One minute you’re on this new software that shows what your baby with a celebrity would look like, and the next you find yourself locked out of your computer. That’s most likely a Trojan attack. Trojans are sneaky, even for malware.
That’s why we spent the last two months digging into the latest Trojan attacks. We learned the ins and outs of how Trojan viruses infect your computer, how you can get rid of them, and steps you can take to avoid them in the future. So, let’s step up your cybersecurity game with a deep dive on Trojan viruses.
What Is a Trojan Virus?
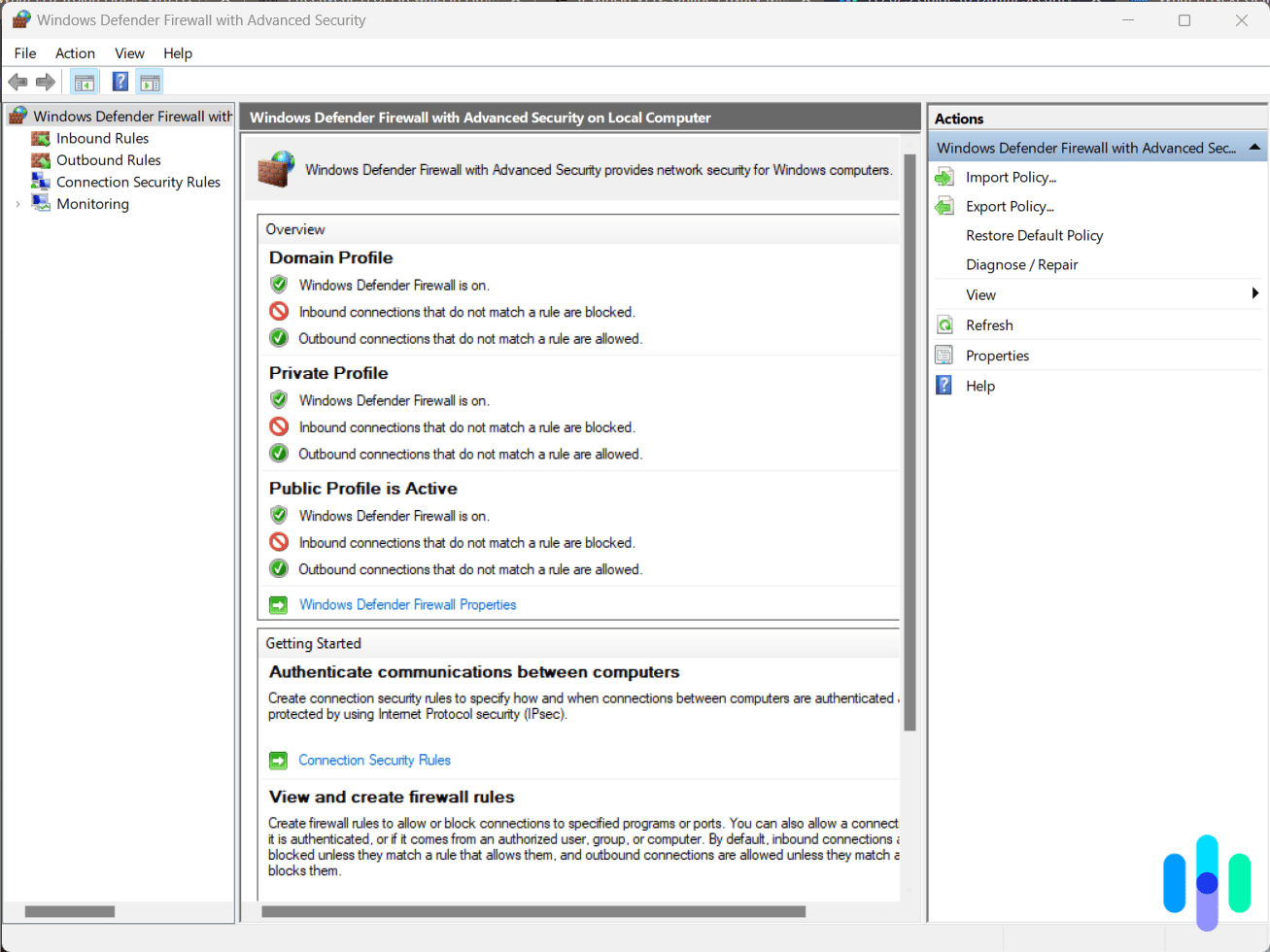
A Trojan is a sneaky type of malware that infiltrates devices by camouflaging as a harmless program. Trojans are hard to detect, even if you’re extra careful. That’s why antivirus software is necessary if you want to protect yourself from this type of malware. We test and rate antivirus software on their ability to detect Trojans all the time, and these are the best ones we’ve tried so far:
A Closer Look At Trojans
A Trojan horse, Trojan malware, or simply a Trojan is a type of malware. It makes up approximately 51.45 percent of all malware,1 which comes as no surprise, given the unique traits of a Trojan. To infiltrate a device, a Trojan presents itself as legitimate software, but hidden beneath its seemingly harmless exterior are malicious codes that can damage your devices.
If you see parallels between Trojan malware and a certain horse of legends, that’s because Trojans actually take their name from the Trojan horse. You know, the wooden horse the Greeks supposedly used to smuggle soldiers into Troy.2 Trojan malware operates similarly to the Greeks’ Trojan horse strategy. The seemingly harmless software is the hollowed-out wooden horse, and the malicious codes hidden within it are the Greek soldiers. Just as the soldiers crept out of the Trojan horse and attacked while the city of Troy slept, malicious codes in Trojan malware carry out hostile attacks on your devices behind your back.
Are Trojans Computer Viruses?
If you read up on Trojans online, you might see the term ‘Trojan virus’ thrown around a lot. While that term is widely accepted, it is incorrect, technically. Trojans and computer viruses are both types of malware, but they each have unique traits.
Did You Know: Trojans, viruses, and worms are all different types of malware. Among those three, Trojans are the best at evading detection, but they also propagate the most slowly because they don’t self-replicate.
The main difference between viruses and Trojans is that viruses self-replicate, while Trojans do not.3 A virus can spread to other devices by creating copies of itself and attaching them to the infected computer’s software, files, and folders. In contrast, when a Trojan infects a device, it stays there until the user copies or downloads the malicious program on a different computer.
How Exactly Do Trojans Work?
Because Trojans don’t self-replicate, most Trojan attacks start with tricking the user into downloading, installing, and executing the malware. For example, a hacker might attach a Trojan installer to an email while employing social engineering to get you to open the attachment. If you do, your device will download and install the Trojan. Ever heard of phishing scams, where scammers send emails from seemingly legitimate business email addresses? Hackers can use similar tactics to spread Trojans.
How Much Damage Can Trojans Do?
So, still thinking that the attachment was legitimate, you unwittingly downloaded and installed a Trojan. What happens now? The malware executes and starts damaging your computer, but the amount of damage depends on how the hacker designed the Trojan. In general, Trojan malware can:
- Delete your files
- Install additional malware
- Modify data on your device
- Copy your data
- Disrupt your device’s performance
- Steal your personal information
- Send messages from your email or phone number
Types of Trojan
In computing, Trojans are classified based on what they’re capable of doing. It all comes down to what the Trojan’s malicious code, also called its payload, does to your device once it’s infected. Most fall into one of the following categories:
- Backdoor Trojan: A backdoor Trojan installs a backdoor program without your knowledge. The program then gives the malware creator remote access to your device.
- Remote access Trojan (RAT): RATs are similar to backdoor Trojans in that they provide hackers remote access to infected devices. However, instead of installing a backdoor program, a RAT itself is a backdoor program masquerading as legitimate software.
- Exploit: Exploits contain codes designed to attack a specific piece of software’s vulnerability. The Trojan executes when you launch the vulnerable software on your infected device.
- Rootkit: A rootkit provides cybercriminals privileged access to restricted areas of a device’s software, such as those that require an administrator’s permission to run. It then hides there or conceals the activity of other malware.
- Banking Trojan: Designed specifically to steal financial credentials, banking Trojans target online banking sessions and payment platforms. They can intercept login data, redirect transactions, or inject fake forms into legitimate banking websites to harvest your account details.
- Infostealer Trojan: These Trojans are built to quietly vacuum up sensitive data — passwords, browser history, cryptocurrency wallet info, and more. Then, it sends that data back to the attacker. Infostealers have surged in recent years and are frequently sold or rented on dark web marketplaces.
- DDoS Trojan: DDoS Trojans hijack multiple computers and use them to perform a distributed denial-of-service (DDoS) attack. Hijacked computers are often called zombies.
- Trojan downloader: After infecting a computer, a Trojan downloader downloads additional malware, such as adware or spyware.
- Trojan dropper: Similar to Trojan downloaders, Trojan droppers install additional malware. However, instead of downloading the malware, which requires an internet connection, Trojan droppers already contain the malicious installation code.
- FakeAV Trojans: FakeAV Trojans masquerade as legitimate antivirus software. They don’t actually protect your devices from malware, of course; they fake the detection of malware and extort money in exchange for its deletion.
- Ransomware Trojan: This type of Trojan operates like ransomware, demanding payment of a ransom to restore or undo the damage it did to the target’s files.
- SMS Trojan: SMS Trojans attack the messaging services of mobile devices to intercept text messages. They can also send text messages to premium-rate messaging numbers. Kaspersky Lab detected the first Android SMS Trojan in 42010.
- Trojan-Spy: Trojan-Spy, as the name suggests, spies on a user’s action using tools like keyloggers or by taking screenshots and sending them back to the malware’s source.
- Trojan-Mailfinder: Hackers primarily use Trojan-Mailfinder to spread malware. This Trojan harvests email contacts from its target device and sends the data back to hackers, which they use to spread malware via email.
- Trojan-ArcBomb: “ArcBomb” is a compound of the words “archive” and “bomb.” A Trojan-ArcBomb bombs large amounts of empty data when the infected computer attempts to unpack archived data.
- Trojan-Clicker: Trojan-Clicker is a form of ad fraud. It makes connections to a specific ad-supported webpage repeatedly, awarding the website’s owner revenue from pay-per-click ads.
- Trojan-Notifier: Trojan-Notifier usually accompanies another malware program. Its purpose is to alert the attacker of events related to the malware. For example, when a user installs a backdoor program, the Trojan-Notifier tells the attacker to begin the attack.
- Trojan-Proxy: Trojan-Proxy allows a malicious actor to utilize the infected computer as a proxy to the internet.
- Trojan-PSW: In malware terms, “PSW” stands for “password stealer,” which is exactly what Trojan-PSW is. It steals passwords and login credentials from infected computers.
Pro Tip: Password managers are a great way to protect against Trojan-PSW attacks. They keep your password data in encrypted digital vaults for secure storage. Our favorite password managers are Nordpass and 1Password.
Examples of Trojan Malware Attacks
Trojans spread more slowly than other malware because they don’t self-replicate. However, those that have propagated successfully have caused major financial damages. Here are a few examples:
- Emotet: You know that malware is bad when the Department of Homeland Security calls it “among the most costly and destructive malware.”5 Emotet is a banker Trojan that stole financial information. It spread through spam and phishing emails, and once it had infected a device, it dropped or downloaded additional Trojans and malware to steal data more effectively. Fortunately, thanks to the collaborative effort of multiple countries, Emotet is no longer a threat.6
- Zeus (aka Zbot): Originally, the Zeus Trojan stole financial information from its targets by logging keystrokes to steal passwords. Instead of performing the attacks himself, the maker of Zeus sold its source code to cybercriminals, which is partly why Zeus became widespread. However, since the developer’s retirement in 2010, the source code became available publicly.7 That means that the development of new variants of Zeus continues to this day.
- SeroXen: SeroXen is a stealthy remote access Trojan (RAT) that highlights just how accessible malware has become. It’s sold as a subscription to hackers for as little as $30 per month.8 That’s alarmingly affordable. So far, SeroXen hackers primarily target gamers, but there’s concern corporate hackers will start using it in the future.
- SubSeven: The SubSeven Trojan is a RAT, which gives hackers remote control over Windows computers and networks. When it infiltrates a computer, SubSeven modifies system files and registries, causing the Trojan to execute upon startup. Fortunately, Windows 10’s built-in antivirus can detect SubSeven, and so can other Windows antivirus software.9
Can Trojans Affect Mobile Devices?
Trojans are mostly associated with computers, but that doesn’t mean your smartphone gets a free pass. In fact, there has been a surge of Trojans designed to infect mobile devices. Kaspersky reported over 255,000 trojans targeting mobile banking in 2025 alone.10
Android smartphones and tablets are the most common targets of mobile Trojans. That’s because Android allows the installation of APK files from third-party sources. If you visit a hijacked website, for instance, the website could force your Android phone to install a mobile banking Trojan app. A prompt will ask if you’re sure about the app, but that’s about the only thing standing between your Android phone and the Trojan. That’s why knowing how to remove an Android virus is essential for all Android users. In contrast, with iOS devices, you can only download from the App Store, which is why iPads and iPhones don’t need antivirus.
Mobile Trojan Examples
Here are some examples of Android Trojans:
- Ginp banking Trojan: Ginp coaxes users to enter their mobile banking information to pay €0.75 for COVID-19 data, but it actually steals online banking login credentials that users have entered in the app.11 And this isn’t even the only COVID-related scam cybercriminals use to lure in targets.
- Cerberus: Cerberus is a Trojan for rent. Its makers offer Cerberus’ source codes to hackers on underground forums, the dark web, and even Twitter. Cerberus can do a number of things, such as sending and intercepting text messages, logging keystrokes, harvesting contacts, and installing apps.
- SpyEye/Trojan:Android/Spitmo: SpyEye was the first of many mobile banking Trojans. It steals the mobile transaction authentication numbers (mTANs) that financial institutions send via SMS to validate mobile online money transfers.
- Anatsa Trojan: Surprisingly, this Trojan virus plagues some apps on the Google Play store. The Anatsa usually hides within PDF reader, file manager, or QR code scanner apps.12 Once installed, it quietly requests elevated permissions — often disguised as a routine app update — so it can access sensitive data on your device.
TIP FOR ANDROID USERS: Google actively monitors for apps that contain malware, so it’s safest to install apps directly from the Google Play Store.
History of Trojans
Trojans have a long history of wreaking havoc, but no one knows for certain where they originated. Many consider John Walker’s (not the Marvel character) version of a game called ANIMAL to be the first Trojan, which he released in 1974. Walker hid software called PERVADE inside the game. This hidden software examined all computer directories available to the user, and if ANIMAL didn’t exist in one of the directories, it installed a copy of the game there. ANIMAL and PERVADE fit the definition of a Trojan — software hiding within other software and performing tasks behind a user’s back. However, some believe that because it didn’t have any malicious intent, it wasn’t a Trojan or malware at all. In fact, Walker said in a letter that he made sure PERVADE did not alter or delete other files.
Over a decade after the ANIMAL incident, the PC-Write Trojan appeared. This was one of the earliest Trojans with malicious intent. It pretended to be “version 2.72” of the identically named word processor (the real PC-Write didn’t release a version 2.72). Once executed, it erased all of the infected computer’s files.
Trojans eventually went from being simply destructive to a profit source. In 1989, the AIDS Trojan (aka the PC Cyborg virus) started circulating. It was a ransomware Trojan that deleted or encrypted system files after booting an infected computer a certain number of times. It demanded a $189 ransom for the recovery of the files. If the user didn’t comply, it continued deleting system files until the computer became unusable. Soon after that, other malware authors saw Trojans’ potential in generating profit, and the rest is history.
Detecting and Removing Trojans
The whole point of Trojans is to infect devices with malware and evade detection, so how do we catch it? Well, you can’t tell whether a software program is a Trojan just by looking at it. However, you can detect a Trojan by observing your devices, programs, and apps.
1. Check your programs and apps. Check your computer’s software programs and mobile device’s apps regularly. If you see anything you don’t remember installing, that’s probably a Trojan or a malicious program that a Trojan installed.
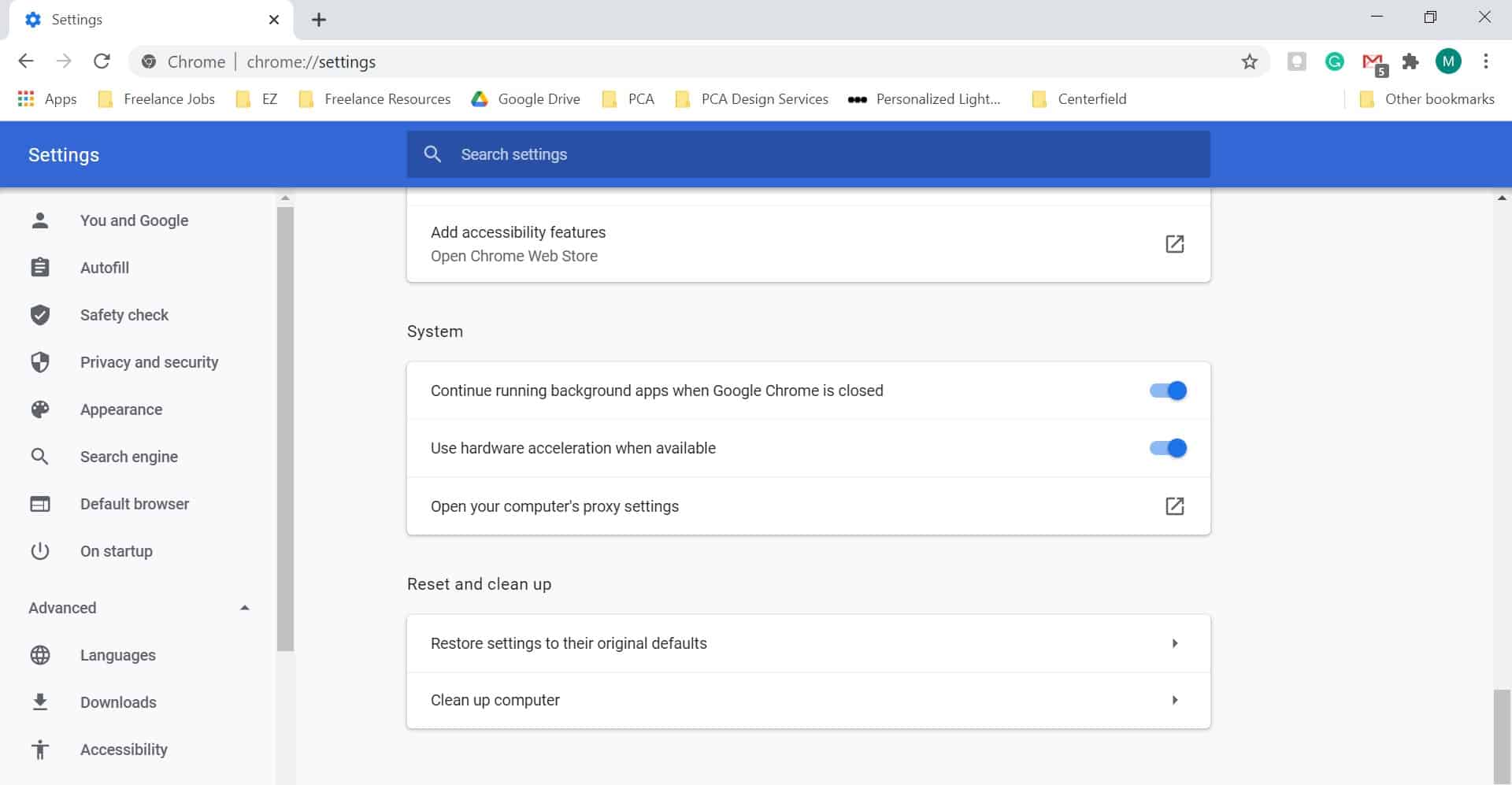
2. Check your startup programs. Trojans can also hide in your computer’s startup process. These Trojans are harder to detect because they’re in the system memory. That’s why you should check your device’s startup programs as well.
3. Check your device’s performance. Malware in general can slow down devices. If you’re experiencing performance issues, it’s best to check your PC’s Task Manager or your Mac’s Activity Monitor to see what’s causing the problem.
On Windows 10 or 11:
- Press Ctrl+Alt+Del.
- Select Task Manager.
- Scroll down to Background Processes.
- Check which processes are eating up your CPU, memory, and disk space.
On Macs:
- Hit Command+Space to open the Spotlight.
- Type in “activity monitor.”
- Check which apps are eating up resources under “% CPU.”
How To Remove a Trojan
If you find a Trojan, whether it’s masquerading as a legitimate program, hiding as a startup program, or operating as a background process, the next step is to remove it. But the process to remove it depends on what it’s masquerading as and the operating system of your device. Here’s a complete breakdown on how to remove any type of Trojan on any of your devices:
Pro Tip: Since Trojans don’t self-replicate, deleting the program that’s hosting the malware works most of the time. However, there are types of Trojans that install additional malicious programs. Simply removing the Trojan may not be enough, so it’s best to use antivirus software to get rid of all traces of a Trojan attack.
Removing Trojans Pretending To Be Programs
If you’re using a Windows PC:
- Open your PC’s settings.
- Click Apps.
- Select Installed Apps (on Windows 10, this appears as “Apps & Features”).
- Click the name of the Trojan program.
- Select Uninstall.
If you’re using a Mac:
- Launch the OS X Finder.
- Hit Command+Shift+A to open the Applications folder.
- Locate the Trojan.
- Drag its icon to the Trash.
- Alternatively, you can select the app, click File, then click Move to Trash.
- Enter your administrator name or password if required.
If you’re using an Android mobile device:
- Go to your Android’s settings.
- Select Apps (on some devices, this may appear as Apps & Notifications).
- Tap App Info.
- Locate the Trojan app and tap it.
- Hit Uninstall.
Removing Trojans Posing as Startup Programs
On Windows:
- Press Windows+R to bring up the Run menu.
- Type “regedit” in the field.
- Select HKEY_CURRENT_USER, then expand the Software folder.
- Locate the Trojan program.
- Right-click its folder and select Delete.
On Mac:
- On your Mac menu bar, click the Apple logo.
- Select System Settings.
- Go to Users & Groups.
- Choose your ID from the list.
- Select Login Items for a list of programs that run on startup.
- Under the Hide column, tick the checkbox next to the Trojan.
Removing Trojans With Malicious Background Processes
On Windows:
- Launch the Task Manager by pressing Ctrl+Alt+Del.
- Right-click the malicious process.
- Select Properties.
- Go to the Details tab and note the product name.
- Close the Properties window and click End Task.
- Uninstall the program (based on the product name) that started the process.
On Mac:
- Hit Command+Space to open the Spotlight.
- Type “activity monitor.”
- Select the malicious package.
- Press the X icon in the toolbar.
- Select Force Quit.
- Uninstall the program that started the process.
Scan Your Devices Using Antivirus Software
The steps we outlined above will help you detect and remove Trojans on your own, but we know they’re painstaking. Who has the time to do all those steps on a regular basis, right? If you want to take an easier path, scanning your devices with antivirus software will save you lots of time and energy. You can purchase antivirus software or download a free antivirus; just make sure it has the right features to combat Trojans. We recommend antivirus software with the following features:
- Real-time scans
- Signature-based scans
- Behavior-based malware detection
- Email security
- Firewall
Protect Yourself: Avoid Trojan Infection
It’s not enough to have even the best antivirus software; after all, no antivirus software is perfect. As digital safety advocates, we encourage safe online behavior to protect computers, mobile phones, and any internet-connected device from threats like Trojans. But how exactly can we stay safe online? Well, first, we must know where Trojans originate so we know what to avoid.
Where Trojans Come From
Trojans can sneak onto your devices from more places than you might expect — an infected flash drive, a sketchy email, a compromised website, you name it. That said, most Trojans tend to show up through these common sources:
- File-sharing sites: File-sharing sites are useful, but they have downsides. One is that hackers can upload cracked copies of legitimate software injected with Trojans and wait for unsuspecting targets to take the bait.
- Email attachments: A single click is all it takes for a Trojan attachment to infect a computer. If you click the infected attachment, it will download and install Trojan malware, which will then do what it’s programmed to do.
- Infected websites: If you visit a hijacked website, malicious codes injected into it will take you to another malicious website or install a Trojan.
- Hacked Wi-Fi: Hacked Wi-Fi, or even a fake Wi-Fi hotspot made to look like a real public hotspot, can give hackers easy access to your device. If you connect to one, the hacker can execute all kinds of attacks on your device, like installing backdoor programs or RATs.
How To Avoid Trojan Infections
Now that we know where Trojans often come from, it’s easier to remain cautious. Follow these tips to become safer from Trojan infections:
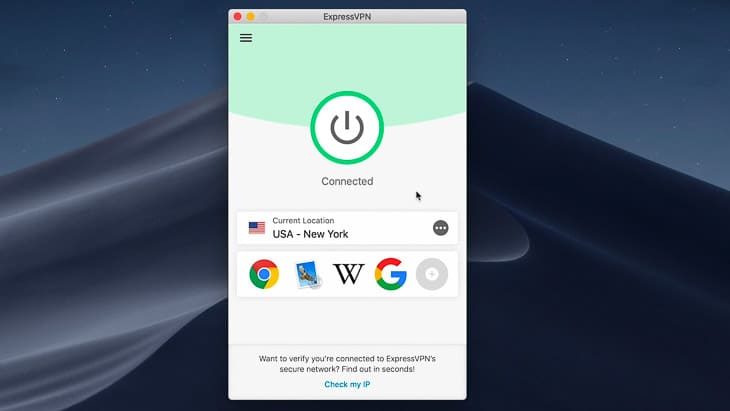
- Use a VPN when downloading from a file-sharing site. A VPN hides your IP address from hackers trying to spy on your device while you download from a file-sharing site. Also, VPNs hide your browsing history. While some VPNs might slow down your downloads, we’ve tested several VPNs for torrenting that had minimal impact on our torrent experience.
- When unsure, do not open an email attachment or IM file. If your antivirus has email protection, scan the attachment before opening it.
- Do not visit unsecured websites. Most browsers will warn you if you attempt to open an unsecured website. If you see one of those warnings, back out immediately.
- Connect to a VPN when on public Wi-Fi. Connecting to a public Wi-Fi network is always risky. To be on the safe side, use a VPN to hide your browsing history from anyone else on the network. What’s more, VPNs change your IP address, making you less susceptible to hacking.
- Do not install apps or programs from unofficial websites or app repositories. Official software download pages and app repositories are there for a reason — so we can download programs and apps free of malware.
- Check an app’s permissions before installing. A Trojan disguised as a legitimate app can exploit its permissions to carry out malicious tasks behind the scenes. For example, a simple flashlight or calculator app that requests permission to send SMS messages or access your contacts should raise immediate red flags.
Recap
Trojans are sneaky and have the potential to inflict various kinds of damage. But if there’s anything we want you to take from this article, it’s that Trojans are not impossible to guard against. If you monitor your devices for irregularities, use digital safety tools like antivirus software and VPNs, and practice safe online behaviors proactively, you can save yourself the trouble of dealing with a Trojan-infected device.
FAQs
Trojans and malware are a lot to deal with, so let's answer frequently asked Trojan-related questions to clear things up.
-
What is a Trojan virus on a computer?
A Trojan virus on a computer, or simply a Trojan, is a malicious software program or code masquerading as legitimate and harmless software. Once it infects a device, it executes its task, which may include deleting or modifying data, stealing data, installing additional malware, and disrupting system performance.
However, “Trojan virus” is a misnomer, because Trojans and computer viruses are two distinct types of malware. Viruses can spread via self-replication, while Trojans do not self-replicate. Viruses often attach themselves to other software, while Trojans are software that contains malicious codes. The correct term is simply “Trojan” or “Trojan malware.”
-
How does a Trojan virus work?
Trojans infect a device by tricking its user into downloading seemingly harmless software that contains malicious codes. Once downloaded, installed, and launched, the malicious code executes.
-
Can Trojan viruses be removed?
Trojan viruses can be removed in various ways. If you know which software contains the malware, you can simply uninstall it. However, the most effective way to remove all traces of a Trojan virus is to install antivirus software capable of detecting and removing Trojans.
-
Are Trojan viruses bad?
Trojan viruses are bad because they trick users into downloading malware that harms devices in various ways. As an example, remote access Trojans (RATs) give hackers remote access to infected computers, which can result in spying, data theft, and identity theft.
-
How can I tell if I have a Trojan virus?
We recommend running a full virus scan on your computer if you think you have a trojan virus. That’s the best way to tell if you have a Trojan virus. You can run the scan with your device’s built-in antivirus or a third-party antivirus software.