There are many types of malware out there, from viruses to adware. One of the most problematic types, though, is spyware. Spyware isn’t designed to disrupt only your computer; it’s designed to disrupt your entire life. But, there are steps you can take to protect yourself, and we’re here to show you how.
Our team of cybersecurity experts took a deep dive into the latest spyware out there targeting everything from Macs to Androids. We figured out how to get rid of them and how to prevent them in the first place. Here’s everything you need to know about current spyware threats.
What Is Spyware?
As you might guess from the name, spyware is malicious computer software that compromises your digital security by allowing others to spy on you in some way. Most often, these spies want to find out more about you so they can send you targeted ads. In addition, some spies are looking to steal your PII (personally identifiable information), either for themselves or to sell it on the black market. What sorts of things can a hacker steal with spyware?1
- Social Security numbers
- Email addresses
- Physical addresses
- Phone numbers
- IP addresses
- Login information
- Digital images
Defining Spyware
In the simplest terms, spyware is any software that monitors your computer covertly and transmits the data it collects to someone else. In fact, companies and organizations sometimes install spyware deliberately. Some employers, for instance, use it to monitor what their employees are up to. Sometimes, it shows up in schools as well so administrators can keep an eye on students. However, hackers use most spyware for more malicious purposes: to steal your data without you knowing it and use that data to make money off of you in some way.
What Does Spyware Do?
Basically, spyware has three jobs: infiltration, monitoring, and transmitting.
- Infiltration: First, it must infiltrate your device, finding a way in without you detecting it, and then hiding in some nook or cranny.
- Monitoring: Once it’s in your computer, the spyware’s job is to monitor you covertly and capture as much data about you as it can. It uses a variety of methods to do this (see below).
- Transmitting: Finally, spyware needs to transmit the data it collects to the spyware author so they can use it themselves or sell it to a third party.
Who Does Spyware Target and Why?
The real answer to the question “who does spyware target?” is “everyone.” Normally, hackers don’t use spyware to target specific groups. Instead, they collect information from anyone they can. Why? Simply put, every piece of information is potentially valuable, and the goal of spyware is to gather as much of it as possible. So, what specific value can your information have?
- Financial value: Some information is directly financial, such as bank account numbers and passwords.
- Identity theft: Other times, hackers use information to piece together your identity so that someone else can pretend to be you (aka identity theft).
- Ads: Many companies use your personal information to target you directly for ads and spam. This is another type of malware, called adware. Learn how to remove adware.
- Ransomware: Occasionally, hackers use what the spyware uncovers to extort you in some way. They might, for instance, lock you out of your device or encrypt all of its files, holding your data ransom. In this case, spyware can be synonymous with ransomware.
What Are the Different Types of Spyware?
Spyware might be easy to stop if there was only one kind. However, hackers use a variety of methods to spy on you. These are some of the common ones:
- Keyloggers (keyboard loggers): One of the oldest forms of spyware, keyloggers can be either software or hardware. Essentially, they allow someone to see what keystrokes you’re making. Of course, this enables them to piece together anything you type, but they are interested especially in gathering passwords, Social Security numbers, or anything else that might allow them to impersonate you.
- Password stealers: Password stealers are a bit like keyloggers, but they are slightly more sophisticated. Instead of recording all your keystrokes, password stealer programs look for any data that could be passwords. They work in a variety of ways. Some are essentially keyloggers that use sophisticated algorithms to spot certain kinds of words you type. Others work as Trojan viruses, waiting to steal passwords.
- Infostealers: Hackers design infostealers to steal information or data directly from your computer files. Infostealers are often Trojan viruses. Once you activate infostealers, they gather information from registries and files, which could include password and banking information or even compromising photos or videos.
- Banking Trojans: Banking Trojans are often infostealers of one type or another. However, hackers program them specifically to lie in wait until you open a banking app. Then, they go to work, stealing usernames and passwords.
- Browser hijackers: Usually, browser hijackers show up as a form of adware. The software manipulates your browser settings so that you get unwanted ads. In addition, it may reset your homepage to a specific advertiser’s page.2
- Adware: Almost all of us are familiar with this form of spyware. Adware posts ads to your device. Sometimes, adware is attached to specific browsers or is set up to activate based on your behaviors. It isn’t unusual for companies to bundle ads in their software packages. Adware, however, hijacks your system and gives you nothing but ads, either temporarily or permanently.
- Dialers: Not really in use much anymore, dialers were once one of the most problematic types of malware. Once on your computer, they would dial phone numbers with the intent of running up enormous charges. One reason they were so insidious is that they ran in the background. That meant you couldn’t detect them until you received your phone bill.
- Modem hijacker: In the early days of the internet, modem hijackers worked much like dialers. They took over your phone modem and used the line to make expensive calls. These days, the term “modem hijacker” has taken on an entirely new meaning. It refers to a particular kind of hacker who looks for flaws and loopholes in your modem software. They use these vulnerabilities to either intercept your messages or use your modem to send their own messages.
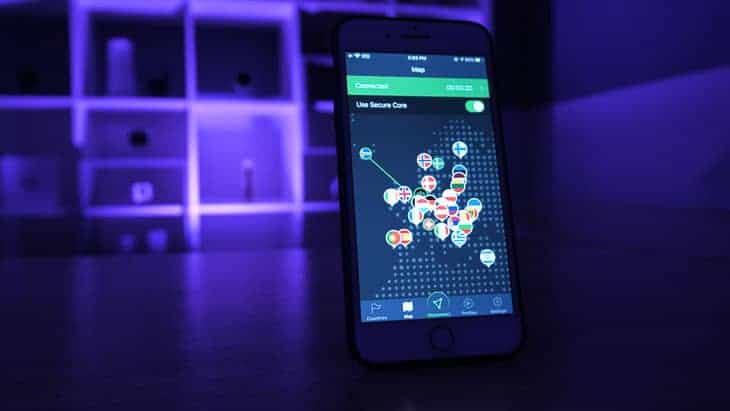
- Commercial spyware: A number of companies market spyware that you can place on your devices intentionally. Sometimes, for example, parents use it to protect their kids online; this type of software is commonly known as parental controls. Some companies also use spyware to monitor employees. Though not illegal, this sort of software does fit the definition of spyware.3 In fact, some employees might want to consider installing VPN software, since it can get past these monitors. In addition, a VPN conceals your browsing history and changes your IP address.

FUN FACT: The Soviets invented the first keyloggers in the 1970s for use on IBM electric typewriters at Moscow embassies.4
How Do You Get Spyware?
There are various ways you can wind up with spyware on your device. These are some of the most common:
- Clicking on a pop-up or prompt without reading what it says
- Downloading software from someone you don’t know
- Opening email attachments from people you don’t know
- Downloading pirated movies, music, or games
- Downloading legitimate files bundled with malicious software
How Do You Know if Your Computer Is Infected?
Probably the easiest way to know if your computer is infected with spyware is to run a scan using an antivirus program that detects spyware specifically. That being said, spyware is trickier to spot than most other forms of malware because it doesn’t always change your computer’s behavior in noticeable ways. It’s useful, then, to know some of the warning signs of spyware:
- You find strange programs on your computer.
- Your laptop loses its charge too quickly.
- Programs misbehave or crash.
- Your computer runs more slowly than it once did.
- You notice websites in your browsing history that you haven’t visited.
- Random lights are blinking on your computer.
- You receive more pop-up ads.
- Your homepage changes.
- Your webcam records suddenly with no explanation.
- Your browser keeps getting redirected.
Is Your Phone Infected With Spyware?
It turns out that your phone is just as susceptible to spyware as your computer. Make sure not to ignore these signs:5
- Your phone makes unusual noises.
- You get text messages that make no sense.
- Your battery loses its charge too quickly.
- Your phone works more slowly than normal.
- Your phone uses more data suddenly.
- Your phone heats up.
- Your phone shuts down or restarts unexpectedly.
Desktops vs. Mobile Devices: Which Are Safer?
Mobile devices used to be safer than PCs and laptops when it came to spyware and other kinds of malware. This had to do with how the two types of devices developed. Specifically, early computers weren’t built to resist malware because most of them didn’t connect to the internet. From the beginning, though, smartphones and other mobile devices were connected to the internet. As a result, they came with features like sandboxing, which keeps an attack on one file or application so it can’t spread to others.
Times have changed, however. These days, computers come preloaded with security features like antivirus software and firewalls. In fact, some operating systems, such as Chrome OS, are configured to fight malware specifically. That being said, these changes haven’t eliminated cyberthreats. Instead, malware has evolved. As a result of these changes, PCs and mobile devices are now roughly equal when it comes to security.
Some Spyware Examples
Over the years, hackers have come up with thousands of pieces of spyware. These are some of the most memorable examples:
- Gator: Gator came bundled with products like password managers. Once installed, the spyware collected information from users, including their browsing history and credit card numbers. The company behind Gator, Claria, then used that data to target users with pop-up ads.
- CoolWebSearch: Once installed on a computer, this present-day spyware changes the user’s homepage to CoolWebSearch.com, collects information about users, slows down their computers, and creates pop-up ads, including some for pornographic sites. CoolWebSearch also hides from many antivirus programs, making the spyware difficult to remove. For example, CoolWebSearch comes bundled with other software that must be detected and uninstalled, or else the original spyware will continue to reinstall itself.
- WhenU-DesktopBar: This adware promises users it’ll look for coupons and other deals on the pages they visit. However, it also monitors internet traffic and collects search profiles.6
What Problems Can Spyware Cause?
Spyware can cause a wide range of problems. Some of these are mere annoyances, while others can wreck your day (or even your life).
Disrupted Operations
At a minimum, spyware can disrupt the way your computer operates. It can:
- Reconfigure your browser, changing your homepage, favorites, and other internet settings
- Redirect your browser traffic, sending you to commercial sites
- Inundate you with tiresome pop-up ads
- Send you false search engine results
- Change internal settings on your device such as your security settings or drive permissions
Damaged Hardware
Spyware can affect your hardware by:
- Draining your device’s memory
- Taking up bandwidth and processing power
- Causing your device to run hot, which could cause permanent damage
Stolen Data
Spyware isn’t just a threat to your computer. The most insidious spyware is designed to:
- Gather enough PII to steal your identity
- Steal your bank passwords and other information in order to take over your accounts
- Spy on you by recording your browsing history or taking over your device’s camera7
How Does Spyware Work?
Spyware itself may be complex, but it actually works pretty simply. Most often, hackers look for ways to trick you based on your everyday habits and behaviors, things you do without thinking. For example, spyware may ask you to take one of these actions:
- Click on a link. The web is full of links, and you can’t really get from one place to another unless you click on some. Often, we get so used to clicking that it becomes automatic. All a hacker needs to do, then, is set up a link that takes you to a fake website. If the fake website looks enough like the real version, the hacker may be able to convince you to download a fake file full of malware as well.
- Download a file. Unlike with clicking on links, we are likely to stop and think before we download a file. Still, if a hacker can convince you that file is something you need, you’ll probably download it. Maybe the file is labeled as a movie you’ve been dying to see or says it’s supposed to stop pop-up ads. You click “OK,” and the next thing you know, your computer is infected with spyware.
- Visit a website. The whole point of using the internet is to visit websites. It’s simple, then, for hackers to set up a fake site that promises juicy tidbits about the royal family, or teaches you how to play the harmonica. Once you’re there, you’re susceptible to malware infection.
How Does Spyware Collect Your Data?
Once spyware infiltrates your computer, its job is to collect data about you. There are three basic ways it can do that:
- Monitor your keystrokes. Keyloggers and password stealers monitor what you type and look for useful information that a hacker can use against you.
- Track your online activity. Other spyware keeps track of where you go and what you do on the internet. Sometimes, the goal is to learn more about you so companies can send you targeted ads. In more serious cases, a hacker may try to use your browsing behaviors to blackmail you.
- Take control of your device. Finally, spyware may try to take over your device in some way. It might, for instance, search through your files for useful information. It could also change your security settings. In extreme cases, spyware might even take over your device’s camera.
The History of Spyware
The public first began using the term “spyware” in relation to computers sometime in the 1990s. However, spyware was only a conceptual term back then. It referred to tactics that one government might use to spy on another government. The first commercial application of spyware was in the 1999 freeware game Elf Bowling, which turned out to include tracking software. As a result, by the early 2000s, cybersecurity companies were already using “spyware” in essentially the same way we use it today. In fact, Lavasoft released the first antivirus software package specifically for spyware in 2000.8 Since then, the industry has come to recognize spyware as one of the most problematic, insidious forms of malware.
The Spyware / User Privacy Debate
Some companies take offense to their products being labeled “spyware.” They prefer the term “adware” and argue that it improves our lives. Their attitude has opened up a larger debate about the value of such software and its positives and negatives.
The Positive Side of Adware
One side of the debate is that adware and tracking software make our lives more convenient. By monitoring your behaviors, companies argue, software can send you ads tailored to your specific interests. In fact, spyware advocates note that smart homes can’t operate effectively if they don’t spy on us, since that’s how they learn to respond to our needs. The CEO of Nomiku, a kitchen tech company, said, “We get insights from the fridge. It has a freakin’ camera in it. Wow, this guy really loves onions. He’s Shrek! Let’s give him more things with onions.”9
The Negative Side of Adware
On the other side of this debate, privacy advocates argue that giving companies so much of our personal information is dangerous. For instance, we cannot predict when a hacker might find a way to access all that information.10 As we report in our guide to data breaches, for example, a Yahoo breach exposed over 3 billion user records in 2013, and in 2019, a Facebook breach exposed 540 million records. Ultimately, we can never know when the next breach will happen, or who it will happen to.
Preventing Spyware
Because spyware targets your everyday behaviors, you can prevent most attacks easily by modifying your behaviors in pretty small ways:
- Only download files from sites and people you trust.
- Take the time to read all disclosures before installing software.
- Avoid interacting with pop-ups.
- Regularly update your software, including browsers, apps, and especially antivirus.
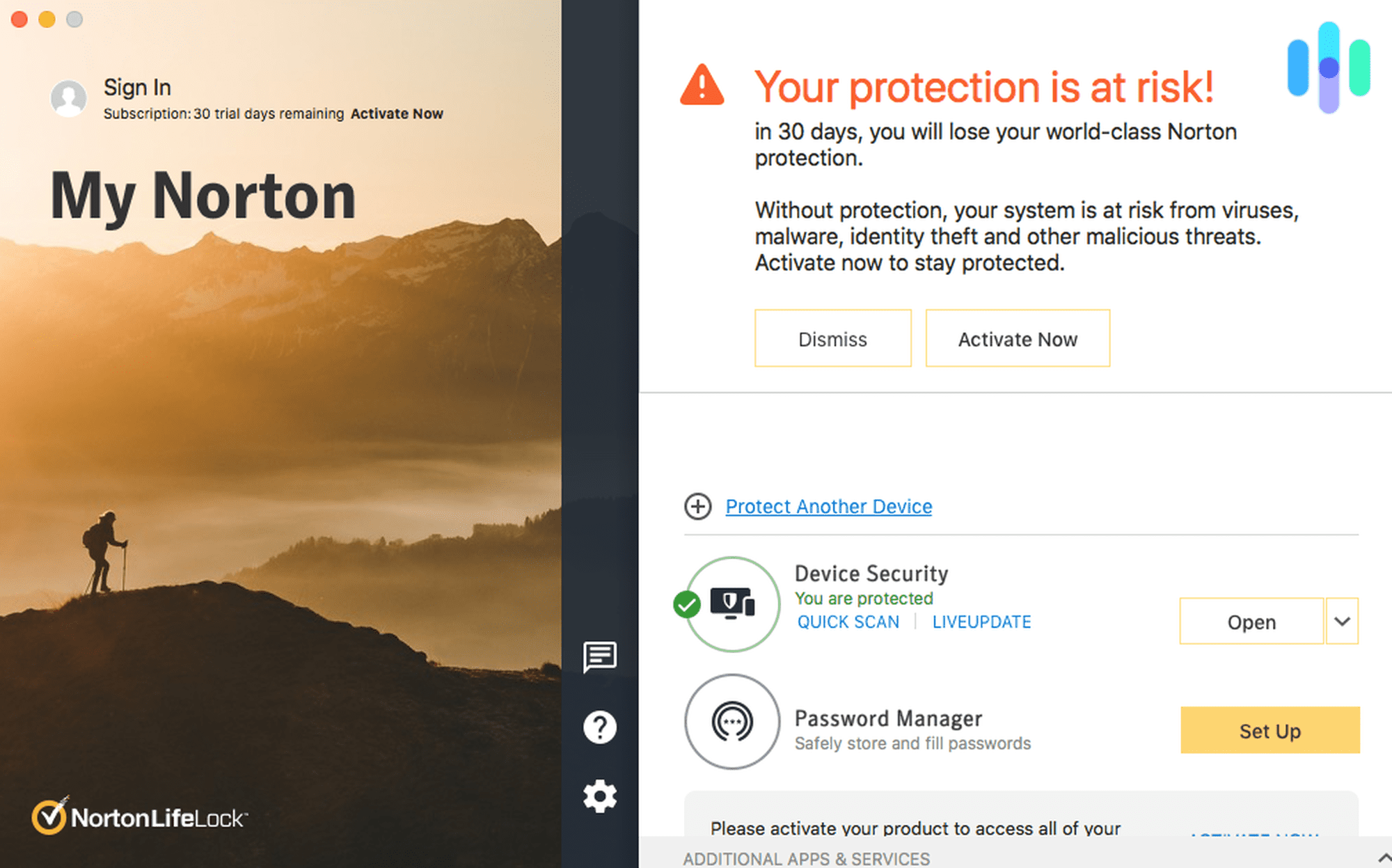
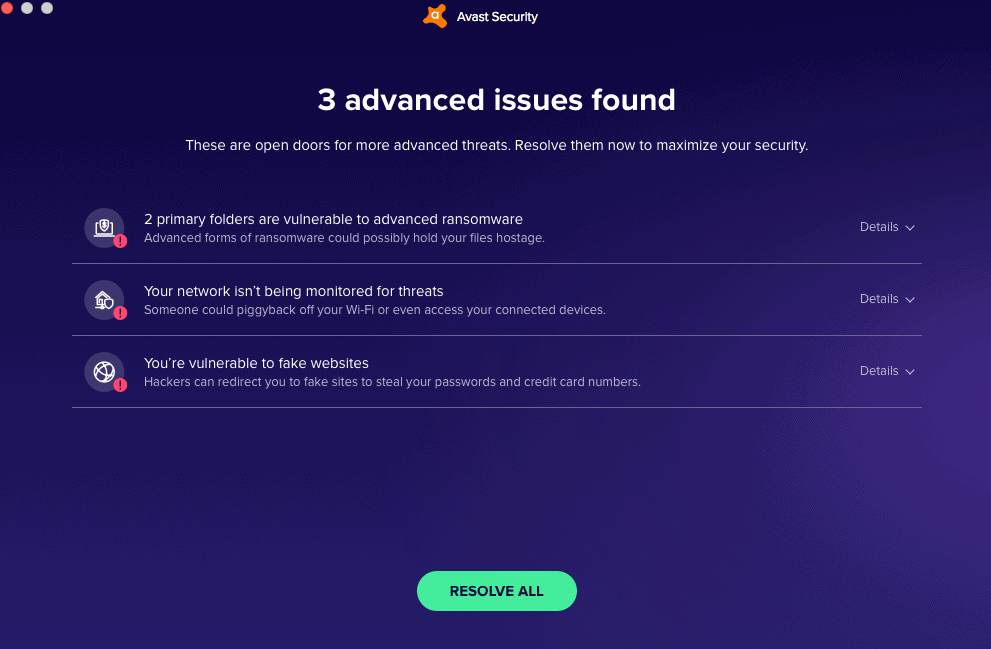
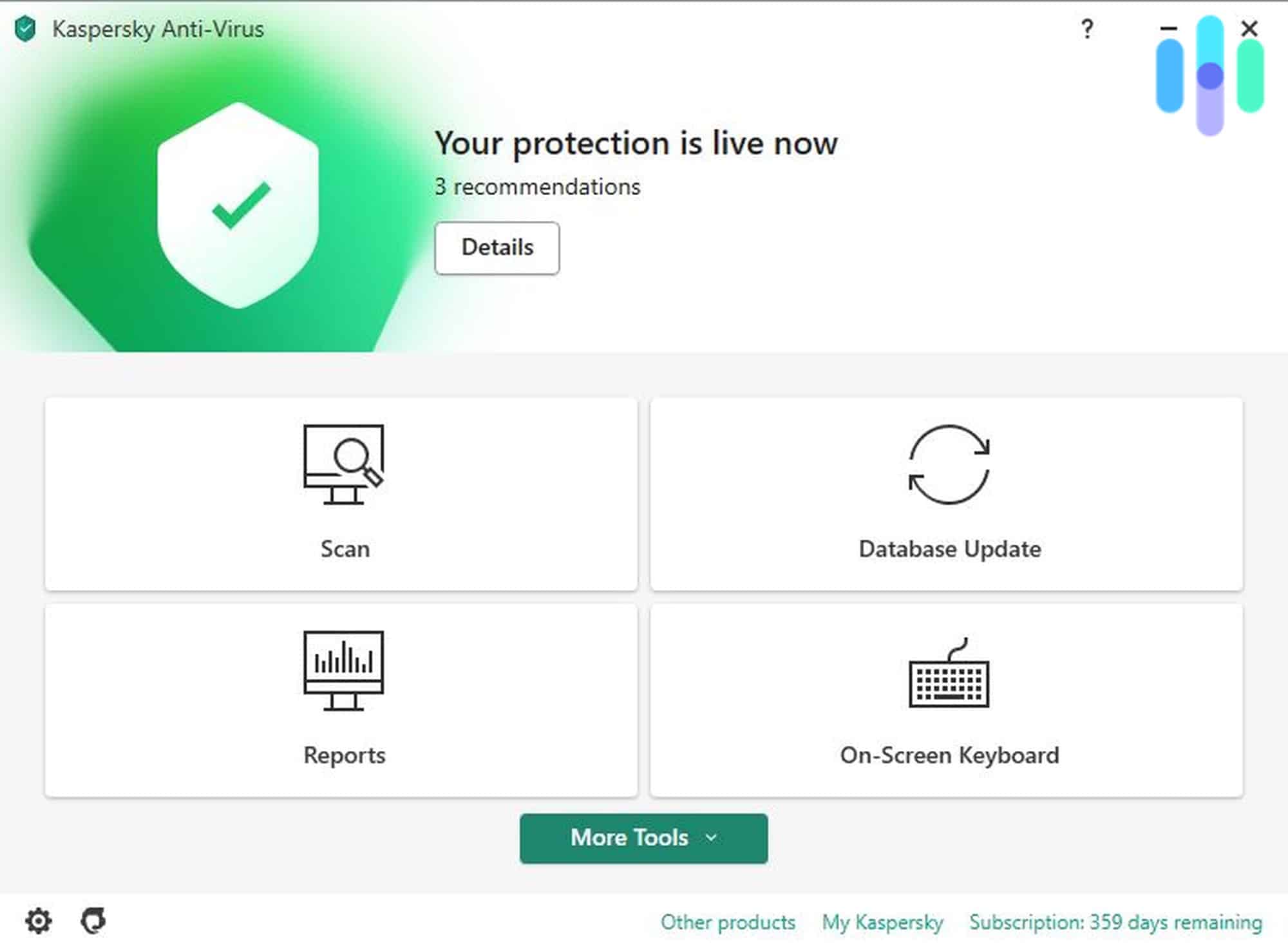
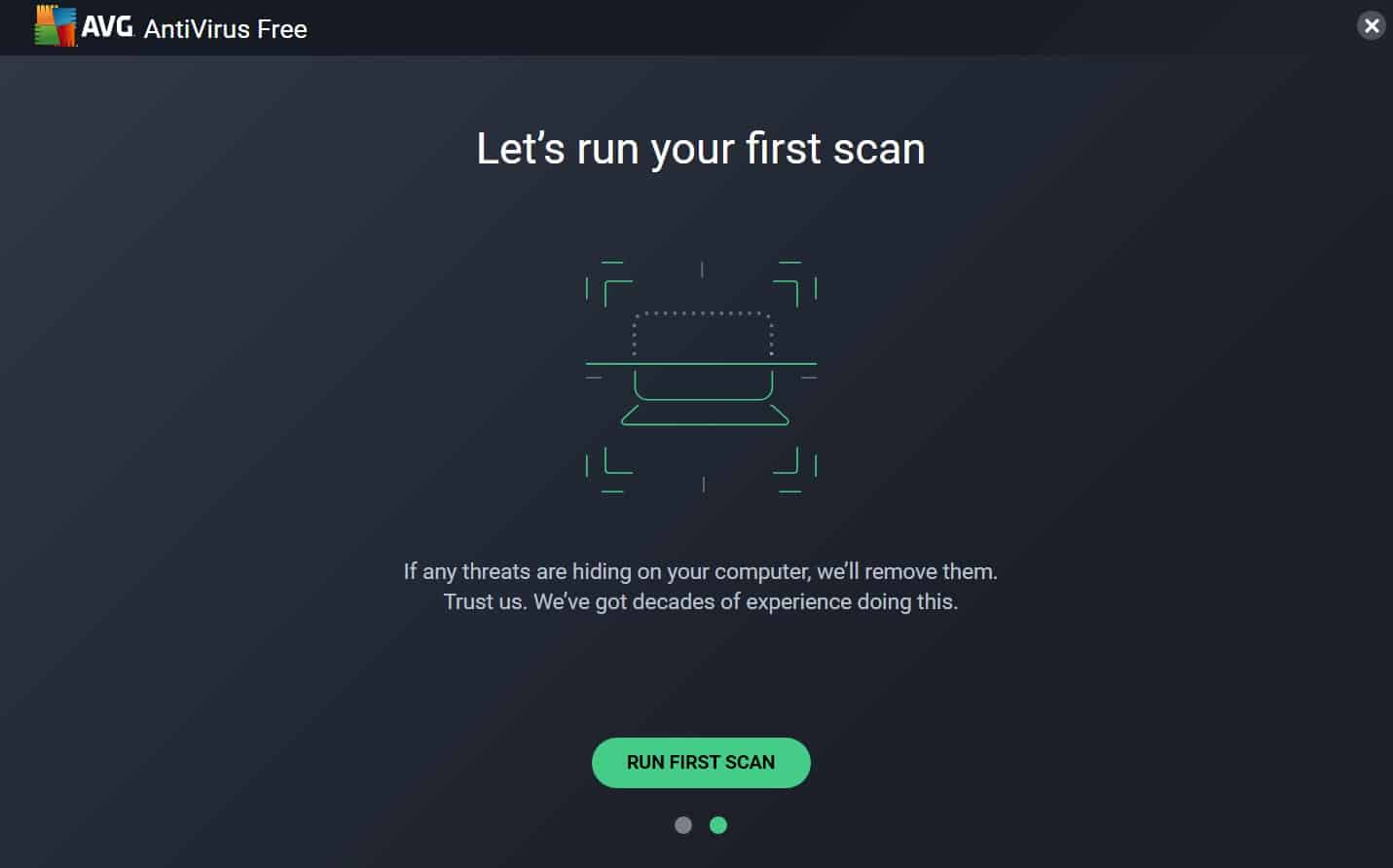
- Use top antivirus software that includes spyware detection specifically.
Removing Spyware
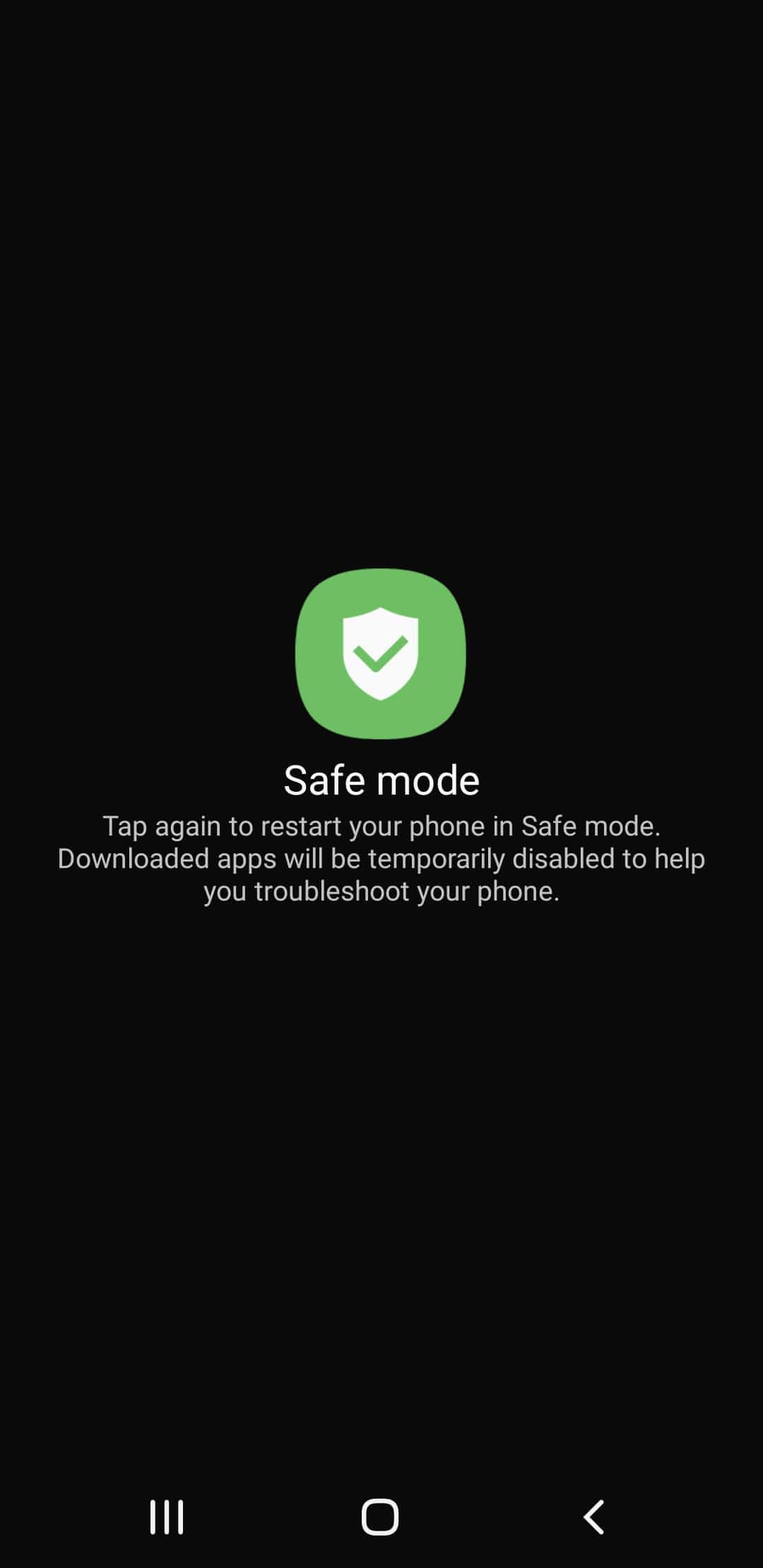
Even if you practice all the best behaviors for preventing spyware, your device may wind up getting infected anyway. What do you do? The simplest answer is to download and install an antivirus program or app that addresses spyware specifically.
- Choose the best antivirus program for your device, whether you need a Windows antivirus, Mac antivirus, Android antivirus, or Linux antivirus.
- Visit the company’s webpage and sign up for a subscription.
- Download the app on your particular device.
- Install the app.
- Use the app’s scanner to identify the spyware.
- Have the app either delete or quarantine the spyware.
There are also manual methods for deleting spyware from your device, assuming you know the name of the spyware itself.
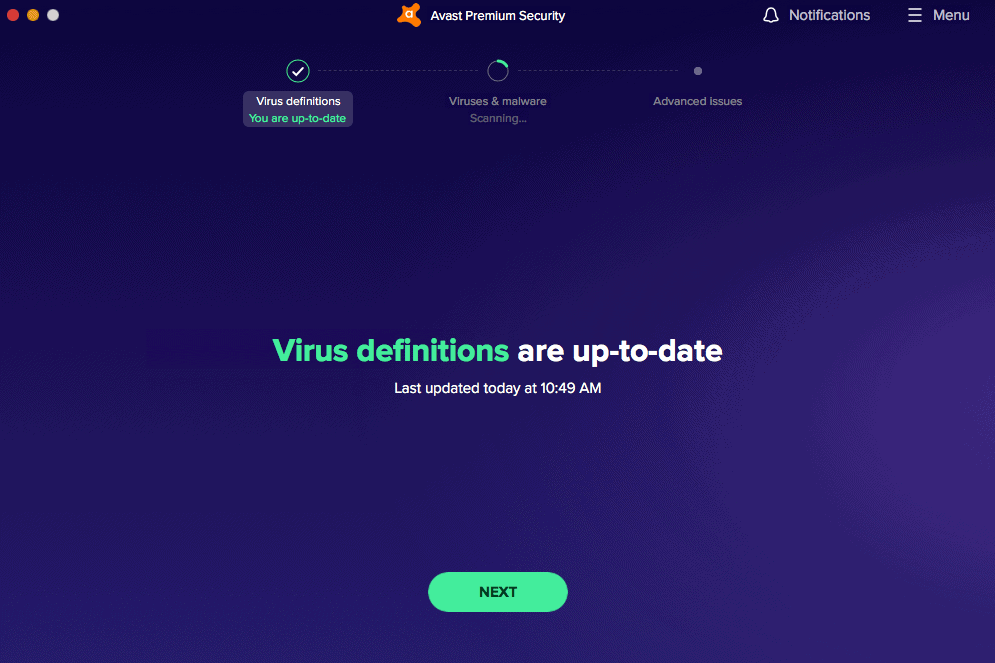
Windows Devices
Even though there’s tons of news stories about how Windows Copilot is spyware, it’s actually not. You need to consent to giving your keylogging data over to Microsoft. But, that doesn’t mean Windows devices don’t get spyware. They’re actually one of the main targets. To manually remove spyware from a Windows device:
- Reboot your device in safe mode.
- Navigate to the Task Manager.
- Choose the Processes tab.
- Find the offending spyware in the list of processes.
- Once you’ve identified the malware program, click End Task.
- Click File.
- Click Run New Task.
- Type the MSConfig in the box.
- Click OK.
- Go to the Service tab.
- Uncheck the suspicious service.
- Click Apply.
- Click OK.
- Restart the device normally.11
Macs
Although Macs were once thought of as impervious to viruses, now it seems like there’s a new malware for Macs every day. At the beginning of this year, a spyware called LightSpy expanded from only targeting Android and iOS devices to also targeting macOS.12 It can steal massive amounts of data including payment details.
To manually remove spyware from Macs:
- Reboot your device in safe mode.
- Navigate to the Launchpad.
- Open the Activity Monitor.
- Check for any unusual programs.
- Once you’ve identified the spyware program, click the X in the top left area of the window.
- Open your Finder.
- Toggle to Applications.
- Look for suspicious apps.
- Once you’ve identified a suspicious app, drag it to the trash.
- Empty the trash.
- Restart the device normally.13
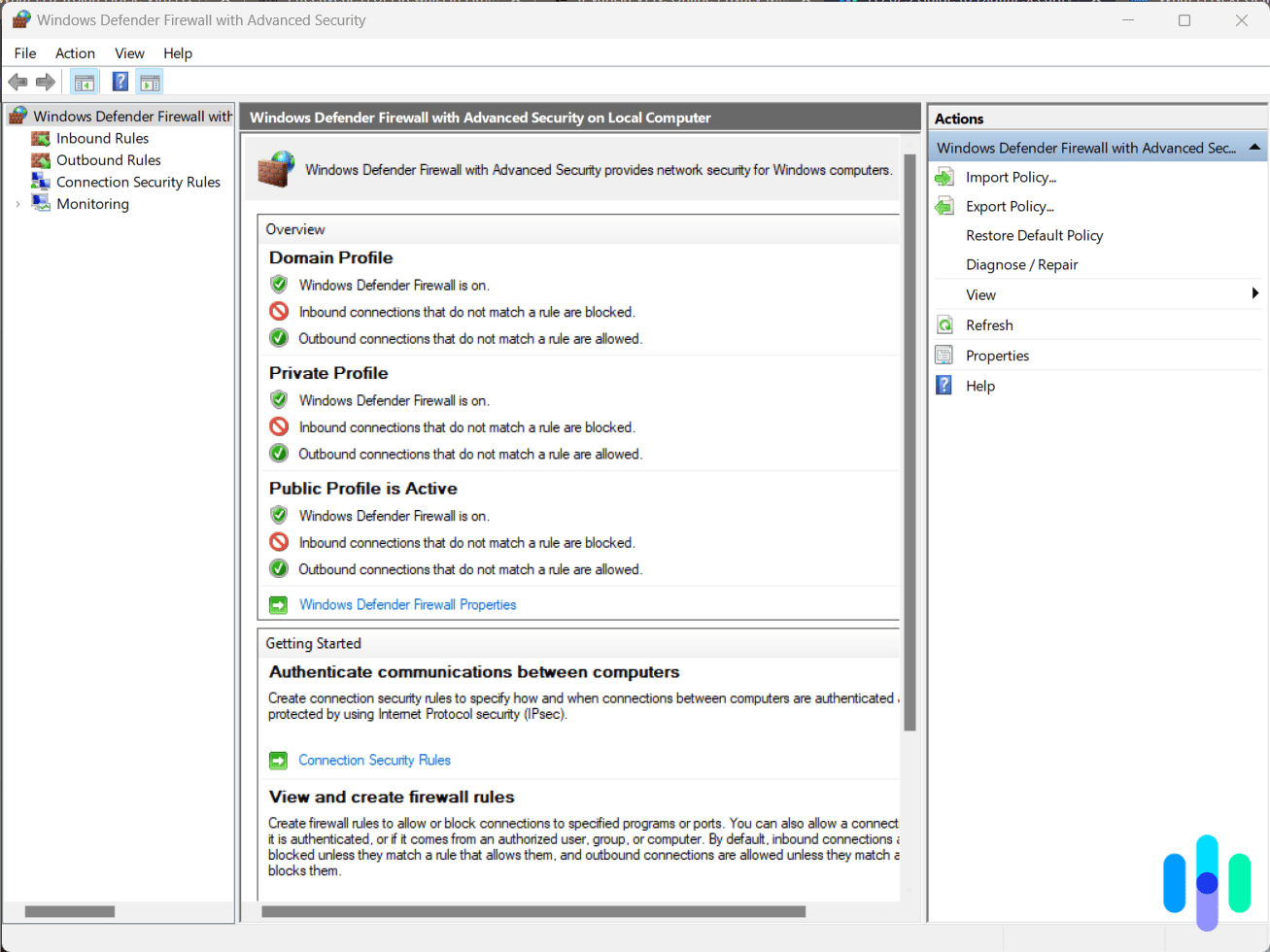
Androids
When it comes to Androids, spyware seems to plague third-party apps. And the Google Play store even hosts some. Just recently, spyware was found in six apps that were available on the Google Play store for over two years.14 Here’s how to manually remove spyware like this from Android devices:
- Reboot your device in safe mode.
- Navigate to Settings.
- Choose Apps.
- Select the infected app.
- Choose the Uninstall option.
- Restart the device normally.15
Choosing the Right Tools to Fight Spyware
There are dozens of antivirus packages on the market, so how do you choose between them? Here’s a list of what to look for when making your decision.
- Spyware detection: If you’re interested in removing spyware specifically, make sure the antivirus you choose has robust tools to do that.
- Scans: Consider the types of scans the antivirus runs. You’ll want to run scans on demand whenever you’re concerned you might have an infection. You may also find it useful to schedule scans so you won’t have to remember to run them regularly. Look for software that lets you do both.
- Detection methods: Antivirus software uses different methods to spot spyware. It may compare files to its own library of known spyware. In addition, it may look for similarities between a file and known spyware. The best programs, though, use behavior-based detection, which watches files for suspicious actions and detects spyware even if it’s not in the virus database.
- Privacy policy: Reputable antivirus software always has a published privacy policy. Take the time to read through this page. Look for companies that keep as little of your PII as possible and don’t sell this information to third parties.
- Price: Prices of antivirus packages can vary widely and are based on factors like detection methods, privacy policies, and extra features (detailed below). Most companies insist that you sign up for at least a one-year subscription. At the top end, that can cost as much as $180 annually. Most personal antivirus subscriptions, however, average $36 to $48 for the year. You may be able to find discounts for signing up for multiple years.
- Safety extras: Along with the price, you should consider carefully what you’re paying for. What kind of extra features does it have, for example? These are some you might want:
- VPN
- Identity theft protection
- Password manager
- Parental controls
Some Additional Privacy Tips
Preventing and eliminating spyware is crucial to maintain your privacy. However, there are other dangers to your privacy besides spyware. How can you protect yourself? Here are some useful suggestions:
- Install a browser plug-in like Privacy Badger that monitors how many companies are tracking you.
- Delete your browser cookies every day.
- Install plug-ins like Ghostery that block trackers.
- Use one of the best VPNs to keep your internet connection secure.
Recap
Spyware is a particularly malicious form of malware because it doesn’t just damage your device; it steals your personal data to spy on you, putting your identity at risk. Protect yourself. Know the types of spyware, like keyloggers and banking Trojans. Most importantly, deal with them by choosing the right antivirus software.
FAQs
Here are answers to some of the most frequently asked questions about spyware.
-
What is spyware on a computer?
Spyware is any software that collects information about you. In some cases, people use spyware legally. For example, parents monitor what their children see on the internet, and businesses track what their employees are doing. More often, though, hackers use spyware illegally in order to sell you products, steal your identity, or blackmail you.
-
What are examples of spyware?
These are some of the most common examples of spyware:
- Gator
- CoolWebSearch
- 180 Search Assistant
- HuntBar
- Cydoor
-
What is spyware, in simple words?
In simple words, spyware is software that spies on your computer. It collects personal information about you, including your usernames, passwords, and web browsing habits.
-
What is spyware on a phone?
Spyware on a phone is any software designed to collect information about you. This includes personally identifiable information, text messages, photos and videos, and your physical movements. In some instances, spyware can be used legally. Some parents, for example, monitor their children’s phones using spyware. More often, though, spyware is used to sell you a product, steal your identity, or blackmail you.
-
How can I tell if I have spyware?
The best way to tell if you have spyware is to run a virus scan. Signs you might have spyware include your device slowing down and suspicious network activity.