The Best Antivirus for Macs 2026
We tested the best antiviruses for Mac this year and found that Norton offers excellent device and online protection overall.
- AI-powered scam protection feature detects online scams
- Beginner-friendly interface
- Includes a password manager
- Detects ransomware, spyware, trojans, and viruses
- 24/7 customer support
- Easy-to-use MacOS app
- Mac version includes VPN, password manager, and performance booster
- App Store app rated 4.6/5.0
- Fast scans on Mac devices
In the past, hackers targeted Windows machines more often than Macs simply because there were more of them. Today, our Macs are fair game for the worst viruses and you need more than a built-in firewall to stay safe.
We tested the top antivirus software for Macs for hundreds of hours, bombarding them with malware. Every name on our short list performed well, but Norton particularly excelled for its all-around (device and online) protections. Meanwhile, Aura outperformed the others through its excellent customer support, and TotalAV gave us impressive value with a low starting price. Keep reading for the rest of our top picks.
Mac Tip: Before we slap on any kind of extra protection for our Macs, we always install the latest security updates. Whether you do this manually or automatically, we recommend you start here.
Best Antiviruses for Mac at a Glance
| System |
Norton Antivirus

|
Aura Antivirus

|
TotalAV Antivirus
|
Surfshark Antivirus
|
Bitdefender
|
Trend Micro Antivirus

|
Avast Antivirus

|
|---|---|---|---|---|---|---|---|
| Ranking | 1st | 2nd | 3rd | 4th | 5th | 6th | 7th |
| Ratings | 9.7/10 | 9.5/10 | 9.3/10 | 8.9/10 | 8.7/10 | 8.6/10 | 8.5/10 |
| Behavior-based Detection | Yes | No | No | Yes | Yes | Yes | Yes |
| Real-time Protection | Yes | No | Yes | Yes | Yes | Yes | Yes |
| Firewall | Yes | No | No | No | No | No | Yes |
| Max Devices | 5 | 10 | 8 | 5 | 5* | 10 | 10 |
| Phishing and Ransomware Protection | Yes | Yes | Yes | Yes | Yes | Yes | Yes |
| Also Compatible with | iOS, Android, Windows | Android, Windows | iOS, Android, Windows | iOS, Android, Windows | iOS, Android, Windows | iOS, Android, Windows | iOS, Android, Windows |
| Free Version | No | No | Yes | No | Yes | No | Yes |
| Money-back Guarantee | Yes | Yes | Yes | Yes | Yes | Yes | Yes |
| Yearly Pricing Starting at | $29 | $36 | $29 | $32.28 | $59.99 | $19.95 | $34.99 |
| Read Review | Norton Antivirus Review | Aura Antivirus Review | TotalAV Antivirus Review | Surfshark Antivirus Review | Bitdefender Review | Trend Micro Antivirus Review | Avast Antivirus Review |
Our Picks for the Best Antiviruses for Macs
- Norton Antivirus - Best Device and Online Protection
- Aura Antivirus - Best Customer Support
- TotalAV Antivirus - Best System Protection
- Surfshark Antivirus - Best Antivirus/VPN Bundle
- Bitdefender - Best Malware Protection
- Trend Micro Antivirus - Best for Social Media Privacy
- Avast Antivirus - Best Free Version
The Rundown
-
1. Norton Antivirus - Best Device and Online Protection
 View Plans Links To Norton
View Plans Links To NortonProduct Specs
Virus Detection Yes Malware Detection Yes Firewall Yes Full, quick, and scheduled scans Yes Real-time protection Yes Behavior-based monitoring Yes 
Who’s Norton Good For
We gave Norton two thumbs up for its ability to protect devices from malware and also guard against online scams through its AI-powered scam protection feature. The latter is an AI-powered scam detector that worked exceptionally great against phishing. During testing, it immediately recognized phishing emails we opened through Apple Mail.
What We Like
- AI-powered scam protection
- Lightweight macOS application with minimal system impact
- Great virus detection rate
- Affordable prices, especially for single-device users
What We Don’t Like
- Mobile devices such as iPhones count against the device limit
- Prices increase after the first year
- Base plan ($19.99 in the first year) protects only one device
- Clunky user experience if you use multiple Norton products and services
Our Norton Malware Test Results
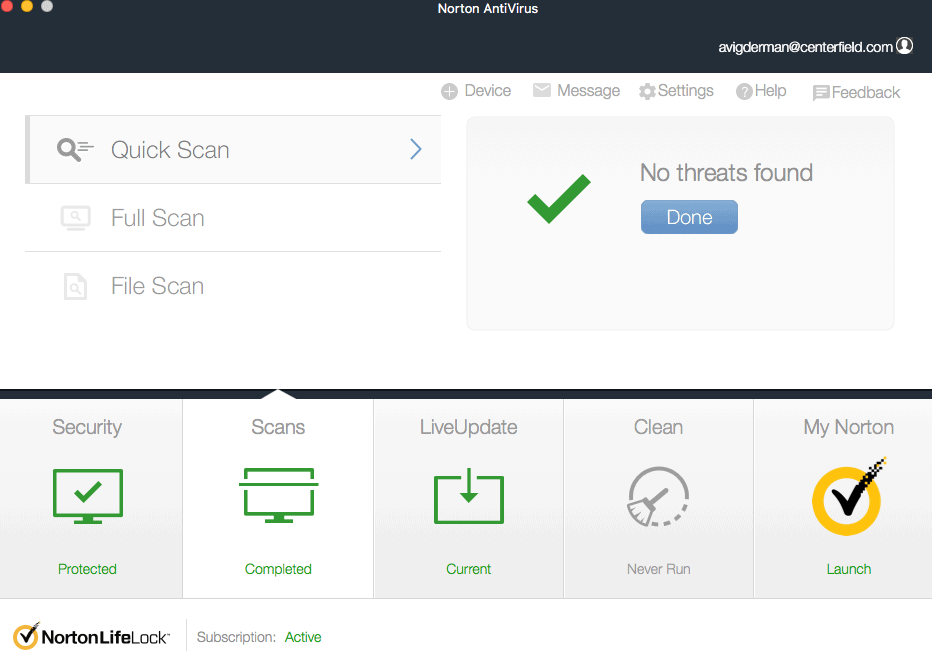
We ran a battery of malware tests on our Macs, and Norton’s antivirus software performed admirably. Right out the gate, we turned on real-time protection so we wouldn’t need to scan our devices regularly. Once on, it detected all five malware test files we tried to download. While not harmful, malware test files work great for testing antivirus software’s effectiveness.
Of course, we also ran scans on our computer. The first full scan took about 30 minutes, which is faster than most of the competition. We like that it didn’t take too long, but not too fast either. During the scan, the app showed us which files it was scanning, which built our confidence that Norton is really looking at every nook and cranny of our macOS device.
FYI: The initial full scan lasts longer than typical full scans. We suggest running it when your device is not in use.
Our Experience with Norton Security Features
Besides keeping malware off our devices, Norton included useful security tools. Our favorites were the AI-powered scam protection feature and the password manager.
Norton’s scam protection uses AI to detect potential online scams. We received a lot of phishing emails lately in our burner email (the one we use to sign up for deals and discounts). We tried opening a few of them, and Norton interrupted us 10 out of 10 times. We can tell AI was really at work. Norton flagged down even the most convincing phishing emails we received.
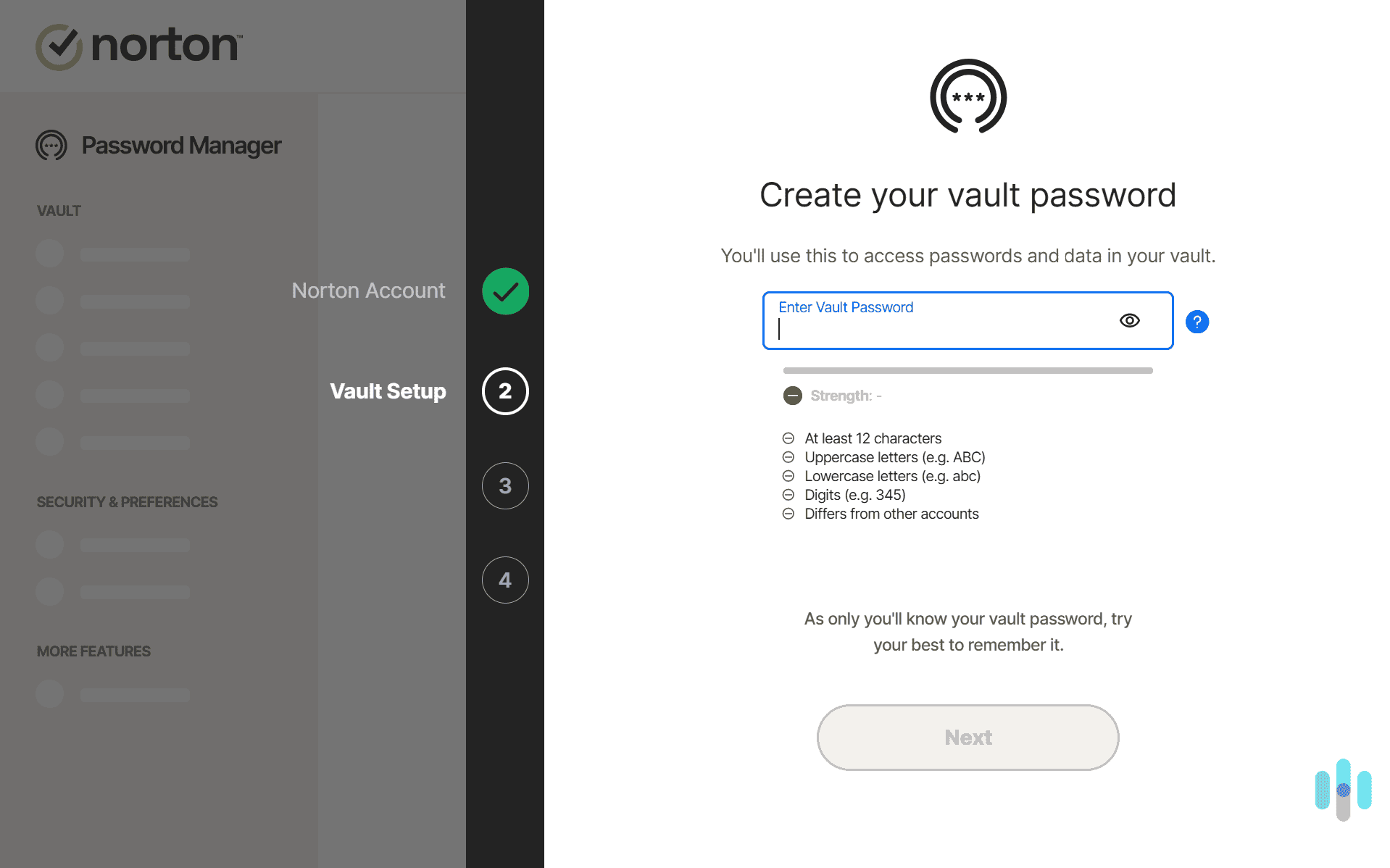
Norton made us come up with a secure password to our vault with stringent requirements we weren’t used to. The password manager, on the other hand, kept our passwords safely stored in an encrypted vault. We believe there are better password managers for Mac, but having one included in every Norton plan increases the value of the antivirus subscription.
Pricing
Speaking of antivirus subscriptions, we think Norton’s pricing is on point, especially in the first year. The Antivirus Plus plan (cheapest) costs $19.99 for the whole first year. It even dropped to as low as $14.99 during a sale. Either way, the cost is less than $2 per month. Watch out for the device limit though. The cheapest plan protects only one device, and mobile devices count against the device limit. Plus, renewal prices are slightly higher. The Antivirus Plus plan renews at $24.99 after the first year.
Pro Tip: “Low introductory price” deals are common in the industry. It’s always a good idea to research renewal prices before signing up. If you’re not sure if you’ll continue using the service after the first year, we also recommend turning off auto-renewal in your account dashboard.
-
2. Aura Antivirus - Best Customer Support
 Select a Plan Links To Aura.com
Select a Plan Links To Aura.comProduct Specs
Virus Detection Yes Malware Detection Yes Firewall No Full, quick, and scheduled scans No scheduled scans Real-time protection Yes Behavior-based monitoring No 
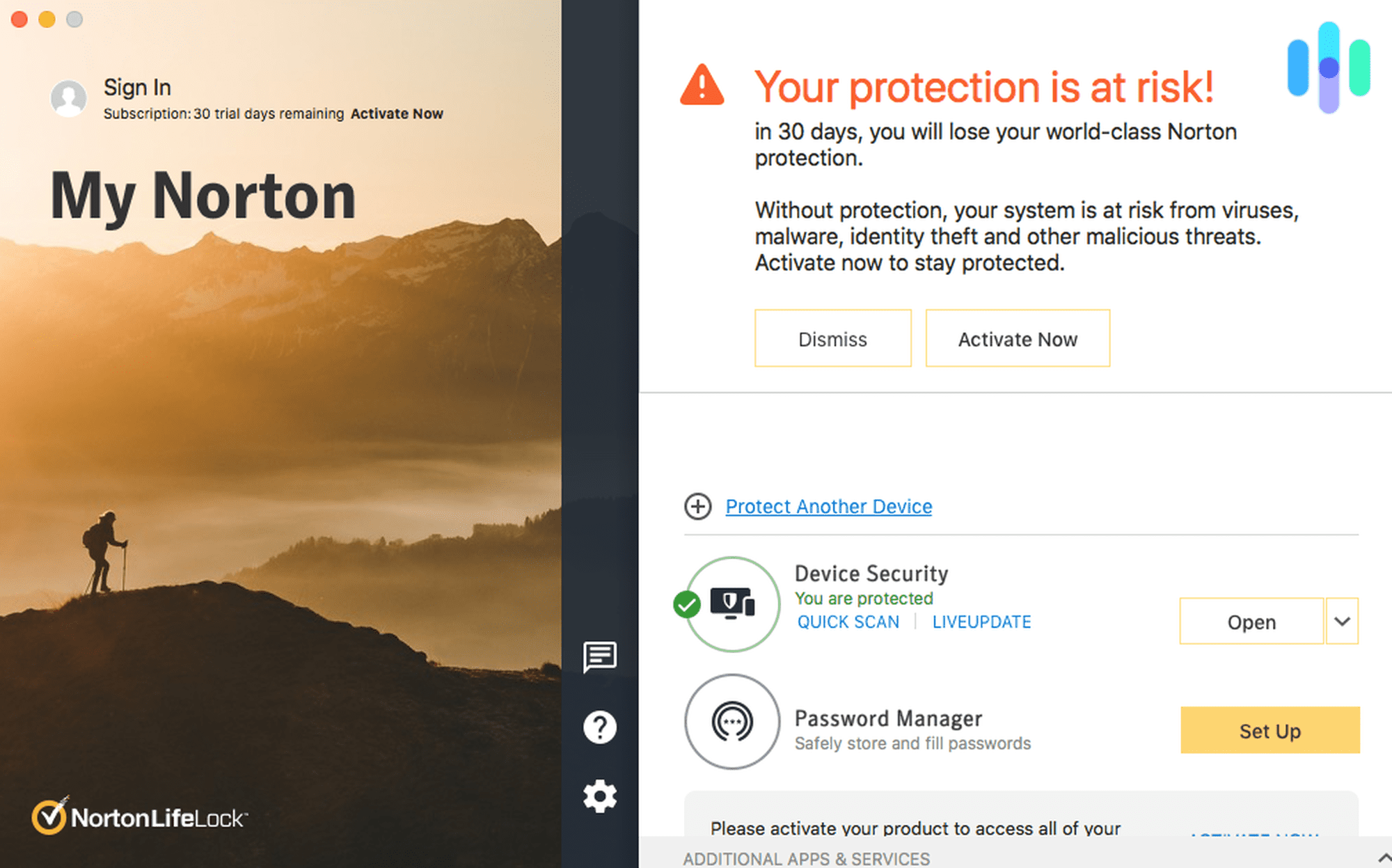
Who’s Aura Good For
If you find yourself at the Apple Genius Bar more often than you’d like to admit, you’ll appreciate Aura’s customer support. It’s based in the U.S. and available 24/7 so anytime you need help, Aura’s professionals will be there for you. And unlike the Apple Genius Bar, you’ll never leave the interaction with a repair fee.
What We Like
- High-quality customer support agents
- Affordable plans starting at $3 per month
- 60-day money-back guarantee
- Bundles with identity and credit monitoring
What We Don’t Like
- Real-time detection is not available on MacOS
- Only available in an annual plan
- Limited third-party testing
Our Aura Malware Test Results
Since Aura Antivirus has not been tested by traditional third-party antivirus testing agencies like AV-Test, we ran our own comprehensive tests.We hid the EICAR malware test files on our MacBook Pro, then ran quick and complete scans to see if it found them all. For both scan types, Aura found the file, even when we hid it in an encrypted zip file.
Our Experience with Aura’s Extra Security Features
While we’re not huge fans of Aura’s VPN, we really like the identity theft protection that comes bundled with their Ultimate plan. In fact, Aura offers one of our favorite identity theft protection services.
However, the $5 per month price tag comes with limited capabilities compared to Aura’s identity theft protection plans that start at $12 per month. The main difference is that the antivirus bundle only includes one-bureau monitoring instead of three-bureau monitoring. We still think it’s great value, though, as it costs less than half the standard rate.
>> Read More: Aura Identity Theft Protection Review 2026
FYI: You can always keep an eye on your credit on your own for free. Annual Credit Report allows you to pull credit reports from all three major credit bureaus for free on a weekly basis.1
Pricing
With annual plans that include a VPN starting at $3 per month, the value of Aura’s bundles is hard to beat. Sure, TotalAV offers a slightly lower starting price, but it does not include their VPN service. Surfshark’s antivirus and VPN bundle starts at $2.49 per month, but that requires a two-year commitment.
Beyond the Basic plan, we also find Aura’s Ultimate plan to provide great value. We rarely see subscriptions that offer $1 million identity theft insurance for under $10 and Aura’s Antivirus Ultimate bundle offers it for half that.
-
3. TotalAV Antivirus - Best System Protection
Get TotalAV Links To TotalAVProduct Specs
Virus Detection Yes Malware Detection Yes Firewall No Full, quick, and scheduled scans Yes Real-time protection Yes Behavior-based monitoring No Who’s TotalAV Good For
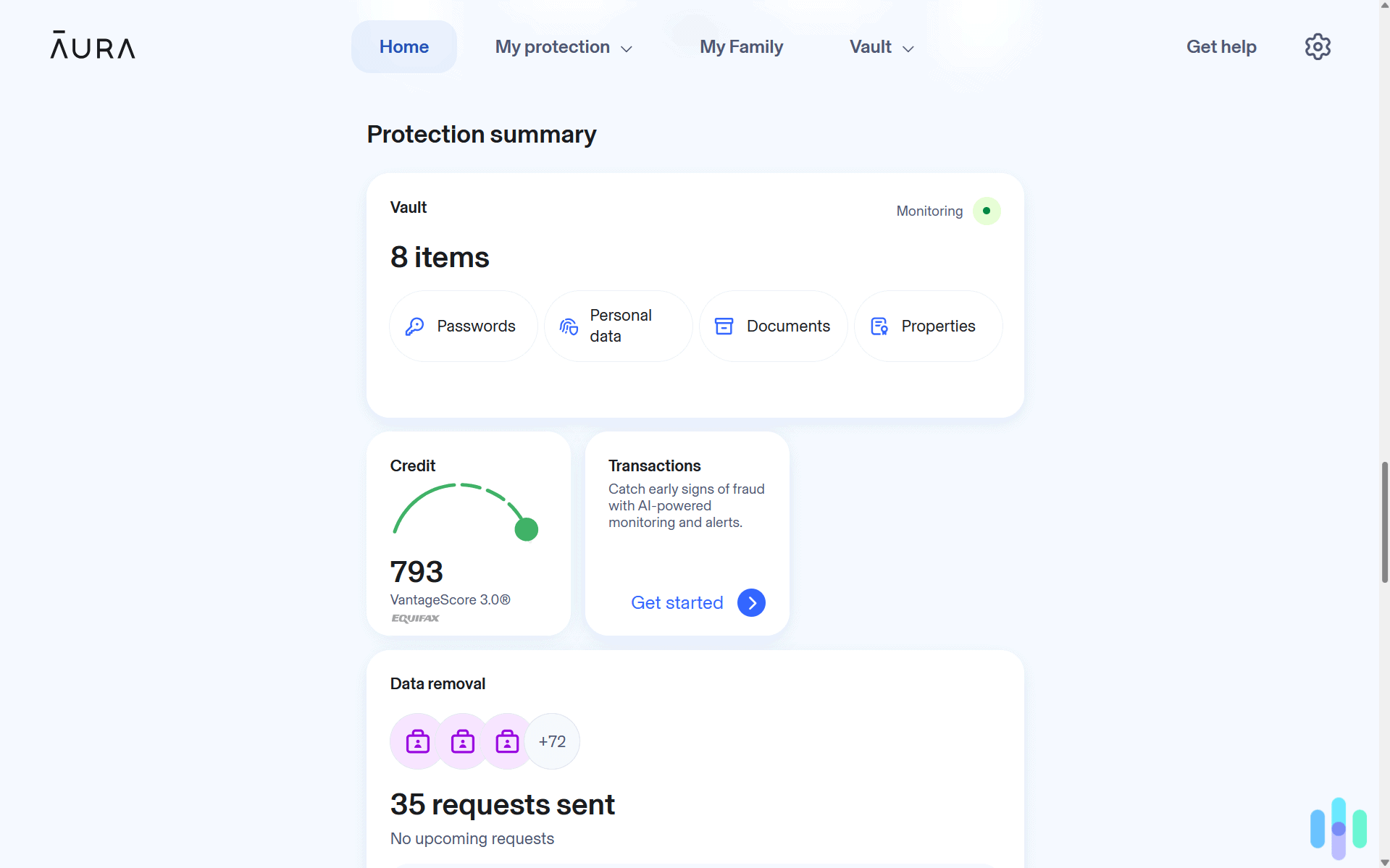
TotalAV is a reasonably priced, feature-packed antivirus for Mac users who want a little extra help keeping their devices clean and safe from viruses. TotalAV performed well in our malware tests and offers a decent, stripped-down VPN with its premium plans.
Pros
- Solid malware protection for Macs
- Quick and full system scans
- System tune-up feature
- Extra phishing protection
Cons
- No firewall
- No behavior-based detection
- In-app ads
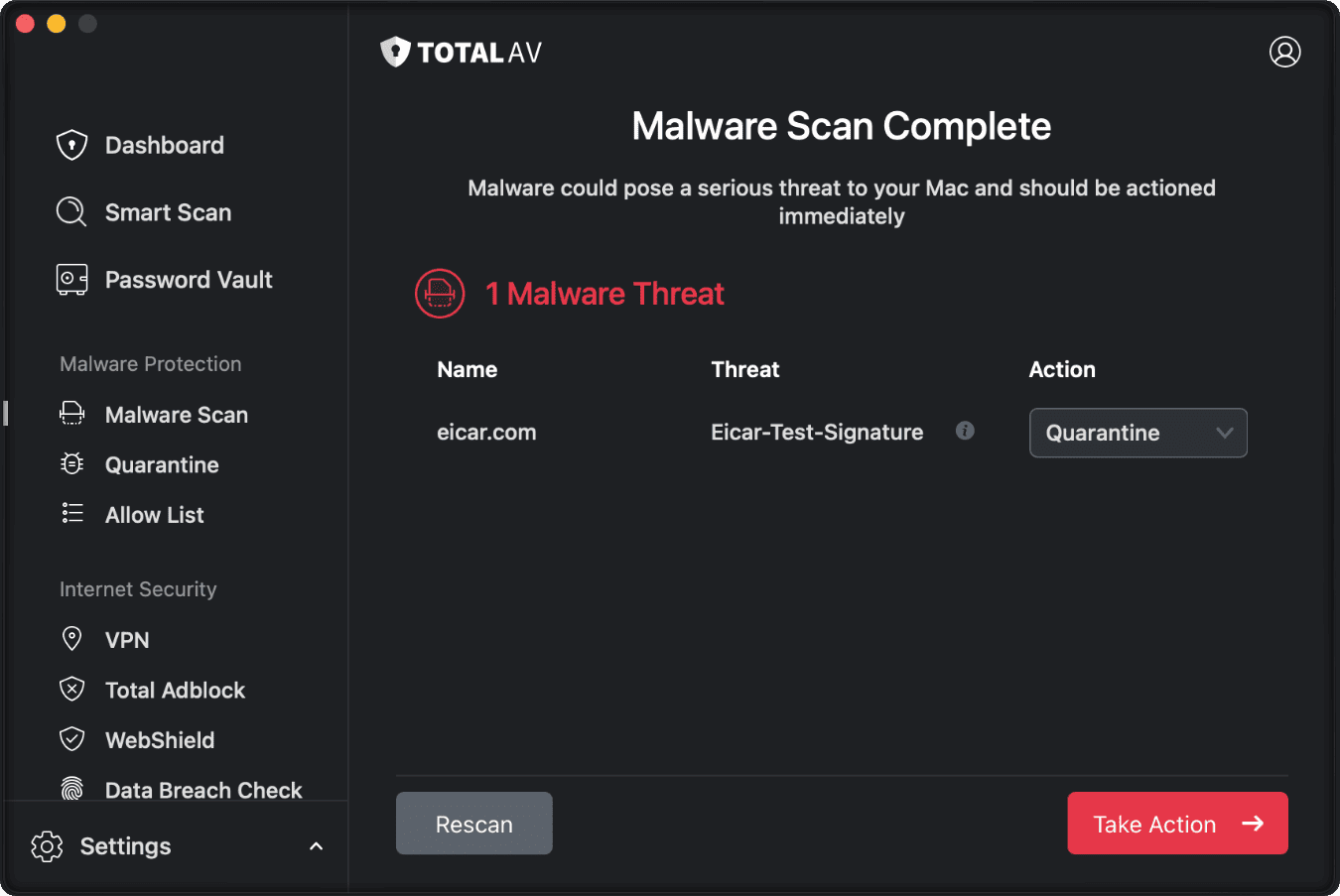
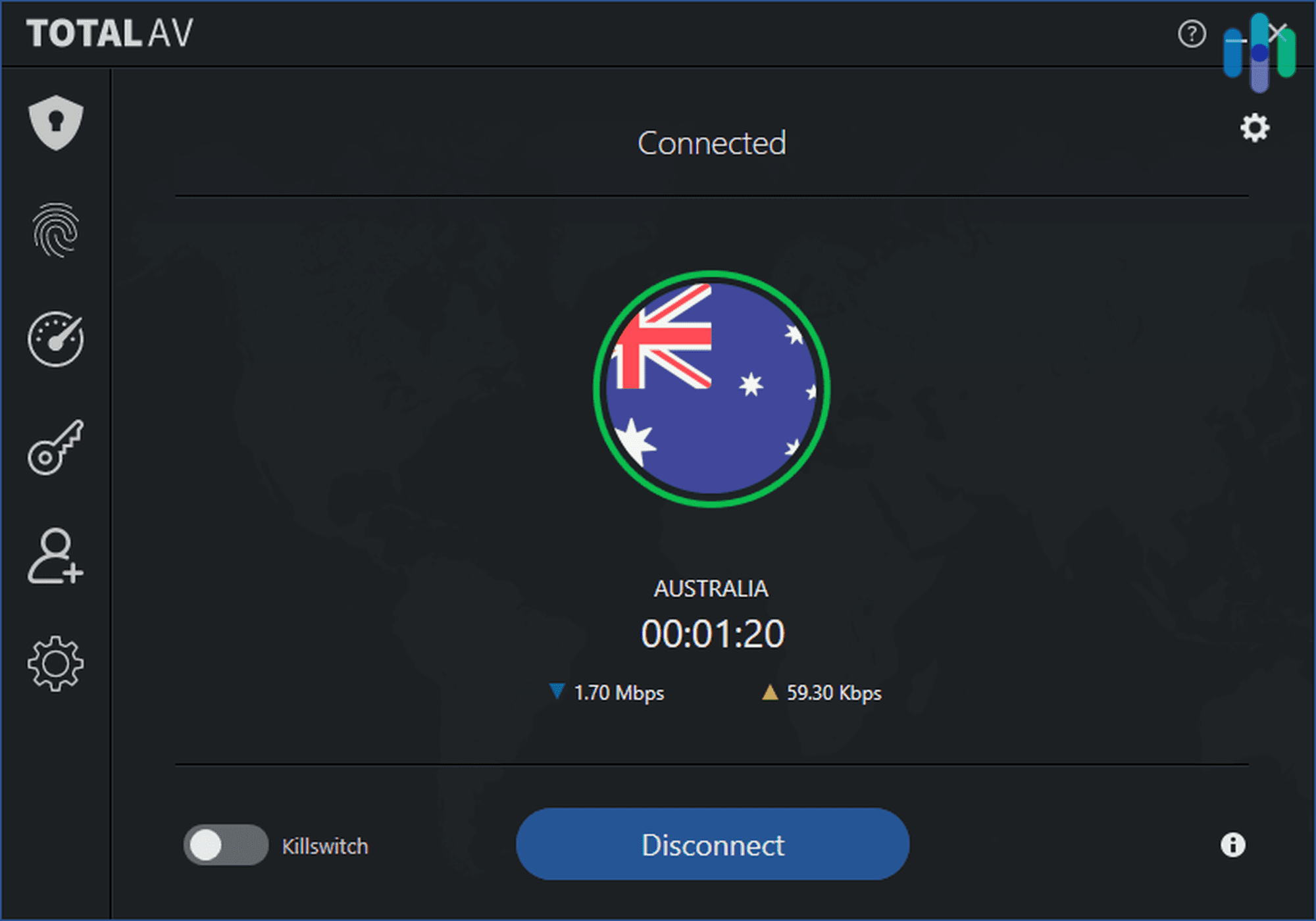
TotalAV nailing one of our test viruses, locking it in quarantine quickly. Our TotalAV Malware Test Results
TotalAV performed better in our Mac malware tests than it did in our Windows tests, blocking and quarantining myriad viruses delivered in multiple formats, including compressed files. Our in-house results match the latest lab results from independent testing authority AV-Comparatives, where TotalAV had a 98.7 percent protection rate.1
We generally prefer antiviruses that use behavior-based detection to spot threats. They don’t just look for malware; they look for suspicious system behavior that malware could be causing. But the fact that Total AV lacked this feature didn’t seem to matter in our tests.
>>Go Deeper: A Complete Guide to Antivirus Protection
Did You Know: One thing we noticed during the installation process: TotalAV needs Mac Mavericks (10.9) or later to run. So if you’ve got an older machine, wait for your next Mac to try TotalAV.
Our Experience with TotalAV’s Extra Security Features
Like all true antiviruses, TotalAV scanned our system for threats in real time. TotalAV’s deeper scanning options came in two forms. Smart Scan is quicker and looks for trackers, cookies, and junk lurking in your system. We got rid of nearly 2 GB of clutter on our first go. The full malware scan takes longer and scours your system for embedded viruses, trojans, and spyware. TotalAV took about half an hour to scan our 120 GB system drive, which is pretty fast.
>>Read More: How to Spot and Prevent Spyware Attacks
These features are a click away in a well-designed, dark-themed dashboard that includes a VPN (on premium plans), ad blocker, and an anti-phishing feature called “WebShield.” Similar to but less comprehensive than Norton’s scam protection, “WebShield” works with your browser to identify scammy websites and links before you click. We found that it’s most similar to the browser-based malware blocker that comes with NordVPN, one of the best antivirus VPN bundles we tested this year.
FYI: We tested TotalVPN’s free version, but we don’t recommend it. Real-time virus scanning — a core feature — only works for the first few hours, then you have to pay to unlock it.
Pricing
For an antivirus that offers so much core and extra security, TotalAV’s pricing is reasonable. We recommend either of their two premium plans: “Total Internet” ($39 per year, $129 at renewal) or “Total Security” ($49, $149 at renewal). They both include the VPN. Comparable plans from Norton are similarly priced and include parental controls, but TotalAV’s device limit is higher — six and eight respectively — which will come in handy for larger households.
What Else You Get with TotalAV: TotalAV for Mac also has a competent ad blocker and a “System Tune-up” feature that scours your system for junk and duplicate files. Just be careful before you delete those duplicates! We lost a few important files this way. On premium plans, you’ll also find a password vault.
-
4. Surfshark Antivirus - Best with VPN
Get Surfshark Links to Surfshark.comProduct Specs
Virus Detection Yes Malware Detection Yes Firewall No Full, quick, and scheduled scans Yes Real-time protection Yes Behavior-based monitoring Yes Who’s Surfshark Good For
Surfshark’s Antivirus for Mac is a powerful add-on for its premium VPN subscribers. Surfshark plans are cheap ($2.49 per month for 27 months) and well-rounded with extra ransomware and webcam protection.
Pros
- Cheap starter plans
- Stellar user experience
- Behavior-based malware detection
- Extra ransomware and webcam protection
Cons
- No firewall
- Five-device limit for antivirus
- No system tune-up
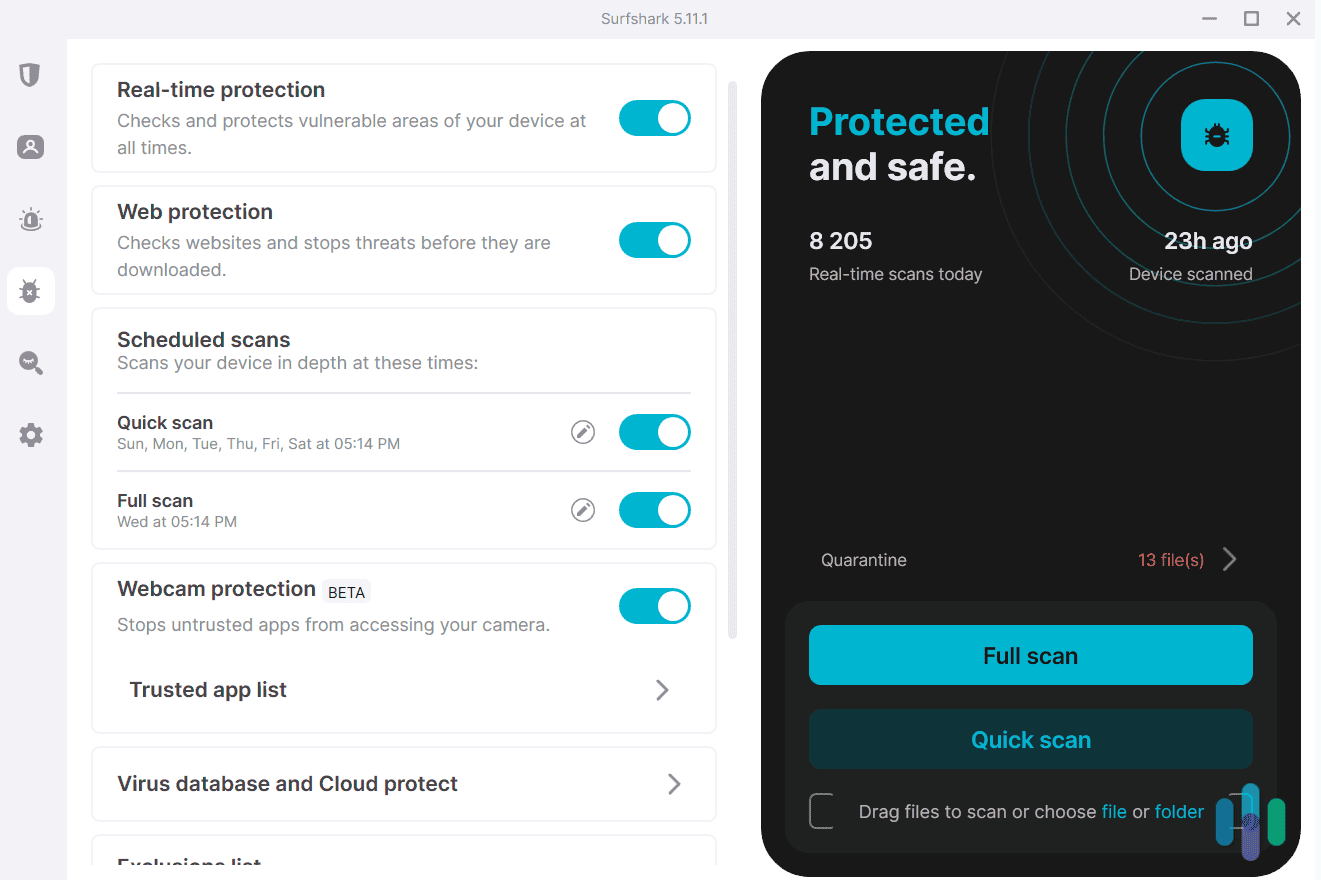
Our Surfshark Malware Test Results
Surfshark handled our battery of malware test files with high accuracy, including compressed files and files that tested its cloud-based detection capabilities. Surfshark also caught our attempt to force it to download a corrupt file from an automatic page load — commonly known as “drive-by malware.” It did stumble in our phishing test though. All in all, Surfshark’s Mac malware catch rate was excellent.
FYI: We noticed that Surfshark wasn’t only shielding us from malware. It was simultaneously flagging the utilities we used to unzip potential threats, like Unarchiver, as well as other inbound connections from media players like Plex.
Our Experience with Surfshark’s Extra Security Features
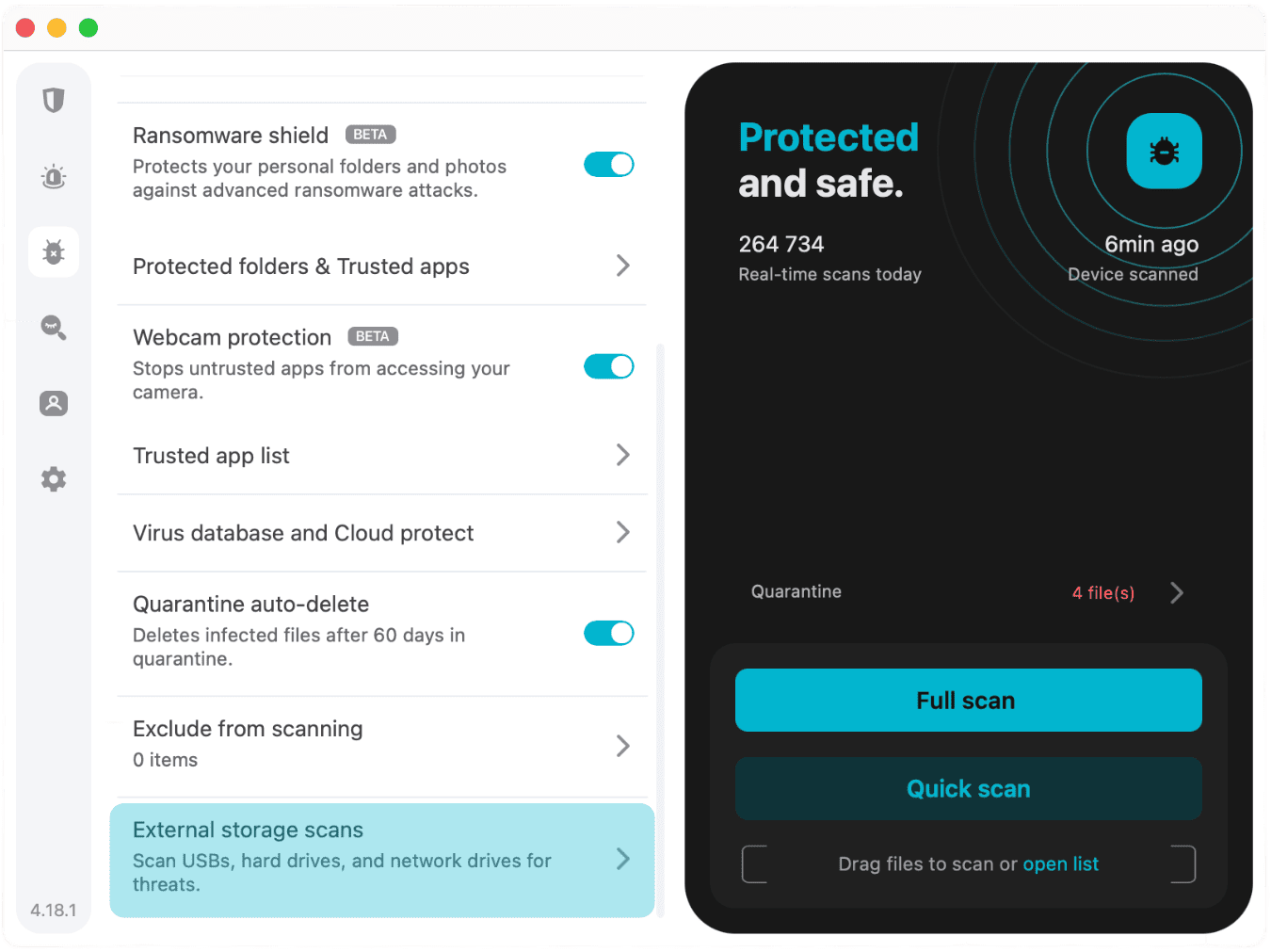
Surfshark has invested a lot in user experience, so their Mac dashboard is top-notch and easy to use. You can run or schedule quick or deep system scans, whitelist apps you trust, and even scan external/NAS drives, which is great. Our 1 TB Seagate hard drive might take hours to check, so we liked that we could run those scans separately.
Surfshark has a special external storage scan option (in blue above) that guaranteed all our files were clean while saving time. Surfshark’s “Ransomware Shield” and “Webcam Protection” features are both in beta, but they worked in our tests. The first puts sensitive documents in a vault and flags any programs that try to interact with them. The second requires you to whitelist any apps that use your camera (and presumably catches any malware that attempts to hijack it). Our only issue with Surfshark was a missing firewall. We like to keep a software firewall running to catch anything our native Mac firewall doesn’t.
Pro Tip: Unlike TotalAV, which covers machines running older OS, you won’t be able to use Surfshark’s Antivirus unless you’re on Mac OS 10.15 (Catalina) or higher.
Pricing
Surfshark is $2.49 per month for the first 27 months. Surfshark’s post-honeymoon rate is a little murkier than TotalAV or Bitdefender (below), which also has a quality Mac antivirus. Safe to say it will shoot up considerably when you renew. It’s also worth pointing out that Surfshark is a VPN first, so you can’t purchase the antivirus separately. It’s more of a perk (among many other perks) you get with their higher-tier plans.
>>Compare: Surfshark versus Bitdefender Antivirus
What Else You Get with Surfshark: The “Surfshark One” plan also came with a standard data breach monitor and a not-so-standard feature that let us create alternative IDs, and even email aliases, to plug into online forms. The latter was actually very handy when dealing with companies we didn’t know or trust.
-
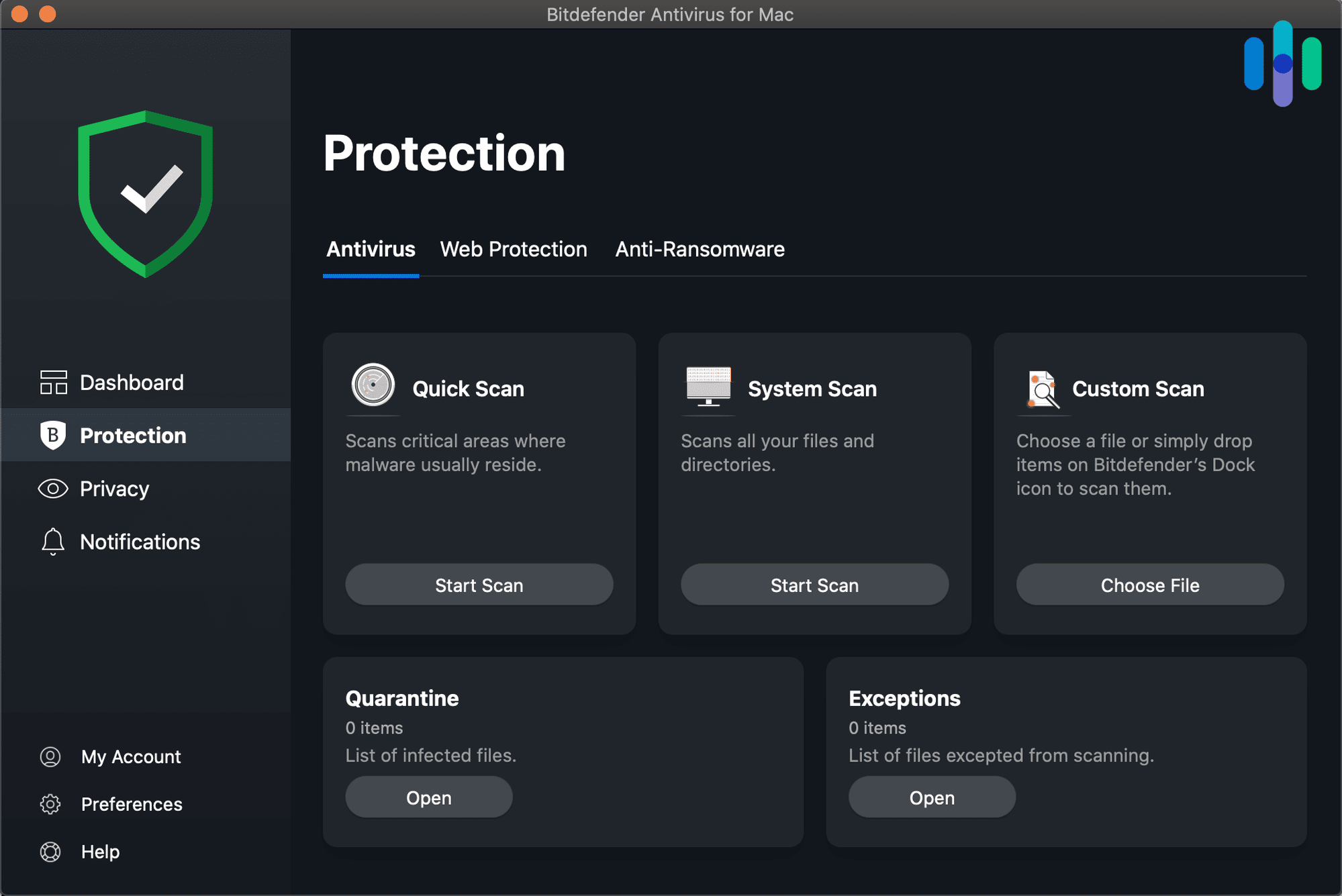
5. Bitdefender - Best Malware Protection
View Plans Links to BitdefenderProduct Specs
Virus Detection Yes Malware Detection Yes Firewall Yes Full, quick, and scheduled scans Yes Real-time protection Yes Behavior-based monitoring Yes Who’s Bitdefender Good For
For those who know their way around antivirus software, Bitdefender provides heavy-duty malware protection with powerful behavior-based virus detection. Like TotalAV, Bitdefender has a free version. Unlike TotalAV, their free software doesn’t hide core features behind a paywall.
>>Read More: The Best Free Antiviruses of 2025
Pros
- Free version with real-time virus monitoring
- Behavior-based malware detection
- 100 percent malware catch rate
- Smart phishing and ransomware protection
Cons
- A little pricier than the competition
- No firewall for Mac
- Requires a separate app for the VPN
Our Bitdefender Malware Test Results
Bitdefender was aggressive in blocking malware. It caught fresh viruses we attempted to sneak onto our Mac desktop as well as trickier files stuffed with adware and spyware we’d compressed and hidden deep within our system. And it was successful 100 percent of the time, which is a much higher rate than we usually see in our in-house tests. AV-Comparatives’ latest tests produced nearly identical results in bulk. Bitdefender was at the top of their list with a 99.6 percent catch rate.
>>Compare: Bitdefender vs. Norton Antivirus
FYI: We noticed, in our malware tests, that Bitdefender paralyzed both Windows and Mac bugs. This is the kind of thoroughness we like to see in an antivirus.
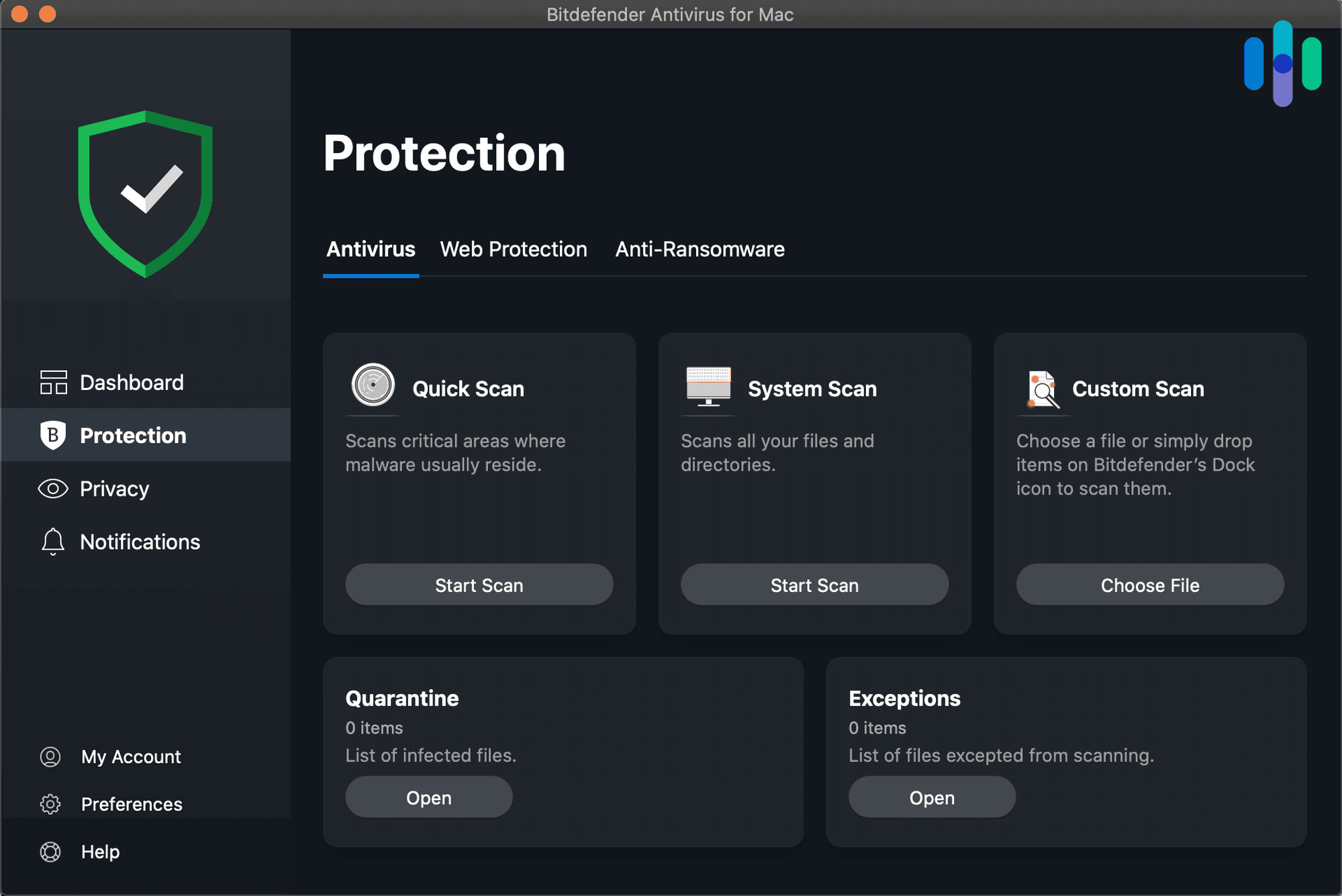
Bitdefender’s dashboard made it easy for us to run and schedule system scans. Our Experience with Bitdefender’s Extra Security Features
Unlike most antiviruses we’ve tested, Bitdefender’s dashboard wasn’t unified. The VPN, which comes with premium subscriptions, is a separate app. This isn’t great for user experience. The antivirus app for Mac is also missing a firewall. However, Bitdefender is equipped with a number of other security features that protected our Mac beyond its quick and deep system scans.
Extra phishing protection is one of Bitdefender’s main draws. Getting phished can be devastating so this was good to see. The results of our AMTSO phishing tests, which Bitdefender passed repeatedly, were even better.
Pro Tip: Our initial deep scan with Bitdefender took about an hour and a half, which is significantly longer than our experience with Surfshark and Norton but a lot quicker than what we experienced with McAfee.
Pricing
All Bitdefender’s paid plans come with protection for up to five devices, starting with its “Total Security” plan ($59.99 for the first year), which is slightly more expensive than a comparable TotalAV or Norton plan. However, if you’re in the market for an unlimited VPN, which we recommend, you’ll want to stick with their “Premium Security” plan ($79.99 per year). Otherwise, Bitdefender will throttle your VPN use to a not-very-useful 200 MB per day.
For families, Bitdefender does have a family-oriented option with a very generous 15-device limit. The only issue we see here is that VPN use is again throttled, which is a shame. Otherwise, at $69.99 ($119.99 at renewal) Bitdefender’s family package is a steal.
>>Learn More: How Much Should I Be Paying for an Antivirus?
What Else You Get with Bitdefender: Unusually, Bitdefender comes with a security feature called “AutoPilot,” which detects vulnerabilities in your current security setup and makes improvements. You’ll also find cryptomining protection and, with premium plans, parental controls and a password manager.
-
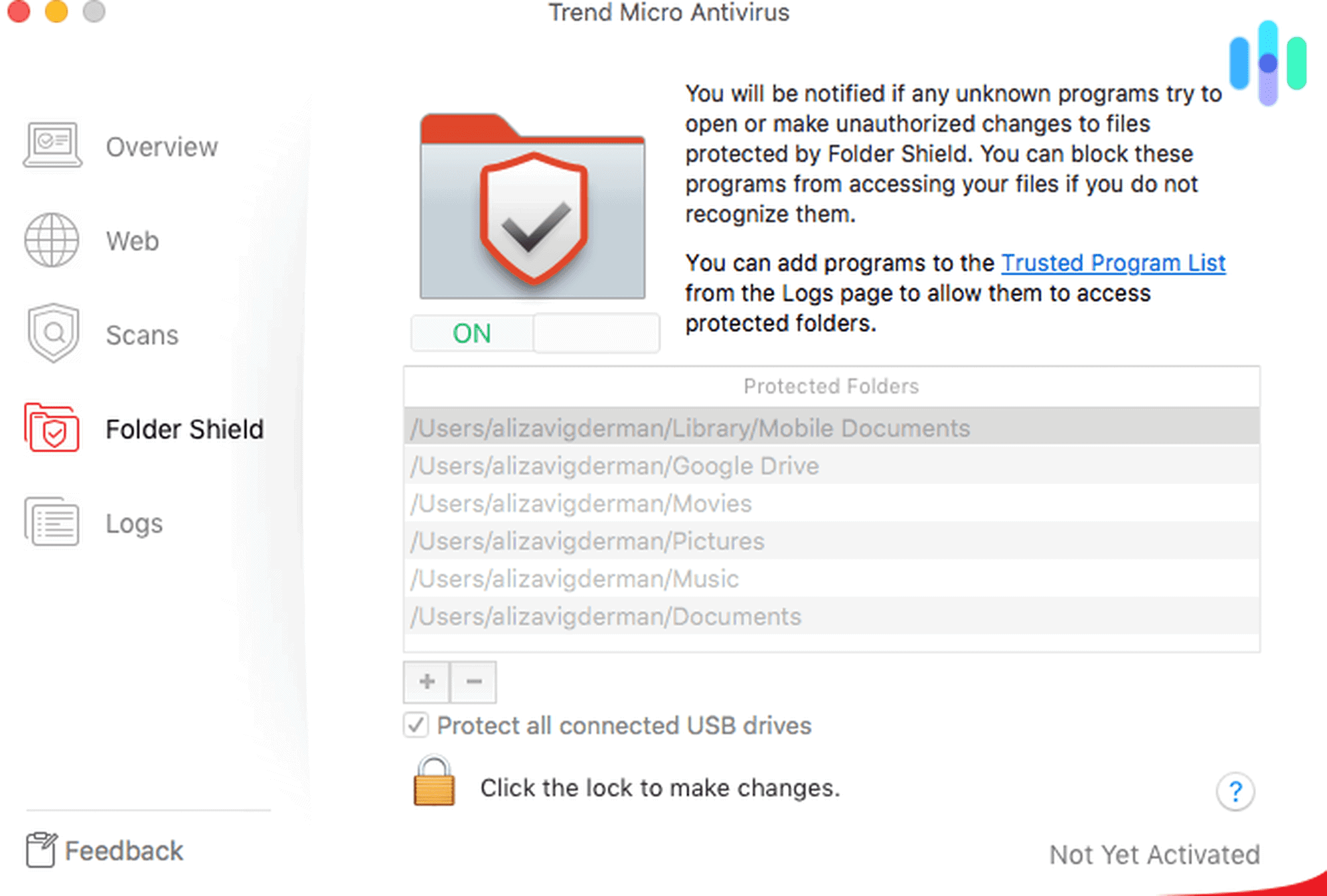
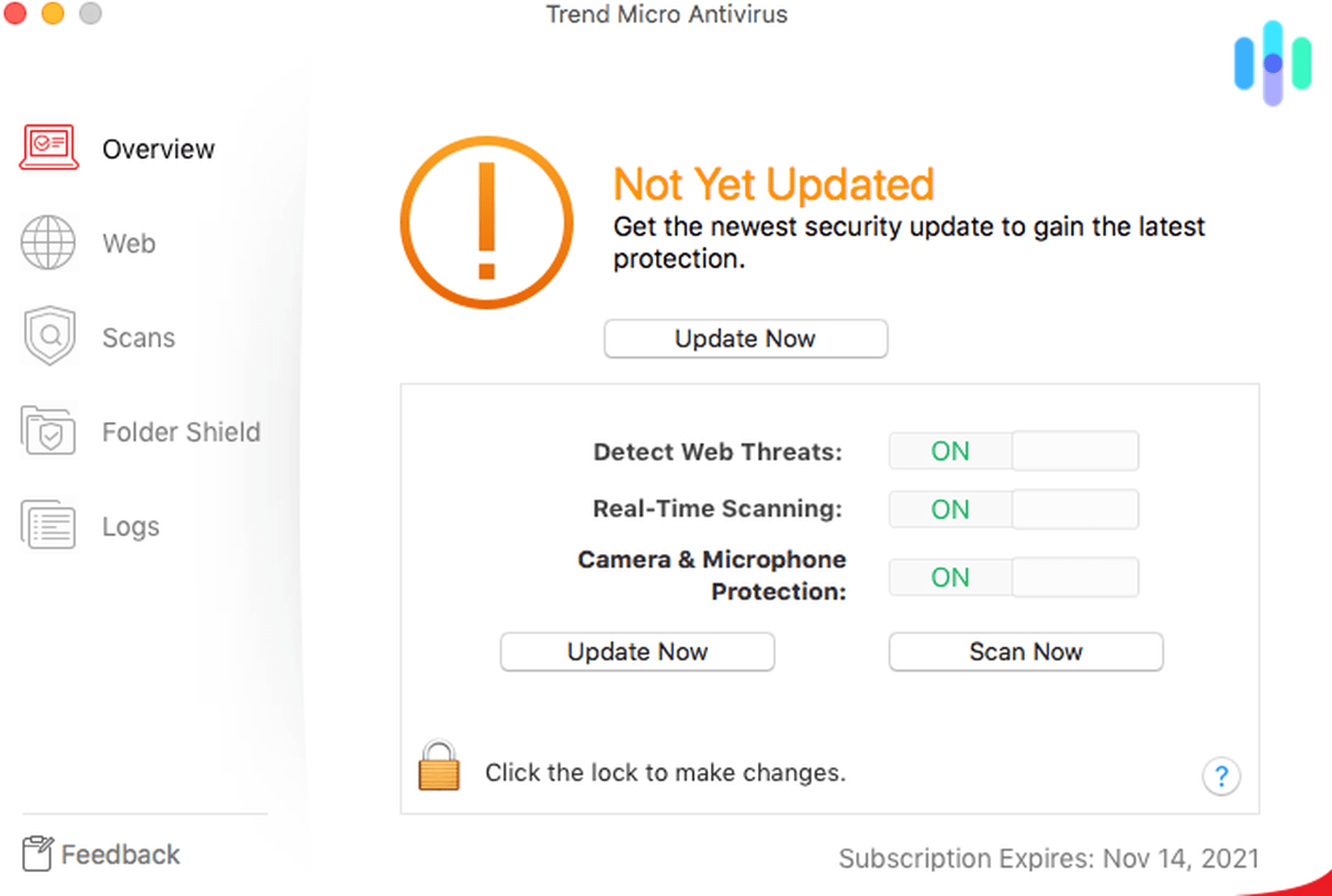
6. Trend Micro Antivirus - Best for Social Media Privacy
Product Specs
Virus Detection Yes Malware Detection Yes Firewall Yes Full, quick, and scheduled scans Yes Real-time protection Yes Behavior-based monitoring Yes Who’s Trend Micro This Good For
Trend Micro is a decent antivirus that’s not too expensive. The app and installation process are both a little clunky on Macs. But once you get it up and running, Trend Micro’s AV does its job with a good virus catch rate. It also has a useful social media tool that can help Mac users enjoy a little privacy from social media companies.
Pros
- Cheap starter plan
- Privacy scanner combats data snoops
- Folder scan protects sensitive docs
- Extra malware protection for browsers
Cons
- Clunky app and installation
- No free version
- History of ugly data breaches
Our Trend Micro Malware Test Results
Trend Micro caught two-thirds of the test bugs we introduced onto our system, which wasn’t horrible. For the record, it performed much better in independent tests, which we usually defer to. However, one of the files we slipped past Trend Micro would have forced the app to hand over our password and session data. We weren’t too pleased with that.
FYI: When Trend Micro performed its first “Smart Scan,” it wasn’t a full system scan like we got with TotalAV, Aura or Surfshark. It was a partial scan. To scan our entire system, we had to click “Full Scan” (buried one layer deep in its Overview tab). Our full scan only took about 30 minutes, which was pretty snappy.
Our Experience with Trend Micro’s Extra Security Features
When we tested NordVPN, we really liked its browser protection because it flagged suspicious websites in our search results with an unobtrusive shield (red for shady, green for good). Trend Micro has a similar feature, though with a green highlight, which was more than a splash of color.
>>Go Deeper: A Complete Guide to Private Browsing
Trend Micro put our sensitive documents in a special folder where other apps couldn’t access them. Trend Micro’s “Privacy Scanner” feature identified privacy settings in our favorite social media platforms that were allowing companies to secretly collect data from us. For folks who aren’t already on top of this, this may be an eye-opener. Just keep in mind that Trend Micro isn’t protecting us with this feature; it’s making helpful privacy suggestions we have to act on.
>>Read More: Is Social Media Ruining Our Lives?
Pro Tip: When we activated Trend Micro’s “Web Threat Protection” feature, it kicked in for Safari but not Chrome, even though Chrome was our default browser. Once we closed Safari and refreshed Chrome, our protection worked.
Pricing
Trend Micro’s pricing is a little wonky in so far as a basic feature like 24/7 customer support is only available with their top-tier plan, “Premium Security Suite.” The same goes for its VPN. Pricing for that plan is $54.99 for the first year and $149.99 at renewal. You’ll notice that this renewal rate is a bit more than comparable TotalAV or Bitdefender plans. Cheaper single-device packages start at $19.95, similar to Norton but with fewer extra security features.
>>Learn more: Do I Really Need a VPN?
Are you a growing family? Like Norton, Trend Micro’s “Premium Security Suite” covers 10 devices, making it a pretty good deal for households with a lot of devices. Even better, unlike Bitdefender, Trend Micro doesn’t throttle its VPN.
What Else You Get with Trend Micro: Trend Micro’s “Premium Security Suite” plan includes identity theft protection. Because ID theft and cybercrime go hand in hand, this is a very useful ad-on — with one caveat. While Trend Micro’s highest-tiered plan covers 10 devices, its ID theft protection only covers the registered user. So if your kids get into trouble, they wouldn’t be covered.
>>Learn More: The Best Family Identity Theft Protection Packages This Year
-
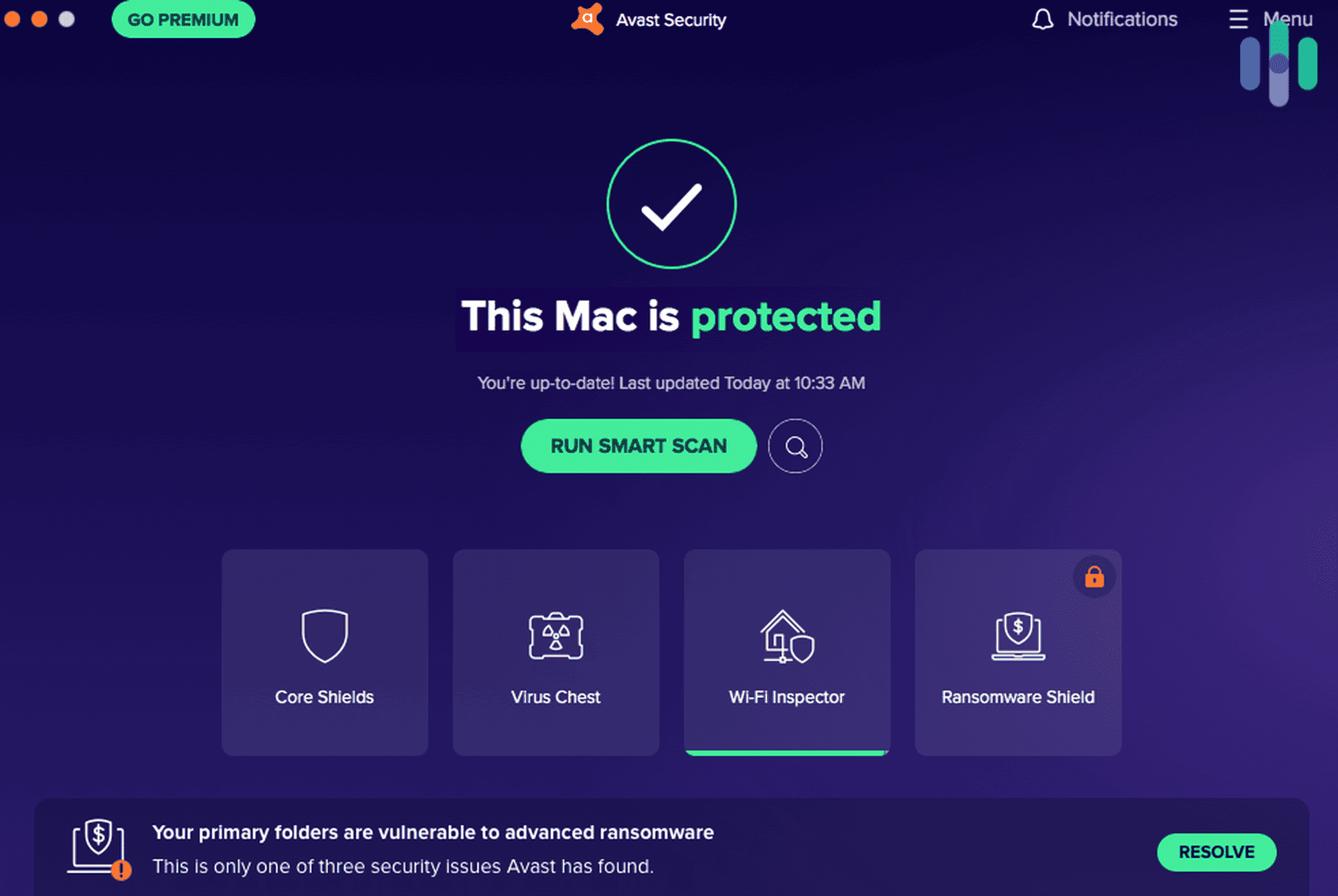
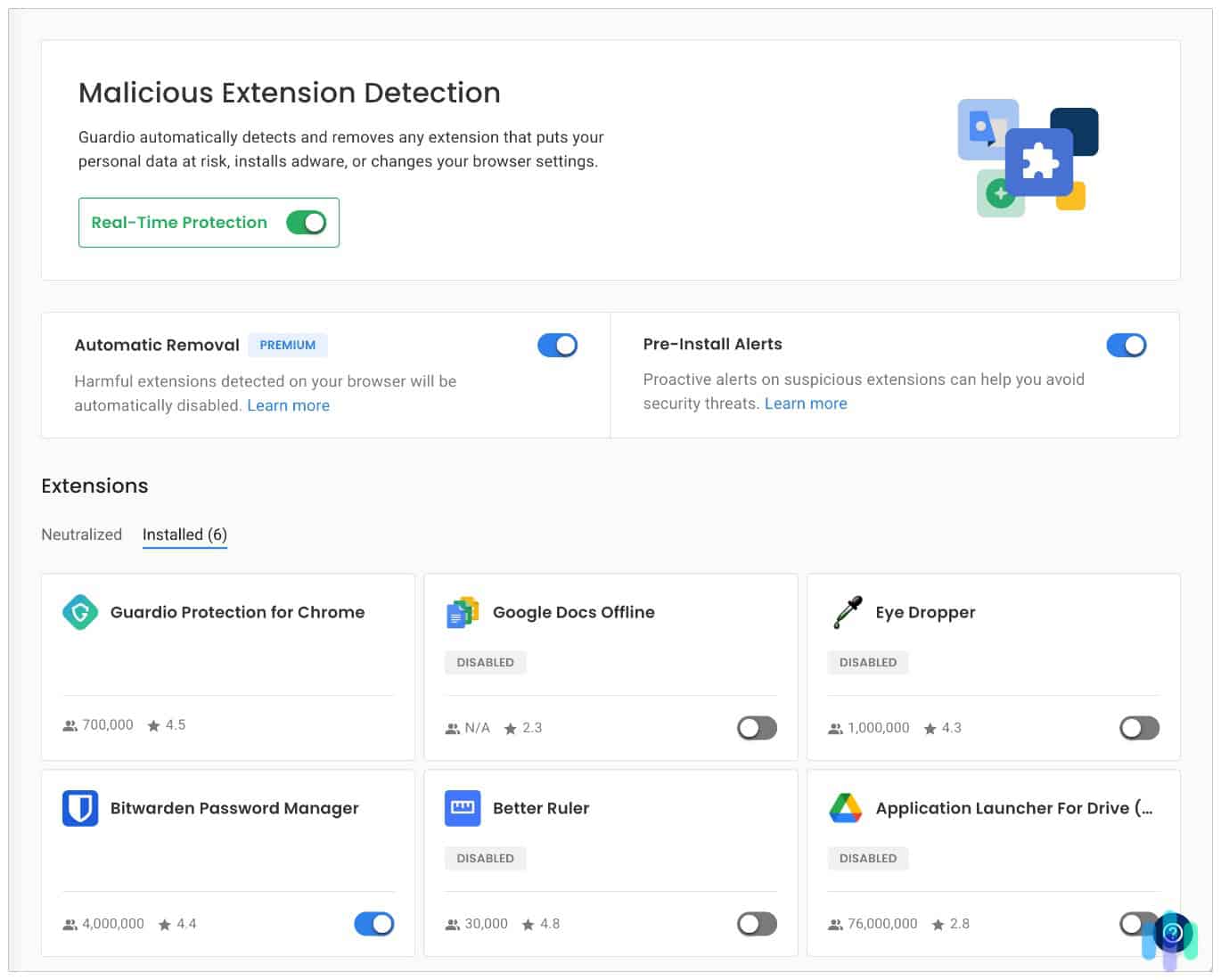
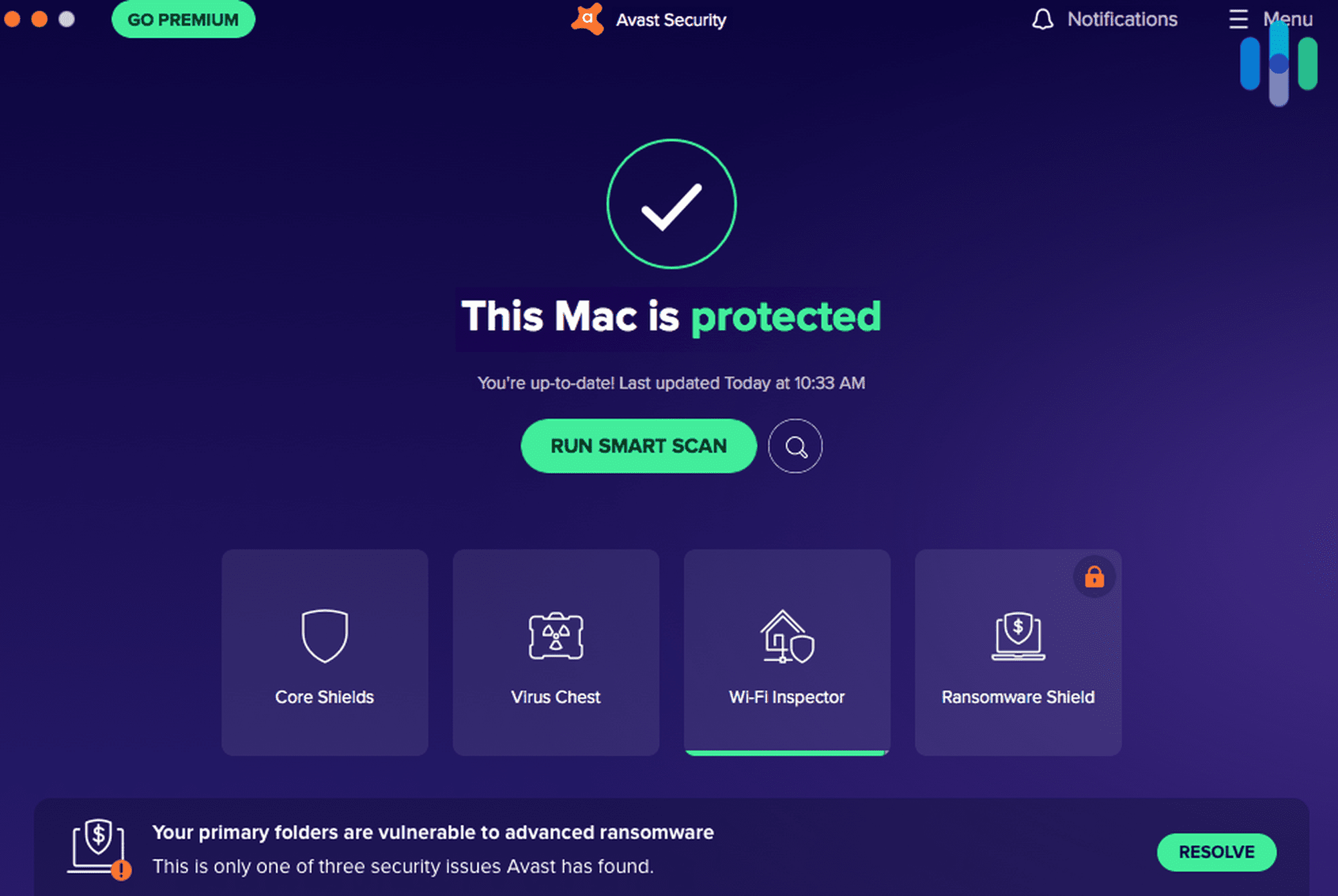
7. Avast Antivirus - Best Free Version
View Plans Links to Avast.comProduct Specs
Virus Detection Yes Malware Detection Yes Firewall Yes On-demand Scanning Yes On-access Scanning Yes Behavior-based monitoring Yes Who’s Avast This Good For
For Mac users on a budget, Avast’s free antivirus may be all you need. Avast is also the only AV on this list that has a firewall for Macs. However, this feature, and others we tested and liked, are only available with a paid plan.
Pros
- 60-day free trial for Macs
- Firewall with premium plan
- Core features available on free version
- Extra security for online payments
Cons
- May sell our data
- No phone or chat support
- Annoying pop-ups
Our Avast Malware Test Results
In our in-house malware tests, Avast didn’t pass with flying colors, but it did well enough, catching around 60 percent of the viruses we threw at it. For an antivirus with a 100 percent catch rate, check out our experience testing Kaspersky. That said, according to AV-Test’s latest Mac-only results, Avast was impenetrable. These figures are significant because of the sheer number of tests performed.
>>Compare: Kaspersky vs. Avast
Notably, Avast included as core features with its free version tools that are often locked behind paywalls, including a web shield that blocks malicious downloads.
Pro Tip: We started on Avast’s free version, only upgrading to test its ransomware and phishing protection. Most of the security features we used day to day, like real-time monitoring, were free.
Our Experience with Avast’s Extra Security Features
Upgrading to Avast’s premium plan gave us ransomware protection for our sensitive documents and a phishing shield that flagged suspicious email attachments. We also enjoyed two features unique to Avast. The first was a “Wi-Fi Inspector” that told us if any devices we were sharing a network with were potential threats.
The second was a tool that verified if a site accepting online payments was actually safe. It’s so easy to fall victim to credit card fraud these days; this feature alone was worth a full subscription.
>>Learn More: The Best Identity Theft Services With Fraud Detection
Look Out: Avast’s free version is good, but they still want you to upgrade. If you get an alert upon installation that says you’ve got ransomware on your Mac, you probably don’t. It’s a scare tactic we don’t like but have come to expect. See below.
Avast alerts us to a potential ransomware threat that didn’t actually exist. Pricing
Avast’s pricing is relatively straightforward. The free version covers all your basic needs. If you upgrade, a single Mac license runs $49.99 per year ($77.99 at renewal). This is the priciest option we’ve tested, and it’s not feasible for anyone with more than one device to protect — which is all of us.
Avast’s second option ($69.99 per year) makes a lot more sense. It covers 10 devices, not all of which need to be Macs. And that price will only shoot up to $99 at renewal, making it one of the cheapest premium antivirus plans we’ve tested this year.
What Else You Get with Avast: Avast is the only antivirus on this list that comes with a firewall for Macs. This might not seem like much for Mac users who already have a built-in firewall. But remember: Your native firewall only monitors inbound connections. For everything else, you need a software firewall to keep safe.
>>Read more: The Best Firewalls of 2026
Methodology: How We Ranked The Best Antivirus Apps for Mac
How We Test Antivirus Software
Picking the right antivirus means looking past detection rate claims and marketing copy. Our recommendations are guided by our Editorial Guidelines, which means our team installs and puts every antivirus through its paces on both desktop and mobile devices. Our evaluations cover malware detection against live and simulated, scan time completion speed (full and quick scans), and a careful assessment of how much each software affects device performance. We also test real-time protection reliability, phishing link detection, and ransomware blocking. Subscription pricing, simultaneous device limits, and plan flexibility and refund policies round out each evaluation to make sure every pick delivers protection at a fair price.
How We Ranked These Suites
Mac’s reputation for security has historically led users to underestimate their exposure, but macOS-targeted malware, adware, and phishing attacks have grown considerably more sophisticated in recent years. We designed our ranking criteria around the threat vectors and platform behaviors that matter most to macOS users. Here’s what drove our scores:
- macOS Optimization: We tested each suite’s malware detection performance specifically on macOS, testing against Mac-targeted adware, browser hijackers, and increasingly common macOS ransomware variants. We also verified whether each product offered a native Apple Silicon build or relied on Rosetta 2 emulation.
- System Impact on Mac Performance: We measured how each suite affected Mac responsiveness during full and background scans. We tracked CPU usage, memory footprint, and the impact on common tasks like video editing, browser performance, and file transfers, since Mac users tend to run resource-intensive workflows.
- Gatekeeper and macOS Security Feature Compatibility: We assessed how well each antivirus suite worked alongside macOS’s built-in security architecture, including Gatekeeper, XProtect, and System Integrity Protection. We checked whether each product complemented Apple’s native defenses or introduced conflicts that undermined the stability and security of the broader macOS environment.
- Privacy Feature Depth for Mac Users: We evaluated each product’s broader privacy toolset, including webcam and microphone access monitoring, network traffic analysis, and browser privacy tools. We assessed whether these additions delivered meaningful protection for Mac users concerned about data harvesting and unauthorized system access, or simply padded feature lists without adding real security value.
Every suite on this list cleared all four criteria across repeated Mac-specific testing — not just on the platforms each provider happened to perform best on.
About Our Team
Security.org’s antivirus recommendations are overseen by Brett Cruz, a cybersecurity expert and antivirus specialist with years of hands-on experience evaluating antivirus suites, VPNs, and digital security tools. Brett’s rigorous, reader-focused methodology shapes every recommendation on this page.
Supporting Brett is Security.org’s independent roster of security researchers and product testers. We have 20+ specialists who have collectively published 740+ guides and reviews representing over 25,000 hours of accumulated security product testing since 2018. That team includes:
- Gene Petrino: Former S.W.A.T. commander and law enforcement veteran, serving as a lead advisor across our antivirus and cybersecurity coverage
- Ozzie Enriquez: West Point graduate and former Deputy Director of Security at the Missile Defense Agency, U.S. Pentagon, contributing expertise in cybersecurity strategy and threat intelligence as a senior advisor
- Corey Birnstengel: Editor, videographer, and product reviewer behind 200+ in-depth video reviews spanning eight security and consumer tech product categories
- Cort Honey: Product tester with an engineering background, 1,000+ hours of hands-on evaluation experience, and a specialty in making technically complex security software digestible and actionable for everyday users
No security provider can pay to change our lists, since our recommendations are completely independent, and that’s not a policy we make exceptions to.
Do I Really Need an Antivirus for My Mac?
Apple reviews and approves any software for use on Macs before it can be distributed. This reduces your chances of infecting your Mac with malware to a degree. After that, you may have to give your new apps system permissions before you can use them. If they need to establish incoming connections over your network, you’d have to approve them in your firewall settings.
These are useful safety features that certainly enhance your digital security. However, in practice they’re not enough. One, we know that malware-riddled apps occasionally make it into the Apple Store despite Apple’s careful screening.3 Even more important: your Mac’s native antivirus doesn’t monitor your internet activity in real time like an antivirus does, and your built-in firewall doesn’t block outbound connections, only inbound.
For all these reasons and more we strongly recommend fortifying your Mac’s built-in malware protection with a quality antivirus.
Did You Know: It’s easy to review your firewall permissions on a Mac. Just open up System Settings > Network. Then on the Firewall tab, click options. That will bring up a screen with all your firewall permissions. If you see something that doesn’t look right, block it and investigate.
How Do I Install and Use an Antivirus with My Mac?
Installing antivirus software on your Mac is usually very easy. After you download and install the Mac app, your antivirus should lead you through the permissions process. This usually means you’ll have to give your AV full disk access, some extensions privileges, and permission to run in the background (for real-time monitoring).
After that, we recommend running a full system scan so you can start with a clean slate. If your antivirus comes with a firewall, like Avast, switch that on. Finally, toggle on extra security features like phishing, ransomware, and webcam protection. For antiviruses with web shields, you’ll also have to add and enable browser extensions.
Pro Tip: In our experience, antiviruses don’t work well together. We recommend that if you’ve already got one antivirus running, you should uninstall it (and toggle off any system permissions you gave it) before starting a new one.
Are Free Antiviruses for Mac Any Good?
TotalAV, Bitdefender, and Avast offer free versions. Not all of these are perfect solutions for Mac users, however. TotalAV paywalls critical real-time virus monitoring, for example. Bitdefender doesn’t. However, if you want to use Bitdefender’s VPN for more than the skimpy, allotted 200 MB per day, you’ll need to upgrade to a paid plan.
Avast, on the other hand, has a free version with most core features enabled. The downside of not paying is that Avast’s free plan doesn’t have phishing or ransomware protection, and it doesn’t come with a VPN like most of the other options on this list. That said, if you want to try a free antivirus first, we recommend Avast, which also has a firewall for Macs.
Free Version or Free Trial?: If you’ve got the option, and are just testing the waters, go with the free version. There’s no credit card involved. When you trial a paid plan, even for free, it usually involves putting a credit card down.
Summing Up
For many years Windows machines were the ones hackers chose. Not anymore. But picking an antivirus to protect your Mac is tough because many companies are still producing apps that work better with Windows.
The seven antiviruses on this list are exceptions. They’re all best-in-class and work well with Macs. For price, user experience, and overall security, Norton ($19.99 per year) is our top pick. That said, if you want a bundle with one of the best identity theft protection services, go with Aura. And if you want to focus on device protection, TotalAV earned our recommendation.
Frequently Asked Questions
-
What’s the best antivirus for Mac?
Our top pick is Norton. It’s easy to use, it performed well in our malware tests, and it’s comparatively cheap.
-
Do Macs have built-in antivirus?
Yes, but most of Apple’s antivirus efforts revolve around the Apple Store and protecting Macs from malicious programs loaded through apps. There are too many other modes of attack to make this approach your only security solution.
-
How much does a quality antivirus for Mac cost?
Nothing — if you go with one of the free options on this list. Bitdefender and Avast are both very good choices. Just keep in mind that, with a free plan, you’re forgoing extra security features you may want to have and that could cost as little as $20 per year.
-
Do all antiviruses come with VPNs?
No, not all, but several options on this list do — take TotalAV, Aura, Surfshark, and Bitdefender, for example. Bundling your VPN with your antivirus is a good idea and will usually save you money.
-
Why can’t I use my built-in firewall to protect my Mac?
Mac’s native firewall monitors inbound connections, not outbound. And it won’t protect you from phishing scams, social engineering scams, or from zero-day exploits. You need an antivirus with behavior-based detection for that.
-
AV Comparatives. (2024). Independent Tests of Anti-Virus Software.
av-comparatives.org/wp-content/uploads/2024/11/avc_real-world_protection_2024b.pdf -
AnnualCreditReport. (2025). Homepage.
-
Securelist. (2025). Take my money: OCR crypto stealers in Google Play and App Store.
securelist.com/sparkcat-stealer-in-app-store-and-google-play/115385/