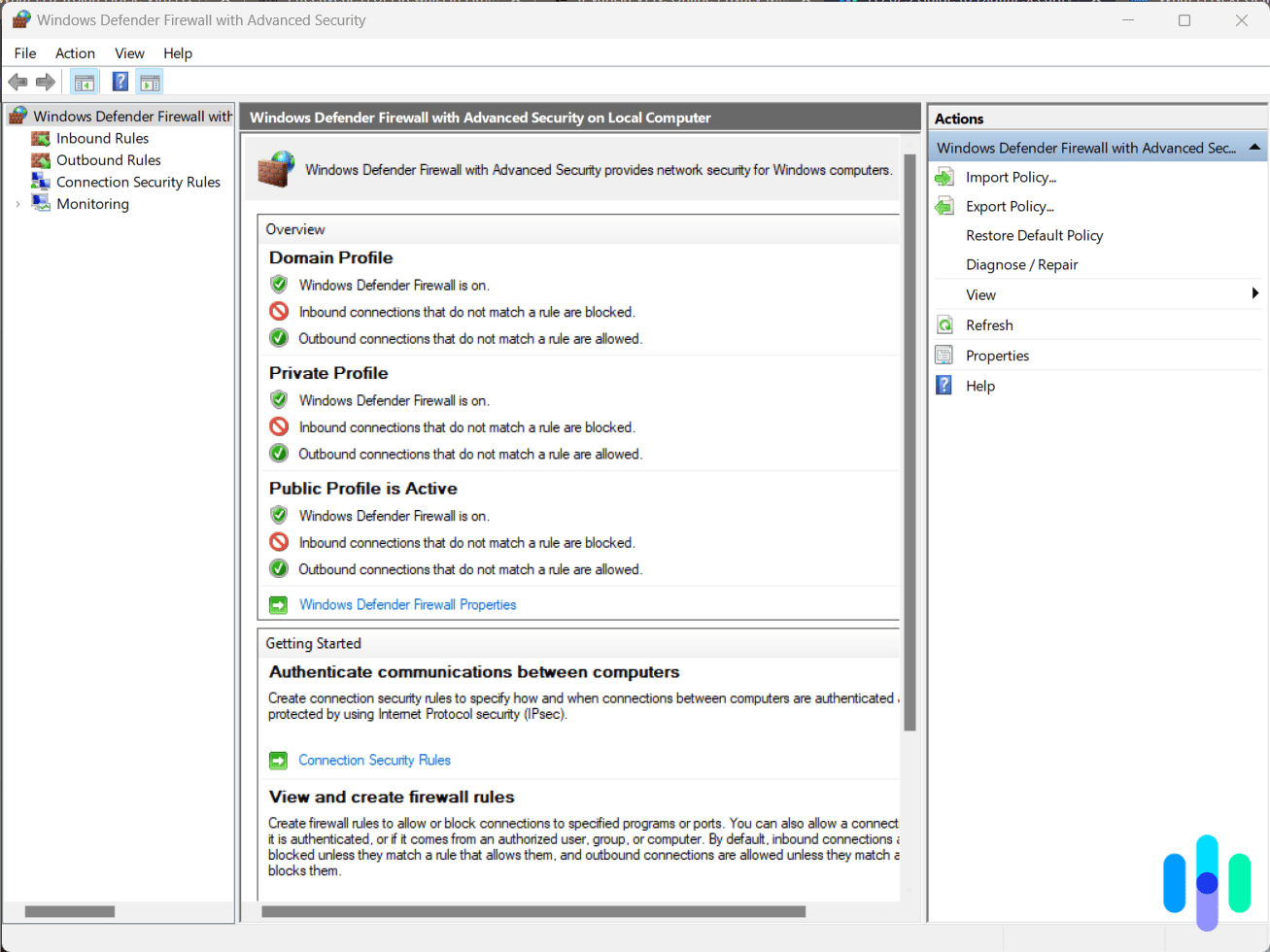
- Firewall: Given the ability of computer worms to spread through networks, an antivirus with a built-in firewall is ideal. If there’s an infected device in your network, the firewall prevents the worm from entering your other devices.
- Automatic and regular updates: Computer worms evolve continuously, so an out-of-date antivirus may not detect newer ones. Automatic and regular updates ensure that your antivirus can detect and stop the latest strains of malware.
- Behavioral-based detection: Some computer worms are harder to detect even with an updated antivirus. Behavioral detection is a handy feature, as it doesn’t rely on malware databases. Instead, it looks for files with suspicious behavior, such as those that self-replicate in the background.
If you’re looking for strong antivirus software, most of the best antivirus tools we’ve tested offer those features.
From Our Experts: A strong antivirus is one that can detect, remove, and prevent all types of malware, including computer worms.
Is a Computer Worm a Virus?
Strictly speaking, a computer worm is not a virus. Worms and viruses are both types of malware, but they behave and spread differently.
What Is a Computer Virus?
A computer virus is a type of malicious program that attaches itself to a legitimate program. When you execute the infected program, the virus also carries out its mission, like deleting or rewriting system files. Most of the time, the infected program continues to function properly, but there are instances where the virus corrupts or overwrites the entire program.
How a Virus Spreads
Unlike worms, viruses do not self-replicate without human interaction. Viruses need the user to execute a program or open a file. A virus may be able to copy itself and move from one device or another. However, once on the new device, it needs action from the user to execute.
Worm vs. Virus vs. Trojan
A trojan virus is another type of malware often confused with worms and viruses, so let’s throw it into the mix. Here’s a handy table that shows the differences between these three types of malware.
| Worm | Virus | Trojan horse | |
|---|---|---|---|
| Purpose | Consume resources, carry out malicious tasks | Carry out malicious tasks | Steal data |
| How it spreads | When a copy of the infected file or software is made, either through storage devices, emails, or the internet | Self-replicates without action from the user and can move from one device to another through email, LANs, instant messaging, and peer-to-peer file-sharing platforms | When a copy of the infected program is created |
| Speed of contagion | Moderate | Fast | Slow |
| Execution | When the infected file or software is launched | As soon as it enters a device | Through an infected program that’s pretending to be a software utility |
In a Nutshell: Worms, viruses, and trojans are all types of malware with different characteristics. A worm spreads the fastest because it self-replicates, a virus causes the most damage because it can alter program codes, and a trojan is hardest to detect because it pretends to be a software utility.
Are There Good Computer Worms?
Researchers have created helpful computer worms called anti-worms or, more simply, helpful worms. The Nachi family of worms, also known as Welchia, is an example.11 It spread like a regular computer virus does, but instead of doing harm, it searched and deleted a harmful computer worm called “Blaster.” In addition, it exploited a Microsoft vulnerability, which allowed it to install Microsoft security patches without permission from the user. Anti-worms seek to perform tasks that its creators feel are useful. However, the morality of creating helpful worms is in question, as they still perform tasks on a person’s computer without their approval.
Recap
Computer worms are genuinely dangerous, and what makes them especially nasty is how fast they spread compared to other malware. Knowing the warning signs of a worm infection and understanding how to remove one are both essential skills for anyone using a connected device today. That said, your best line of defense is still a solid antivirus program. If you haven’t installed one yet, don’t wait — the right antivirus can catch a worm before it ever gets the chance to dig in.
FAQs
Learning what a computer worm is in a few minutes can be taxing, so allow us to review and answer the frequently asked questions about computer worms.
-
What is a computer worm, and how does it work?
A computer worm is a type of malware capable of self-replication without human interaction. By self-replicating, it eats up computer resources, resulting in slowdowns and crashes. A computer worm may also install backdoor programs that hackers can use to infiltrate computers.
-
What are examples of computer worms?
There have been many examples of computer worm outbreaks, such as the Morris worm, the CodeRed worm, the WannaCry worm, and the LoveBug worm.
-
Why is a computer worm dangerous?
A computer worm is dangerous because it carries out a wide variety of attacks, such as crashing computers through self-replication, installing malicious programs, or giving hackers backdoor access to devices.
-
How does a computer worm differ from a virus?
A computer worm differs from a virus in that it doesn’t need a software program to attach itself to. Rather, it infiltrates computers, smartphones, tablets, and networks by exploiting vulnerabilities, and once it has infiltrated, spreads on its own. A virus usually executes only when the user launches a virus-infected program.